FastStone Capture 11.0 记录
FastStone Capture 11.0 记录
目录
程序信息
PE32
操作系统: Windows(95)[I386, 32 位, GUI]
链接程序: Turbo Linker(2.25*,Delphi)[GUI32,signed]
编译器: Borland Delphi(6)[Enterprise]
语言: Object Pascal (Delphi)
签名工具: Windows Authenticode(2.0)[PKCS #7]
安装程序: Autorun Pro Enterprise II
(Heur)许可: Licensing[Strings]
附加: Binary[偏移=0x00742200,大小=0x2980]
证书: WinAuth(2.0)[PKCS #7]
分析工具:
IDR、
ida pro 9.0,插件DelphiHelpereset/DelphiHelper
注册验证流程
ida 反编译结果不一定准确,要结合汇编,特别是不定参数的函数。
注册按钮事件:TRegister_BntRegisterClick
int __usercall TRegister_BntRegisterClick@<eax>(int *TRegister_OBJ@<eax>, char *a2@<ebx>)
{
// [COLLAPSED LOCAL DECLARATIONS. PRESS NUMPAD "+" TO EXPAND]
v65[2] = &savedregs;
v65[1] = &loc_72AB31;
v65[0] = NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v65);
v64[2] = &savedregs;
v64[1] = &loc_72AA66;
v64[0] = NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v64);
LStrLAsg(&v127, (__int32)"(");
LStrLAsg(&v126, (__int32)").");
v3 = TRegister_OBJ[200];
WStrCatN(v137, 5);
WStrAsg(&v136, *(_DWORD *)(v3 + 56));
WStrFromLStr((int)&v124, v127);
WStrFromLStr((int)&v123, v126);
WStrCatN(v135, 3);
WStrFromLStr((int)&v122, v127);
WStrFromLStr((int)&v121, v126);
WStrCatN(v134, 3);
WStrFromLStr((int)&v120, v127);
WStrFromLStr((int)&v119, v126);
WStrCatN(v133, 3);
WStrFromLStr((int)&v118, v127);
WStrFromLStr((int)&v117, v126);
WStrCatN(v132, 3);
WStrFromLStr((int)&v116, v127);
WStrFromLStr((int)&v115, v126);
WStrCatN(v131, 3);
WStrFromLStr((int)&v114, v127);
WStrFromLStr((int)&v113, v126);
WStrCatN(v130, 3);
WStrFromLStr((int)&v112, v127);
WStrFromLStr((int)&v111, v126);
WStrCatN(v129, 3);
WStrCatN(v128, 6);
TTntEdit_GetText(TRegister_OBJ[193], (int)&v109);
Trim_0(v109, &v110);
LStrFromWStr(&v143, v110);
TTntEdit_GetText(TRegister_OBJ[193], (int)&v108);
Trim_0(v108, &v141);
TControl_GetText(TRegister_OBJ[195], &v106);
Trim(v106, &v107);
UpperCase(v107, &v139);
LStrClr(&v138);
v4 = LStrLen((int)v139) - 1;
if ( v4 >= 0 )
{
v125 = v4 + 1;
v3 = 0;
do
{
LOBYTE(a2) = v139[v3];
if ( (unsigned __int8)a2 >= 0x41u && (unsigned __int8)a2 <= 0x5Au )
{
LStrFromChar(v105, a2);
LStrCat(&v138, *(int *)v105);
}
if ( LStrLen(v138) == 5 || LStrLen(v138) == 11 || LStrLen(v138) == 17 )
LStrCat(&v138, (int)"-");
++v3;
--v125;
}
while ( v125 );
}
LStrLAsg((volatile __int32 *)&v140, v138);
if ( v143 || (WStrCmp((int)v141, 0), !v5) )
{
x_name_8E8850(v141, &v142);
WStrCmp((int)v141, 0);
if ( v5
|| sub_728E24((int)TRegister_OBJ, (int)v140)
|| sub_728ED4((int)TRegister_OBJ, (int)v143, (unsigned __int8)a2, (unsigned int)TRegister_OBJ, v3)
|| !(unsigned __int8)TRegister_x_do_check1_729B90((int)TRegister_OBJ, v142, v140)
|| !(unsigned __int8)x_do_check2_729C64((__int32)TRegister_OBJ, v142, (__int32)v140)
|| x_check3_729D38((int)TRegister_OBJ, (int)v140) < 1 )
{
if ( !v143
|| sub_728E24((int)TRegister_OBJ, (int)v140)
|| sub_728ED4((int)TRegister_OBJ, (int)v143, (unsigned __int8)a2, (unsigned int)TRegister_OBJ, v3)
|| !(unsigned __int8)TRegister_x_do_check1_729B90((int)TRegister_OBJ, v143, v140)
|| !(unsigned __int8)x_do_check2_729C64((__int32)TRegister_OBJ, v143, (__int32)v140)
|| x_check3_729D38((int)TRegister_OBJ, (int)v140) < 1 )
{
Handle = (HWND)TWinControl_GetHandle(0);
sub_8DEE44(*(int *)v128, 2u, gvar_0072AB78, v61, Handle, -1, 0, 0);
__writefsdword(0, v30);
goto LABEL_56;
}
v9 = x_check3_729D38((int)TRegister_OBJ, (int)v140);
v10 = v9;
if ( v9 > 1 )
{
switch ( v9 )
{
case 1111:
v40 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v84, (int)v143);
WStrCat3(&v83, *(_DWORD *)v137, *(_DWORD *)v134, v84);
sub_8D3B38(v83, v16, 0, 0, 0, (wchar_t *)&v85);
sub_8DEE44(v85, 2u, gvar_0072AB78, v55, v40, -1, 0, 0);
break;
case 4997:
v41 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v81, (int)v143);
WStrCat3(&v80, *(_DWORD *)v137, *(_DWORD *)v132, v81);
sub_8D3B38(v80, v17, 0, 0, 0, (wchar_t *)&v82);
sub_8DEE44(v82, 2u, gvar_0072AB78, v56, v41, -1, 0, 0);
break;
case 4998:
v42 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v78, (int)v143);
WStrCat3(&v77, *(_DWORD *)v137, *(_DWORD *)v131, v78);
sub_8D3B38(v77, v18, 0, 0, 0, (wchar_t *)&v79);
sub_8DEE44(v79, 2u, gvar_0072AB78, v57, v42, -1, 0, 0);
break;
case 4999:
v43 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v75, (int)v143);
WStrCat3(&v74, *(_DWORD *)v137, *(_DWORD *)v130, v75);
sub_8D3B38(v74, v19, 0, 0, 0, (wchar_t *)&v76);
sub_8DEE44(v76, 2u, gvar_0072AB78, v58, v43, -1, 0, 0);
break;
default:
if ( v9 >= 5000 )
{
v45 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v67, (int)v143);
WStrCat3(&v66, *(_DWORD *)v137, *(_DWORD *)v129, v67);
sub_8D3B38(v66, v21, 0, 0, 0, (wchar_t *)&v68);
sub_8DEE44(v68, 2u, gvar_0072AB78, v60, v45, -1, 0, 0);
}
else
{
v44 = (HWND)TWinControl_GetHandle(0);
IntToStr(v10, &v71);
WStrFromLStr((int)&v72, v71);
v20 = v72;
WStrFromLStr((int)&v70, (int)v143);
WStrCat3(&v69, *(_DWORD *)v137, *(_DWORD *)v133, v70);
sub_8D3B38(v69, v13, v20, 0, 0, (wchar_t *)&v73);
sub_8DEE44(v73, 2u, gvar_0072AB78, v59, v44, -1, 0, 0);
}
break;
}
}
else
{
v39 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v87, (int)v143);
WStrCat3(&v86, *(_DWORD *)v137, *(_DWORD *)v135, v87);
sub_8D3B38(v86, v15, 0, 0, 0, (wchar_t *)&v88);
sub_8DEE44(v88, 2u, gvar_0072AB78, v54, v39, -1, 0, 0);
}
LStrAsg(*((_DWORD *)*TMainPanel_0090A5DC + 539) + 48, v143);
WStrClr(*((_DWORD *)*TMainPanel_0090A5DC + 539) + 52);
LStrAsg(*((_DWORD *)*TMainPanel_0090A5DC + 539) + 56, v140);
*((_BYTE *)*TMainPanel_0090A5DC + 2108) = 1;
sub_787CB0((int)*TMainPanel_0090A5DC, (unsigned __int8)a2, (int)TRegister_OBJ, v10);
