一、绕过前端限制
1、抓包
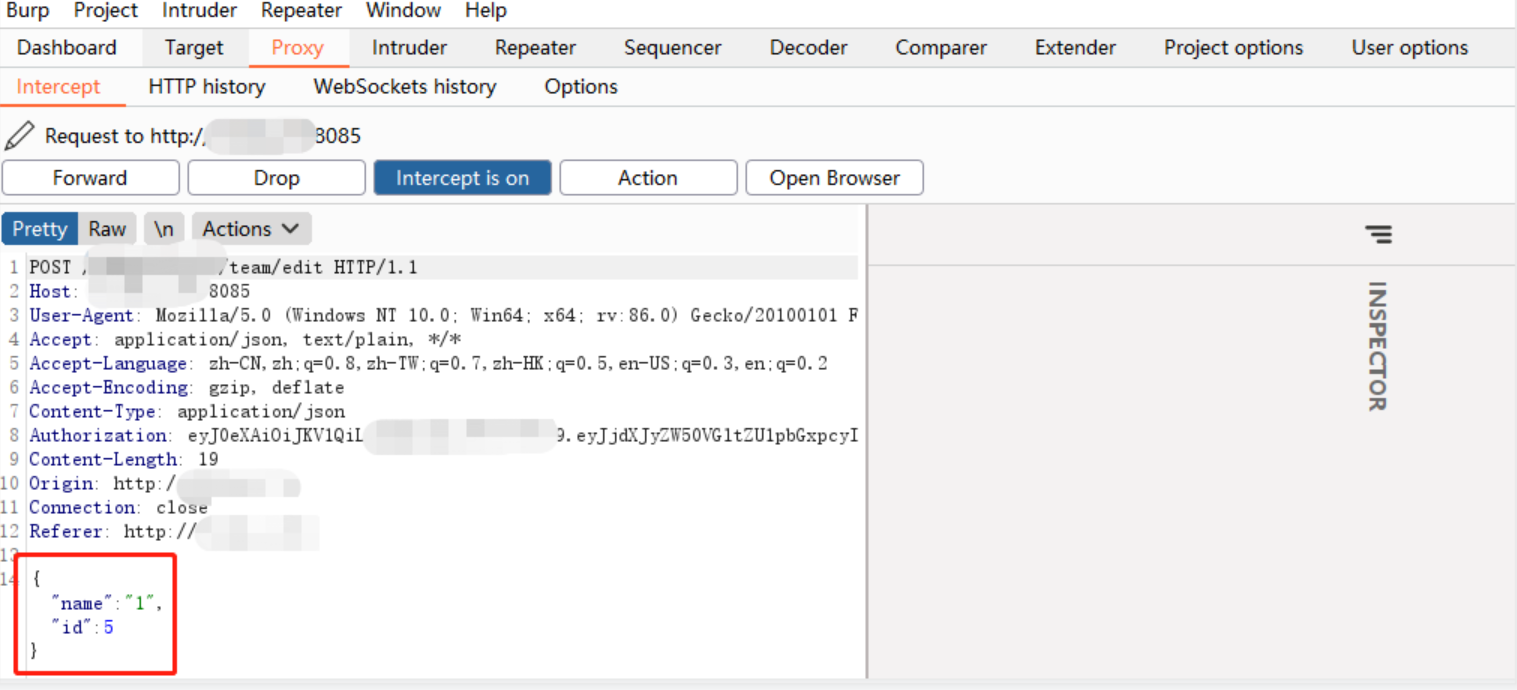

3、修改参数:增加长度超过 20
注意:接口 15s 会超时,需要在 15s 内操作完毕
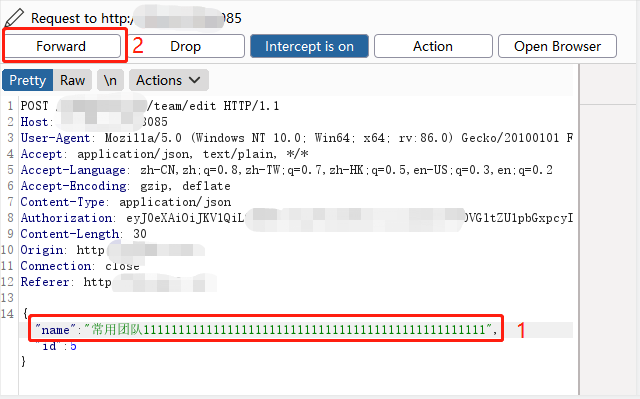
拓展:
参数修改成其他格式email=<img src=x onerror=alert(8905)>
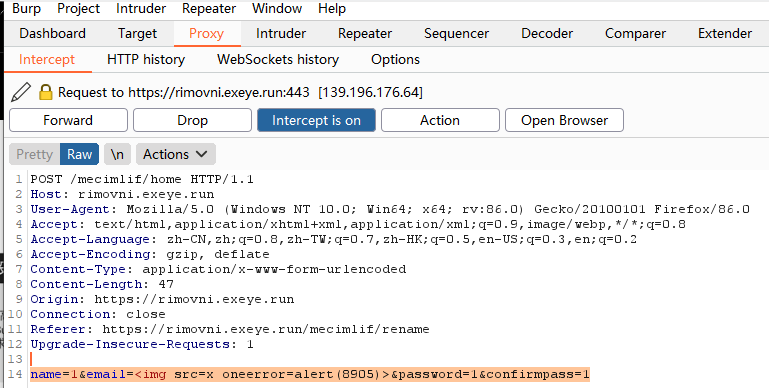
