BUUCTF [XMAN2018排位赛]四道misc题汇总
XMAN2018的四道misc题在这里记录下
目录
[XMAN2018排位赛]通行证
a2FuYmJyZ2doamx7emJfX19ffXZ0bGFsbg==
base64
kanbbrgghjl{zb____}vtlaln
栅栏密码加密,每组7位
kzna{blnl_abj_lbh_trg_vg}
凯撒密码,移位13
xman{oyay_now_you_get_it}
[XMAN2018排位赛]file
先用volatility测试了下,提示没有推荐的操作系统
记录下文件挂载+extundelete恢复文件的操作
mount挂载镜像
挂载到mnt233文件夹下
mount 233.img mnt233
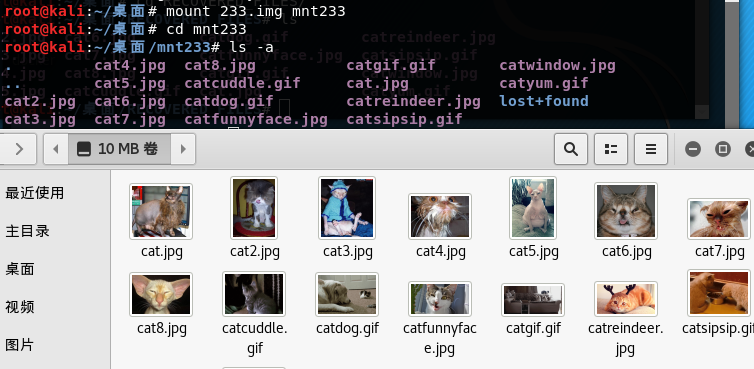
猫猫狗狗的照片,没啥东西
取消挂载
umount -a 233.img
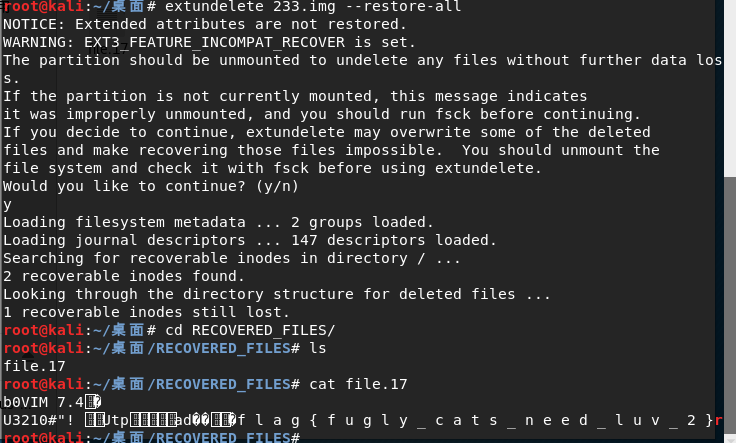
用extundelete恢复下删除的文件
extundelete恢复文件
恢复所有文件
extundelete 233.img --restore-all
在同目录生成RECOVERED_FILES文件夹,发现被删除的文件,得到flag
[XMAN2018排位赛]AutoKey
键盘流量
直接用UsbKeyboardDataHacker跑一下
python UsbKeyboardDataHacker.py attachment.pcapng
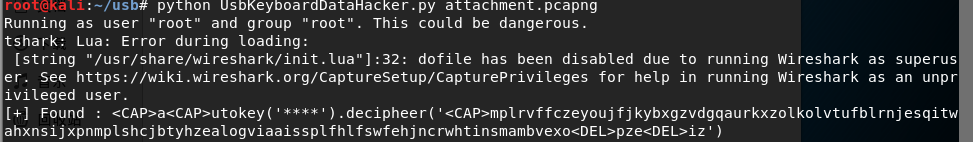
可以得知是autokey加密
密文