sub_78B280((int)*TMainPanel_0090A5DC);
TCustomForm_Close(TRegister_OBJ);
}
else
{
v7 = x_check3_729D38((int)TRegister_OBJ, (int)v140);
v8 = v7;
if ( v7 > 1 )
{
switch ( v7 )
{
case 1111:
v33 = (HWND)TWinControl_GetHandle(0);
WStrCat3(&v101, *(_DWORD *)v137, *(_DWORD *)v134, &v102);
sub_8D3B38(v101, (int)v141, 0, 0, 0, v23);
sub_8DEE44(v102, 2u, gvar_0072AB78, v48, v33, -1, 0, 0);
break;
case 4997:
v34 = (HWND)TWinControl_GetHandle(0);
WStrCat3(&v99, *(_DWORD *)v137, *(_DWORD *)v132, &v100);
sub_8D3B38(v99, (int)v141, 0, 0, 0, v24);
sub_8DEE44(v100, 2u, gvar_0072AB78, v49, v34, -1, 0, 0);
break;
case 4998:
v35 = (HWND)TWinControl_GetHandle(0);
WStrCat3(&v97, *(_DWORD *)v137, *(_DWORD *)v131, &v98);
sub_8D3B38(v97, (int)v141, 0, 0, 0, v25);
sub_8DEE44(v98, 2u, gvar_0072AB78, v50, v35, -1, 0, 0);
break;
case 4999:
v36 = (HWND)TWinControl_GetHandle(0);
WStrCat3(&v95, *(_DWORD *)v137, *(_DWORD *)v130, &v96);
sub_8D3B38(v95, (int)v141, 0, 0, 0, v26);
sub_8DEE44(v96, 2u, gvar_0072AB78, v51, v36, -1, 0, 0);
break;
default:
if ( v7 >= 5000 )
{
v38 = (HWND)TWinControl_GetHandle(0);
WStrCat3(&v89, *(_DWORD *)v137, *(_DWORD *)v129, &v90);
sub_8D3B38(v89, (int)v141, 0, 0, 0, v27);
sub_8DEE44(v90, 2u, gvar_0072AB78, v53, v38, -1, 0, 0);
}
else
{
v37 = (HWND)TWinControl_GetHandle(0);
IntToStr(v8, &v92);
WStrFromLStr((int)&v93, v92);
WStrCat3(&v91, *(_DWORD *)v137, *(_DWORD *)v133, v93);
sub_8D3B38(v91, (int)v141, v14, 0, 0, (wchar_t *)&v94);
sub_8DEE44(v94, 2u, gvar_0072AB78, v52, v37, -1, 0, 0);
}
break;
}
}
else
{
v32 = (HWND)TWinControl_GetHandle(0);
WStrCat3(&v103, *(_DWORD *)v137, *(_DWORD *)v135, &v104);
sub_8D3B38(v103, (int)v141, 0, 0, 0, v22);
sub_8DEE44(v104, 2u, gvar_0072AB78, v47, v32, -1, 0, 0);
}
LStrClr((_DWORD *)(*((_DWORD *)*TMainPanel_0090A5DC + 539) + 48));
WStrAsg(*((_DWORD *)*TMainPanel_0090A5DC + 539) + 52, v141);
LStrAsg(*((_DWORD *)*TMainPanel_0090A5DC + 539) + 56, v140);
*((_BYTE *)*TMainPanel_0090A5DC + 2108) = 1;
sub_787CB0((int)*TMainPanel_0090A5DC, (unsigned __int8)a2, (int)TRegister_OBJ, v8);
sub_78B280((int)*TMainPanel_0090A5DC);
TCustomForm_Close(TRegister_OBJ);
}
__writefsdword(0, v29);
goto LABEL_56;
}
v6 = (HWND)TWinControl_GetHandle(0);
sub_8DEE44(v136, 2u, gvar_0072AB78, v46, v6, -1, 0, 0);
(*(void (__fastcall **)(int))(*(_DWORD *)TRegister_OBJ[193] + 192))(TRegister_OBJ[193]);
__writefsdword(0, v28);
LABEL_56:
__writefsdword(0, v31);
WStrArrayClr(&v66, 5);
LStrClr(&v71);
WStrArrayClr(&v72, 20);
LStrClr(&v92);
WStrArrayClr(&v93, 12);
LStrClr(v105);
LStrClr(&v106);
LStrClr(&v107);
WStrArrayClr(&v108, 17);
LStrArrayClr(&loc_72AB3B);
WStrArrayClr(v128, 10);
LStrArrayClr(v62);
WStrClr(&v141);
return LStrArrayClr(v63);
}
校验一:TRegister_x_do_check1_729B90
char *__fastcall TRegister_x_do_check1_729B90(int TRegister_OBJ, _BYTE *name, char *code)
{
char *v3; // ebx
unsigned int v6[5]; // [esp-Ch] [ebp-24h] BYREF
_BYTE *v7; // [esp+8h] [ebp-10h] BYREF
_BYTE *v8; // [esp+Ch] [ebp-Ch] BYREF
char *v9; // [esp+10h] [ebp-8h]
_BYTE *v10; // [esp+14h] [ebp-4h]
int savedregs; // [esp+18h] [ebp+0h] BYREF
v3 = 0;
v7 = 0;
v8 = 0;
v9 = code;
v10 = name;
LStrAddRef((int)name);
LStrAddRef((int)v9);
v6[2] = (unsigned int)&savedregs;
v6[1] = (unsigned int)&loc_729C53;
v6[0] = (unsigned int)NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v6);
if ( X_CHECK1_7292D0(TRegister_OBJ, v10, v9, 0)
|| (x_word_and_number_8DA638((int)v10, (int *)&v8, 0), X_CHECK1_7292D0(TRegister_OBJ, v8, v9, 0)) )
{
LOBYTE(v3) = 1;
}
else
{
v3 = 0;
}
if ( !(_BYTE)v3 )
{
if ( X_CHECK1_7292D0(TRegister_OBJ, v10, v9, 1)
|| (x_word_and_number_8DA638((int)v10, (int *)&v7, v3), X_CHECK1_7292D0(TRegister_OBJ, v7, v9, 1)) )
{
LOBYTE(v3) = 1;
}
else
{
v3 = 0;
}
}
__writefsdword(0, v6[0]);
LStrArrayClr(&loc_729C5A);
return v3;
}
X_CHECK_7292D0
char __fastcall X_CHECK_7292D0(__int32 TRegister_OBJ, _BYTE *name, char *code, char type)
{
// [COLLAPSED LOCAL DECLARATIONS. PRESS NUMPAD "+" TO EXPAND]
v45 = _InterlockedExchange(&TRegister, (__int32)code);
v46 = name;
TRegister = TRegister_OBJ;
LStrAddRef((int)name);
LStrAddRef(v45);
v18 = &savedregs;
v17[1] = (unsigned int)&loc_7296BF;
v17[0] = (unsigned int)NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v17);
v16[2] = (unsigned int)&savedregs;
v16[1] = (unsigned int)&loc_72965E;
v16[0] = (unsigned int)NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v16);
v44 = 0;
UpperCase(v46, &name_upper_1);
Trim(v45, &v37);
UpperCase(v37, &raw_code_upper);
if ( name_upper_1 && raw_code_upper )
{
if ( LStrLen((int)raw_code_upper) == 23 ) // 4*5+3
{
LStrCopy((int)raw_code_upper, 1, 5, (int)&v36);
LStrCopy((int)raw_code_upper, 7, 5, (int)&v35);
LStrCopy((int)raw_code_upper, 13, 5, (int)&v34);
LStrCopy((int)raw_code_upper, 19, 5, (int)&v33);
v15 = v33;
// raw_code_upper
LStrCatN(&raw_code_upper, 4);
}
if ( LStrLen((int)name_upper_1) >= 3 && LStrLen((int)raw_code_upper) == 20 )
{
LStrCopy((int)raw_code_upper, 1, 8, (int)&part1);
LStrClr(&v42);
v4 = 1;
v5 = 1;
v6 = 1;
while ( v4 <= LStrLen((int)part1) || v5 <= LStrLen((int)name_upper_1) )
{
// part1和name 交叉
if ( v6 % 2 )
{
if ( v5 <= LStrLen((int)name_upper_1) )
{
v8 = name_upper_1;
LOBYTE(v8) = name_upper_1[v5 - 1];
LStrFromChar(v31, v8);
LStrCat(&v42, *(int *)v31);
++v5;
}
}
else if ( v4 <= LStrLen((int)part1) )
{
v7 = part1;
LOBYTE(v7) = part1[v4 - 1];
LStrFromChar(v32, v7);
LStrCat(&v42, *(int *)v32);
++v4;
}
++v6;
}
// CODE:007294B5 push offset aMe4t6cblv ; "me4T6cBLV"
// CODE:007294BA push [ebp+part1] ; int
// CODE:007294BD push offset aCpcwxrvcjz30pk ; "CpCwxrvCJZ30pKLu8Svxjhnhut437glCpofVssn"...
