[PHP]用PHP自己写一个基于zoomeye的api(偷懒必备quq)
0x01 起因

因为手速慢,漏洞刷不过别人,一个个手补确实慢,所以想自己写一个api,一键抓取zoomeye的20页,然后就可以打批量了 ovo(真是太妙了!)
0x02 动工
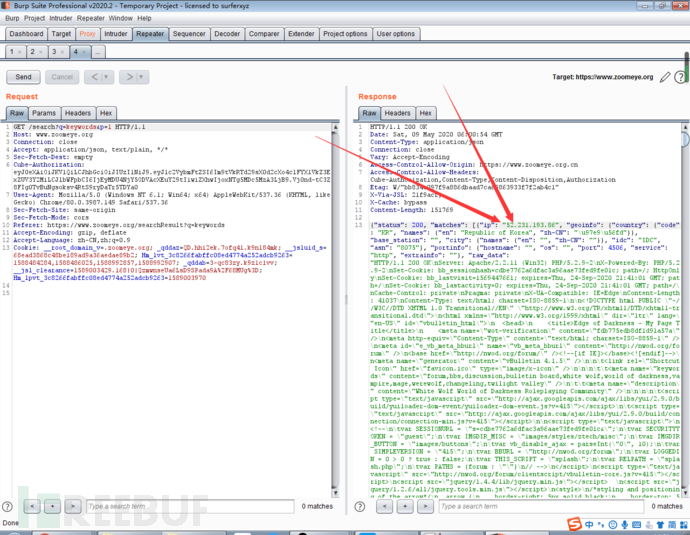
1.抓包做准备
要做一个抓取的,当然是先抓包啦~
拿出我的bp~
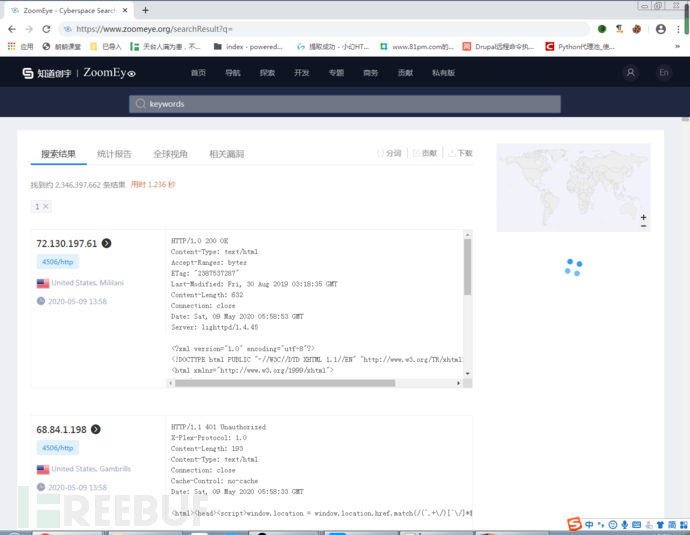 先输入一个关键字,方便在bp里面找我输入的关键字
先输入一个关键字,方便在bp里面找我输入的关键字
然后回车~
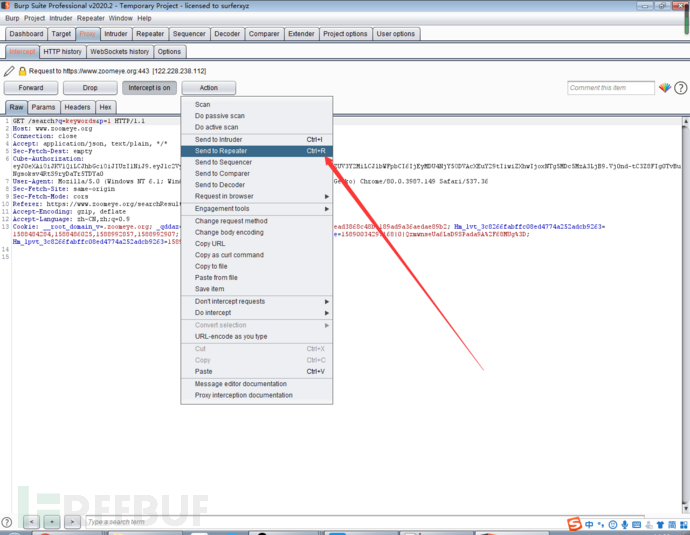
 发现我输入的关键字在这个GET的请求包里面,但是他到底是不是呢?
