2024强网杯-谍影重重5.0
<p>这里主要是因为这题类型是第一次做,而且网上师傅们的方法也很多样,但是作为wp又有点难理解,所以我就整合了一下,可以零基础也能明白其中的指令和操作原理,并贴了参考wp的文章,内容必然会有些不足和瑕疵,感谢各位师傅批评</p>
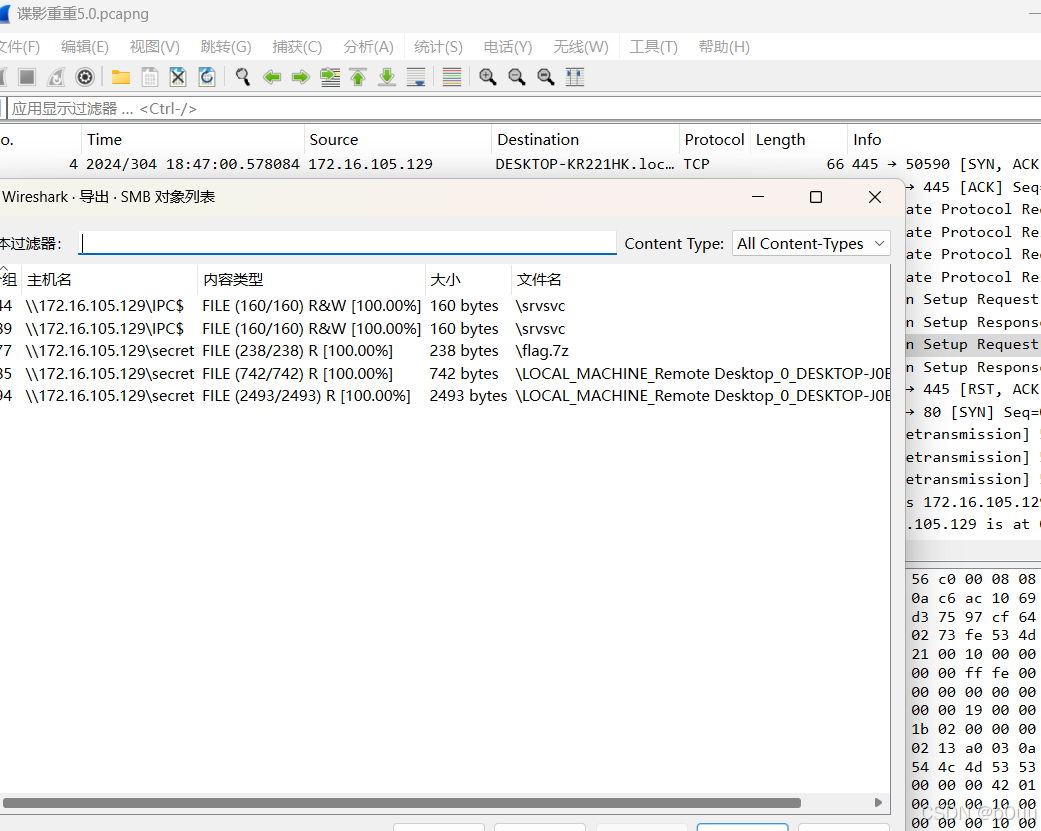
根据这个协议的分析,应该可以确定这个是和SMB协议有关的流量,这个做的不多,可以从其他的博客文章上先学习一下
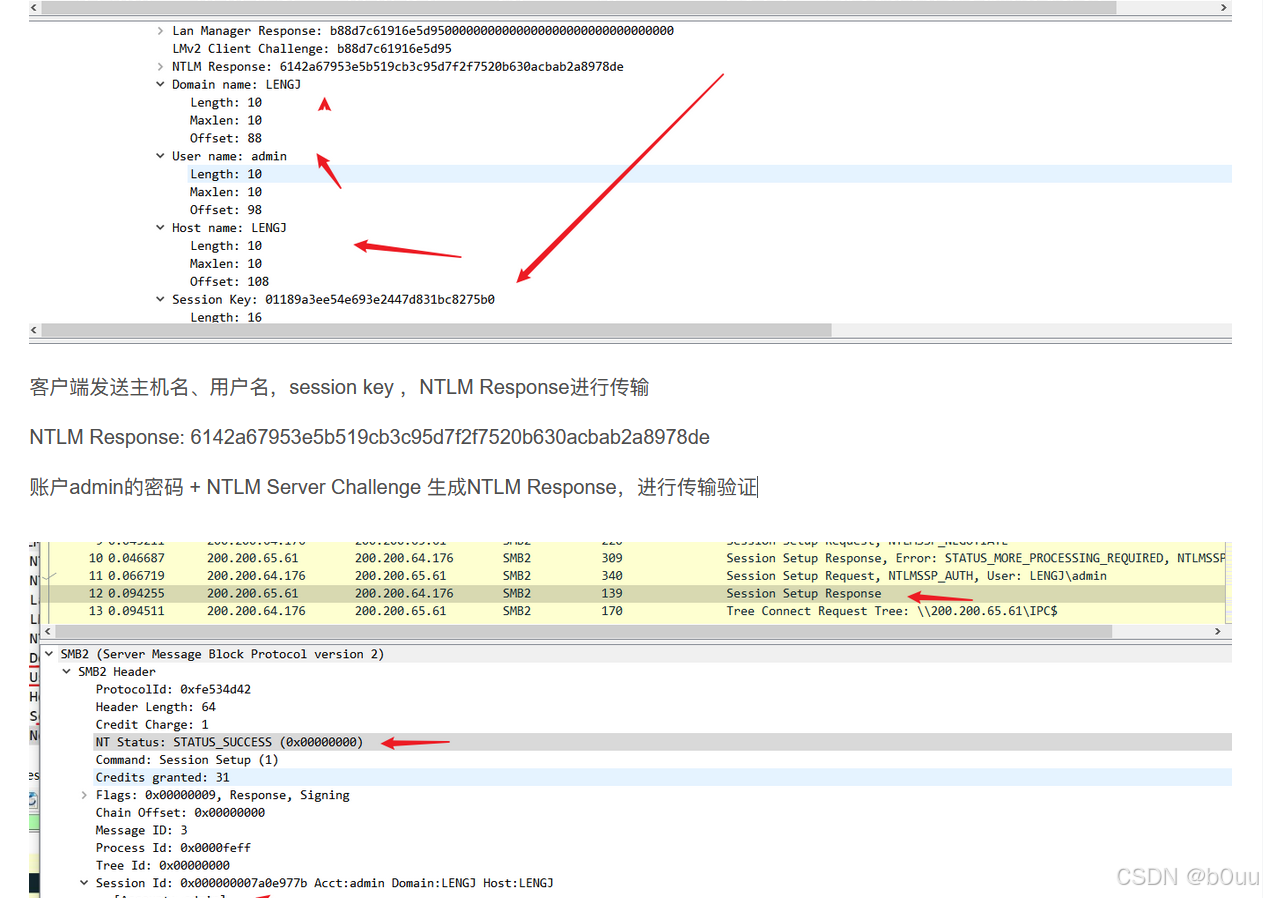
这里看到有NTLM验证传输,再去流量包里看内容,里面有很多地方出现NTLM的地方,但是基本上都是乱码,猜测是被混淆了,接着用工具跑一下看看有没有什么思路
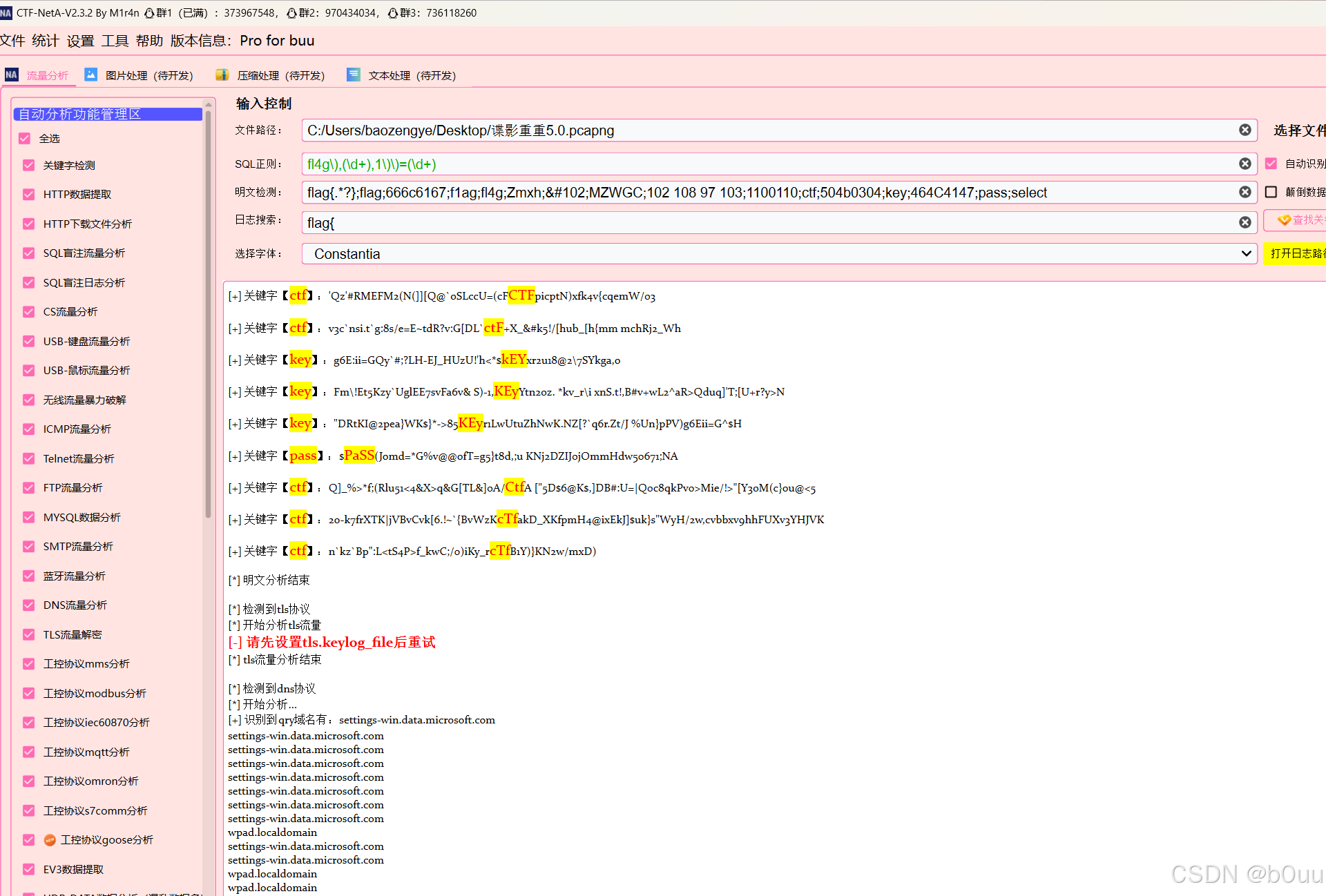
很好,这里提示需要TLS密钥文件,那基本上就是要找到身份验证的密钥来解密流量包
但是其中并没有密钥,但是有hash数据,可以通过hash数据来爆破密钥
哈希格式是 username::domain:challenge:HMAC-MD5:blob 所以就可以开始手撕哈希了
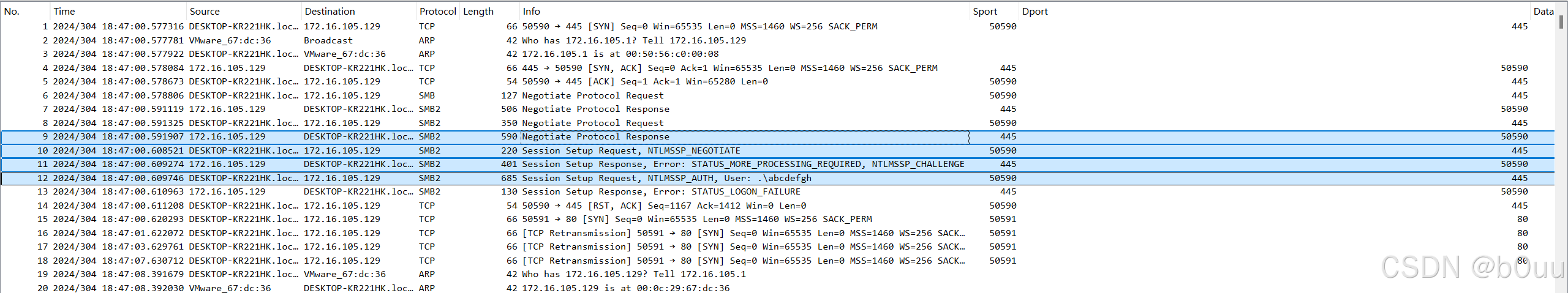
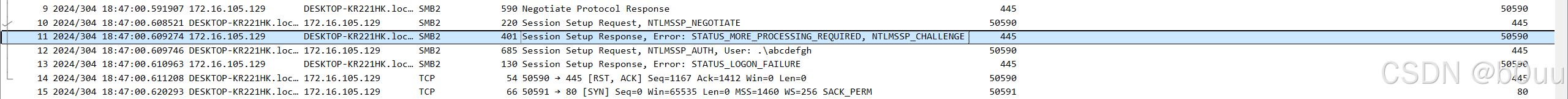
前四个数据包是验证的过程
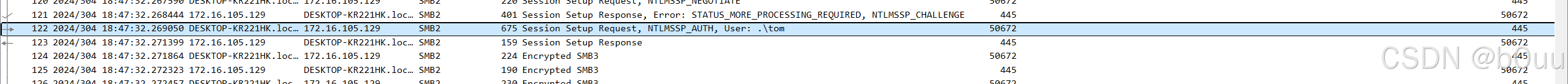
这个数据包的最后有一个User,后面跟着的就是用户名
tom
domian的值由数据包内容获得(IP或者机器名)
172.16.105.129
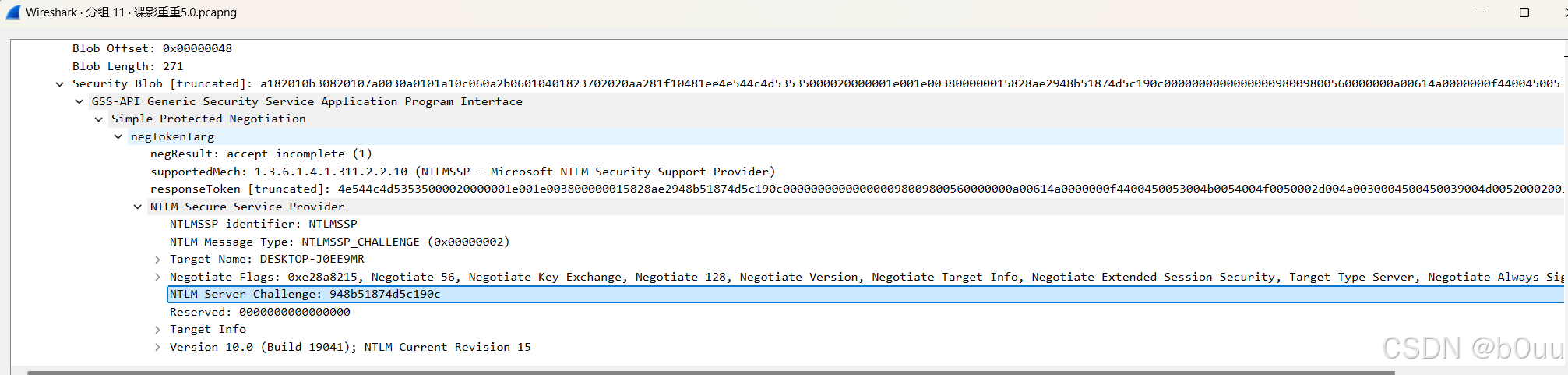
 在这个数据包中可以获得challenge的值
在这个数据包中可以获得challenge的值
948b51874d5c190c
