Kubernetes对接 Harbor 镜像仓库(Containerd)
一、Containerd 对接 Harbor
前提: k8s节点 hosts 文件需要能解析Harbor域名:192.168.1.250 reg.linux.io
- coredns 解析域名(可选)
~# kubectl edit cm/coredns -n kube-system
apiVersion: v1
data:
Corefile: |
.:53 {
errors
health {
lameduck 5s
}
ready
kubernetes cluster.local in-addr.arpa ip6.arpa {
pods insecure
fallthrough in-addr.arpa ip6.arpa
ttl 30
}
hosts {
192.168.1.250 reg.linux.io
fallthrough
}
prometheus :9153
...
}
~# kubectl delete pod -n kube-system -l k8s-app=kube-dns
1.1 创建hosts.toml文件或者证书文件存储的目录
创建hosts.toml文件或者证书文件存储的目录,这个创建的目录名称必须是Harbor的域名(如果不是则报x509),然后将证书文件或者hosts.toml文件放入该目录下才会生效。
~# mkdir -pv /etc/containerd/certs.d/reg.linux.io
1.2 修改config.toml配置
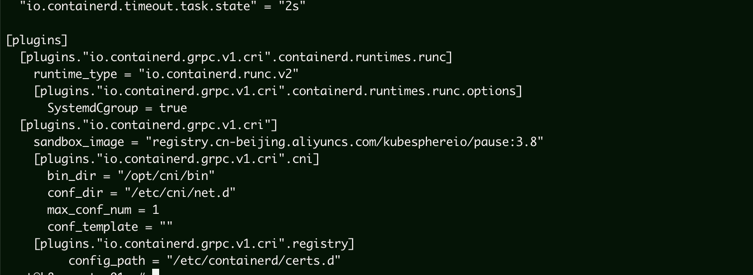
找到 [plugins."io.containerd.grpc.v1.cri".registry]下的config_path,然后指定证书存储目录,改完需重启containerd。
根据 containerd 配置规则,当使用 config_path 指定了证书和私有仓库配置文件目录时,不允许再使用 mirrors 配置,解决办法有两种:
- 删除 mirrors 配置,这里使用此红配置方式
- 移除 config_path 并仅使用 mirrors
[plugins]
...
[plugins."io.containerd.grpc.v1.cri".registry]
config_path = "/etc/containerd/certs.d"
# [plugins."io.containerd.grpc.v1.cri".registry.mirrors]
# [plugins."io.containerd.grpc.v1.cri".registry.mirrors."docker.io"]
# endpoint = ["https://registry-1.docker.io"]
1.3 配置认证方式
1.3.1 忽略证书的方式
- 忽略证书,就是我们只需要在/etc/containerd/certs.d/reg.linux.io/目录下面创建文件hosts.toml即可,不需要Harbor认证的自签名证书,无需重启containerd
cat >> /etc/containerd/certs.d/reg.linux.io/hosts.toml << EOF
server = "https://reg.linux.io"
[host."https://reg.linux.io"]
capabilities = ["pull", "resolve", "push"]
skip_verify = false
ca = ["ca.crt"]
EOF
1.3.2 启用证书的方式
需要把自签名Harbor域名的CA证书上传到/etc/containerd/certs.d/reg.linx.io/目录下
~# ls /etc/containerd/certs.d/reg.linux.io
ca.crt hosts.toml
在该目录下创建hosts.toml文件并指定CA证书
~# cat /etc/containerd/certs.d/reg.linux.io/hosts.toml
server = "https://reg.linux.io"
[host."https://reg.linux.io"]
capabilities = ["pull", "resolve","push"]
skip_verify = false
ca = ["ca.crt"]
二、Kubernetes对接Harbor
2.1 方式一:通过Secret使用镜像
~# kubectl create secret docker-registry harbor-secret \
--docker-server=reg.linux.io \
--docker-username=admin \
--docker-password=Harbor12345 \
-n default
~# cat myapp.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: myapp
name: myapp
spec:
replicas: 3
selector:
matchLabels:
app: myapp
strategy: {}
template:
metadata:
labels:
app: myapp
spec:
imagePullSecrets:
- name: harbor-secret
containers:
- image: reg.linux.io/privatelib/myapp:v1
name: myapp
resources: {}
~# cat myapp.yaml |kubectl apply -f -
2.2 方式二:通过ServviceAccount使用镜像
# 创建 sa
~# cat serviceaccount-harbor.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: harbor-sa
namespace: default
root@k8s-master01:~# kubectl apply -f serviceaccount-harbor.yaml
# patch 使用补丁修改、更新资源的字段
~# kubectl patch serviceaccount harbor-sa -n default -p '{"imagePullSecrets": [{"name": "harbor-secret"}]}'
~# cat myapp.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: myapp
name: myapp
spec:
replicas: 3
selector:
matchLabels:
app: myapp
strategy: {}
template:
metadata:
labels:
app: myapp
spec:
serviceAccount: harbor-sa
containers:
- image: reg.linux.io/privatelib/myapp:v1
name: myapp
resources: {}
~# kubectl apply -f myapp.yaml



 浙公网安备 33010602011771号
浙公网安备 33010602011771号