发现我输入的关键字在这个GET的请求包里面,但是他到底是不是呢?
发送到repeat模块看看呗

2.使用php的curl来模拟访问
PHP支持的由Daniel Stenberg创建的libcurl库允许你与各种的服务器使用各种类型的协议进行连接和通讯。
libcurl目前支持http、https、ftp、gopher、telnet、dict、file和ldap协议。libcurl同时也支持HTTPS认证、HTTP POST、HTTP PUT、 FTP 上传(这个也能通过PHP的FTP扩展完成)、HTTP 基于表单的上传、代理、cookies和用户名+密码的认证。
PHP中使用cURL实现Get和Post请求的方法
这些函数在PHP 4.0.2中被引入。
就是说,在php4.0.2中就已经引入了curl,而且还可以做post和get,真是太有用了有木有
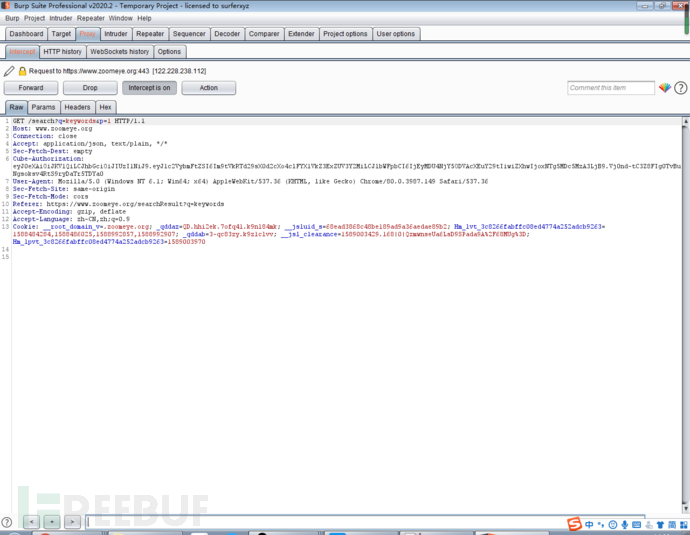
拿出我刚刚记录好的请求包~
GET /search?q=keywords&p=1 HTTP/1.1
Host: www.zoomeye.org
Connection: close
Accept: application/json, text/plain, */*
Sec-Fetch-Dest: empty
Cube-Authorization: eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1c2VybmFtZSI6I**tVkRTd29sX0d2cXo4clFYX1VkZ3ExZUV3Y2MiLCJlbWFpbCI6IjEyMDU4NjY5ODVAcXEuY29tIiwiZXhwIjoxNTg5MDc5MzA3LjB9.Vj0nd-tC3Z8FIg0TvBuNgsoksv4RtS9ryDaTr5TDYa0
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Referer: https://www.zoomeye.org/searchResult?q=keywords
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: __root_domain_v=.zoomeye.org; _qddaz=QD.hhi2ek.7ofq41.k9nl84mk; __jsluid_s=68ead3868c48be189ad9a36aedae89b2; Hm_lvt_3c8266fabffc08ed4774a252adcb9263=1588484284,1588486025,1588992857,1588992907; _qddab=3-qc83zy.k9z1clvv; __jsl_clearance=1589003429.168|0|QzmwnseUa6LsD9SPada9A%2F68MUg%3D; Hm_lpvt_3c8266fabffc08ed4774a252adcb9263=1589003970
然后用php语言来描述他:
<?php
function curl_post($url) {
/*-----------------SET COOKIE-------*/
$cookies=' __root_domain_v=.zoomeye.org; _qddaz=QD.hhi2ek.7ofq41.k9nl84mk; __jsluid_s=68ead3868c48be189ad9a36aedae89b2; Hm_lvt_3c8266fabffc08ed4774a252adcb9263=1588484284,1588486025,1588992857,1588992907; _qddab=3-qc83zy.k9z1clvv; __jsl_clearance=1588999664.016|0|HlMEMiGt3peQ%2FyF5pwOoAVi7Hhg%3D; Hm_lpvt_3c8266fabffc08ed4774a252adcb9263=1588999939';