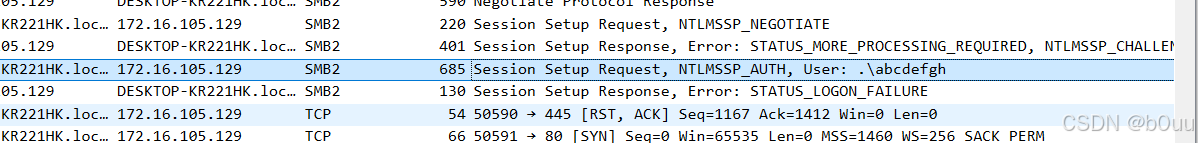
在下面这个数据包中可以获得客户端加密后的challenge值
b8926c1772e66b3f
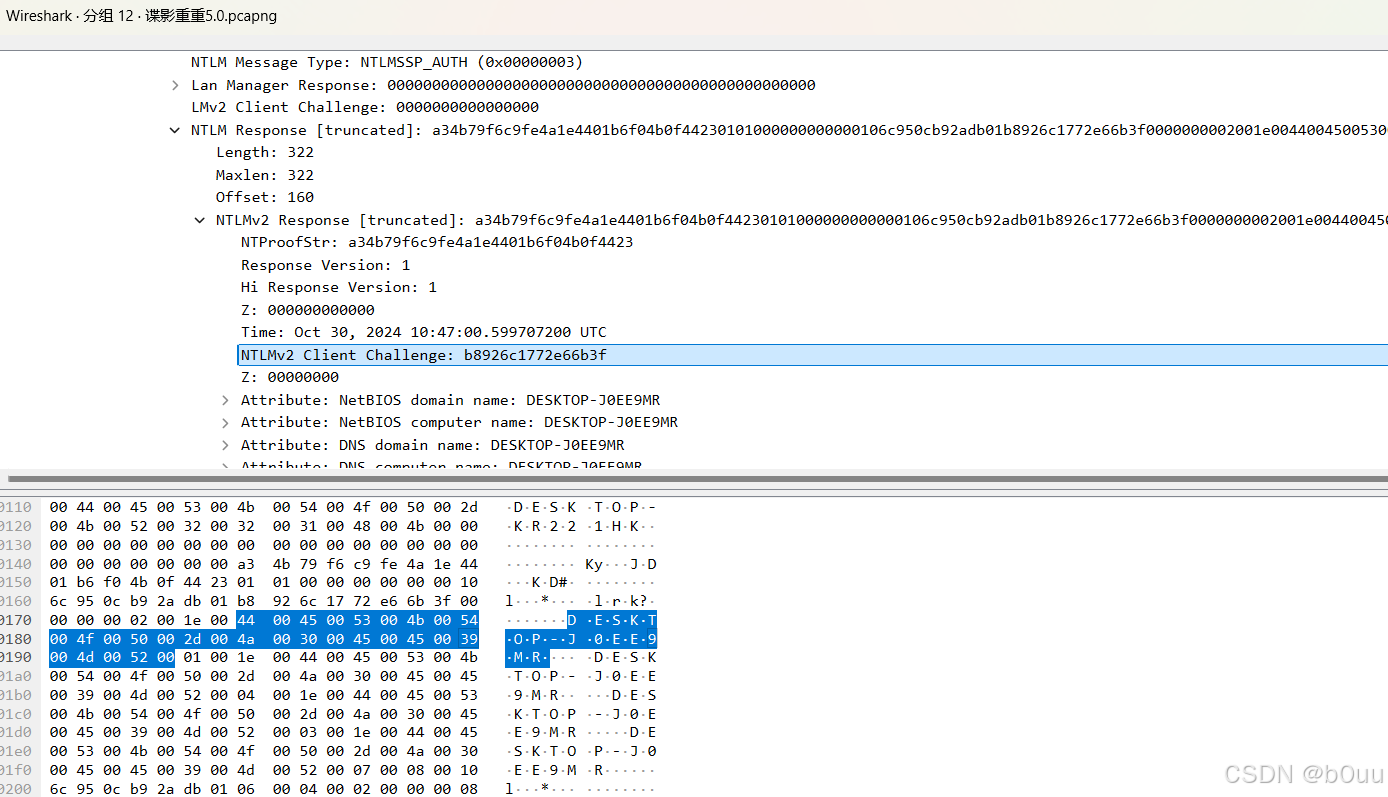
在这个数据包中还可以获得response的值
a34b79f6c9fe4a1e4401b6f04b0f44230101000000000000106c950cb92adb01b8926c1772e66b3f0000000002001e004400450053004b0054004f0050002d004a0030004500450039004d00520001001e004400450053004b0054004f0050002d004a0030004500450039004d00520004001e004400450053004b0054004f0050002d004a0030004500450039004d00520003001e004400450053004b0054004f0050002d004a0030004500450039004d00520007000800106c950cb92adb0106000400020000000800300030000000000000000100000000200000bd69d88e01f6425e6c1d7f796d55f11bd4bdcb27c845c6ebfac35b8a3acc42c20a001000000000000000000000000000000000000900260063006900660073002f003100370032002e00310036002e003100300035002e003100320039000000000000000000
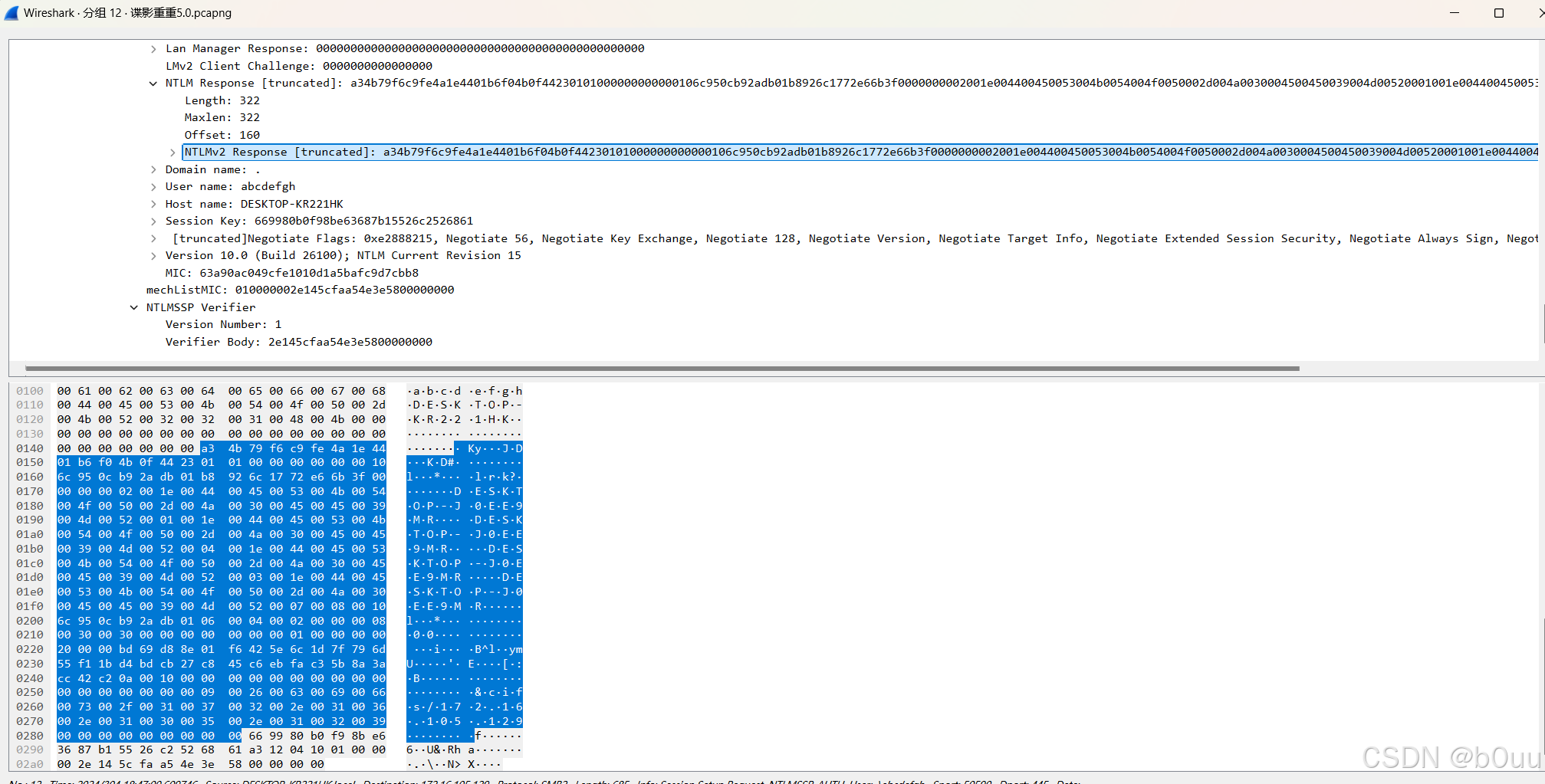