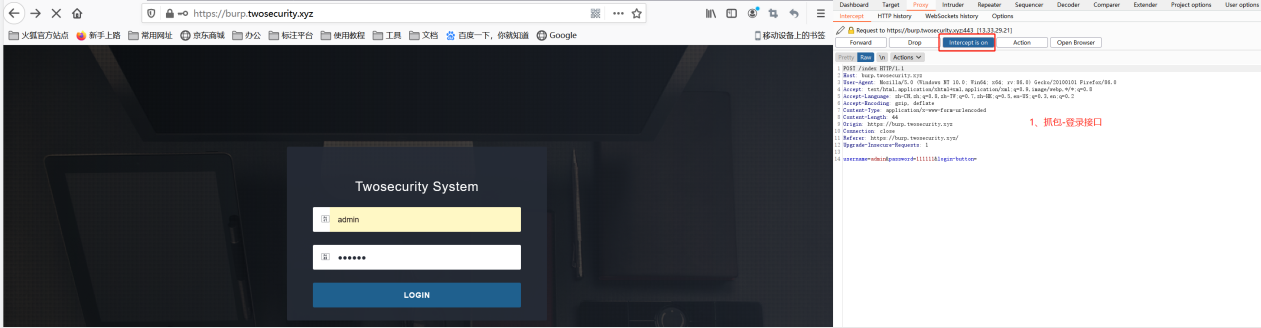
二、暴力破解登录密码
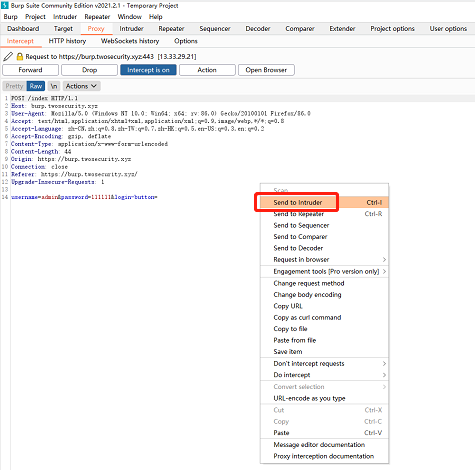
1、抓包-登录接口
2、右键-Send to Intruder
3、进入 Intruder

(1)Positions -> attack type 选择 Sniper(爆破模式)
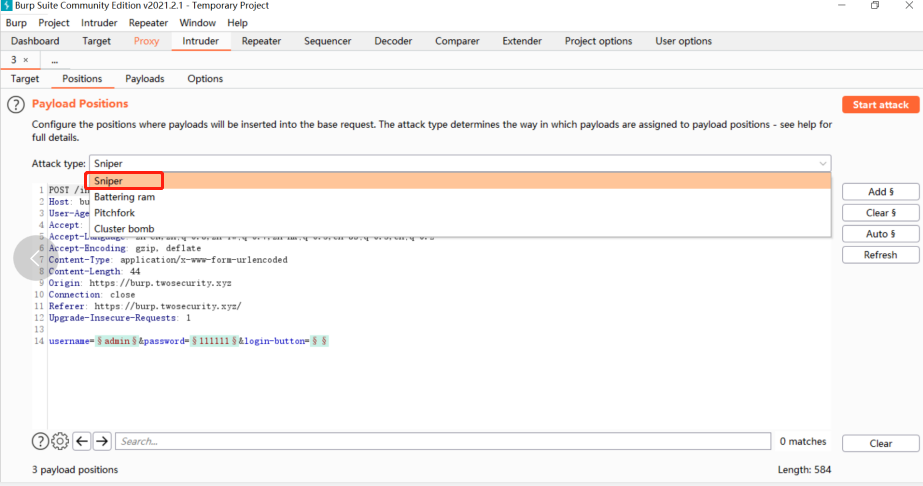
(2)清空默认的爆破参数,设置指定的爆破参数 password

