快速了解常用的非对称加密算法,再也不用担心面试官的刨根问底
面试官:说一说你常用的加密算法有哪些?
加密算法通常被分为两种:对称加密算法和非对称加密算法。其中,对称加密算法在加密和解密时使用的密钥相同;非对称加密算法在加密和解密时使用的密钥不同,分为公钥和私钥。此外,还有一类叫做消息摘要算法,是对数据进行摘要并且不可逆的算法。
这次我们了解一下非对称加密算法。
非对称加密算法
非对称加密算法在加密和解密时使用两个不同的密钥,其中一个可以公开的密钥被称为公钥,另外一个完全保密的密钥被称为私钥。只有同一个公钥私钥对才能正常加密和解密。
对于同一个公钥私钥对,如果使用公钥对数据进行加密,只有用对应的私钥才能进行解密;如果使用私钥对数据进行加密,只有用对应的公钥才能进行解密。
常见的非对称加密算法有:RSA算法、DSA。
RSA算法
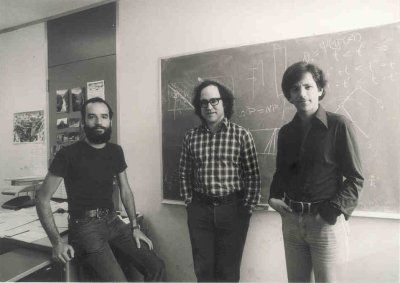
RSA算法是目前最有影响力的公钥加密算法,它由Ron Rivest、Adi Shamir和Leonard Adleman三位大佬在1977年麻省理工学院工作时一起提出的,RSA就是他们三人姓氏开头字母拼在一起组成的。
另外,1973年,在英国政府通讯总部工作的数学家Clifford Cocks在一个内部文件中提出了一个与之等效的算法,但该算法被列入机密,直到1997年才得到公开。
RSA算法利用了两个数论特性:
- p1、p2为两个质数, n=p1 * p2。已知p1、p2求n简单,已知n求p1、p2很难。
- (m^e) mod n=c,已知m、e、n求c简单,已知e、n、c求m很难。
公钥私钥生成过程:随机选取两个质数p1、p2,n=p1 * p2,再随机选取一个与φ(n)互质且小于φ(n)的整数e,然后再计算e对于φ(n)的模反元素d,最后得到n和e为公钥,n和d为私钥。
加密过程:(m^e) mod n = c,其中m为明文,c为密文,n和e为公钥。
解密过程:(c^d) mod n = m,其中m为明文,c为密文,n和d为私钥。
我们用Java写个例子:
import javax.crypto.Cipher;
import java.nio.charset.Charset;
import java.nio.charset.StandardCharsets;
import java.security.GeneralSecurityException;
import java.security.KeyFactory;
import java.security.KeyPair;
import java.security.KeyPairGenerator;
import java.security.PrivateKey;
import java.security.PublicKey;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.X509EncodedKeySpec;
import java.util.Base64;
public class RsaUtil {
private static final String RSA = "RSA";
private static final Charset CHARSET = StandardCharsets.UTF_8;
/**
* 加密
*
* @param input 明文
* @param publicKey 公钥
* @return 密文
* @throws GeneralSecurityException
*/
public static String encrypt(String input, String publicKey) throws GeneralSecurityException {
Cipher cipher = Cipher.getInstance(RSA);
PublicKey pubKey = KeyFactory.getInstance(RSA)
.generatePublic(new X509EncodedKeySpec(Base64.getDecoder().decode(publicKey)));
cipher.init(Cipher.ENCRYPT_MODE, pubKey);
byte[] data = cipher.doFinal(input.getBytes(CHARSET));
return Base64.getEncoder().encodeToString(data);
}
/**
* 解密
*
* @param input 密文
* @param privateKey 私钥
* @return 明文
* @throws GeneralSecurityException
*/
public static String decrypt(String input, String privateKey) throws GeneralSecurityException {