HMAC-MD5的值就是NTProofStr的值,也可以在上面的数据包中获得
a34b79f6c9fe4a1e4401b6f04b0f4423
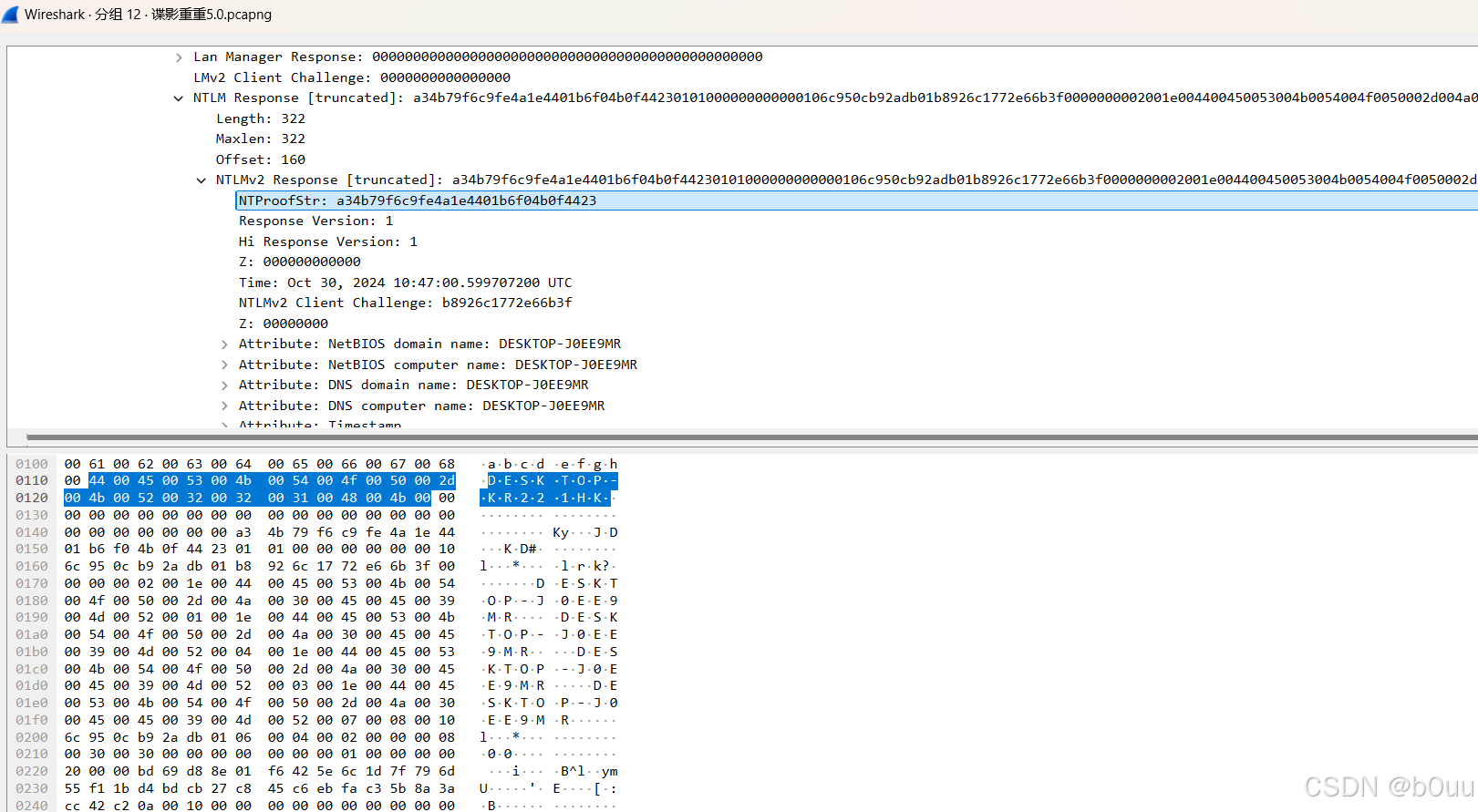
最后的blob值就是对应数据包中Response去掉NTProofStr的后半部分
0101000000000000106c950cb92adb01b8926c1772e66b3f0000000002001e004400450053004b0054004f0050002d004a0030004500450039004d00520001001e004400450053004b0054004f0050002d004a0030004500450039004d00520004001e004400450053004b0054004f0050002d004a0030004500450039004d00520003001e004400450053004b0054004f0050002d004a0030004500450039004d00520007000800106c950cb92adb0106000400020000000800300030000000000000000100000000200000bd69d88e01f6425e6c1d7f796d55f11bd4bdcb27c845c6ebfac35b8a3acc42c20a001000000000000000000000000000000000000900260063006900660073002f003100370032002e00310036002e003100300035002e003100320039000000000000000000
所以这样就可以将这几个值拼接在一起,得到一个NTLMhash
