Linux 利用Google Authenticator实现ssh登录双因素认证
1.介绍
双因素认证:双因素身份认证就是通过你所知道再加上你所能拥有的这二个要素组合到一起才能发挥作用的身份认证系统。双因素认证是一种采用时间同步技术的系统,采用了基于时间、事件和密钥三变量而产生的一次性密码来代替传统的静态密码。每个动态密码卡都有一个唯一的密钥,该密钥同时存放在服务器端,每次认证时动态密码卡与服务器分别根据同样的密钥,同样的随机参数(时间、事件)和同样的算法计算了认证的动态密码,从而确保密码的一致性,从而实现了用户的认证。因每次认证时的随机参数不同,所以每次产生的动态密码也不同。由于每次计算时参数的随机性保证了每次密码的不可预测性,从而在最基本的密码认证这一环节保证了系统的安全性。
说白了,就像我们几年前去银行办卡送的口令牌,以及网易游戏中的将军令,在你使用网银或登陆游戏时会再让你输入动态口令的。
2.目的
实现登录Linux 服务器时,除了输入用户名密码外,需要输入一次性的动态口令才能验证成功。
3.安装过程
3.1安装chrony
生成动态口令的其中一个因素是时间,需要保持终端设备和服务器的系统时间一致,才能生成同一的动态口令
简单说下chrony:chrony 是网络时间协议的(NTP)的另一种实现,与网络时间协议后台程序(ntpd)不同,它可以更快地更准确地同步系统始终。
国内比较好用的ntp服务器:官网
注,同步时间时请准确设置系统时区
[root@localhost ~]# yum install -y chrony [root@localhost ~]# vim /etc/chrony.conf server 0.cn.pool.ntp.org iburst [root@localhost ~]# systemctl restart chronyd [root@localhost ~]# chronyc sources 210 Number of sources = 4 MS Name/IP address Stratum Poll Reach LastRx Last sample =============================================================================== ^? 