/*-----------------SET COOKIE---------*/
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_SSL_VERIFYPEER, false);
curl_setopt($ch, CURLOPT_SSL_VERIFYHOST, false);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($ch, CURLOPT_HEADER, TRUE);
$headers = array();
$headers[] = 'Host:www.zoomeye.org';
$headers[] = 'Connection: close';
$headers[] = 'Accept: application/json, text/plain, */*';
$headers[] = 'Sec-Fetch-Dest: empty';
/**/
$headers[] = 'Cube-Authorization: eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1c2VybmFtZSI6I**tVkRTd29sX0d2cXo4clFYX1VkZ3ExZUV3Y2MiLCJlbWFpbCI6IjEyMDU4NjY5ODVAcXEuY29tIiwiZXhwIjoxNTg5MDc5MzA3LjB9.Vj0nd-tC3Z8FIg0TvBuNgsoksv4RtS9ryDaTr5TDYa0';
$headers[] = 'User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36';
$headers[] = 'Sec-Fetch-Site: same-origin';
$headers[] = 'Sec-Fetch-Mode: cors';
$headers[] = 'Referer: https://www.zoomeye.org/searchResult?q=%22Office%20Anywhere%202017%22';
$headers[] = 'Accept-Language: zh-CN,zh;q=0.9';
$headers[] = 'Cookie: '.$cookies;
$headers[] = 'If-None-Match: W/"3828048cfa646c65b99b190eb8c4418ee44f4da2"';
curl_setopt($ch, CURLOPT_HTTPHEADER, $headers);
$output= curl_exec($ch);
curl_close($ch);
return $output;
}
$a=curl_post('https://www.zoomeye.org/search?q=keywords&p=1');
vardump($a);
?>这样子就可以完成一次php中curl对zoomeye的请求了
curl_setopt($ch, CURLOPT_URL, $url);这句是设定请求的url
curl_setopt($ch, CURLOPT_SSL_VERIFYPEER, false);
