ICMP隐蔽隧道攻击分析与检测(四)
• ICMP隧道攻击通讯特征和特征提取
一、ICMP Ping正常通讯特征总结
- 一个正常的 ping 每秒最多只会发送两个数据包,而使用 ICMP隧道的服务器在同一时间会产生大量 ICMP 数据包
- 正常的icmp数据包里,请求数据包与对应的响应数据包内容一样
- 数据包中payload的大小固定,Windows下为32bytes,Linux下为48bytes
- 数据包中payload的内容固定,Windows下为 "abcdefghijklmnopqrstuvwabcdefghi" ,Linux下为 " !”#$%&’()+,-./01234567" ,如果指定ping发送的长度,则为不断重复的固定字符串
- type类型只有2种,8和0,8为请求数据,0为响应数据
二、ICMP隧道攻击通讯特征总结
- 一个正常的 ping 每秒最多只会发送两个数据包,而使用 ICMP 隧道的服务器在同一时间会产生大量 ICMP 数据包
- 请求数据包与对应的响应数据包内容不一样
- 数据包中 payload 的大小可以是任意大小,通常大于64bytes,当然 icmptunnel 可以配置限制所有数据包的 payload 为64bytes
- 个别ICMP隧道工具产生的数据包内容前面会增加 'TUNL' 标记以用于识别隧道
三、ICMP隧道攻击检测思路
- 检测同一来源数据包的数量:正常ping每秒只会发送2个数据包,而ICMP隧道可以每秒发送多个
- 检测数据包中 Payload 的大小:正常ping产生的数据包Payload的大小是固定的,而ICMP隧道数据包大小可以任意
- 检测响应数据包中 Payload 跟请求数据包是否不一致:正常Ping产生的数据包请求响应内容一致,而ICMP隧道请求响应数据包基本不一致
- 检测数据包中 Payload 的内容:正常ping产生的Payload为固定字符串,ICMP隧道的payload可以为任意
- 检测数据包的协议标签可能存在特殊字段:icmptunnel 会在所有的 ICMP Data 前面增加 'TUNL' 标记以用于识别隧道
- 检测数据包 ICMP Data 里面可能存在一些系统命令:'whoami','ls','ipconfig',......
四、IDS检测规则落地
1、禁止 ping ???
2、ICMP Data 字段形成一个白名单,不在白名单内的告警
pass: 匹配到规则后,suricata停止扫描数据包,并跳到所有规则末尾(仅针对当前数据包)
dsize: 匹配一个指定payload大小的数据包
itype: 匹配指定的ICMP类型值
icode: 匹配指定的ICMP代码值
nocase: 匹配内容不区分大小写
pass icmp any any -> any any (msg:"Whitecap: OSX or Linux ICMP Echo Request"; icode:0; itype:8; dsize:56; content:"!\"#$%&'()*+,-./01234567"; classtype:misc-activity; sid:5110001; rev:1;) pass icmp any any -> any any (msg:"Whitecap: OSX or Linux ICMP Echo Reply"; icode:0; itype:0; dsize:56; content:"!\"#$%&'()*+,-./01234567"; classtype:misc-activity; sid:5110002; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Windows XP/7/8 ICMP Echo Request"; icode:0; itype:8; dsize:32; content:"abcdefghijklmnopqrstuvwabcdefghi"; classtype:misc-activity; sid:5110003; rev:1; nocase;) pass icmp any any -> any any (msg:"Whitecap: Windows XP/7/8 ICMP Echo Reply"; icode:0; itype:0; dsize:32; content:"abcdefghijklmnopqrstuvwabcdefghi"; classtype:misc-activity; sid:5110004; rev:1; nocase;) pass icmp any any -> any any (msg:"Whitecap: Nmap ICMP Echo Request"; icode:0; itype:8; dsize:0; classtype:misc-activity; sid:5110005; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Nmap ICMP Echo