223.112.179.133 0 6 0 10y +0ns[ +0ns] +/- 0ns ^* dns1.synet.edu.cn 2 6 33 0 +113us[ +284us] +/- 28ms ^? 2001:da8:202:10::61 0 6 0 10y +0ns[ +0ns] +/- 0ns ^? 42.96.167.209 2 6 10 8 +2011us[ +949us] +/- 127ms [root@localhost ~]# date 2016年 12月 31日 星期六 09:30:24 CST
3.2安装依赖组件
[root@localhost ~]# yum install -y git automake libtool pam-devel
3.3下载谷歌认证模块
[root@localhost ~]# git clone https://github.com/google/google-authenticator-libpam.git [root@localhost ~]# ll drwxr-xr-x 11 root root 4096 12月 27 16:29 google-authenticator-libpam [root@localhost ~]# cd google-authenticator-libpam/ [root@localhost google-authenticator-libpam]# ./bootstrap.sh [root@localhost google-authenticator-libpam]# ./configure [root@localhost google-authenticator-libpam]# make && make install [root@localhost google-authenticator-libpam]# google-authenticator [root@localhost google-authenticator-libpam]# cd ~ [root@localhost ~]# vim /etc/pam.d/sshd auth required pam_google_authenticator.so no_increment_hotp [root@localhost ~]# vim /etc/ssh/sshd_config asswordAuthentication yes ChallengeResponseAuthentication yes UsePAM yes [root@localhost ~]# systemctl restart sshd [root@localhost ~]# google-authenticator Do you want authentication tokens to be time-based (y/n) y
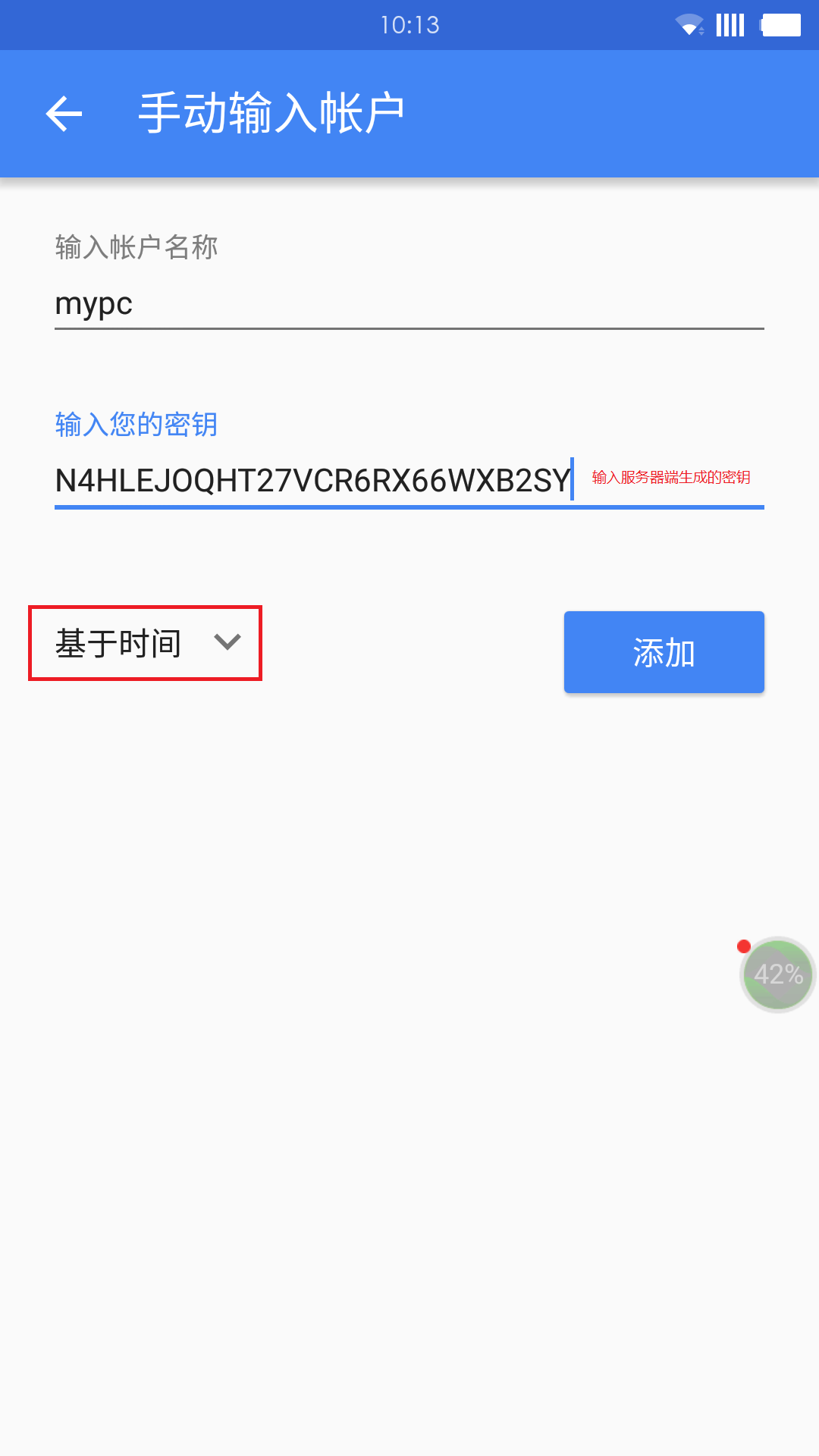
#你想做的认证令牌是基于时间的吗? Warning: pasting the following URL into your browser exposes the OTP secret to Google: https://www.google.com/chart?chs=200x200&chld=M|0&cht=qr&chl=otpauth://totp/root@localhost.localdomain%3Fsecret%3DN4HLEJOQHT27VCR6RX66WXB2SY%26issuer%3Dlocalhost.localdomain
Your new secret key is: N4HLEJOQHT27VCR6RX66WXB2SY Your verification code is 299695 Your emergency scratch codes are: 44477086 92790948 29251218 26350870 30696065 Do you want me to update your "/root/.google_authenticator" file? (y/n) y