curl_setopt($ch, CURLOPT_SSL_VERIFYHOST, false);这两句是忽略ssl证书
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);这句是确定返回形式 差不多就是0为直接打印屏幕,1为返回到具体变量里面
curl_setopt($ch, CURLOPT_HEADER, TRUE);保留head
最后就会把返回值$a打印在屏幕上了
来看看效果
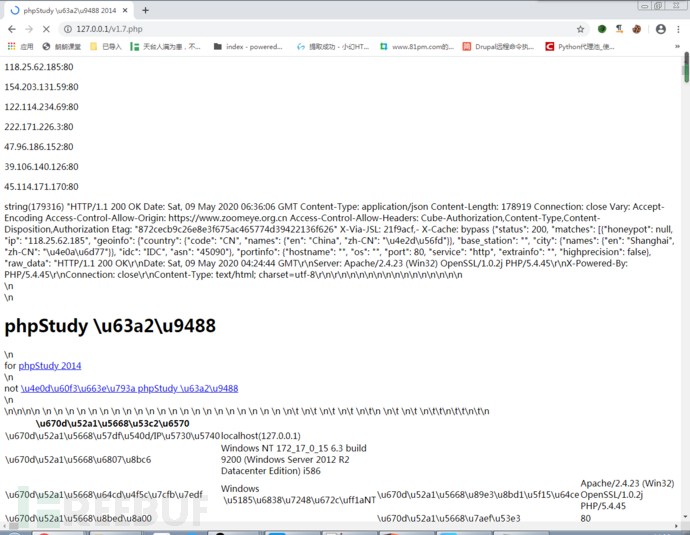
 可能有的小伙伴会问 可是返回的是这个啊
可能有的小伙伴会问 可是返回的是这个啊

别急啊,右键去看看源代码
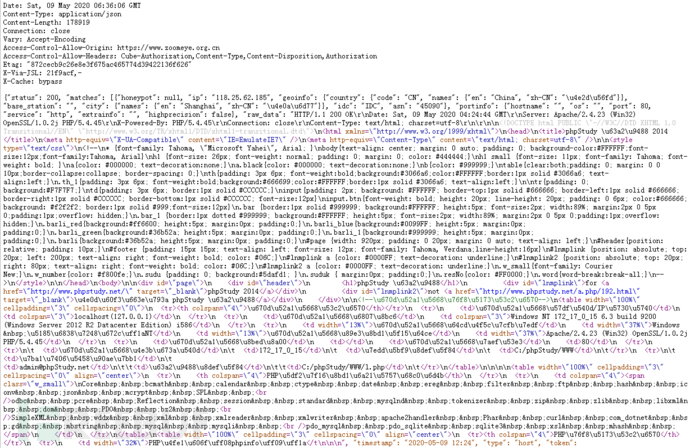 这时候就和之前的用bp的返回的值一模一样了
这时候就和之前的用bp的返回的值一模一样了
只要取出ip +port就行了 大功告成
这里有两种方法:
1.先从请求包里面取出json数组进行解析
2.直接用正则全局匹配
我用的是第二种方法
因为我这边json解析老是出问题,所以用了正则:
$pattern = '/"ip": "(.*?)"(.*?)", "geoinfo(.*?)/i';
preg_match_all($pattern, $a, $match);
这样子就能把之前的a中的ip取出来了
然后只要再取一次port,把两个进行拼接就行了
$patternone = '/"port":(.*?)(.*?), "service"(.*?)/i';
preg_match_all($patternone, $a, $match1);
但是其实这样子取出来的,还是port":xxx ,"service"的形式,所以用取文本的函数进行二次过滤:
function getSubstr($str, $leftStr, $rightStr) {
$left = strpos($str, $leftStr);
$right = strpos($str, $rightStr,$left);
if($left < 0 or $right < $left) return '';
return substr($str, $left + strlen($leftStr), $right-$left-strlen($leftStr));
}然后只要getSunstr取出来就行了,但是正则以后的数据是存放在match数组里面的,所以用for循环来循环取出放到新数组port里面
for ($i=0;$i<=count($match1[0]);$i++) {
$port[$i]=getSubstr($match1[0][$i],'"port": ',', "service');
}
然后进行拼接:
for ($i=0;$i<=$ccc;$i++) {
$url[$i]=$match[1][$i];
if(checkIp($url[$i])) {
echo addslashes($url[$i].':'.$port[$i].'</p>');
}
}
checkip是检查ip那个数组的ip合法性
不然会有奇怪的东西跟进来

0x03所以完整代码如下:
<?php
function getSubstr($str, $leftStr, $rightStr) {
$left = strpos($str, $leftStr);
$right = strpos($str, $rightStr,$left);
if($left < 0 or $right < $left) return '';
return substr($str, $left + strlen($leftStr), $right-$left-strlen($leftStr));