tom::172.16.105.129:948b51874d5c190c:a34b79f6c9fe4a1e4401b6f04b0f4423:0101000000000000106c950cb92adb01b8926c1772e66b3f0000000002001e004400450053004b0054004f0050002d004a0030004500450039004d00520001001e004400450053004b0054004f0050002d004a0030004500450039004d00520004001e004400450053004b0054004f0050002d004a0030004500450039004d00520003001e004400450053004b0054004f0050002d004a0030004500450039004d00520007000800106c950cb92adb0106000400020000000800300030000000000000000100000000200000bd69d88e01f6425e6c1d7f796d55f11bd4bdcb27c845c6ebfac35b8a3acc42c20a001000000000000000000000000000000000000900260063006900660073002f003100370032002e00310036002e003100300035002e003100320039000000000000000000
但是这样这样的格式有错误,所以这里只做知识拓展了,要搞还得是,tshark
利用命令行来打
# username domain ntproofstr ntresponsetshark -n -r dy.pcapng -Y 'ntlmssp.messagetype == 0x00000003' -T fields -e ntlmssp.auth.username -e ntlmssp.auth.domain -e ntlmssp.ntlmv2_response.ntproofstr -e ntlmssp.auth.ntresponse# ntlmserverchallenge$ tshark -n -r traffic.pcapng -Y 'ntlmssp.messagetype == 0x00000002' -T fields -e ntlmssp.ntlmserverchallenge
下面这个才是拼接之后成功爆破的,可能我的格式出了问题,一直在报错
tom::.:c1dec53240124487:ca32f9b5b48c04ccfa96f35213d63d75:010100000000000040d0731fb92adb01221434d6e24970170000000002001e004400450053004b0054004f0050002d004a0030004500450039004d00520001001e004400450053004b0054004f0050002d004a0030004500450039004d00520004001e004400450053004b0054004f0050002d004a0030004500450039004d00520003001e004400450053004b0054004f0050002d004a0030004500450039004d0052000700080040d0731fb92adb0106000400020000000800300030000000000000000100000000200000bd69d88e01f6425e6c1d7f796d55f11bd4bdcb27c845c6ebfac35b8a3acc42c20a001000000000000000000000000000000000000900260063006900660073002f003100370032002e00310036002e003100300035002e003100320039000000000000000000