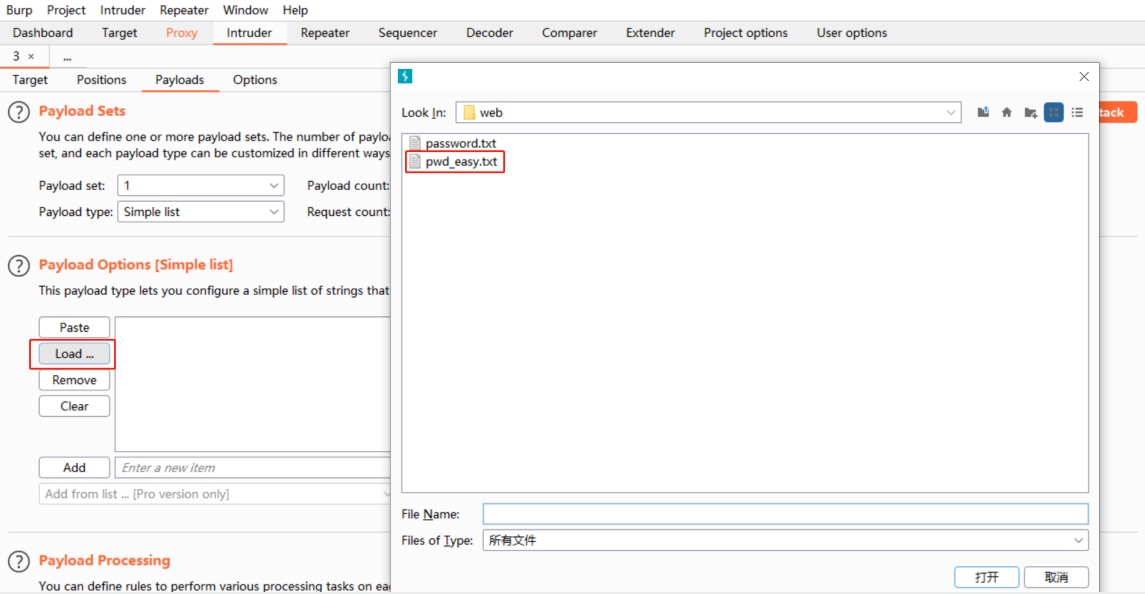
(3)Payloads 选择弱口令密码文档
(4)点击 Start attack 开始爆破
错误情况
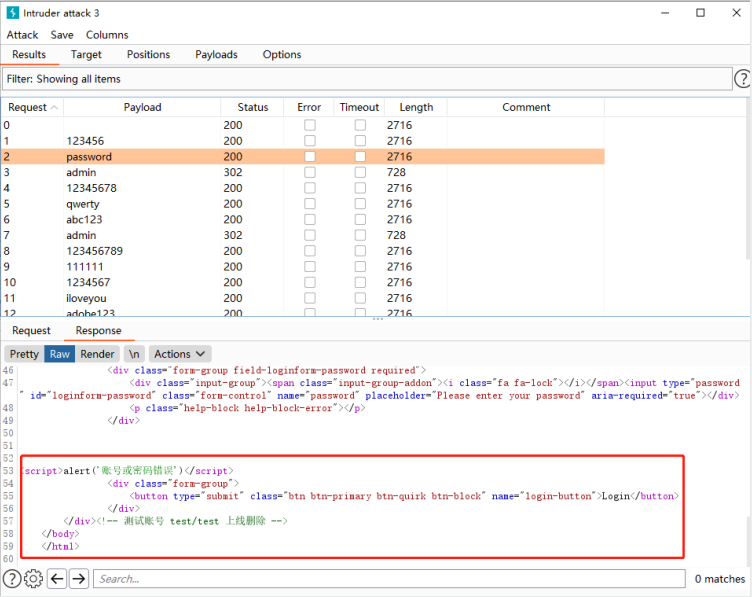
破解成功