Reply"; icode:0; itype:0; dsize:0; classtype:misc-activity; sid:5110006; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Group Policy Slow Link Detection"; icode:0; itype:8; dsize:>1400; content:"WANG2"; classtype:misc-activity; sid:5110007; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Group Policy Slow Link Detection"; icode:0; itype:0; dsize:>1400; content:"WANG2"; classtype:misc-activity; sid:5110008; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Solarwinds Status Query"; icode:0; itype:8; dsize:23; content:"SolarWinds Status Query"; classtype:misc-activity; sid:5110009; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Solarwinds Status Query"; icode:0; itype:0; dsize:23; content:"SolarWinds Status Query"; classtype:misc-activity; sid:5110010; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Domain Controller ICMP Traffic"; icode:0; itype:8; dsize:1; content:"?"; classtype:misc-activity; sid:5110011; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Domain Controller ICMP Traffic"; icode:0; itype:0; dsize:1; content:"?"; classtype:misc-activity; sid:5110012; rev:1;) pass icmp any any -> any any (msg:"Whitecap: McAfee ICMP ping Request"; icode:0; itype:8; dsize:36; content:"EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE"; offset:3; classtype:misc-activity; sid:5110013; rev:2;) pass icmp any any -> any any (msg:"Whitecap: McAfee ICMP ping Reply"; icode:0; itype:0; dsize:36; content:"EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE"; offset:3; classtype:misc-activity; sid:5110014; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Lots of Xs"; icode:0; itype:8; dsize:32; content:"xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx"; classtype:misc-activity; sid:5110015; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Lots of Xs"; icode:0; itype:0; dsize:32; content:"xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx"; classtype:misc-activity; sid:5110016; rev:1;) pass icmp any any -> any any (msg:"Whitecap: DHCP ICMP Duplicate IP Check"; icode:0; itype:8; dsize:11; content:"DhcpIcmpChk"; classtype:misc-activity; sid:5110017; rev:1;) pass icmp any any -> any any (msg:"Whitecap: DHCP ICMP Duplicate IP