// CODE:007294C2 lea eax, [ebp+var_48] ; char **
LStrCatN(&v30, 3); //
// me4T6cBLV
// TDCP_blowfish
sub_718EC4(*(_BYTE **)(TRegister + 0x2F8), (int)v30, (int)VMT_71BA08_TDCP_sha1);
if ( type )
{
WStrFromLStr((int)&v27, (int)part1);
// CODE:0077FD6D add eax, 840h ; 'TMainPanel.?f840:WideString'
// CODE:0077FD72 mov edx, offset a96338 ; "96338"
// CODE:0077FD77 call @WStrAsg
// CODE:0077FD7C mov eax, [ebp+var_4]
// CODE:0077FD7F add eax, 844h ; 'TMainPanel.?f844:WideString'
// CODE:0077FD84 mov edx, offset a96888 ; "96888"
// CODE:0077FD89 call @WStrAsg
WStrFromLStr((int)&v26, v42); // 96888
v14 = (char *)v26;
// push part1
// push 96xx8
// push v44
WStrCatN(v28, 3);
LStrFromWStr(&v29, *(_DWORD *)v28);
// TDCP_idea
sub_718EC4(*(_BYTE **)(TRegister + 0x2F4), v29, (int)VMT_71D038_TDCP_sha512);
}
else
{
WStrFromLStr((int)&v23, (int)part1);
WStrFromLStr((int)&v22, v42); // 96338
v14 = v22;
WStrCatN(v24, 3);
LStrFromWStr(&v25, *(_DWORD *)v24);
// TDCP_idea
sub_718EC4(*(_BYTE **)(TRegister + 0x2F4), v25, (int)VMT_71D038_TDCP_sha512);
}
// TDCP_blowfish
(*(void (__fastcall **)(_DWORD, int, char **))(**(_DWORD **)(TRegister + 0x2F8) + 84))(
*(_DWORD *)(TRegister + 0x2F8),
v42,
&v40);
// TDCP_idea
(*(void (__fastcall **)(_DWORD, char *, __int32 *))(**(_DWORD **)(TRegister + 0x2F4) + 84))(
*(_DWORD *)(TRegister + 0x2F4),
v40,
&v21);
LStrLAsg((volatile __int32 *)&v40, v21);
LStrClr(&calc);
v9 = LStrLen((int)v40);
if ( v9 > 0 )
{
v10 = 1;
do
{
if ( (unsigned __int8)v40[v10 - 1] >= 'A' && (unsigned __int8)v40[v10 - 1] <= 'Z' && LStrLen(calc) < 8 )
{
v11 = v40;
LOBYTE(v11) = v40[v10 - 1];
LStrFromChar(v20, v11);
LStrCat(&calc, *(int *)v20);
}
++v10;
--v9;
}
while ( v9 );
}
LStrCopy((int)raw_code_upper, 9, 8, (int)&v19);
LStrCmp(calc, v19);
if ( v12 )
v44 = 1;
__writefsdword(0, (unsigned int)v14);
}
else
{
__writefsdword(0, (unsigned int)v15);
}
}
else
{
__writefsdword(0, v16[0]);
}
__writefsdword(0, v17[0]);
LStrArrayClr(&loc_7296C6);
WStrArrayClr(&v22, 3);
LStrClr(&v25);
WStrArrayClr(&v26, 3);
LStrArrayClr(v18);
LStrArrayClr(v18);
return v44;
}
使用的加密函数:
密码库:DcPCryptV2
算法:idea、blowfish
采用hash计算得到key,
procedure TDCP_cipher.InitStr(const Key: RawByteString; HashType: TDCP_hashclass);
var
Hash: TDCP_hash;
Digest: pointer;
begin
if fInitialized then
Burn;
try
GetMem(Digest, HashType.GetHashSize div 8);
Hash := HashType.Create(Self);
Hash.Init;
Hash.UpdateStr(Key);
Hash.Final(Digest^);
Hash.Free;
if MaxKeySize < HashType.GetHashSize then
begin
Init(Digest^, MaxKeySize, nil);
end
else
begin
Init(Digest^, HashType.GetHashSize, nil);
end;
FillChar(Digest^, HashType.GetHashSize div 8, $FF);
FreeMem(Digest);
except
raise EDCP_cipher.Create
('Unable to allocate sufficient memory for hash digest');
end;
end;
加密结果base64编码
function TDCP_cipher.EncryptString(const Str: RawByteString): RawByteString;
var
lLength : integer;
begin
{$IFDEF NEXTGEN}
Result.SetLength(AnsiLength(Str));
Encrypt(Str.GetBuffer[0], Result.GetBuffer[0], AnsiLength(Str));
{$ELSE}
SetLength(Result, Length(Str));
Encrypt(Str[1], Result[1], Length(Str));
{$ENDIF}
Result := Base64EncodeStr(Result);
end;
function TDCP_cipher.DecryptString(const Str: RawByteString): RawByteString;
begin
Result := Base64DecodeStr(Str);
{$IFDEF NEXTGEN}
Decrypt(Result.GetBuffer[0], Result.GetBuffer[0], AnsiLength(Result));
{$ELSE}
Decrypt(Result[1], Result[1], Length(Result));
{$ENDIF}
end;
加解密采用cfb8 分组模式
procedure TDCP_blockcipher64.EncryptCFB8bit(const Indata; var Outdata; Size: longword);
var
i: longword;
p1, p2: Pbyte;
Temp: array[0..7] of byte;
begin
if not fInitialized then
raise EDCP_blockcipher.Create('Cipher not initialized');
p1:= @Indata;
p2:= @Outdata;
FillChar(Temp, SizeOf(Temp), 0);
for i:= 1 to Size do
begin
EncryptECB(CV,Temp);
p2^:= p1^ xor Temp[0];
Move(CV[1],CV[0],8-1);
CV[7]:= p2^;
Inc(p1);
Inc(p2);
end;
end;
procedure TDCP_blockcipher64.DecryptCFB8bit(const Indata; var Outdata; Size: longword);
var
i: longword;
p1, p2: Pbyte;
TempByte: byte;
Temp: array[0..7] of byte;
begin
if not fInitialized then
raise EDCP_blockcipher.Create('Cipher not initialized');
p1:= @Indata;
p2:= @Outdata;
FillChar(Temp, SizeOf(Temp), 0);
for i:= 1 to Size do
begin
TempByte:= p1^;
EncryptECB(CV,Temp);
p2^:= p1^ xor Temp[0];
Move(CV[1],CV[0],8-1);
CV[7]:= TempByte;
Inc(p1);
Inc(p2);
end;
end;
校验二:x_do_check_2_729C64
char *__fastcall x_do_check_2_729C64(__int32 a1, _BYTE *a2, __int32 a3)
{
char *v3; // ebx
unsigned int v6[5]; // [esp-Ch] [ebp-24h] BYREF
_BYTE *v7; // [esp+8h] [ebp-10h] BYREF
_BYTE *v8; // [esp+Ch] [ebp-Ch] BYREF
__int32 v9; // [esp+10h] [ebp-8h]
_BYTE *v10; // [esp+14h] [ebp-4h]
int savedregs; // [esp+18h] [ebp+0h] BYREF
v3 = 0;
v7 = 0;
v8 = 0;
v9 = a3;
v10 = a2;
LStrAddRef((int)a2);
LStrAddRef(v9);
v6[2] = (unsigned int)&savedregs;
v6[1] = (unsigned int)&loc_729D27;
v6[0] = (unsigned int)NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v6);
if ( x_check_2_72975C(a1, v10, v9, 0)
|| (x_word_and_number_8DA638((int)v10, (int *)&v8, 0), x_check_2_72975C(a1, v8, v9, 0)) )
{
