
实验需求:
1、按照图例配置防火墙接口及安全区域
2、FW启动源地址转换代理内部终端及服务器上网
3、PC和Server能ping通GW_Router
网卡桥接:

一、配置防火墙接口IP
interface GigabitEthernet1/0/0
ip address 172.16.10.1 255.255.255.0
#
interface GigabitEthernet1/0/1
ip address 10.168.10.1 255.255.255.0
#
interface GigabitEthernet1/0/2
ip address 202.100.10.1 255.255.255.0
二、创建防火墙安全区域并将接口添加到安全区域
firewall zone trust
add interface GigabitEthernet1/0/1
#
firewall zone untrust
add interface GigabitEthernet1/0/2
#
firewall zone dmz
add interface GigabitEthernet1/0/0
####[FW-GigabitEthernet1/0/1]service-manage all permit #要通过电脑web页面去管控防火墙,需要优先添加该命令,放行https的页面管理流量。
三、添加默认路由

四、创建安全策略
security-policy
rule name permit_trust_dmz
source-zone dmz
source-zone trust
destination-zone untrust
service icmp
action permit
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
页面配置

五、创建NAT策略
nat-policy
rule name nat
source-zone dmz
source-zone trust
destination-zone untrust
source-address 10.168.10.0 mask 255.255.255.0
action source-nat easy-ip
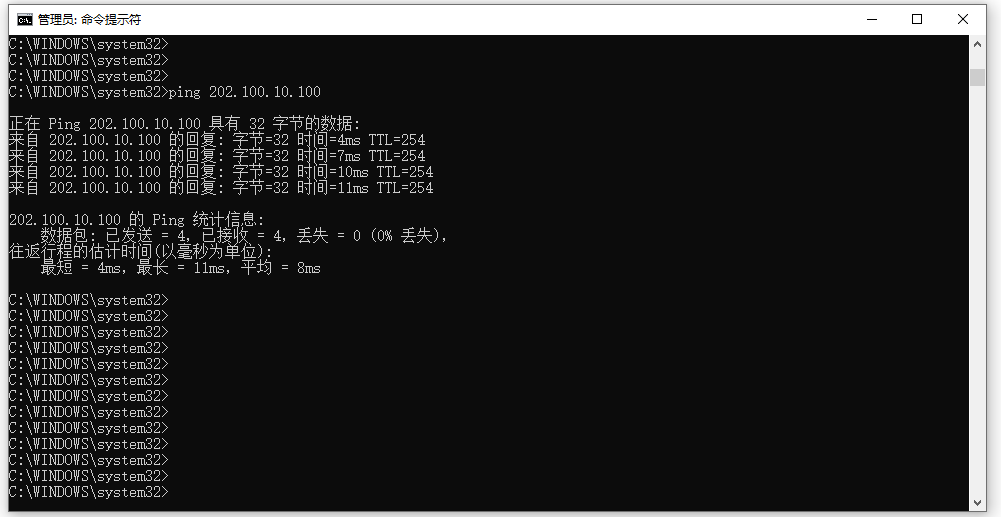
六、验证

[FW]display firewall session table
2022-12-21 09:03:23.110
Current Total Sessions : 5
tcp VPN: public --> public 10.168.10.100:6845 --> 10.168.10.1:8443
netbios-name VPN: public --> public 10.168.10.100:137 --> 10.168.10.255:137
tcp VPN: public --> public 10.168.10.100:6865 --> 10.168.10.1:8443
tcp VPN: public --> public 10.168.10.100:6864 --> 10.168.10.1:8443
icmp VPN: public --> public 10.168.10.100:1[202.100.10.1:2050] --> 202.100.10.100:2048


 浙公网安备 33010602011771号
浙公网安备 33010602011771号