作者:马宁
最近被一个软件网络连接的问题,折腾得死去活来。问题本身不复杂,主要是网络设置不同造成的,在这里不多说了。在调试过程中,用到了Windows CE下的几个网络监测工具,才了解到Windows CE下也可以用我们平时用的网络监测工具,写出来和大家共享一下吧。
环境设置
我用Windows CE 6.0 R2环境做实验,开发环境搭建可以参考:
我们使用Device Emulator作为测试平台,创建OS Design的过程就不多说了,可以参考:
http://blog.csdn.net/aawolf/archive/2007/12/19/1953448.aspx
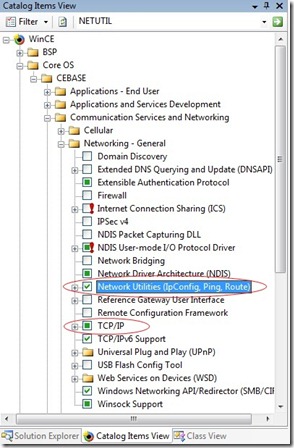
需要指出的是,需要在OS Design中加入SYSGEN_NETUTILS。如果在Catalog Item中选择的话,选择如图所示的Network Utilities (IpConfig, Ping, Route), TCP/IP选项(SYSGEN_TCPIP)也会被加入。
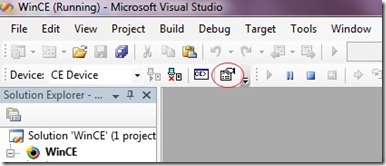
OS Design创建和编译完成后,我们要部署到Device Emulator上。设置Device Emulator的外观和网络连接,选择Connectivity Options。下图红色圆圈位置:
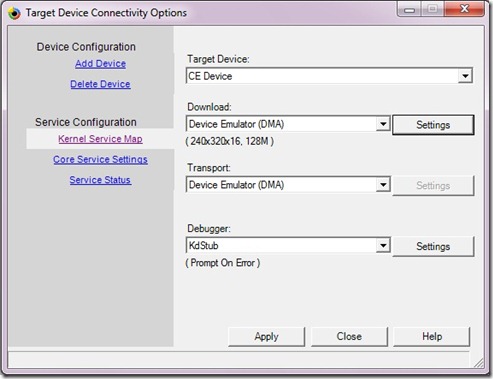
在Connectivity Options对话框里,Download和Transport选择“Device Emulator(DMA)”,Debugger选择“KdStub”,点击Download后的Settings按钮。
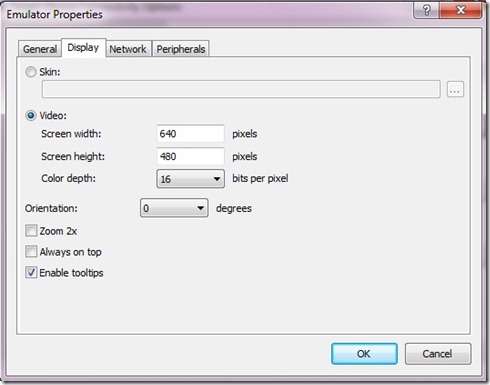
在Display页面里将分辨率设置为640和480。
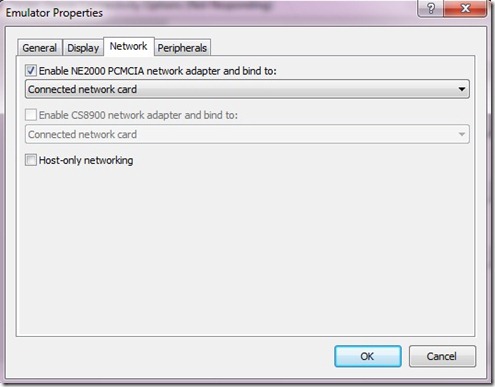
在Network页面里,选择“Enable NE2000 …”网卡的选项,这样,PC上的网络连接就可以被映射为Device Emulator的NE2000网卡了。需要提醒一点的是,需要在PC上安装Virtual PC虚拟网卡驱动,最简单的办法就是安装Virtual PC 2007.