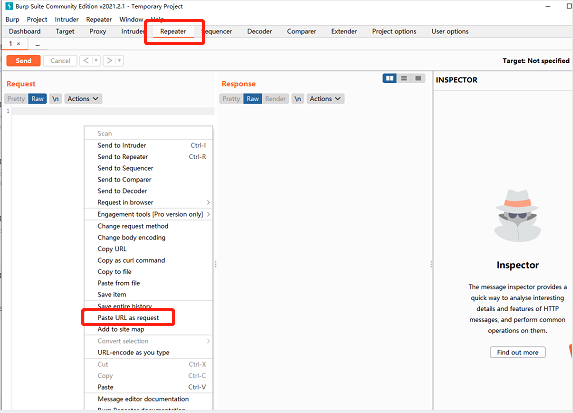
三、Repeater 重放请求
1、目标网站搜索内容,搜索成功后,复制完整链接

2、打开 Burpsuite
(1)Repeater,右键- Paste URL as request
(2)点击 Send
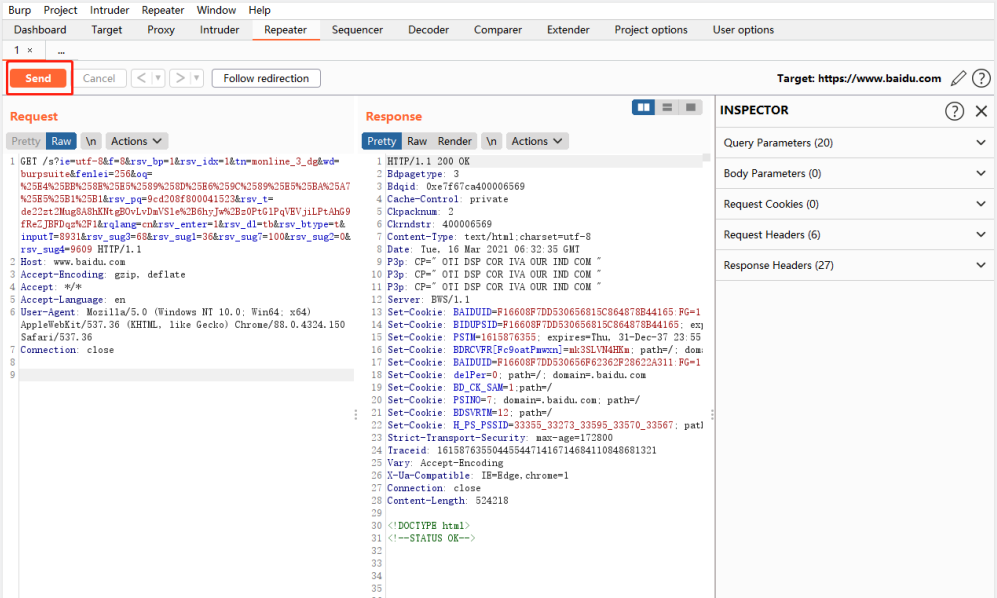
(3)重放成功
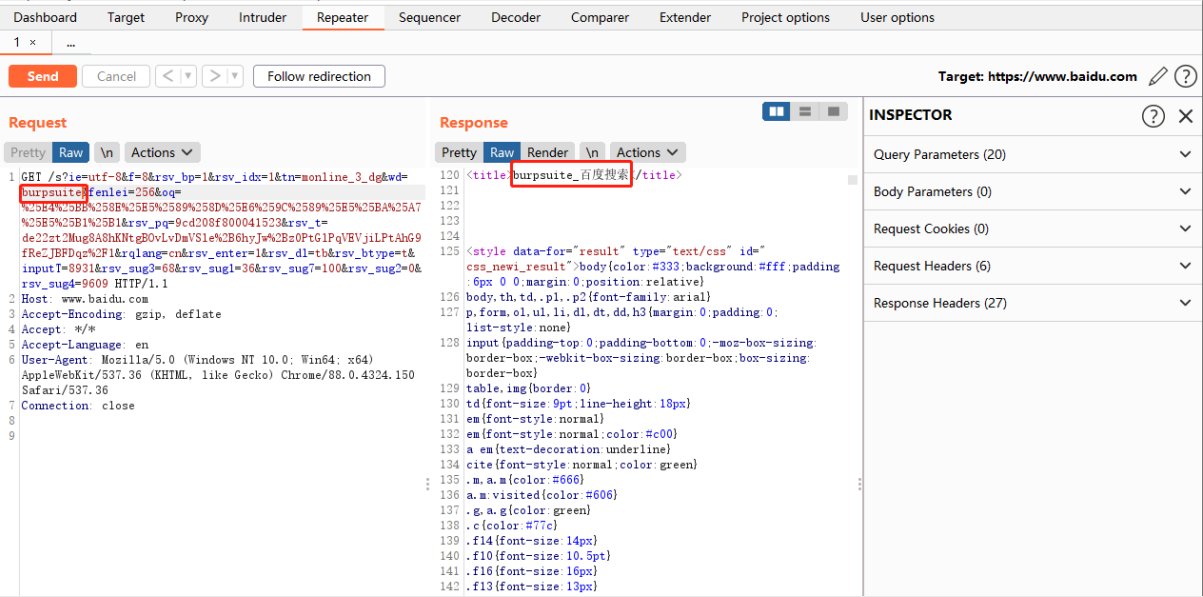
(4)修改参数,重新发送请求成功

参考:
https://zhishihezi.net/b/03c82a3d82cdf5a1d066e0e2423e48dd#start


 浙公网安备 33010602011771号
浙公网安备 33010602011771号