}
function checkIp($ip) {
$arr = explode('.',$ip);
if(count($arr) != 4) {
return false;
} else {
for ($i = 0;$i < 4;$i++) {
if(($arr[$i] <'0') || ($arr[$i] > '255')) {
return false;
}
}
}
return true;
}
function curl_post($url) {
/*-----------------SET COOKIE-------*/
$cookies=' __root_domain_v=.zoomeye.org; _qddaz=QD.hhi2ek.7ofq41.k9nl84mk; __jsluid_s=68ead3868c48be189ad9a36aedae89b2; Hm_lvt_3c8266fabffc08ed4774a252adcb9263=1588484284,1588486025,1588992857,1588992907; _qddab=3-qc83zy.k9z1clvv; __jsl_clearance=1588999664.016|0|HlMEMiGt3peQ%2FyF5pwOoAVi7Hhg%3D; Hm_lpvt_3c8266fabffc08ed4774a252adcb9263=1588999939';
/*-----------------SET COOKIE---------*/
/*---------------set ca-------------*/
$ca='eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1c2VybmFtZSI6I**tVkRTd29sX0d2cXo4clFYX1VkZ3ExZUV3Y2MiLCJlbWFpbCI6IjEyMDU4NjY5ODVAcXEuY29tIiwiZXhwIjoxNTg5MDc5MzA3LjB9.Vj0nd-tC3Z8FIg0TvBuNgsoksv4RtS9ryDaTr5TDYa0';
/*----------------end ---set-------------*/
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_SSL_VERIFYPEER, false);
curl_setopt($ch, CURLOPT_SSL_VERIFYHOST, false);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($ch, CURLOPT_HEADER, TRUE);
$headers = array();
$headers[] = 'Host:www.zoomeye.org';
$headers[] = 'Connection: close';
$headers[] = 'Accept: application/json, text/plain, */*';
$headers[] = 'Sec-Fetch-Dest: empty';
/**/
$headers[] = 'Cube-Authorization: '.$ca;
$headers[] = 'User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36';
$headers[] = 'Sec-Fetch-Site: same-origin';
$headers[] = 'Sec-Fetch-Mode: cors';