到这里,我们已经配置完Device Emulator的网络配置,选择Target菜单里的Attach Device,将编译好的NK.bin下载到Device Emulator上,并运行。
Ping命令
等Device Emulator启动之后,我们可以在输入命令进行调试了。在Target目录中选Target Control,Command Shell会出现。下图所示:
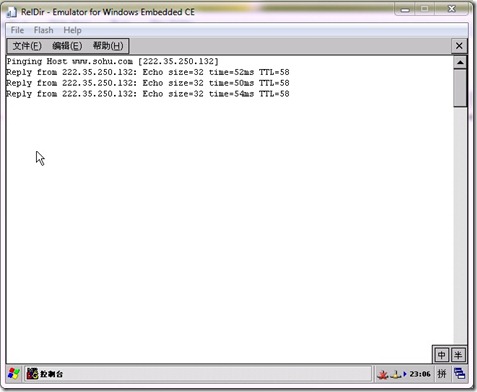
先运行ping命令,如果我们直接输入s ping x.x.x.x的话,会在模拟器中显示一个命令行窗口,并且输出执行结果。S的意思是在CE中运行某个应用程序。结果如下图:
不过问题随之而来,命令行窗口会在ping命令执行完成后,自动退出。我们想查看ping命令的执行情况,就需要眼疾手快了。难道,没有其他的办法了吗?
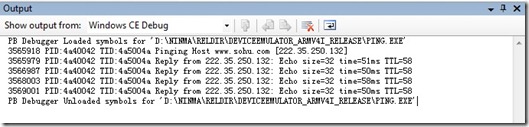
有,我们输入s ping x.x.x.x /d,执行结果会输出到output窗口中。
下面的演示我会将output里的结果贴出来,不再截图了。
ipconfig命令
接下来是另外一个简单的网络监测工具:ipconfig。在Command Shell中输入s ipconfig /all /d。/all 是ipconfig的命令,显示所有的配置信息,除此之外还有/renew和/release两个参数,用于更新网卡的IP地址。/d还是将结果显示到Output窗口中。
PB Debugger Loaded symbols for 'D:\NINMA\RELDIR\DEVICEEMULATOR_ARMV4I_RELEASE\IPCONFIG.EXE'
122396 PID:5860042 TID:5890056 Windows IP configuration
122465 PID:5860042 TID:5890056 Ethernet adapter Local Area Connection:
122465 PID:5860042 TID:5890056 IP Address ........ : 192.168.0.163
122465 PID:5860042 TID:5890056 Subnet Mask ....... : 255.255.255.0
122465 PID:5860042 TID:5890056 IP Address ........ : fe80::203:ffff:fe55:8d9f%5
122465 PID:5860042 TID:5890056 Default Gateway ... : 192.168.0.1
122465 PID:5860042 TID:5890056 Adapter Name ...... : NE20001
122465 PID:5860042 TID:5890056 Description ....... : NE20001
122465 PID:5860042 TID:5890056 Adapter Index ..... : 2
122465 PID:5860042 TID:5890056 Address............ : 00 03 ff 55 8d 9f
122465 PID:5860042 TID:5890056 DHCP Enabled....... : YES
122465 PID:5860042 TID:5890056 DHCP Server........ : 192.168.0.1
122465 PID:5860042 TID:5890056 Primary WinsServer :
122465 PID:5860042 TID:5890056 Secondary WinsServer:
122465 PID:5860042 TID:5890056 Lease obtained on : Sunday, July 5 ,2009 18 : 5 : 30
122465 PID:5860042 TID:5890056 Lease expires on : Sunday, July 12 ,2009 18 : 5 : 30
122465 PID:5860042 TID:5890056 AutoConfig Enabled : YES
122465 PID:5860042 TID:5890056
122465 PID:5860042 TID:5890056 Tunnel adapter []:
122467 PID:5860042 TID:5890056 Interface Number .. : 4
122467 PID:5860042 TID:5890056
122468 PID:5860042 TID:5890056 Tunnel adapter [6to4 Pseudo-Interface]:
122468 PID:5860042 TID:5890056 Interface Number .. : 3
122468 PID:5860042 TID:5890056
122469 PID:5860042 TID:5890056 Tunnel adapter [Automatic Tunneling Pseudo-Interface]:
122469 PID:5860042 TID:5890056 Interface Number .. : 2
122470 PID:5860042 TID:5890056 IP Address ........ : fe80::5efe:192.168.0.163%2
122470 PID:5860042 TID:5890056
122474 PID:5860042 TID:5890056 Host name.......... : WindowsCE
122474 PID:5860042 TID:5890056 Domain Name........ :
122474 PID:5860042 TID:5890056 DNS Servers........ : 62.244.19.19
122474 PID:5860042 TID:5890056 192.168.0.1
122474 PID:5860042 TID:5890056 NODETYPE........... : 8
122474 PID:5860042 TID:5890056 Routing Enabled.... : NO
122474 PID:5860042 TID:5890056 Proxy Enabled...... : NO
122474 PID:5860042 TID:5890056
PB Debugger Unloaded symbols for 'D:\NINMA\RELDIR\DEVICEEMULATOR_ARMV4I_RELEASE\IPCONFIG.EXE'