#你希望我更新你的“/root/.google_authenticator”文件吗(y/n)? Do you want to disallow multiple uses of the same authentication token? This restricts you to one login about every 30s, but it increases
your chances to notice or even prevent man-in-the-middle attacks (y/n) y
#你希望禁止多次使用同一个验证令牌吗?这限制你每次登录的时间大约是30秒, 但是这加大了发现或甚至防止中间人攻击的可能性(y/n)? By default, a new token is generated every 30 seconds by the mobile app. In order to compensate for possible time-skew between the client and the server, we allow an extra token before and after the current time. This allows for a time skew of up to 30 seconds between authentication server and client. If you experience problems with poor time synchronization, you can increase the window from its default size of 3 permitted codes (one previous code, the current code, the next code) to 17 permitted codes (the 8 previous codes, the current code, and the 8 next codes). This will permit for a time skew of up to 4 minutes between client and server. Do you want to do so? (y/n) y
#默认情况下,令牌保持30秒有效;为了补偿客户机与服务器之间可能存在的时滞,
我们允许在当前时间前后有一个额外令牌。如果你在时间同步方面遇到了问题, 可以增加窗口从默认的3个可通过验证码增加到17个可通过验证码,
这将允许客户机与服务器之间的时差增加到4分钟。你希望这么做吗(y/n)? If the computer that you are logging into isn't hardened against brute-force login attempts, you can enable rate-limiting for the authentication module. By default, this limits attackers to no more than 3 login attempts every 30s. Do you want to enable rate-limiting? (y/n) y
#如果你登录的那台计算机没有经过固化,以防范运用蛮力的登录企图,可以对验证模块
启用尝试次数限制。默认情况下,这限制攻击者每30秒试图登录的次数只有3次。 你希望启用尝试次数限制吗(y/n)?
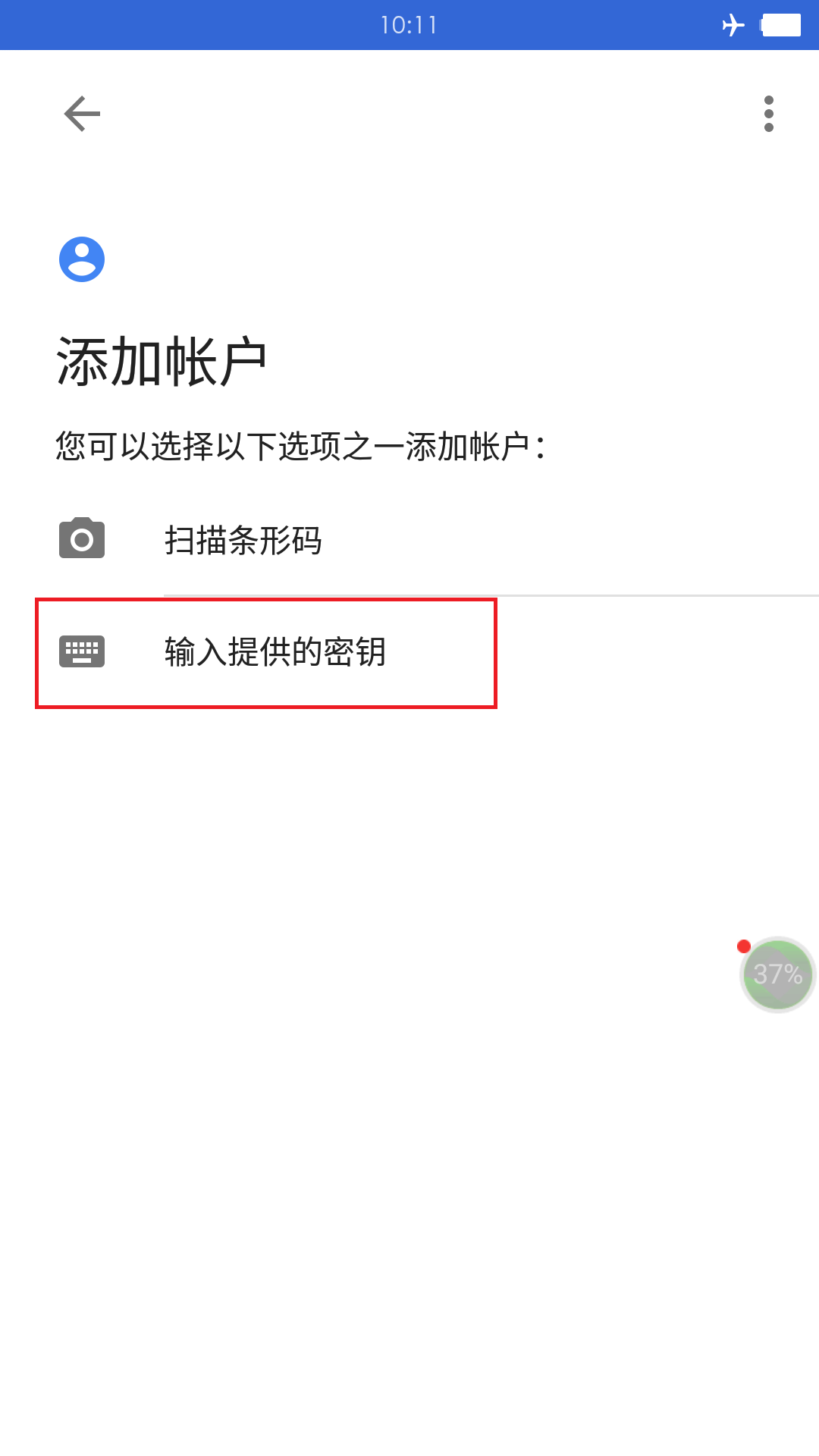
3.4 手机安装身份验证器
app下载地址:http://www.coolapk.com/apk/com.google.android.apps.authenticator2

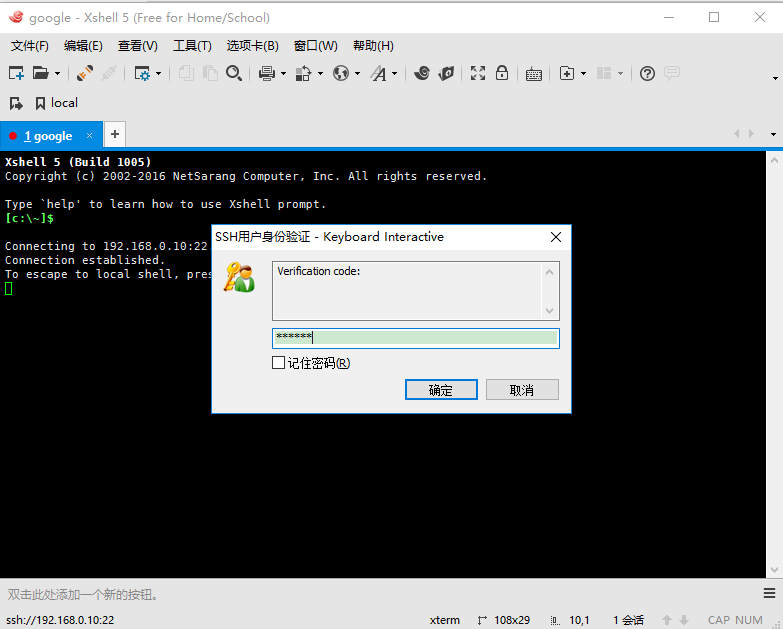
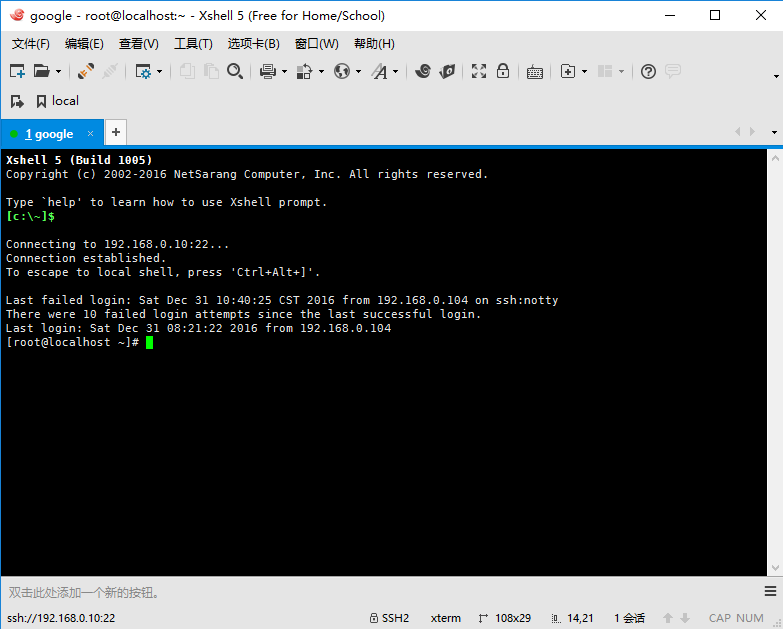