Check"; icode:0; itype:0; dsize:11; content:"DhcpIcmpChk"; classtype:misc-activity; sid:5110018; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Solarwinds ICMP Version 5"; icode:0; itype:8; dsize:<80; content:"SolarWinds.Net ICMP Version 5.0.4.16Copyright 1995-2005 SolarWinds.Net"; classtype:misc-activity; sid:5110019; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Solarwinds ICMP Version 5"; icode:0; itype:0; dsize:<80; content:"SolarWinds.Net ICMP Version 5.0.4.16Copyright 1995-2005 SolarWinds.Net"; classtype:misc-activity; sid:5110020; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Solarwinds Sonar ICMP Scan"; icode:0; itype:8; dsize:24; content:"Orion Network Sonar Scan"; classtype:misc-activity; sid:5110021; rev:1;) pass icmp any any -> any any (msg:"Whitecap: Solarwinds Sonar ICMP Scan"; icode:0; itype:0; dsize:24; content:"Orion Network Sonar Scan"; classtype:misc-activity; sid:5110022; rev:1;) pass icmp any any -> $DNS_SERVERS any (msg:"Whitecap: ICMP to DNS Servers"; icode:0; itype:8; dsize:<57; classtype:misc-activity; threshold:type limit, track by_src, count 1, seconds 60; sid:5110500; rev:2;) pass icmp any any -> $DNS_SERVERS any (msg:"Whitecap: ICMP to DNS Servers"; icode:0; itype:0; dsize:<57; classtype:misc-activity; threshold:type limit, track by_src, count 1, seconds 60; sid:5110501; rev:2;) pass icmp any any -> any any (msg:"Whitecap: Domain controller to domain controller"; icode:0; itype:8; dsize:32; content:"|00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00|"; classtype:misc-activity; threshold:type limit, track by_src, count 1, seconds 60; sid:5110502; rev:2;) pass icmp any any -> any any (msg:"Whitecap: Domain controller to domain controller"; icode:0; itype:0; dsize:32; content:"|00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00|"; classtype:misc-activity; threshold:type limit, track by_src, count 1, seconds 60; sid:5110503; rev:2;) pass icmp any any -> any any (msg:"Whitecap: All As"; icode:0; itype:8; dsize:64; content:"|AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA|"; classtype:misc-activity; sid:5110504; rev:1;) pass icmp any any -> any any (msg:"Whitecap: All As"; icode:0; itype:0; dsize:64; content:"|AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA AA|"; classtype:misc-activity; sid:5110505; rev:1;) pass icmp any any -> any any (msg:"Whitecap: All 0s"; icode:0; itype:8; dsize:56; content:"|00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00|"; classtype:misc-activity; sid:5110506; rev:1;) pass icmp any any -> any any (msg:"Whitecap: All 0s"; icode:0; itype:0; dsize:56; content:"|00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00|"; classtype:misc-activity; sid:5110507; rev:1;) pass icmp [$ICMP_SRC_HOSTS_IGNORE] any -> any any (msg:"ICMP Pass: Ignore Hosts"; icode:0; itype:8; classtype:misc-activity; sid:5111000; rev:1;) pass icmp [$ICMP_SRC_HOSTS_IGNORE] any -> any any (msg:"ICMP Pass: Ignore Hosts"; icode:0; itype:0; classtype:misc-activity; sid:5111001; rev:1;) pass icmp any any -> [$ICMP_DST_HOSTS_IGNORE] any (msg:"ICMP Pass: Ignore Hosts"; icode:0; itype:8; classtype:misc-activity; sid:5111002; rev:1;) pass icmp any any -> [$ICMP_DST_HOSTS_IGNORE] any (msg:"ICMP Pass: Ignore Hosts"; icode:0; itype:0; classtype:misc-activity; sid:5111003; rev:1;)
3, 检测包大于多少,或者发送频率高于某个数,报警
alert icmp any any -> any any (msg:"Whitecap Echo Request Payload > 100 bytes"; icode:0; itype:8; dsize:>100; classtype:misc-activity; sid:5113000; rev:1;) alert icmp any any -> any any (msg:"Whitecap Echo Reply Payload > 100 bytes"; icode:0; itype:0; dsize:>100; classtype:misc-activity; sid:5113001; rev:1;)
4、检测 Data 里面包含的特殊字段报警(例如检测 base64、操作系统常见命令等)
alert icmp any any -> any any (msg:"LOCAL ICMP Large ICMP Packet (Base64)"; dsize:>800; content:"="; pcre:"/^(?:[A-Za-z0-9+/]{4})*(?:[A-Za-z0-9+/]{2}==|[A-Za-z0-9+/]{3}=|[A-Za-z0-9+/]{4})$/"; classtype:misc-activity; sid:1000028; rev:1;)
五、基于统计分析ICMP隧道攻击
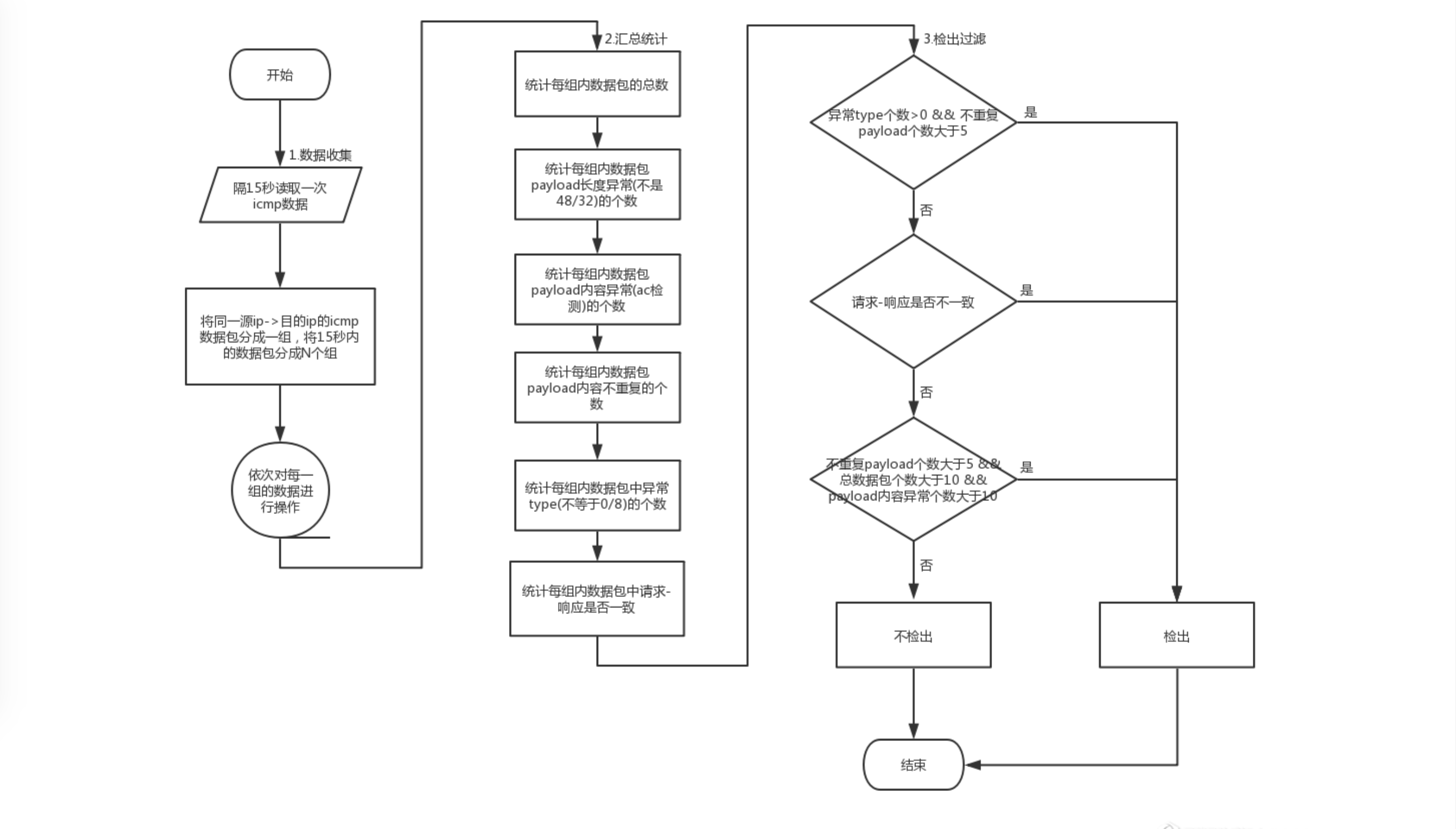
数据收集
- 读入实时流量数据,设置15秒处理一次数据
- 根据数据包的源ip、目的ip大小排序拼接后进行分组,将同一个ip向目的ip发送的请求/响应数据包分到一个组中
- 分组字段time_sort_sip_dip 加上时间戳timestamp
- 为了过滤掉上一次15秒内该源ip、目的ip之间的数据包,保证每个15秒内只处理当前15秒内的同一ip、目的ip的数据
汇总统计
根据分组后的数据,分别统计以下特征指标,作为最终是否检出的依据:
- 在一个时间窗内,ICMP请求响应的数据包数量
- 捕获到的ICMP请求响应中,其payload部分是否是操作系统的正常长度
- 序号相同的ICMP数据包应当属于一对ICMP请求响应消息,他们的payload是否一致
- ICMP请求响应的payload内容是否正常
- ICMP请求是否是畸形Ping报文(Type是否异常)


 浙公网安备 33010602011771号
浙公网安备 33010602011771号