Netstat命令
接下来是netstat,显示网络当前的状态。输入s netstat -e /d,显示以太网的统计数据,比如发送和接收到的字节数等。
PB Debugger Loaded symbols for 'D:\NINMA\RELDIR\DEVICEEMULATOR_ARMV4I_RELEASE\WINSOCK.DLL'
273033 PID:5120022 TID:514005e
273035 PID:5120022 TID:514005e Interface Statistics Received Sent
273036 PID:5120022 TID:514005e Bytes 145754 14193
273036 PID:5120022 TID:514005e Unicast Packets 503 98
273036 PID:5120022 TID:514005e NonUnicast Packets 19 7
273036 PID:5120022 TID:514005e Discards 0 0
273037 PID:5120022 TID:514005e Errors 0 0
PB Debugger Unloaded symbols for 'D:\NINMA\RELDIR\DEVICEEMULATOR_ARMV4I_RELEASE\WINSOCK.DLL'
273037 PID:5120022 TID:514005e Unknown Protocols 0
273037 PID:5120022 TID:514005e Name =
273037 PID:5120022 TID:514005e Index =2
273037 PID:5120022 TID:514005e Physical Addrress =0003FF558D9F
273037 PID:5120022 TID:514005e Description =NE20001
273037 PID:5120022 TID:514005e Type =6
273037 PID:5120022 TID:514005e Mtu =1500
273037 PID:5120022 TID:514005e Speed - bps =10000000
273038 PID:5120022 TID:514005e Administrative Status =1
273038 PID:5120022 TID:514005e Oprerational Status =5
273038 PID:5120022 TID:514005e Output Queue Length =0
PB Debugger Unloaded symbols for 'D:\NINMA\RELDIR\DEVICEEMULATOR_ARMV4I_RELEASE\NETSTAT.EXE'
输入s s netstat -n /d,会显示当前活动的TCP连接,包括地址和端口号:
471308 PID:53a0062 TID:53b0062 GetTcpTable.
471308 PID:53a0062 TID:53b0062
471308 PID:53a0062 TID:53b0062 UDP TABLE
471308 PID:53a0062 TID:53b0062 Loc Addr Loc Port
471309 PID:53a0062 TID:53b0062 0.0.0.0 137
471309 PID:53a0062 TID:53b0062 0.0.0.0 138
输入s netstat -p tcp /d,会显示指定网络协议的信息,如下:
1998793 PID:5f0003e TID:460006e TCP Statistics:
1998793 PID:5f0003e TID:460006e --------------
1998793 PID:5f0003e TID:460006e Active Opens = 9
PB Debugger Unloaded symbols for 'D:\NINMA\RELDIR\DEVICEEMULATOR_ARMV4I_RELEASE\WINSOCK.DLL'
1998793 PID:5f0003e TID:460006e Passive Opens = 0
1998793 PID:5f0003e TID:460006e Connect Attempt Fails = 0
1998793 PID:5f0003e TID:460006e Reset Connections = 9
1998793 PID:5f0003e TID:460006e Current Connections = 0
1998793 PID:5f0003e TID:460006e Segments Received = 57
1998793 PID:5f0003e TID:460006e Segments Sent = 72
1998793 PID:5f0003e TID:460006e Segments Retransmitted = 2
1998793 PID:5f0003e TID:460006e Errors Received = 0
1998793 PID:5f0003e TID:460006e Sgmnts sent w/Reset Flag= 12
1998793 PID:5f0003e TID:460006e Cumulative Connections = 0
1998793 PID:5f0003e TID:460006e Time-Out Algorithm = 4
1998793 PID:5f0003e TID:460006e Time-Out Minimim = 300
1998793 PID:5f0003e TID:460006e Time-Out Maximum = 120000
1998793 PID:5f0003e TID:460006e Maximum Connections = Dynamic (-1)
-s选项显示各种协议的统计信息,比如IP, IPv6, ICMP, ICMPv6, TCP, TCPv6, UDP和UDPv6协议。-p可以和-s共同使用,用于显示某种协议的统计信息。
-r选项则显示路由表信息,与后边的route print命令类似。
Route命令
输入s route print /d,显示当前的路由表信息:
2379153 PID:4a5006a TID:4bb0076 =============================================================================
2379153 PID:4a5006a TID:4bb0076 Interface List