Cipher cipher = Cipher.getInstance(RSA);
PrivateKey priKey = KeyFactory.getInstance("RSA")
.generatePrivate(new PKCS8EncodedKeySpec(Base64.getDecoder().decode(privateKey)));
cipher.init(Cipher.DECRYPT_MODE, priKey);
byte[] data = cipher.doFinal(Base64.getDecoder().decode(input));
return new String(data, CHARSET);
}
public static void main(String[] args) throws GeneralSecurityException {
// 生成公钥/私钥对:
KeyPairGenerator kpGen = KeyPairGenerator.getInstance(RSA);
kpGen.initialize(1024);
KeyPair keyPair = kpGen.generateKeyPair();
String publicKey = Base64.getEncoder().encodeToString(keyPair.getPublic().getEncoded());
String privateKey = Base64.getEncoder().encodeToString(keyPair.getPrivate().getEncoded());
System.out.println("公钥:" + publicKey);
System.out.println("私钥:" + privateKey);
String msg = "我喜欢你,可以做我女朋友吗?";
System.out.println("加密前:" + msg);
String pwd = RsaUtil.encrypt(msg, publicKey);
System.out.println("加密后:" + pwd);
System.out.println("解密后:" + RsaUtil.decrypt(pwd, privateKey));
}
}
运行结果如下:
公钥:MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDd4brSm8gdJqFi04m3aW8kjVYbd/T4ymyc7l3c2WmwOhVPlZO1eaZJpTvas61rW0HPf267CRIhc52Zp2+e1hoknApvT0gKeRkfSwC5aws/yoT2vZ9J627QbCFkFc8mmfP8LJ5V/rCpmUE12dIW4xVlEYtWPzmNK2iTMzuR99Jq9wIDAQAB
私钥:MIICeAIBADANBgkqhkiG9w0BAQEFAASCAmIwggJeAgEAAoGBAN3hutKbyB0moWLTibdpbySNVht39PjKbJzuXdzZabA6FU+Vk7V5pkmlO9qzrWtbQc9/brsJEiFznZmnb57WGiScCm9PSAp5GR9LALlrCz/KhPa9n0nrbtBsIWQVzyaZ8/wsnlX+sKmZQTXZ0hbjFWURi1Y/OY0raJMzO5H30mr3AgMBAAECgYEAuxPtKlAwzOtaXXIQhrV+AWqttGFTCkXaiAKu31vssap3d2+daACWxTdtHPwr9v2tol9GpKqEP/I0am5zPZA13x+tv068x2TxGf8ZEbp579CKE3NrzTrnhtJN31TT82HIJoJ0TsNUhHbwZPWVAsq98afSCP1rn5RY/kwJ6bzsjhECQQD8Ev044KaUdWd0WZoomMP+5tATUL0HTMmUiBEvrXjOWG2mjuD4M5n/9C11FZWFg+o75riAUiNYE5dfGyK1uDP5AkEA4VZdUOTPt0DclMESX3lOddS3o+TL/OkowErP0mAl3NzbJ1PnDUifQ0q1IZUoCi1nG9eVZScS8xZ7oa7ICgdybwJBAIY/OrsK8cyJBlLx0WcjjOZ5WIGg8zsrCwRevwBsW7VRZPxahbfKC49EJN2BZENaMOo8AzDcDdS/glN1aTPsaUkCQAVLhj3UYp0nxQcp0ki0DQfvy7DqO3Dh+bcrCt8iq0EZX3z5F8DUKAnow4DahGpYzsd0tWn/FQ7pRFZ0SPcTXbkCQQCp7ay9nEo2hEH08E5LekFsuipDjCEpeCgKojZUmFCh7BdawG6XzCLzNMMIIIjqRHlrJaxS41WhedPZR4nTNxGF
加密前:我喜欢你,可以做我女朋友吗?