LOBYTE(v3) = 1;
}
else
{
v3 = 0;
}
if ( !(_BYTE)v3 )
{
if ( x_check_2_72975C(a1, v10, v9, 1)
|| (x_word_and_number_8DA638((int)v10, (int *)&v7, v3), x_check_2_72975C(a1, v7, v9, 1)) )
{
LOBYTE(v3) = 1;
}
else
{
v3 = 0;
}
}
__writefsdword(0, v6[0]);
LStrArrayClr(&loc_729D2E);
return v3;
}
check_2_72975C
char __fastcall check_2_72975C(__int32 a1, _BYTE *a2, __int32 a3, char a4)
{
// [COLLAPSED LOCAL DECLARATIONS. PRESS NUMPAD "+" TO EXPAND]
v48 = _InterlockedExchange(&v50, a3);
v49 = a2;
v50 = a1;
LStrAddRef((int)a2);
LStrAddRef(v48);
v22[2] = &savedregs;
v22[1] = &loc_729B1B;
v22[0] = NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v22);
v21 = &savedregs;
v20 = &loc_729ABA;
ExceptionList = NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)&ExceptionList);
UpperCase(v49, &v44);
Trim(v48, &v40);
UpperCase(v40, &v41);
if ( LStrLen((int)v41) == 23 )
{
LStrCopy((int)v41, 1, 5, (int)&v39);
v18 = v39;
LStrCopy((int)v41, 7, 5, (int)&v38);
LStrCopy((int)v41, 13, 5, (int)&v37);
LStrCopy((int)v41, 19, 5, (int)&v36);
v17 = v36;
LStrCatN(&v41, 4);
}
if ( LStrLen((int)v44) >= 3 && LStrLen((int)v41) == 20 )
{
LStrCopy((int)v41, 1, 8, (int)&v46);
LStrClr(&v45);
v4 = 1;
v5 = 1;
v6 = 1;
while ( v4 <= LStrLen((int)v46) || v5 <= LStrLen((int)v44) )
{
if ( v6 % 2 )
{
if ( v5 <= LStrLen((int)v44) )
{
v8 = v44;
LOBYTE(v8) = v44[v5 - 1];
LStrFromChar(v34, v8);
LStrCat(&v45, *(int *)v34);
++v5;
}
}
else if ( v4 <= LStrLen((int)v46) )
{
v7 = v46;
LOBYTE(v7) = v46[v4 - 1];
LStrFromChar(v35, (char *)v7);
LStrCat(&v45, *(int *)v35);
++v4;
}
++v6;
}
sub_718EC4(
*(_BYTE **)(v50 + 760),
(int)"09232849248398340903834873297239340547237623242043324398489390309284343843223493299435",
(int)VMT_71D038_TDCP_sha512);
if ( a4 )
{
WStrFromLStr((int)&v31, (int)v46);
WStrFromLStr((int)&v30, v45);
v16 = v30;
WStrCatN(v32, 3);
LStrFromWStr(&v33, *(_DWORD *)v32);
sub_718EC4(*(_BYTE **)(v50 + 756), v33, (int)VMT_71BA08_TDCP_sha1);
}
else
{
WStrFromLStr((int)&v27, (int)v46);
WStrFromLStr((int)&v26, v45);
v16 = v26;
WStrCatN(v28, 3);
LStrFromWStr(&v29, *(_DWORD *)v28);
sub_718EC4(*(_BYTE **)(v50 + 756), v29, (int)VMT_71BA08_TDCP_sha1);
}
v9 = *v46 - '2';
if ( v9 >= 0 )
{
v10 = v9 + 1;
do
{
(*(void (__fastcall **)(_DWORD, int, char **))(**(_DWORD **)(v50 + 756) + 84))(
*(_DWORD *)(v50 + 756),
v45,
&v43);
--v10;
}
while ( v10 );
}
(*(void (__fastcall **)(_DWORD, char *, __int32 *))(**(_DWORD **)(v50 + 760) + 84))(
*(_DWORD *)(v50 + 760),
v43,
&v25);
LStrLAsg((volatile __int32 *)&v43, v25);
LStrClr(&v42);
v11 = LStrLen((int)v43);
if ( v11 > 0 )
{
v12 = 1;
do
{
if ( (unsigned __int8)v43[v12 - 1] >= 0x41u && (unsigned __int8)v43[v12 - 1] <= 0x5Au && LStrLen(v42) < 4 )
{
v13 = v43;
LOBYTE(v13) = v43[v12 - 1];
LStrFromChar(v24, v13);
LStrCat(&v42, *(int *)v24);
}
++v12;
--v11;
}
while ( v11 );
}
LStrCopy((int)v41, 17, 4, (int)&v23);
LStrCmp(v42, v23);
if ( v14 )
v47 = 1;
__writefsdword(0, v16);
}
else
{
__writefsdword(0, (unsigned int)v17);
}
__writefsdword(0, v18);
LStrArrayClr(&loc_729B22);
WStrArrayClr(&v26, 3);
LStrClr(&v29);
WStrArrayClr(&v30, 3);
LStrArrayClr(v20);
LStrArrayClr(v20);
return v47;
}
校验三:x_check3_729D38
int __fastcall x_check3_729D38(int a1, int a2)
{
_DWORD *v3; // [esp-44h] [ebp-94h]
unsigned int v4; // [esp-38h] [ebp-88h]
_DWORD v5[3]; // [esp-34h] [ebp-84h] BYREF
_DWORD *v6; // [esp-28h] [ebp-78h]
int v7; // [esp-24h] [ebp-74h]
int v8; // [esp-20h] [ebp-70h]
unsigned int v9; // [esp-1Ch] [ebp-6Ch]
_DWORD v10[3]; // [esp-18h] [ebp-68h] BYREF
_DWORD v11[6]; // [esp-Ch] [ebp-5Ch] BYREF
unsigned __int8 *ct2; // [esp+Ch] [ebp-44h] BYREF
_DWORD *t_2; // [esp+10h] [ebp-40h] BYREF
unsigned __int8 *ct6; // [esp+14h] [ebp-3Ch] BYREF
int t_6; // [esp+18h] [ebp-38h] BYREF
unsigned __int8 *ct8; // [esp+1Ch] [ebp-34h] BYREF
int t_8; // [esp+20h] [ebp-30h] BYREF
unsigned __int8 *ct4; // [esp+24h] [ebp-2Ch] BYREF
unsigned int t_4; // [esp+28h] [ebp-28h] BYREF
_DWORD *v20; // [esp+2Ch] [ebp-24h] BYREF
int v21; // [esp+30h] [ebp-20h] BYREF
int v22; // [esp+34h] [ebp-1Ch] BYREF
unsigned int v23; // [esp+38h] [ebp-18h] BYREF
_BYTE *v24; // [esp+3Ch] [ebp-14h] BYREF
char *rowcode; // [esp+40h] [ebp-10h] BYREF
char *v26; // [esp+44h] [ebp-Ch] BYREF
int v27; // [esp+48h] [ebp-8h]
int v28; // [esp+4Ch] [ebp-4h] BYREF
int savedregs; // [esp+50h] [ebp+0h] BYREF
v28 = a2;
LStrAddRef(a2);
v11[2] = &savedregs;
v11[1] = &loc_729F3E;
v11[0] = NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v11);
v10[2] = &savedregs;
v10[1] = &loc_729F11;
v10[0] = NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v10);
v27 = 0;
Trim(v28, &v24);
UpperCase(v24, &rowcode);
if ( LStrLen((int)rowcode) == 23 )
{
LStrCopy((int)rowcode, 1, 5, (int)&v23);
v9 = v23;
LStrCopy((int)rowcode, 7, 5, (int)&v22);
v8 = v22;
LStrCopy((int)rowcode, 13, 5, (int)&v21);
v7 = v21;
LStrCopy((int)rowcode, 19, 5, (int)&v20);
v6 = v20;
// 第1,3,5,7,,(0索引 中偶数位,0,2,4,6)
LStrCatN(&rowcode, 4);
}
if ( LStrLen((int)rowcode) == 20 )
{
v5[2] = &savedregs;
v5[1] = &loc_729EFD;
v5[0] = NtCurrentTeb()->NtTib.ExceptionList;