2379153 PID:4a5006a TID:4bb0076 0x2 00 03 ff 55 8d 9f NE20001
2379153 PID:4a5006a TID:4bb0076 =============================================================================
2379153 PID:4a5006a TID:4bb0076 =============================================================================
2379153 PID:4a5006a TID:4bb0076 Active Routes
PB Debugger Unloaded symbols for 'D:\NINMA\RELDIR\DEVICEEMULATOR_ARMV4I_RELEASE\WINSOCK.DLL'
2379153 PID:4a5006a TID:4bb0076 The no. of entries is ::: 7
2379153 PID:4a5006a TID:4bb0076 Destination Netmask GatewayAddress Interface Metric
2379153 PID:4a5006a TID:4bb0076 ----------------------------------------------------------------------------
2379153 PID:4a5006a TID:4bb0076 0.0.0.0 0.0.0.0 192.168.0.1 192.168.0.163 30
2379153 PID:4a5006a TID:4bb0076 127.0.0.0 255.0.0.0 127.0.0.1 127.0.0.1 1
2379153 PID:4a5006a TID:4bb0076 192.168.0.0 255.255.255.0 192.168.0.163 192.168.0.163 30
2379153 PID:4a5006a TID:4bb0076 192.168.0.163 255.255.255.255 127.0.0.1 127.0.0.1 30
2379153 PID:4a5006a TID:4bb0076 192.168.0.255 255.255.255.255 192.168.0.163 192.168.0.163 30
2379153 PID:4a5006a TID:4bb0076 224.0.0.0 240.0.0.0 192.168.0.163 192.168.0.163 30
2379153 PID:4a5006a TID:4bb0076 255.255.255.255 255.255.255.255 192.168.0.163 192.168.0.163 1
2379153 PID:4a5006a TID:4bb0076 =============================================================================
Route除了print命令外,还有Add和Delete命令。大家可以参考Route的帮助,我们就不多解释了。
Tracert命令
Tracert命令用于跟踪你的设备到某个IP地址的路由。输入s Tracert www.sohu.com –p,需要说明的是,Tracert结果输入到output的参数是-p。
Tracing route to www.sohu.com [222.35.250.135]
over a maximum of 30 hops:
2634835 PID:27002de TID:5650052 1
2634847 PID:27002de TID:5650052 5 ms
2634853 PID:27002de TID:5650052 6 ms
2634855 PID:27002de TID:5650052 1 ms
2635521 PID:27002de TID:5650052 192.168.0.1
2635521 PID:27002de TID:5650052
2636524 PID:27002de TID:5650052 2
2640537 PID:27002de TID:5650052 *
2640720 PID:27002de TID:5650052 179 ms
2640923 PID:27002de TID:5650052 203 ms
2641022 PID:27002de TID:5650052 222.35.*.*
2641022 PID:27002de TID:5650052
2641823 PID:27002de TID:5650052 3
2642038 PID:27002de TID:5650052 213 ms
2642241 PID:27002de TID:5650052 199 ms
2642444 PID:27002de TID:5650052 200 ms
2642543 PID:27002de TID:5650052 222.35.*.*
2642543 PID:27002de TID:5650052
2643345 PID:27002de TID:5650052 4
2643755 PID:27002de TID:5650052 406 ms
2643958 PID:27002de TID:5650052 202 ms
2644060 PID:27002de TID:5650052 102 ms
2644980 PID:27002de TID:5650052 222.35.*.*
2644981 PID:27002de TID:5650052
2645883 PID:27002de TID:5650052 5
2649895 PID:27002de TID:5650052 *
2650171 PID:27002de TID:5650052 273 ms
2650381 PID:27002de TID:5650052 205 ms
2656618 PID:27002de TID:5650052 222.35.*.*
Trace complete.
好了,对于Windows CE上的网络监测工具,我们就先介绍到这里。我们将在后边继续介绍另一个功能强大的网络检测工具——netlog。
更多关于Windows Embedded CE开发的文章,请参考“Windows Embedded CE 中国研发团队”的中文博客:http://blogs.msdn.com/wincechina/





 浙公网安备 33010602011771号
浙公网安备 33010602011771号