mplrvffczeyoujfjkybxgzvdgqaurkxzolkolvtufblrnjesqitwahxnsijxpnmplshcjbtyhzealogviaaissplfhlfswfehjncrwhtinsmambvexo<DEL>pze<DEL>iz
处理一下密文,把<DEL>前面字母的删去
处理后
mplrvffczeyoujfjkybxgzvdgqaurkxzolkolvtufblrnjesqitwahxnsijxpnmplshcjbtyhzealogviaaissplfhlfswfehjncrwhtinsmambvexpziz
autokey
爆破autokey使用方法看这篇文章里的内容
misc工具合集
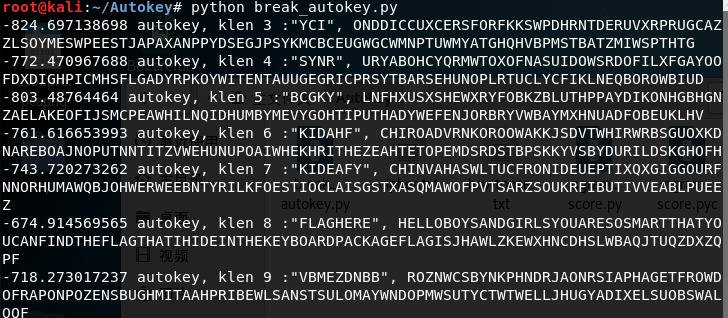
klen8得到可读的语句
HELLOBOYSANDGIRLSYOUARESOSMARTTHATYOUCANFINDTHEFLAGTHATIHIDEINTHEKEYBOARDPACKAGEFLAGISJHAWLZKEWXHNCDHSLWBAQJTUQZDXZQPF
flag为FLAGIS后面的部分
[XMAN2018排位赛]ppap
流量分析
分析流量包
TCP流6发现可疑信息
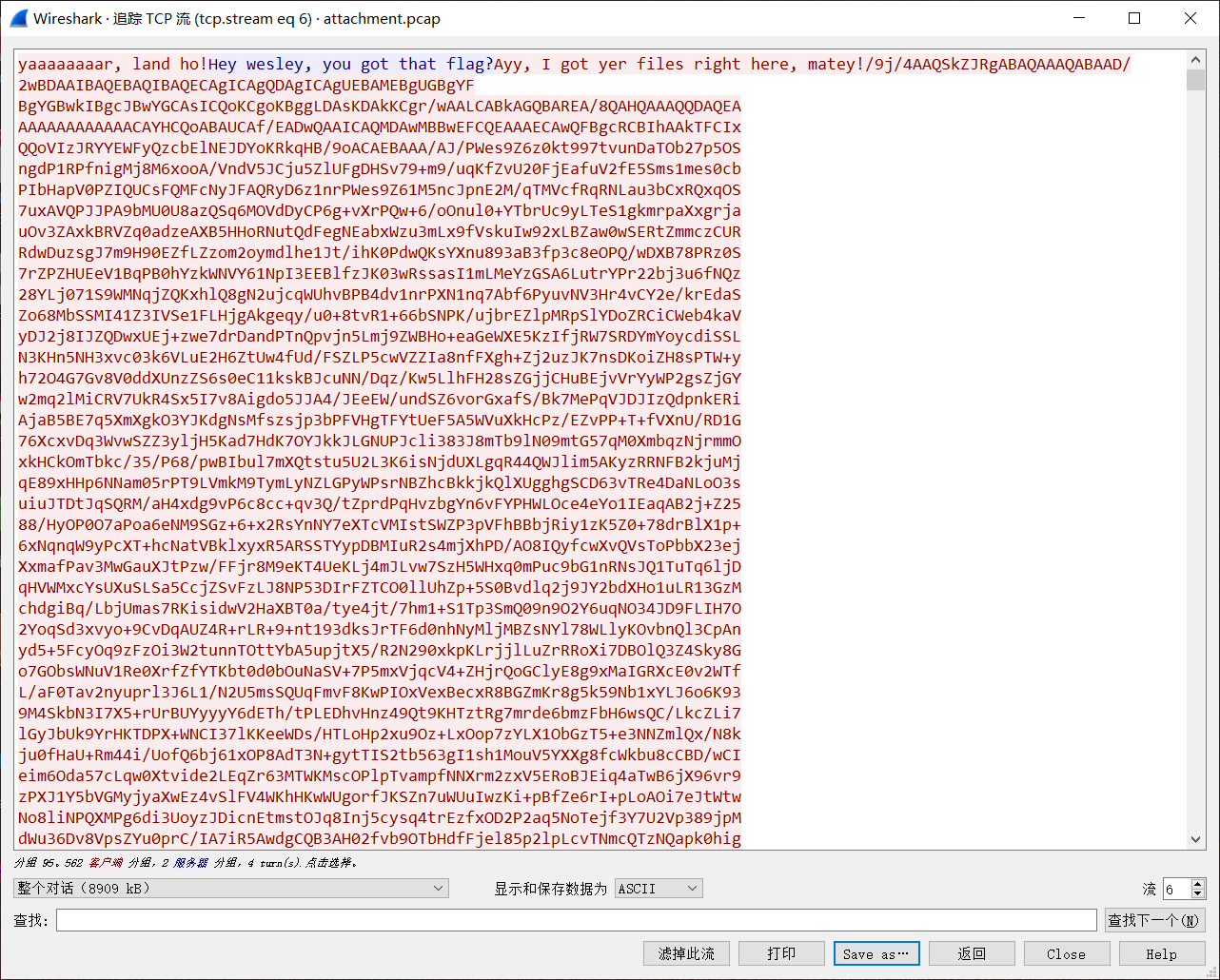
保存成origin.data下来去010editor分析。wireshark里很卡
文件分成了三个部分,分别用一句话和~~~~分割
yaaaaaaaar, land ho!Hey wesley, you got that flag?Ayy, I got yer files right here, matey!