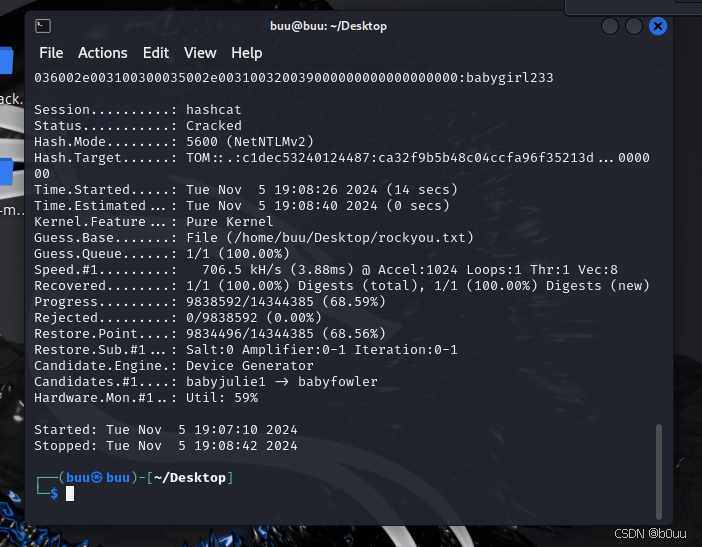 这样就得到了密码babygirl233
这样就得到了密码babygirl233
然后就将密码添加到流量包中
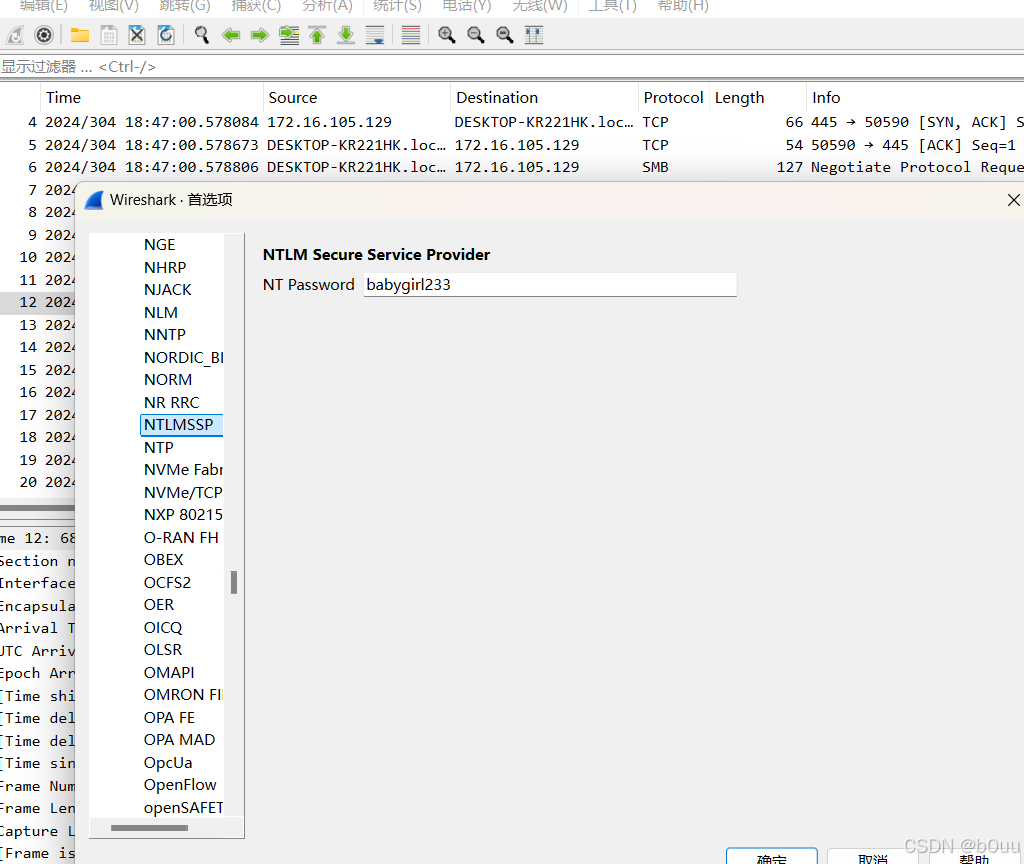
自动解密后,可以导出文件,其中就有一个flag.7z(但是被加密)
通过阅读其他师傅的wp,知道这里出题人是用了mimikatz一把梭,所以用mimikatz来作为密码得到密钥文件
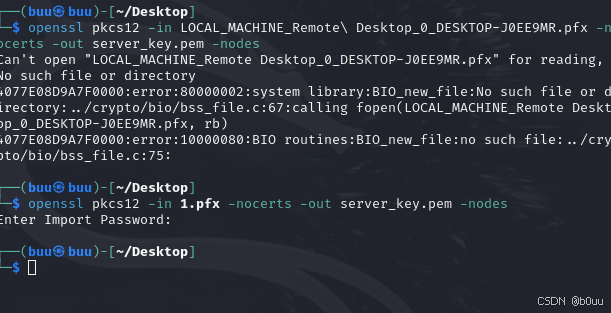
有tls文件后,添加到工具中来解密RDB流量
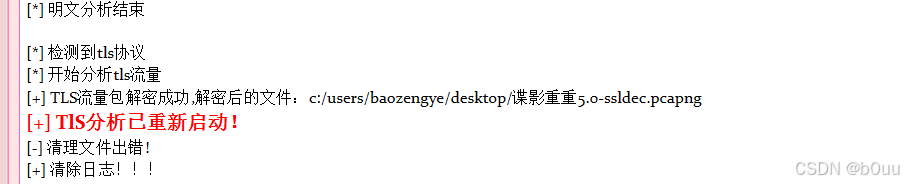
获得一个新的流量包,可以分离着看RDP流量,发现有很多mouse和Scancode,可以看出这应该就是鼠标和键盘的输入流量
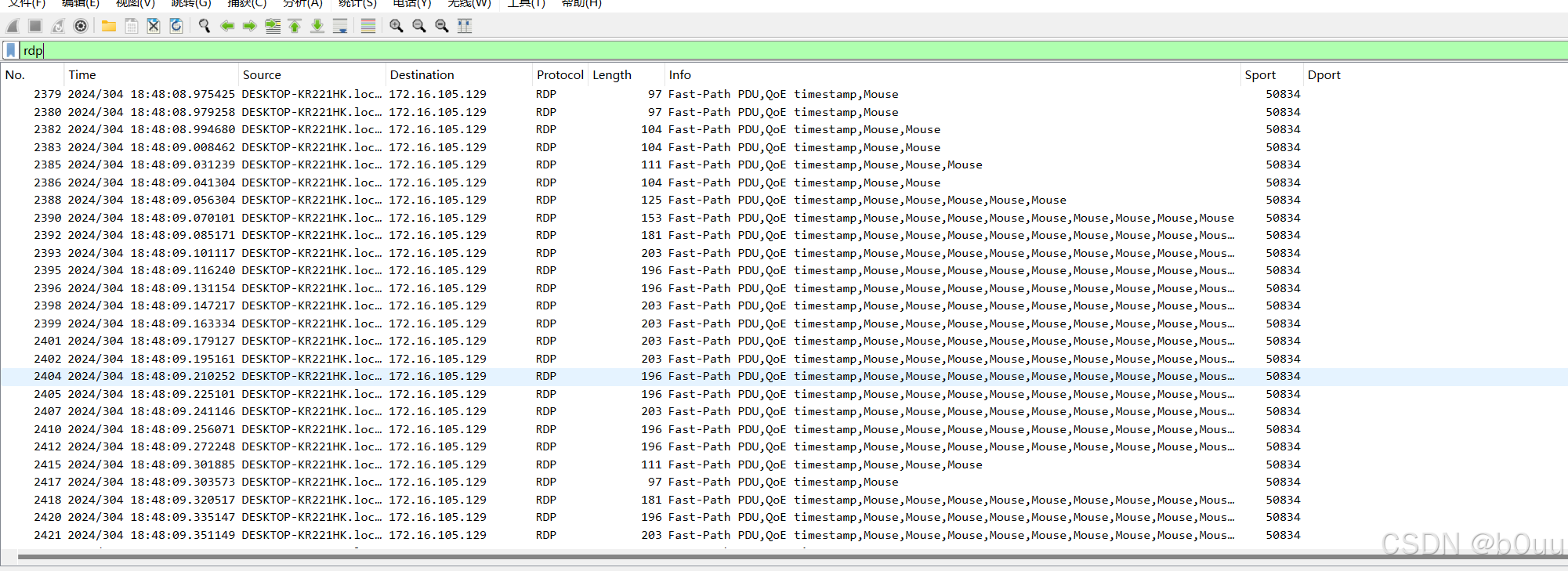
利用tshark命令来筛选
rdp.fastpath.scancode.keycode
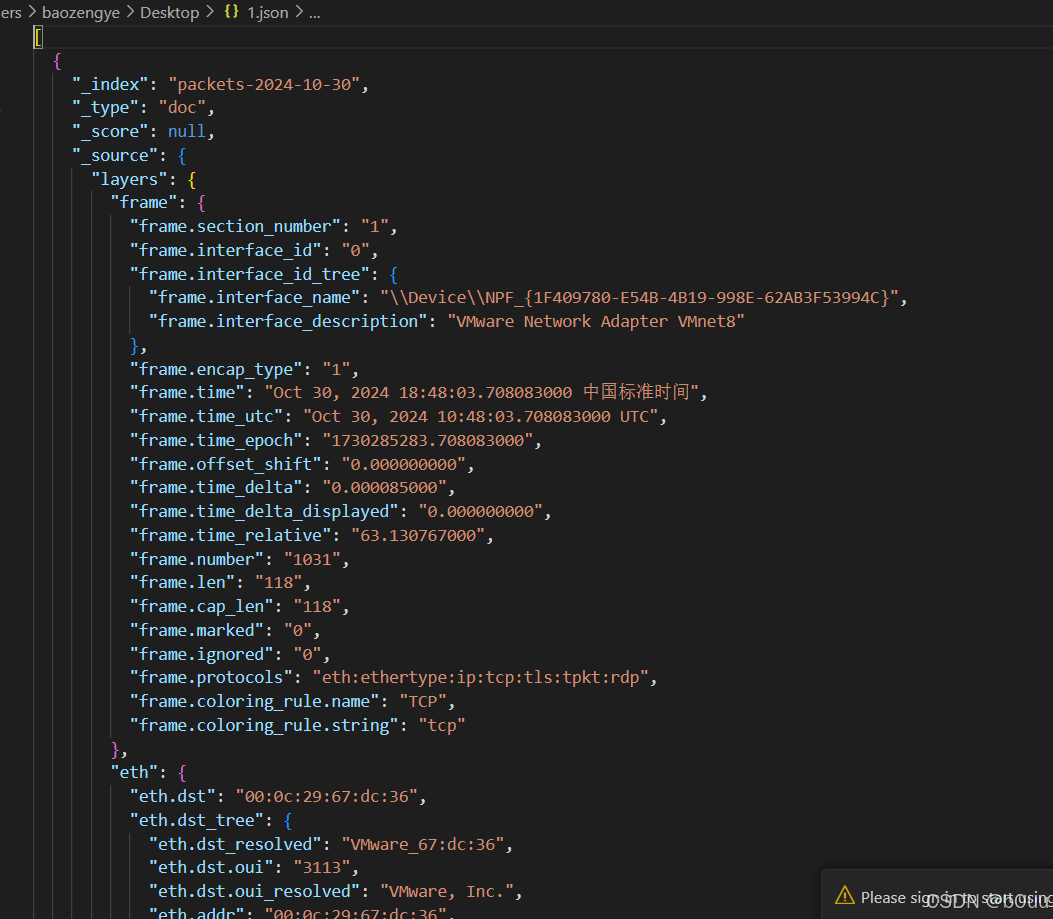
再导出文件解析结果为json文件,如下是部分
import json from jsonpath import jsonpathscancode_map = {
0x01: 'Esc',
0x02: '1',
0x03: '2',
0x04: '3',
0x05: '4',
0x06: '5',
0x07: '6',
0x08: '7',
0x09: '8',
0x0A: '9',
0x0B: '0',
0x0C: '-',
0x0D: '=',
0x0E: '\b',
0x0F: ' ',
0x10: 'Q',
0x11: 'W',
0x12: 'E',
0x13: 'R',