加密后:tRt5hdF0XB8V2wk6BWC2i8UWVQj/jOCRZn3wIfGYqVaYJ9OjC/+VRUI3c5WgpZlKCZd5zrHo3g1LuQ02G934Gcb51cKH4uhWxRY8oxUgs/fibkvc9+w1X7FQarFwAGCs5SddHIL/vYUxHIvQslelyP9l9/EFpgSs0WWSfOfKcUc=
解密后:我喜欢你,可以做我女朋友吗?
RSA算法解决了对称算法的安全性依赖于同一个密钥的缺点。不过,RSA算法在计算上相当复杂,性能欠佳、远远不如对称加密算法。因此,在一般实际情况下,往往通过非对称加密算法来随机创建临时的对称密钥,然后通过对称加密来传输大量、主体的数据。
DSA
DSA(Digital Signature Algorithm,数字签名算法)是 Schnorr 和 ElGamal 签名算法的变种,基于模算数和离散对数的复杂度。
美国国家标准技术研究所(NIST)于1991年提出将DSA用于其DSS(DigitalSignature Standard,数字签名标准),并于1994年将其作为FIPS 186采用。
和RSA算法使用公钥加密私钥解密的方式不同,DSA使用私钥对数据进行加密生成数字签名,然后使用公钥解密后的数据和原数据进行对比,以验证数字签名。
数字签名提供信息鉴定(接收者可以验证消息的来源),完整性(接收方可以验证消息自签名以来未被修改)和不可否认性(发送方不能错误地声称它们没有签署消息)。
我们用Java写个例子:
import java.nio.charset.Charset;
import java.nio.charset.StandardCharsets;
import java.security.GeneralSecurityException;
import java.security.KeyFactory;
import java.security.KeyPair;
import java.security.KeyPairGenerator;
import java.security.PrivateKey;
import java.security.PublicKey;
import java.security.Signature;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.X509EncodedKeySpec;
import java.util.Base64;
public class DsaUtil {
private static final String DSA = "DSA";
private static final String SHA1withDSA = "SHA1withDSA";
private static final Charset CHARSET = StandardCharsets.UTF_8;
/**
* 签名
*
* @param data 数据
* @param privateKey 私钥
* @return 签名
* @throws GeneralSecurityException
*/
public static String sign(String data, String privateKey) throws GeneralSecurityException {
PrivateKey priKey = KeyFactory.getInstance(DSA)
.generatePrivate(new PKCS8EncodedKeySpec(Base64.getDecoder().decode(privateKey)));
Signature signature = Signature.getInstance(SHA1withDSA);
signature.initSign(priKey);
signature.update(data.getBytes(CHARSET));
return Base64.getEncoder().encodeToString(signature.sign());
}
/**
* 验证
*
* @param data 数据
* @param publicKey 公钥
* @param sign 签名
* @return 是否验证通过
*/
public static boolean verify(String data, String publicKey, String sign) throws GeneralSecurityException {
try {
PublicKey pubKey = KeyFactory.getInstance(DSA)
.generatePublic(new X509EncodedKeySpec(Base64.getDecoder().decode(publicKey)));
Signature signature = Signature.getInstance(SHA1withDSA);
signature.initVerify(pubKey);
signature.update(data.getBytes(CHARSET));
return signature.verify(Base64.getDecoder().decode(sign));
} catch (Exception e) {