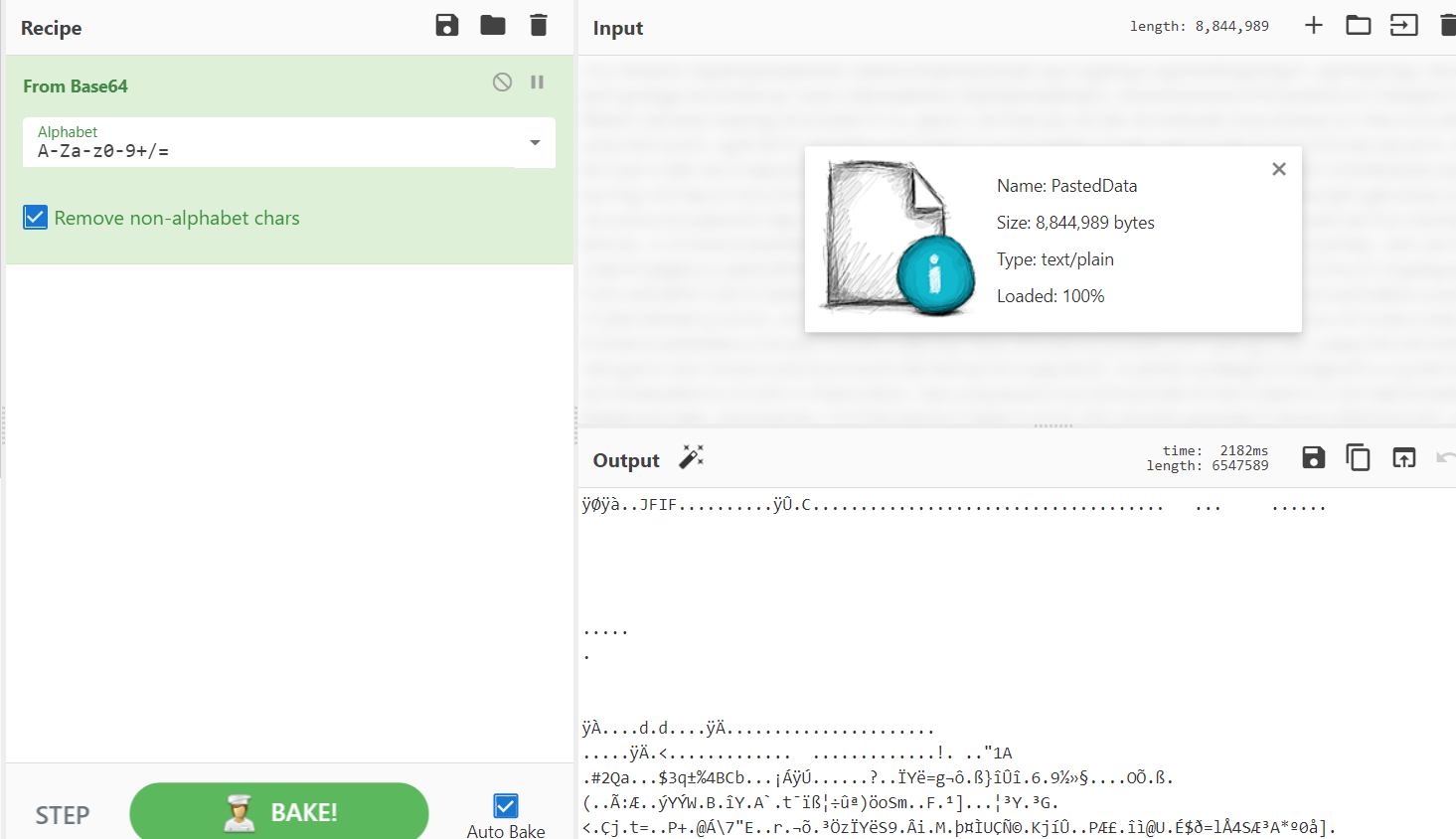
/9j/4AAQSkZJRgABAQAAAQABAAD/2wBDAAIBAQEBAQIBAQECAgICAgQDAgICAgUEBAMEBgUGBgYF......中间省略ANp1gR4ry3FNnC3T49fVNDgV7hQ66vYjtqfgWA4onj52Tx+P7+psawHHHOUlzw4qJsg//n1//9k=
↑↑↑解得jpg图片
~~~~
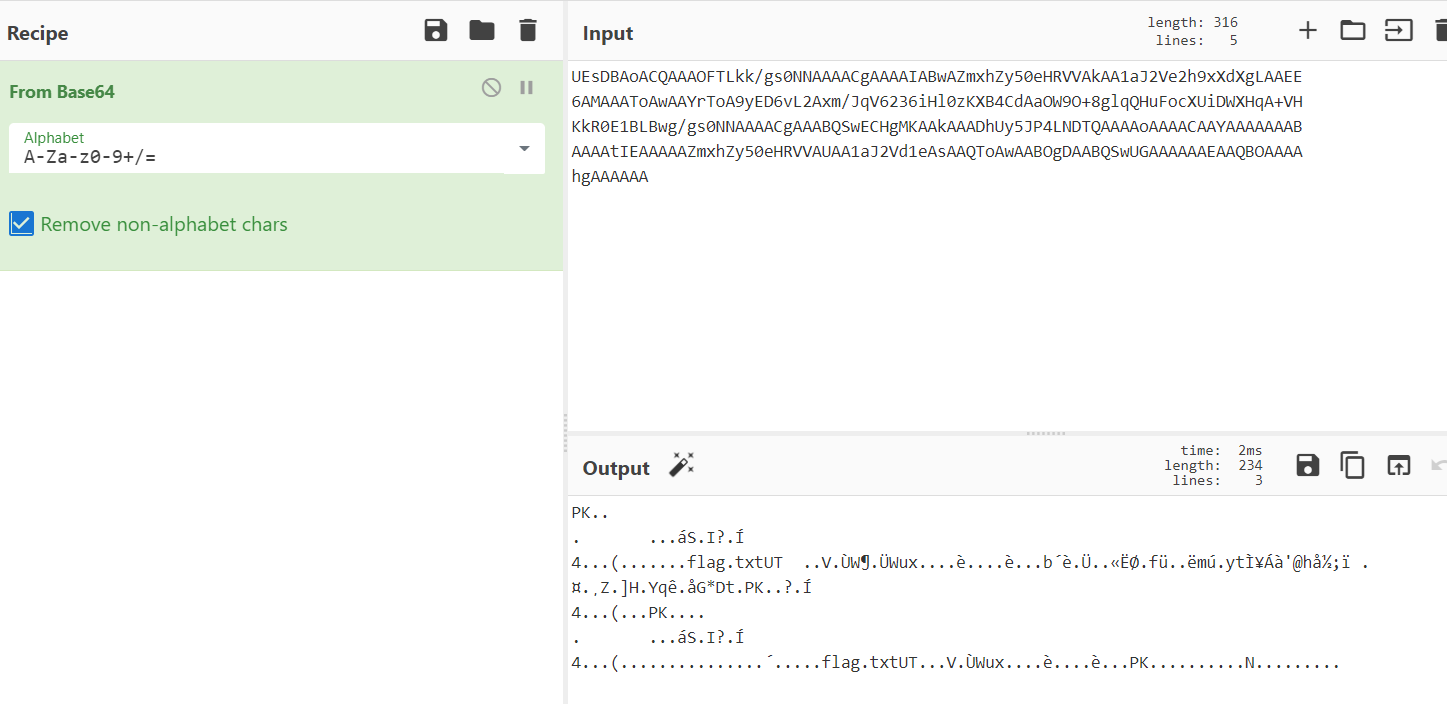
UEsDBAoACQAAAOFTLkk/gs0NNAAAACgAAAAIABwAZmxhZy50eHRVVAkAA1aJ2Ve2h9xXdXgLAAEE
6AMAAAToAwAAYrToA9yED6vL2Axm/JqV6236iHl0zKXB4CdAaOW9O+8glqQHuFocXUiDWXHqA+VH
KkR0E1BLBwg/gs0NNAAAACgAAABQSwECHgMKAAkAAADhUy5JP4LNDTQAAAAoAAAACAAYAAAAAAAB
AAAAtIEAAAAAZmxhZy50eHRVVAUAA1aJ2Vd1eAsAAQToAwAABOgDAABQSwUGAAAAAAEAAQBOAAAA
hgAAAAAA
↑↑↑解得zip文件
And here be the map to the booty!