0x14: 'T',
0x15: 'Y',
0x16: 'U',
0x17: 'I',
0x18: 'O',
0x19: 'P',
0x1A: '[',
0x1B: ']',
0x1C: '\n',
0x1D: 'Ctrl',
0x1E: 'A',
0x1F: 'S',
0x20: 'D',
0x21: 'F',
0x22: 'G',
0x23: 'H',
0x24: 'J',
0x25: 'K',
0x26: 'L',
0x27: ';',
0x28: ''',
0x29: '`',
0x2A: ' Shift ',
0x2B: '\',
0x2C: 'Z',
0x2D: 'X',
0x2E: 'C',
0x2F: 'V',
0x30: 'B',
0x31: 'N',
0x32: 'M',
0x33: ',',
0x34: '.',
0x35: '/',
0x36: ' Shift ',
0x37: '*',
0x38: ' Left Alt ',
0x39: ' ',
0x3A: ' Caps Lock ',
0x3B: ' F1 ',
0x3C: ' F2 ',
0x3D: ' F3 ',
0x3E: ' F4 ',
0x3F: ' F5 ',
0x40: ' F6 ',
0x41: ' F7 ',
0x42: ' F8 ',
0x43: ' F9 ',
0x44: ' F10 ',
0x45: ' Num Lock ',
0x46: ' Scroll Lock ',
0x47: ' Home ',
0x48: ' Up Arrow ',
0x49: ' Page Up',
0x4A: ' Keypad -',
0x4B: ' Left Arrow',
0x4C: ' Keypad 5',
0x4D: ' Right Arrow',
0x4E: ' Keypad +',
0x4F: ' End',
0x50: ' Down Arrow',