__writefsdword(0, (unsigned int)v5);
LStrCopy((int)rowcode, 4, 1, (int)&ct4);
IntToStr(*ct4 - 'M', &t_4);
v4 = t_4;
LStrCopy((int)rowcode, 8, 1, (int)&ct8);
IntToStr(*ct8 - 'D', &t_8);
LStrCopy((int)rowcode, 6, 1, (int)&ct6);
IntToStr(*ct6 - 'I', &t_6);
LStrCopy((int)rowcode, 2, 1, (int)&ct2);
IntToStr(*ct2 - 'O', &t_2);
v3 = t_2;
LStrCatN(&v26, 4);
v27 = StrToInt(v26);
__writefsdword(0, (unsigned int)v3);
__writefsdword(0, v4);
}
else
{
__writefsdword(0, (unsigned int)v6);
}
__writefsdword(0, v9);
LStrArrayClr(&loc_729F45);
LStrClr(&v28);
return v27;
}
根据结果确定许可类型
v9 = x_check3_729D38((int)TRegister_OBJ, (int)v140);
v10 = v9;
if ( v9 > 1 )
{
switch ( v9 )
{
case 1111:
v40 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v84, (int)v143);
WStrCat3(&v83, *(_DWORD *)v137, *(_DWORD *)v134, v84);
sub_8D3B38(v83, v16, 0, 0, 0, (wchar_t *)&v85);
sub_8DEE44(v85, 2u, gvar_0072AB78, v55, v40, -1, 0, 0);
break;
case 4997:
v41 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v81, (int)v143);
WStrCat3(&v80, *(_DWORD *)v137, *(_DWORD *)v132, v81);
sub_8D3B38(v80, v17, 0, 0, 0, (wchar_t *)&v82);
sub_8DEE44(v82, 2u, gvar_0072AB78, v56, v41, -1, 0, 0);
break;
case 4998:
v42 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v78, (int)v143);
WStrCat3(&v77, *(_DWORD *)v137, *(_DWORD *)v131, v78);
sub_8D3B38(v77, v18, 0, 0, 0, (wchar_t *)&v79);
sub_8DEE44(v79, 2u, gvar_0072AB78, v57, v42, -1, 0, 0);
break;
case 4999:
v43 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v75, (int)v143);
WStrCat3(&v74, *(_DWORD *)v137, *(_DWORD *)v130, v75);
sub_8D3B38(v74, v19, 0, 0, 0, (wchar_t *)&v76);
sub_8DEE44(v76, 2u, gvar_0072AB78, v58, v43, -1, 0, 0);
break;
default:
if ( v9 >= 5000 )
{
v45 = (HWND)TWinControl_GetHandle(0);
WStrFromLStr((int)&v67, (int)v143);
WStrCat3(&v66, *(_DWORD *)v137, *(_DWORD *)v129, v67);
sub_8D3B38(v66, v21, 0, 0, 0, (wchar_t *)&v68);
sub_8DEE44(v68, 2u, gvar_0072AB78, v60, v45, -1, 0, 0);
}
else
{
v44 = (HWND)TWinControl_GetHandle(0);
IntToStr(v10, &v71);
WStrFromLStr((int)&v72, v71);
v20 = v72;
WStrFromLStr((int)&v70, (int)v143);
WStrCat3(&v69, *(_DWORD *)v137, *(_DWORD *)v133, v70);
sub_8D3B38(v69, v13, v20, 0, 0, (wchar_t *)&v73);
sub_8DEE44(v73, 2u, gvar_0072AB78, v59, v44, -1, 0, 0);
}
break;
}
kg
otacu/faststone-Capture-keyGen --- otacu/faststone-Capture-keyGen
import hashlib
import base64
import random
import string
from blowfish import BlowFish
from idea import IDEA_Encryption
username = 'bill'
register_code = ''
def randomString(stringLength=8):
letters = string.ascii_uppercase
return ''.join(random.choice(letters) for i in range(stringLength))
def generate_8_upper_case():
# Family License that covers up to 5 computers 1111
family_registeration_code = "{0}{1}{2}{3}{4}{5}{6}{7}".format(randomString(1), 'P', randomString(1), 'N',
randomString(1), 'K', randomString(1), 'E')
# Educational Site License 4997
education_site_registeration_code = "{0}{1}{2}{3}{4}{5}{6}{7}".format(randomString(1), 'V', randomString(1), 'Q',
randomString(1), 'R', randomString(1), 'M')
# Educational Worldwide License 4998
education_worldwide_registeration_code = "{0}{1}{2}{3}{4}{5}{6}{7}".format(randomString(1), 'W', randomString(1),
'Q', randomString(10), 'R',
randomString(1), 'M')
# Corporate Site License 4999
Corporate_site_registeration_code = "{0}{1}{2}{3}{4}{5}{6}{7}".format(randomString(1), 'X', randomString(1), 'Q',
randomString(1), 'R', randomString(1), 'M')
# Corporate Worldwide License 5000
corporate_worldwide_registeration_code = "{0}{1}{2}{3}{4}{5}{6}{7}".format(randomString(1), 'T', randomString(1),
'R', randomString(1), 'K',
randomString(1), 'E')
return [family_registeration_code, education_site_registeration_code, education_worldwide_registeration_code,
Corporate_site_registeration_code, corporate_worldwide_registeration_code]
def get_sha_one_value(data, is_hex):
sha_one = hashlib.sha1(data)
if is_hex:
return sha_one.hexdigest()
else:
return sha_one.digest()
def get_sha_512_value(data, is_hex):
sha_512 = hashlib.sha512(data)
if is_hex:
return sha_512.hexdigest()
else:
return sha_512.digest()
def character_intersect(uname, rcode):
uname_length = len(uname)
rcode_length = len(rcode)
s = ''
i = j = num = 0
while i < uname_length and j < rcode_length:
if num % 2 == 0:
s += uname[i]
i += 1
else:
s += rcode[j]
j += 1
num += 1
if j != rcode_length:
s += rcode[j:8]
if i != uname_length:
s += uname[i:]
return s.upper()
def front_8_character():
s_first = 'me4T6cBLV'
s_second = register_code[:8]
s_third = 'CpCwxrvCJZ30pKLu8Svxjhnhut437glCpofVssnFeBh2G0ekUq4VcxFintMix52vL0iJNbdtWqHPyeumkDUC+4AaoSX+xpl56Esonk4='
sha_one_data = (s_first + s_second + s_third).encode('utf-8')
# sha_one hash
key_sha_one = get_sha_one_value(sha_one_data, False)
# print("front_8_character, key_sha_one: {0}".format(get_sha_one_value(sha_one_data, True)))
# hash for blowfish key
bf = BlowFish(key_sha_one)
bf.generate_subkey()
# sha512 hash
t_first = register_code[:8]
t_second = '96338'
t_third = character_intersect(username, register_code[:8])