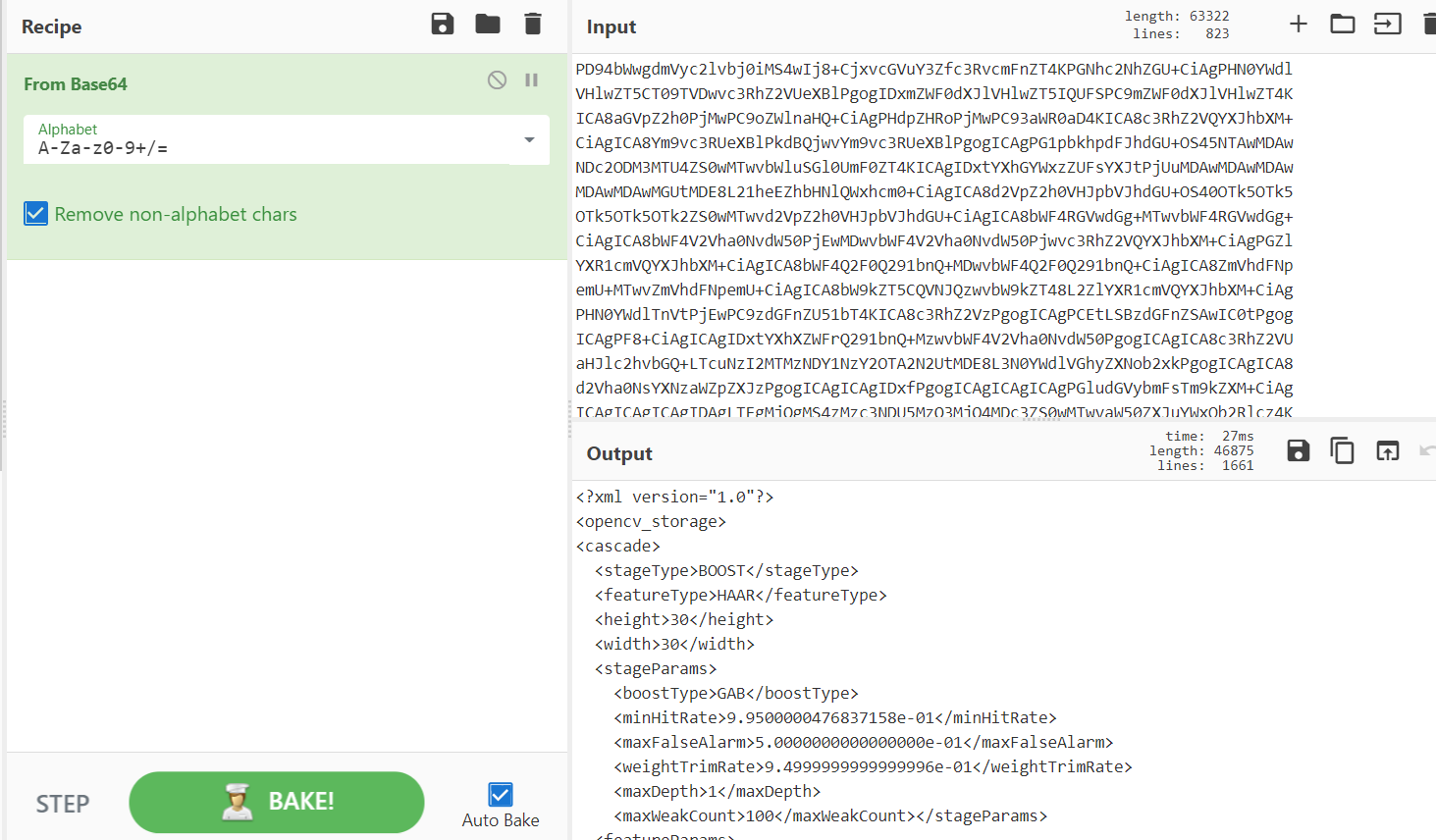
PD94bWwgdmVyc2lvbj0iMS4wIj8+CjxvcGVuY3Zfc3RvcmFnZT4KPGNhc2NhZGU+CiAgPHN0YWdl......中间省略ZT4KPC9vcGVuY3Zfc3RvcmFnZT4K
↑↑↑解得xml文档
I don't understand, this isn't even a ma-Yarrrr, the booty be buried by that which the map points to! (no spaces and no caps)Ayy, now I be off. But remember, the factor of scales be 1.02, and the neighborly sorts be limited to 50! Lastly, if ye sail the seven seas, you do be a pirate!