4.登录验证
注意,第一次登录可能会出现登录失败的情况,查看日志信息显示错误如下:
[root@localhost ~]# tail -n10 /var/log/secure ... Dec 31 09:42:46 localhost sshd[2393]: PAM unable to dlopen(/usr/lib64/security/pam_google_authenticator.so): /usr/lib64/security/pam_google_authenticator.so: cannot open shared object file: No such file or directory Dec 31 09:42:46 localhost sshd[2393]: PAM adding faulty module: /usr/lib64/security/pam_google_authenticator.so ... [root@localhost ~]# ln -sv /usr/local/lib/security/pam_google_authenticator.so /usr/lib64/security/pam_google_authenticator.so "/usr/lib64/security/pam_google_authenticator.so" -> "/usr/local/lib/security/pam_google_authenticator.so"
开始再次登录
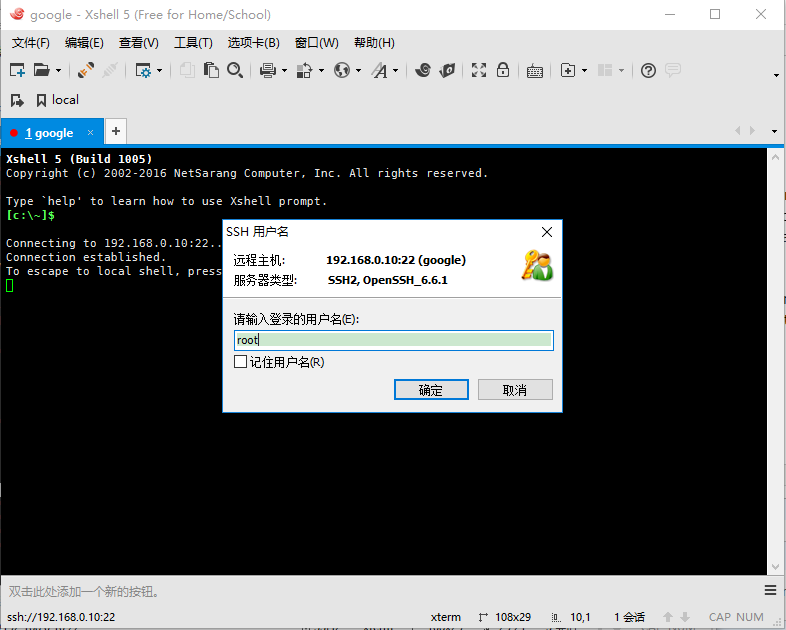
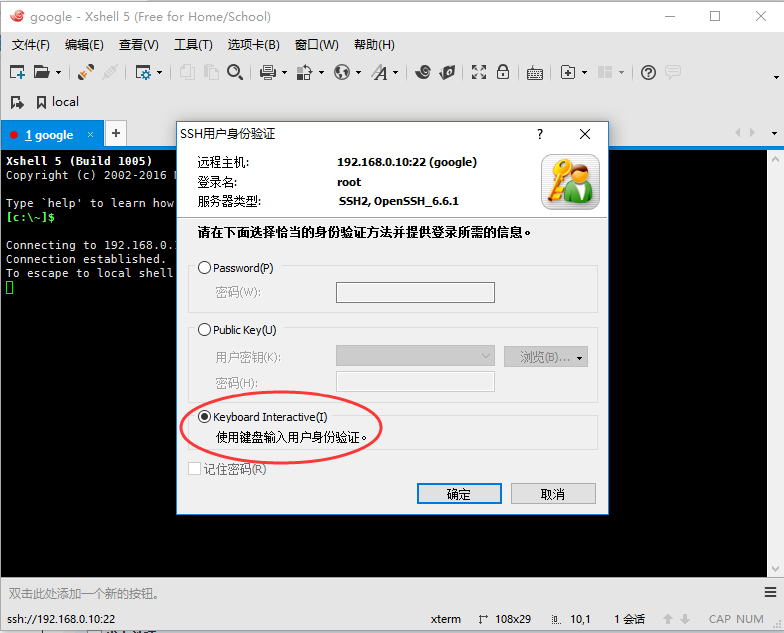

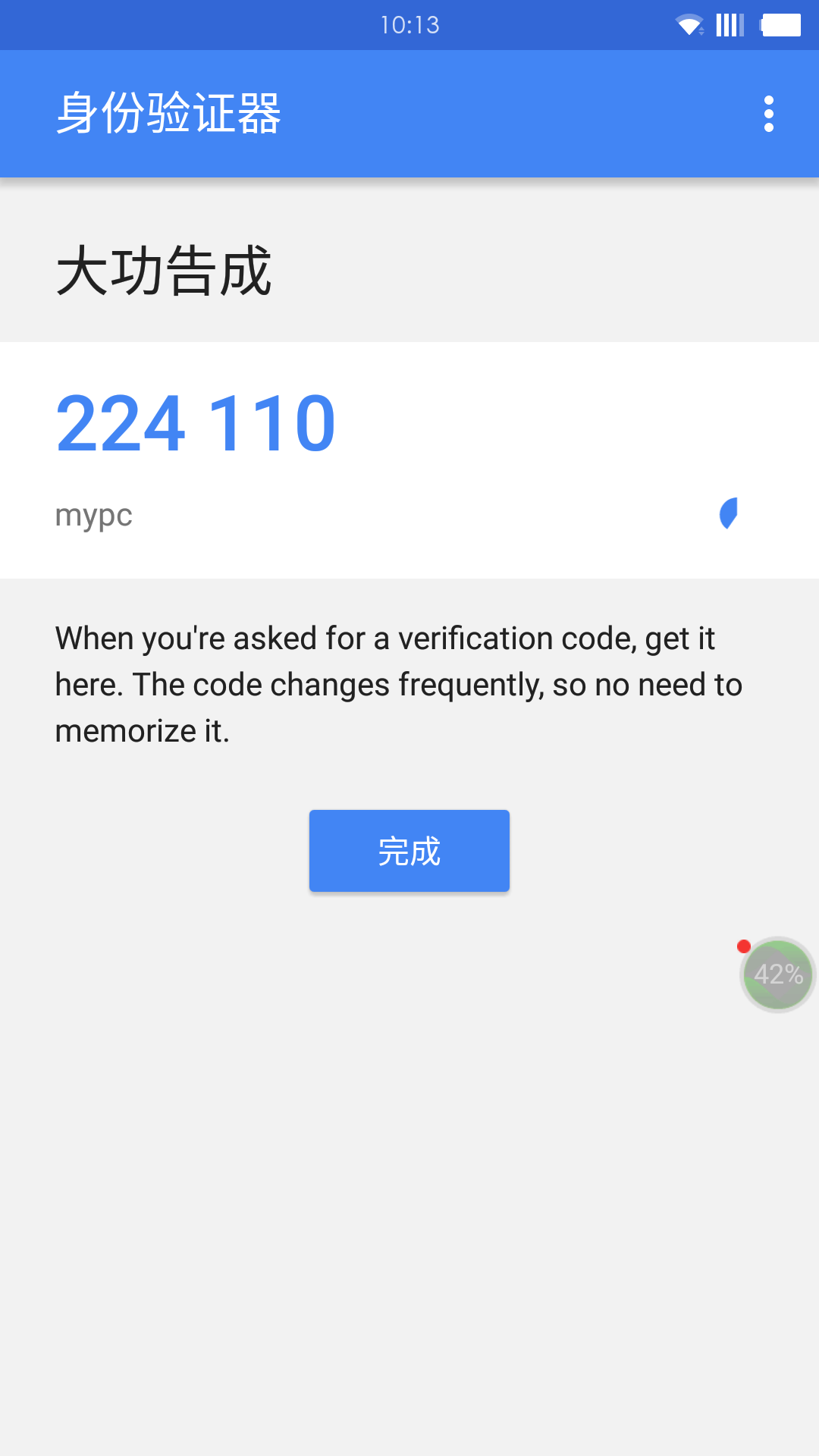
到了激动人心的时刻了,从手机app中获取此刻验证码为077625,在Verification code里面输入,如下:


 浙公网安备 33010602011771号
浙公网安备 33010602011771号