sha_512_data = (t_first + t_second + t_third).encode('utf-8')
key_sha_512 = get_sha_512_value(sha_512_data, False)
# print("front_8_character, key_sha_512: {0}".format(get_sha_512_value(sha_512_data, True)))
# hash for IDEA key
idea = IDEA_Encryption(key_sha_512[0:16])
idea.generate_subkey()
# blowfish encrypt
plain_text = t_third
first_cipher = str()
blowfish_encrypt_result = bf.main_transform(0, 0)
for i in range(len(plain_text)):
tmp = bf.main_transform(blowfish_encrypt_result[0], blowfish_encrypt_result[1])
first_cipher += chr(((tmp[0] >> 24) & 0xff) ^ ord(plain_text[i]))
blowfish_encrypt_result[0] = ((blowfish_encrypt_result[0] << 8) & 0xffffffff) | blowfish_encrypt_result[1] >> 24
blowfish_encrypt_result[1] = ((blowfish_encrypt_result[1] << 8) & 0xffffff00) | ((tmp[0] >> 24) & 0xff) ^ ord(
plain_text[i])
first_cipher_base64 = base64.b64encode(first_cipher.encode('latin1'))
# print("the first 8 character, blowfish base64 cipher: " + str(first_cipher_base64))
# IDEA encrypt
plain_text = first_cipher_base64
two_cipher = str()
IDEA_zero_byte = b'\x00\x00\x00\x00\x00\x00\x00\x00'
IDEA_encrypt_result = idea.encrypt(IDEA_zero_byte)
for i in range(len(plain_text)):
tmp = idea.encrypt(IDEA_encrypt_result)
two_cipher += chr(tmp[0] & 0xff ^ plain_text[i])
IDEA_encrypt_result = IDEA_encrypt_result[1:] + chr(tmp[0] & 0xff ^ plain_text[i]).encode('latin1')
two_cipher_base64 = base64.b64encode(two_cipher.encode('latin1'))
# print("the first 8 character, IDEA base64 cipher" + str(two_cipher_base64))
# choose the first 8 upper character
upper_character = str()
front_8_rcode = register_code[:8]
for i in two_cipher_base64:
if i >= 0x41 and i <= 0x5a:
upper_character += chr(i)
return upper_character[:8] if len(upper_character) >= 8 else []
def middle_8_character():
plain_text = b'09232849248398340903834873297239340547237623242043324398489390309284343843223493299435'
# sha 512 key
key_sha_512 = get_sha_512_value(plain_text, False)
# print("middle_8_character, key_sha_512: {0}".format(get_sha_512_value(plain_text, True)))
# blowfish encryption
bf = BlowFish(key_sha_512[:56])
bf.generate_subkey()
# sha-1 key
s_first = register_code[:8]
s_second = '96338'
s_third = character_intersect(username, register_code[:8])
plain_text = (s_first + s_second + s_third).encode('utf-8')
key_sha_one = get_sha_one_value(plain_text, False)
# print("middle_8_character, key_sha_one: {0}".format(get_sha_one_value(plain_text, True)))
# IDEA encryption
idea = IDEA_Encryption(key_sha_one[:16])
idea.generate_subkey()
# IDEA encrypt
plain_text = (s_third).encode('utf-8')
plain_length = len(plain_text)
first_cipher = bytearray(plain_length)
IDEA_zero_byte = b'\x00\x00\x00\x00\x00\x00\x00\x00'
IDEA_encrypt_result = idea.encrypt(IDEA_zero_byte)
times = ord(register_code[0]) - 0x31
for i in range(plain_length * times):
tmp = idea.encrypt(IDEA_encrypt_result)
first_cipher[i % plain_length] = tmp[0] & 0xff ^ plain_text[i % plain_length]
IDEA_encrypt_result = IDEA_encrypt_result[1:] + chr(tmp[0] & 0xff ^ plain_text[i % plain_length]).encode(
'latin1')
first_cipher_base64 = base64.b64encode(first_cipher)
# print("the middle 8 character, IDEA base64 cipher" + str(first_cipher_base64))
# blowfish encrypt
plain_text = first_cipher_base64
two_cipher = bytearray(len(plain_text))
blowfish_zero_byte = b'\x00\x00\x00\x00\x00\x00\x00\x00'
blowfish_encrypt_result = bf.main_transform(0, 0)
for i in range(len(plain_text)):
tmp = bf.main_transform(blowfish_encrypt_result[0], blowfish_encrypt_result[1])
two_cipher[i] = (tmp[0] >> 24) & 0xff ^ plain_text[i]
blowfish_encrypt_result[0] = ((blowfish_encrypt_result[0] << 8) & 0xffffffff) | blowfish_encrypt_result[1] >> 24
blowfish_encrypt_result[1] = ((blowfish_encrypt_result[1] << 8) & 0xffffff00) | ((tmp[0] >> 24) & 0xff) ^ \
plain_text[i]
two_cipher_base64 = base64.b64encode(two_cipher)
# print("the first 8 character, blowfish base64 cipher: " + str(two_cipher_base64))
upper_character = str()
back_4_rcode = register_code[-4:]
for i in two_cipher_base64:
if i >= 0x41 and i <= 0x5a:
upper_character += chr(i)
return upper_character[:4] if len(upper_character) >= 4 else []
def check(data):
first = str(ord(data[4 - 1]) - ord('M')) # 3
second = str(ord(data[8 - 1]) - ord('D')) # 7
third = str(ord(data[6 - 1]) - ord('I')) # 5
forth = str(ord(data[2 - 1]) - ord('O')) # 1
s = first + second + third + forth
if '-' in s:
return False
return True
def main():
global username
global register_code
username = input('please input a username: ')
username = username.upper()
registeration_code = generate_8_upper_case()
hint_information = [
"Family License",
"Educational Site License",
"Educational Worldwide License",
"Corporate Site License",
"Corporate Worldwide License"
]
for i in range(len(registeration_code)):
register_code = registeration_code[i]
first = front_8_character() # front 8 character
second = middle_8_character()
if len(first) > 0 and len(second) > 0:
full_register_code = register_code + first + second
