Nginx——如何禁用TLSv1.0和TLSv1.1
前言
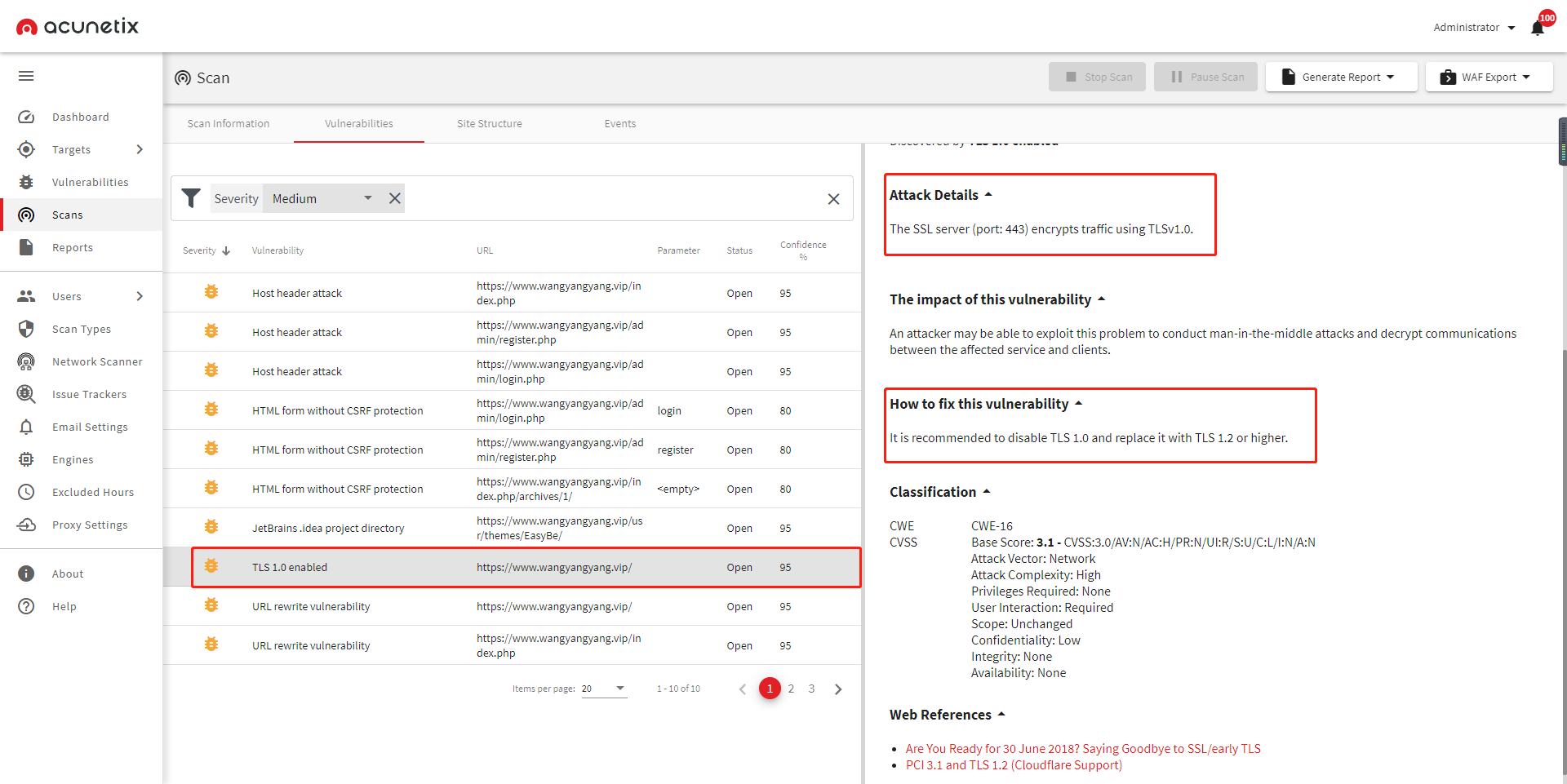
Web安扫提示Nginx使用了不安全的加密协议需要启用TLSv1.2或者更高的协议,但是修改后还是一直扫出了TLSv1.0和TLSV1.1,总结下原因;
工具1: http://s.tool.chinaz.com/https
工具2: https://infinisign.com/tools/sslcheck/?lang=cn
工具3: acunetix
内容
存在多个虚拟主机文件
针对存在多个虚拟主机文件的Nginx解析,每个虚拟主机文件都需要修改;
Nginx的openssl套件不支持

配置符合PFS规范的加密套件
ECDHE-RSA-AES128-GCM-SHA256:ECDHE:ECDH:AES:HIGH:!NULL:!aNULL:!MD5:!ADH:!RC4:!DH:!DHE
开启优先使用服务端加密套件
ssl_prefer_server_ciphers on;
配置示例
server {
listen 80;
listen [::]:80;
listen 443 ssl http2;
listen [::]:443 ssl http2;
ssl_certificate /usr/local/nginx/conf/ssl/www.wangyangyang.vip.pem;
ssl_certificate_key /usr/local/nginx/conf/ssl/www.wangyangyang.vip.key;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:ECDHE:ECDH:AES:HIGH:!NULL:!aNULL:!MD5:!ADH:!RC4;
ssl_prefer_server_ciphers on;
ssl_session_timeout 10m;
ssl_session_cache builtin:1000 shared:SSL:10m;
ssl_buffer_size 1400;
add_header Strict-Transport-Security max-age=15768000;
ssl_stapling on;
ssl_stapling_verify on;
server_name www.wangyangyang.vip;
access_log /data/wwwlogs/www.wangyangyang.vip_nginx.log combined;
index index.html index.htm index.php;
root /data/wwwroot/www.wangyangyang.vip/build;
if ($ssl_protocol = "") { return 301 https://$host$request_uri; }
include /usr/local/nginx/conf/rewrite/none.conf;
#error_page 404 /404.html;
#error_page 502 /502.html;
location ~ [^/]\.php(/|$) {
#fastcgi_pass remote_php_ip:9000;
fastcgi_pass unix:/dev/shm/php-cgi.sock;
fastcgi_index index.php;
include fastcgi.conf;
fastcgi_split_path_info ^(.+?\.php)(/.*)$;
}
location ~ .*\.(gif|jpg|jpeg|png|bmp|swf|flv|mp4|ico)$ {
expires 30d;
access_log off;
}
location ~ .*\.(js|css)?$ {
expires 7d;
access_log off;
}
location ~ /(\.user\.ini|\.ht|\.git|\.svn|\.project|LICENSE|README\.md) {
deny all;
}
}
提示
如果都设置了还不行,那就ping下域名看下对应的ip是否一致,不一致那就到对应的机器上进行修改;
学无止境,谦卑而行.


 浙公网安备 33010602011771号
浙公网安备 33010602011771号