0x51: ' Page Down',
0x52: ' Insert',
0x53: ' Delete',
0x57: ' F11',
0x58: ' F12'
}def convert_hex_string(hex_string):
# 去掉前缀并转换为大写
if hex_string.startswith('0x'):
hex_value = hex_string[2:].upper()
return f'0x{hex_value}'
return None # 如果字符串不以'0x'开头,返回Nonewith open("out.txt", "r", encoding="utf-8") as file:
lines = file.readlines()con = []
for line in lines:
con.append(line.strip('\n'))print(con)
print("\n")
for i in range(len(con)):
if con[i] == con[i - 1]:
continue
try:
print(scancode_map[int(con[i], 16)], end="")
except:
pass
利用脚本得出传输的密码(这里的脚本具体怎么使用的截图没有放出来,但是有一个更好的办法,利用pyrdp,转换为pyrdp可读的文件,然后加载pyrdp的GUI来看RDP的操作,这里先放一下,研究好这个再贴新的,这里放一个网上师傅发的wp的截图)
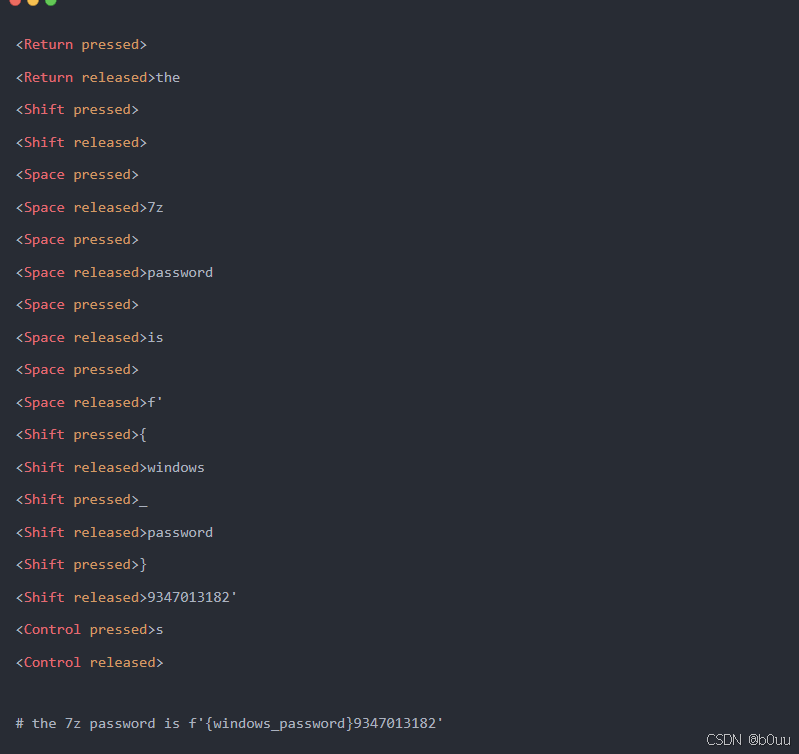
9347013182
再将密码和一开始的密钥拼接起来
babygirl2339347013182
解密flag.7z得到flagflag{fa32a0b2-dc26-41f9-a5cc-1a48ca7b2ddd}


 浙公网安备 33010602011771号
浙公网安备 33010602011771号