result = check(full_register_code)
if result:
print("{0}: {1}".format(hint_information[i], full_register_code))
if __name__ == "__main__":
main()
idea.py
class IDEA_Encryption:
def __init__(self, key):
self.key = key
pass
def add_mod(self, a, b):
return (a + b) % 0x10000
def mul_mod(self, a, b):
tmp_a = (1 << 16) if a == 0 else a
tmp_b = (1 << 16) if b == 0 else b
return (tmp_a * tmp_b) % 0x10001
def rotate_left(self, subKey):
highPart = subKey[0] >> (16 - 5)
for i in range(7):
subKey[i] = ((subKey[i] << 5) | (subKey[i + 1] >> (16 - 5))) & 0xffff
subKey[7] = ((subKey[7] << 5) | highPart) & 0xffff
return subKey
def round(self, data, round):
out = []
tmp = data.copy()
tmp[0] = self.mul_mod(data[0], self.subKey[6 * round])
tmp[1] = self.add_mod(data[1], self.subKey[6 * round + 1])
tmp[2] = self.add_mod(data[2], self.subKey[6 * round + 2])
tmp[3] = self.mul_mod(data[3], self.subKey[6 * round + 3])
out.append(tmp[0] ^ tmp[2])
out.append(tmp[1] ^ tmp[3])
out.append(self.mul_mod(out[0], self.subKey[6 * round + 4]))
out.append(self.add_mod(out[1], out[2]))
out.append(self.mul_mod(out[3], self.subKey[6 * round + 5]))
out.append(self.add_mod(out[2], out[4]))
out[0] = tmp[0] ^ out[4]
out[1] = tmp[1] ^ out[5]
out[2] = tmp[2] ^ out[4]
out[3] = tmp[3] ^ out[5]
out[1], out[2] = out[2], out[1]
return out[:4]
def generate_subkey(self):
subKey = []
for i in range(8):
subKey.append((self.key[i * 2] << 8) | (self.key[2 * i + 1]))
i = 1
tmpKey = subKey.copy()
while i <= 5:
for j in range(5):
tmpKey = self.rotate_left(tmpKey)
for j in range(8):
subKey.append(tmpKey[j])
i += 1
for i in range(5):
self.rotate_left(tmpKey)
subKey.append(tmpKey[0])
subKey.append(tmpKey[1])
subKey.append(tmpKey[2])
subKey.append(tmpKey[3])
self.subKey = subKey
def transform(self, data_encrypt):
cipher_bytes = str()
for s in data_encrypt:
cipher_bytes += chr((s[0] >> 8) & 0xff)
cipher_bytes += chr(s[0] & 0xff)
cipher_bytes += chr((s[1] >> 8) & 0xff)
cipher_bytes += chr(s[1] & 0xff)
cipher_bytes += chr((s[2] >> 8) & 0xff)
cipher_bytes += chr(s[2] & 0xff)
cipher_bytes += chr((s[3] >> 8) & 0xff)
cipher_bytes += chr(s[3] & 0xff)
return cipher_bytes.encode('latin1')
def encrypt(self, data):
data_length = int(len(data) / 8)
data_encrypt = []
for i in range(data_length):
tmp = []
data_copy = data[i * 8: 8 * (i + 1)]
for j in range(4):
tmp.append(((data_copy[j * 2] << 8) | (data_copy[2 * j + 1])) & 0xffff)
for j in range(8):
tmp = self.round(tmp, j)
tmp[1], tmp[2] = tmp[2], tmp[1]
tmp[0] = self.mul_mod(tmp[0], self.subKey[48])
tmp[1] = self.add_mod(tmp[1], self.subKey[49])
tmp[2] = self.add_mod(tmp[2], self.subKey[50])
tmp[3] = self.mul_mod(tmp[3], self.subKey[51])
data_encrypt.append(tmp)
return self.transform(data_encrypt)
blowfish.py
P_Box = (
0x243f6a88, 0x85a308d3, 0x13198a2e, 0x03707344, 0xa4093822, 0x299f31d0,
0x082efa98, 0xec4e6c89, 0x452821e6, 0x38d01377, 0xbe5466cf, 0x34e90c6c,
0xc0ac29b7, 0xc97c50dd, 0x3f84d5b5, 0xb5470917, 0x9216d5d9, 0x8979fb1b,
)
# 4 x 256
S_Box = (
(
0xd1310ba6, 0x98dfb5ac, 0x2ffd72db, 0xd01adfb7, 0xb8e1afed, 0x6a267e96,
0xba7c9045, 0xf12c7f99, 0x24a19947, 0xb3916cf7, 0x0801f2e2, 0x858efc16,
0x636920d8, 0x71574e69, 0xa458fea3, 0xf4933d7e, 0x0d95748f, 0x728eb658,
0x718bcd58, 0x82154aee, 0x7b54a41d, 0xc25a59b5, 0x9c30d539, 0x2af26013,
0xc5d1b023, 0x286085f0, 0xca417918, 0xb8db38ef, 0x8e79dcb0, 0x603a180e,
0x6c9e0e8b, 0xb01e8a3e, 0xd71577c1, 0xbd314b27, 0x78af2fda, 0x55605c60,
0xe65525f3, 0xaa55ab94, 0x57489862, 0x63e81440, 0x55ca396a, 0x2aab10b6,
0xb4cc5c34, 0x1141e8ce, 0xa15486af, 0x7c72e993, 0xb3ee1411, 0x636fbc2a,
0x2ba9c55d, 0x741831f6, 0xce5c3e16, 0x9b87931e, 0xafd6ba33, 0x6c24cf5c,
0x7a325381, 0x28958677, 0x3b8f4898, 0x6b4bb9af, 0xc4bfe81b, 0x66282193,
0x61d809cc, 0xfb21a991, 0x487cac60, 0x5dec8032, 0xef845d5d, 0xe98575b1,
0xdc262302, 0xeb651b88, 0x23893e81, 0xd396acc5, 0x0f6d6ff3, 0x83f44239,
0x2e0b4482, 0xa4842004, 0x69c8f04a, 0x9e1f9b5e, 0x21c66842, 0xf6e96c9a,
0x670c9c61, 0xabd388f0, 0x6a51a0d2, 0xd8542f68, 0x960fa728, 0xab5133a3,
0x6eef0b6c, 0x137a3be4, 0xba3bf050, 0x7efb2a98, 0xa1f1651d, 0x39af0176,
0x66ca593e, 0x82430e88, 0x8cee8619, 0x456f9fb4, 0x7d84a5c3, 0x3b8b5ebe,
0xe06f75d8, 0x85c12073, 0x401a449f, 0x56c16aa6, 0x4ed3aa62, 0x363f7706,
0x1bfedf72, 0x429b023d, 0x37d0d724, 0xd00a1248, 0xdb0fead3, 0x49f1c09b,
0x075372c9, 0x80991b7b, 0x25d479d8, 0xf6e8def7, 0xe3fe501a, 0xb6794c3b,
0x976ce0bd, 0x04c006ba, 0xc1a94fb6, 0x409f60c4, 0x5e5c9ec2, 0x196a2463,
0x68fb6faf, 0x3e6c53b5, 0x1339b2eb, 0x3b52ec6f, 0x6dfc511f, 0x9b30952c,
0xcc814544, 0xaf5ebd09, 0xbee3d004, 0xde334afd, 0x660f2807, 0x192e4bb3,
0xc0cba857, 0x45c8740f, 0xd20b5f39, 0xb9d3fbdb, 0x5579c0bd, 0x1a60320a,
0xd6a100c6, 0x402c7279, 0x679f25fe, 0xfb1fa3cc, 0x8ea5e9f8, 0xdb3222f8,
0x3c7516df, 0xfd616b15, 0x2f501ec8, 0xad0552ab, 0x323db5fa, 0xfd238760,
0x53317b48, 0x3e00df82, 0x9e5c57bb, 0xca6f8ca0, 0x1a87562e, 0xdf1769db,
0xd542a8f6, 0x287effc3, 0xac6732c6, 0x8c4f5573, 0x695b27b0, 0xbbca58c8,
0xe1ffa35d, 0xb8f011a0, 0x10fa3d98, 0xfd2183b8, 0x4afcb56c, 0x2dd1d35b,