分别对其进行base64处理
jpg图片
xml文档
zip文件
做到这里做不动了。看了下原题,不是很理解,这边就记录到这里了
原题地址
https://github.com/krx/CTF-Writeups/tree/master/CSAW 16 Quals/for150 - Yaar Haar Fiddle Dee Dee
非预期
浏览博客的时候找到了这个网址
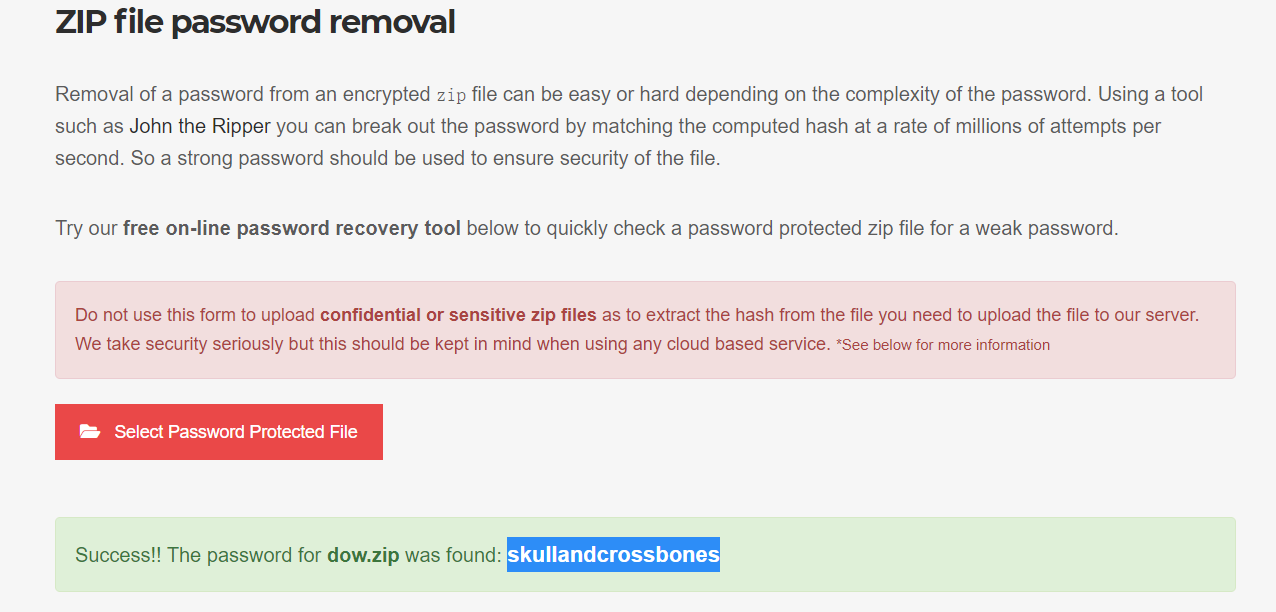
zip解密地址
速度非常快,不懂其解密的原理
试了下其他的压缩包,文件稍大一点(压缩了gif)就没反应了。
我试了下自己加密的几个文件,密码都很简单(88888888,admin,admin123)都无结果,猜测可能用的字典跑的,刚好skullandcrossbones在字典里。
还以为发现了甚么了不得的解密网站
只能说单纯为了flag罢了=。=没什么卵用
本博文仅限于博主个人学习和分享使用,请勿用于违法行为。如有侵权,请联系一定删除!


 浙公网安备 33010602011771号
浙公网安备 33010602011771号