$headers[] = 'Referer: https://www.zoomeye.org/searchResult?q=%22Office%20Anywhere%202017%22';
$headers[] = 'Accept-Language: zh-CN,zh;q=0.9';
$headers[] = 'Cookie: '.$cookies;
$headers[] = 'If-None-Match: W/"3828048cfa646c65b99b190eb8c4418ee44f4da2"';
curl_setopt($ch, CURLOPT_HTTPHEADER, $headers);
$output= curl_exec($ch);
curl_close($ch);
return $output;
}
function get($page) {
$flag=false;
/*----------------SET KEYWORDS-------------*/
$keywords='"phpStudy%20探针%202014%20"';
/*-----------------\SET KEY WORDS!/-------------*/
$store=array();
$a=curl_post('https://www.zoomeye.org/search?q='.$keywords.'&p='.$page);
$status=getSubstr($a,'{"status": ',', "matches"');
if ($status!=200) {
echo $status.'</p>'.'爬取频繁或cookie过期,请重新回到zoomeye输入验证码/重新获取cookie后继续爬取:<a href="https://www.zoomeye.org/searchResult?q='.$keywords.'">回到zoomeye</a>'.PHP_EOL;
return true;
} else {
$pattern = '/"ip": "(.*?)"(.*?)", "geoinfo(.*?)/i';
preg_match_all($pattern, $a, $match);
$patternone = '/"port":(.*?)(.*?), "service"(.*?)/i';
preg_match_all($patternone, $a, $match1);
$port=array();
for ($i=0;$i<=count($match1[0]);$i++) {
$port[$i]=getSubstr($match1[0][$i],'"port": ',', "service');
}
$ccc=count($match[1]);
for ($i=0;$i<=$ccc;$i++) {
$url[$i]=$match[1][$i];
if(checkIp($url[$i])) {
echo addslashes($url[$i].':'.$port[$i].'</p>');
}
}
}
}
for ($i=1;$i<=20;$i++) {
sleep(2);
$flag=get($i);
if($flag) {
break;
}
}
?>
keywords,cookies,Cube-Authorization都要根据自己的zoomeye的请求包修改,因为我太菜了,不会做
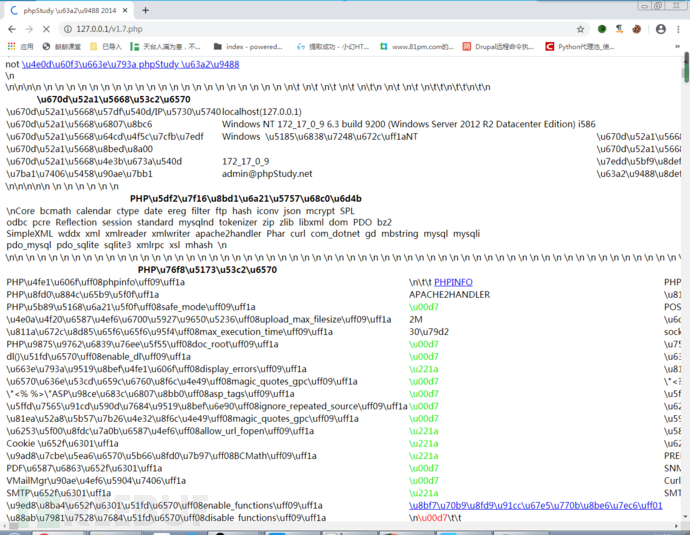
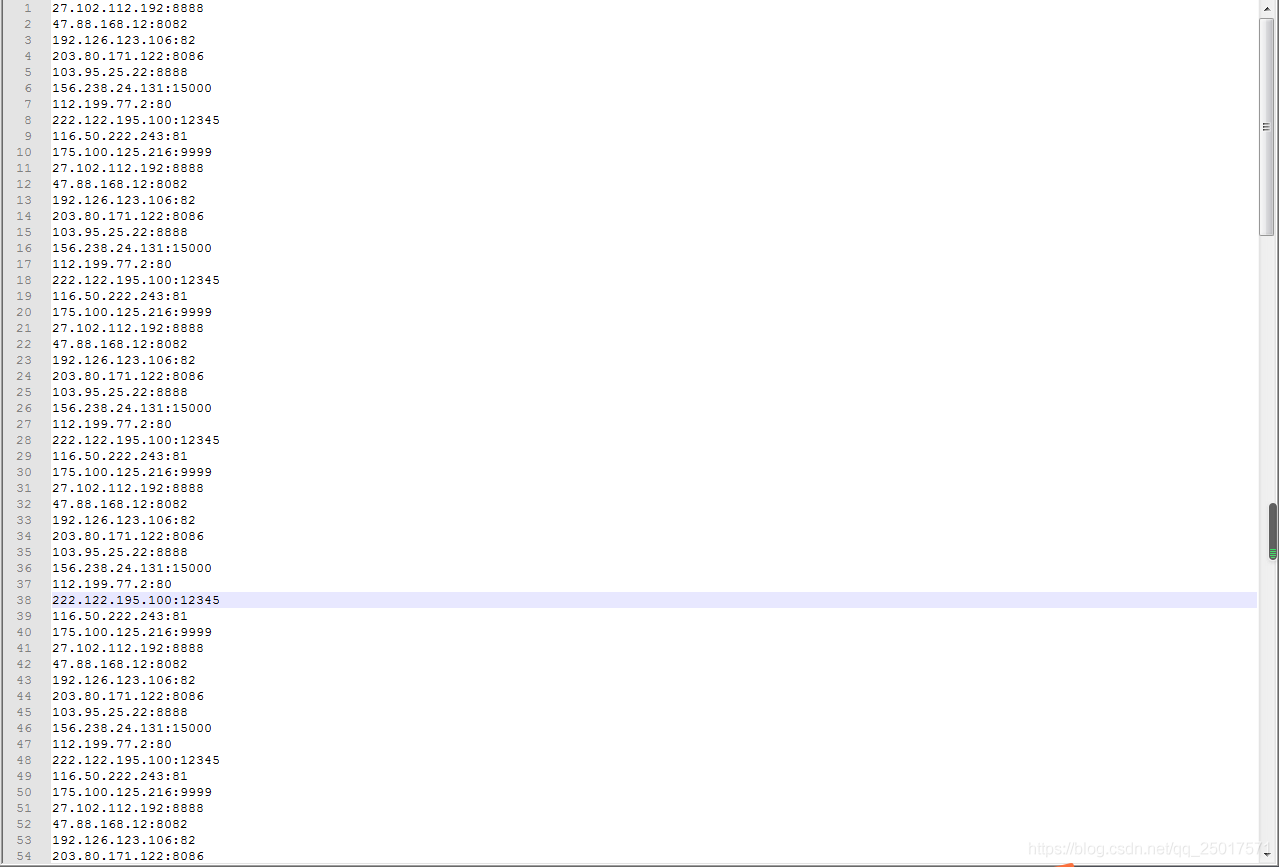
最后附上成果:


 浙公网安备 33010602011771号
浙公网安备 33010602011771号