throw new RuntimeException(e);
}
}
public static void main(String[] args) throws GeneralSecurityException {
// 生成公钥/私钥对:
KeyPairGenerator kpGen = KeyPairGenerator.getInstance(DSA);
kpGen.initialize(1024);
KeyPair keyPair = kpGen.generateKeyPair();
String publicKey = Base64.getEncoder().encodeToString(keyPair.getPublic().getEncoded());
String privateKey = Base64.getEncoder().encodeToString(keyPair.getPrivate().getEncoded());
System.out.println("公钥:" + publicKey);
System.out.println("私钥:" + privateKey);
String msg = "我喜欢你,可以做我女朋友吗?";
System.out.println("数据:" + msg);
String sign = DsaUtil.sign(msg, privateKey);
System.out.println("签名:" + sign);
System.out.println("验证是否通过:" + DsaUtil.verify(msg, publicKey, sign));
}
}
运行结果如下:
公钥:MIIBtzCCASwGByqGSM44BAEwggEfAoGBAP1/U4EddRIpUt9KnC7s5Of2EbdSPO9EAMMeP4C2USZpRV1AIlH7WT2NWPq/xfW6MPbLm1Vs14E7gB00b/JmYLdrmVClpJ+f6AR7ECLCT7up1/63xhv4O1fnxqimFQ8E+4P208UewwI1VBNaFpEy9nXzrith1yrv8iIDGZ3RSAHHAhUAl2BQjxUjC8yykrmCouuEC/BYHPUCgYEA9+GghdabPd7LvKtcNrhXuXmUr7v6OuqC+VdMCz0HgmdRWVeOutRZT+ZxBxCBgLRJFnEj6EwoFhO3zwkyjMim4TwWeotUfI0o4KOuHiuzpnWRbqN/C/ohNWLx+2J6ASQ7zKTxvqhRkImog9/hWuWfBpKLZl6Ae1UlZAFMO/7PSSoDgYQAAoGABDM1s78NZ4C0Bh9V86Z1lylEyCjCg2oAj6Kxd3/2IXhSlplnSpJPLlomet9yWJpagLQieIWHAIyq6JLmdcVxOxUvnLIsrvWKIPr4lz7pIqO1xi4AYunP48gPECHlMgOKPyik3ZkQQ3iHl9MiaWOaeisqsw/gzTUtE1xi8CVscks=
私钥:MIIBSwIBADCCASwGByqGSM44BAEwggEfAoGBAP1/U4EddRIpUt9KnC7s5Of2EbdSPO9EAMMeP4C2USZpRV1AIlH7WT2NWPq/xfW6MPbLm1Vs14E7gB00b/JmYLdrmVClpJ+f6AR7ECLCT7up1/63xhv4O1fnxqimFQ8E+4P208UewwI1VBNaFpEy9nXzrith1yrv8iIDGZ3RSAHHAhUAl2BQjxUjC8yykrmCouuEC/BYHPUCgYEA9+GghdabPd7LvKtcNrhXuXmUr7v6OuqC+VdMCz0HgmdRWVeOutRZT+ZxBxCBgLRJFnEj6EwoFhO3zwkyjMim4TwWeotUfI0o4KOuHiuzpnWRbqN/C/ohNWLx+2J6ASQ7zKTxvqhRkImog9/hWuWfBpKLZl6Ae1UlZAFMO/7PSSoEFgIUA1HUKjMiSvazMzpKczR6w6DDbeM=
数据:我喜欢你,可以做我女朋友吗?
签名:MCwCFHhnd/3yRCIygyD1GPa1K9ZVQ+4rAhR8zAtlrBim9KKEkv+Fxz47opvSuA==
验证是否通过:true
通过Java的示例可以看到,不会直接对数据进行私钥的加密,而是先通过信息摘要算法对数据进行摘要,然后对摘要信息进行私钥的加密。
总结
非对称加密算法在加密和解密时使用两个不同的密钥,分别被称为公钥和私钥,只有同一个公钥私钥对才能正常加密和解密。
常见的非对称加密算法有:RSA算法、DSA。RSA算法主要进行对数据的公钥加密,DSA主要是对数据的签名验证。
竟然已经看到这里了,你我定是有缘人,留下你的点赞和关注,他日必成大器。
微信公众号:万猫学社
微信扫描二维码
关注后回复「电子书」
获取12本Java必读技术书籍


出处:http://www.cnblogs.com/heihaozi/
版权声明:本文遵循 CC 4.0 BY-NC-SA 版权协议,转载请附上原文出处链接和本声明。
微信扫描二维码,关注万猫学社,回复「电子书」,免费获取12本Java必读技术书籍。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号