0x9a53e479, 0xb6f84565, 0xd28e49bc, 0x4bfb9790, 0xe1ddf2da, 0xa4cb7e33,
0x62fb1341, 0xcee4c6e8, 0xef20cada, 0x36774c01, 0xd07e9efe, 0x2bf11fb4,
0x95dbda4d, 0xae909198, 0xeaad8e71, 0x6b93d5a0, 0xd08ed1d0, 0xafc725e0,
0x8e3c5b2f, 0x8e7594b7, 0x8ff6e2fb, 0xf2122b64, 0x8888b812, 0x900df01c,
0x4fad5ea0, 0x688fc31c, 0xd1cff191, 0xb3a8c1ad, 0x2f2f2218, 0xbe0e1777,
0xea752dfe, 0x8b021fa1, 0xe5a0cc0f, 0xb56f74e8, 0x18acf3d6, 0xce89e299,
0xb4a84fe0, 0xfd13e0b7, 0x7cc43b81, 0xd2ada8d9, 0x165fa266, 0x80957705,
0x93cc7314, 0x211a1477, 0xe6ad2065, 0x77b5fa86, 0xc75442f5, 0xfb9d35cf,
0xebcdaf0c, 0x7b3e89a0, 0xd6411bd3, 0xae1e7e49, 0x00250e2d, 0x2071b35e,
0x226800bb, 0x57b8e0af, 0x2464369b, 0xf009b91e, 0x5563911d, 0x59dfa6aa,
0x78c14389, 0xd95a537f, 0x207d5ba2, 0x02e5b9c5, 0x83260376, 0x6295cfa9,
0x11c81968, 0x4e734a41, 0xb3472dca, 0x7b14a94a, 0x1b510052, 0x9a532915,
0xd60f573f, 0xbc9bc6e4, 0x2b60a476, 0x81e67400, 0x08ba6fb5, 0x571be91f,
0xf296ec6b, 0x2a0dd915, 0xb6636521, 0xe7b9f9b6, 0xff34052e, 0xc5855664,
0x53b02d5d, 0xa99f8fa1, 0x08ba4799, 0x6e85076a,
),
(
0x4b7a70e9, 0xb5b32944, 0xdb75092e, 0xc4192623, 0xad6ea6b0, 0x49a7df7d,
0x9cee60b8, 0x8fedb266, 0xecaa8c71, 0x699a17ff, 0x5664526c, 0xc2b19ee1,
0x193602a5, 0x75094c29, 0xa0591340, 0xe4183a3e, 0x3f54989a, 0x5b429d65,
0x6b8fe4d6, 0x99f73fd6, 0xa1d29c07, 0xefe830f5, 0x4d2d38e6, 0xf0255dc1,
0x4cdd2086, 0x8470eb26, 0x6382e9c6, 0x021ecc5e, 0x09686b3f, 0x3ebaefc9,
0x3c971814, 0x6b6a70a1, 0x687f3584, 0x52a0e286, 0xb79c5305, 0xaa500737,
0x3e07841c, 0x7fdeae5c, 0x8e7d44ec, 0x5716f2b8, 0xb03ada37, 0xf0500c0d,
0xf01c1f04, 0x0200b3ff, 0xae0cf51a, 0x3cb574b2, 0x25837a58, 0xdc0921bd,
0xd19113f9, 0x7ca92ff6, 0x94324773, 0x22f54701, 0x3ae5e581, 0x37c2dadc,
0xc8b57634, 0x9af3dda7, 0xa9446146, 0x0fd0030e, 0xecc8c73e, 0xa4751e41,
0xe238cd99, 0x3bea0e2f, 0x3280bba1, 0x183eb331, 0x4e548b38, 0x4f6db908,
0x6f420d03, 0xf60a04bf, 0x2cb81290, 0x24977c79, 0x5679b072, 0xbcaf89af,
0xde9a771f, 0xd9930810, 0xb38bae12, 0xdccf3f2e, 0x5512721f, 0x2e6b7124,
0x501adde6, 0x9f84cd87, 0x7a584718, 0x7408da17, 0xbc9f9abc, 0xe94b7d8c,
0xec7aec3a, 0xdb851dfa, 0x63094366, 0xc464c3d2, 0xef1c1847, 0x3215d908,
0xdd433b37, 0x24c2ba16, 0x12a14d43, 0x2a65c451, 0x50940002, 0x133ae4dd,
0x71dff89e, 0x10314e55, 0x81ac77d6, 0x5f11199b, 0x043556f1, 0xd7a3c76b,
0x3c11183b, 0x5924a509, 0xf28fe6ed, 0x97f1fbfa, 0x9ebabf2c, 0x1e153c6e,
0x86e34570, 0xeae96fb1, 0x860e5e0a, 0x5a3e2ab3, 0x771fe71c, 0x4e3d06fa,
0x2965dcb9, 0x99e71d0f, 0x803e89d6, 0x5266c825, 0x2e4cc978, 0x9c10b36a,
0xc6150eba, 0x94e2ea78, 0xa5fc3c53, 0x1e0a2df4, 0xf2f74ea7, 0x361d2b3d,
0x1939260f, 0x19c27960, 0x5223a708, 0xf71312b6, 0xebadfe6e, 0xeac31f66,
0xe3bc4595, 0xa67bc883, 0xb17f37d1, 0x018cff28, 0xc332ddef, 0xbe6c5aa5,
0x65582185, 0x68ab9802, 0xeecea50f, 0xdb2f953b, 0x2aef7dad, 0x5b6e2f84,
0x1521b628, 0x29076170, 0xecdd4775, 0x619f1510, 0x13cca830, 0xeb61bd96,
0x0334fe1e, 0xaa0363cf, 0xb5735c90, 0x4c70a239, 0xd59e9e0b, 0xcbaade14,
0xeecc86bc, 0x60622ca7, 0x9cab5cab, 0xb2f3846e, 0x648b1eaf, 0x19bdf0ca,
0xa02369b9, 0x655abb50, 0x40685a32, 0x3c2ab4b3, 0x319ee9d5, 0xc021b8f7,
0x9b540b19, 0x875fa099, 0x95f7997e, 0x623d7da8, 0xf837889a, 0x97e32d77,
0x11ed935f, 0x16681281, 0x0e358829, 0xc7e61fd6, 0x96dedfa1, 0x7858ba99,
0x57f584a5, 0x1b227263, 0x9b83c3ff, 0x1ac24696, 0xcdb30aeb, 0x532e3054,
0x8fd948e4, 0x6dbc3128, 0x58ebf2ef, 0x34c6ffea, 0xfe28ed61, 0xee7c3c73,
0x5d4a14d9, 0xe864b7e3, 0x42105d14, 0x203e13e0, 0x45eee2b6, 0xa3aaabea,
0xdb6c4f15, 0xfacb4fd0, 0xc742f442, 0xef6abbb5, 0x654f3b1d, 0x41cd2105,
0xd81e799e, 0x86854dc7, 0xe44b476a, 0x3d816250, 0xcf62a1f2, 0x5b8d2646,
0xfc8883a0, 0xc1c7b6a3, 0x7f1524c3, 0x69cb7492, 0x47848a0b, 0x5692b285,
0x095bbf00, 0xad19489d, 0x1462b174, 0x23820e00, 0x58428d2a, 0x0c55f5ea,
0x1dadf43e, 0x233f7061, 0x3372f092, 0x8d937e41, 0xd65fecf1, 0x6c223bdb,
0x7cde3759, 0xcbee7460, 0x4085f2a7, 0xce77326e, 0xa6078084, 0x19f8509e,
0xe8efd855, 0x61d99735, 0xa969a7aa, 0xc50c06c2, 0x5a04abfc, 0x800bcadc,
0x9e447a2e, 0xc3453484, 0xfdd56705, 0x0e1e9ec9, 0xdb73dbd3, 0x105588cd,
0x675fda79, 0xe3674340, 0xc5c43465, 0x713e38d8, 0x3d28f89e, 0xf16dff20,
0x153e21e7, 0x8fb03d4a, 0xe6e39f2b, 0xdb83adf7,
),
(
0xe93d5a68, 0x948140f7, 0xf64c261c, 0x94692934, 0x411520f7, 0x7602d4f7,
0xbcf46b2e, 0xd4a20068, 0xd4082471, 0x3320f46a, 0x43b7d4b7, 0x500061af,
0x1e39f62e, 0x97244546, 0x14214f74, 0xbf8b8840, 0x4d95fc1d, 0x96b591af,
0x70f4ddd3, 0x66a02f45, 0xbfbc09ec, 0x03bd9785, 0x7fac6dd0, 0x31cb8504,
0x96eb27b3, 0x55fd3941, 0xda2547e6, 0xabca0a9a, 0x28507825, 0x530429f4,
0x0a2c86da, 0xe9b66dfb, 0x68dc1462, 0xd7486900, 0x680ec0a4, 0x27a18dee,
0x4f3ffea2, 0xe887ad8c, 0xb58ce006, 0x7af4d6b6, 0xaace1e7c, 0xd3375fec,
0xce78a399, 0x406b2a42, 0x20fe9e35, 0xd9f385b9, 0xee39d7ab, 0x3b124e8b,
0x1dc9faf7, 0x4b6d1856, 0x26a36631, 0xeae397b2, 0x3a6efa74, 0xdd5b4332,
0x6841e7f7, 0xca7820fb, 0xfb0af54e, 0xd8feb397, 0x454056ac, 0xba489527,
0x55533a3a, 0x20838d87, 0xfe6ba9b7, 0xd096954b, 0x55a867bc, 0xa1159a58,
0xcca92963, 0x99e1db33, 0xa62a4a56, 0x3f3125f9, 0x5ef47e1c, 0x9029317c,
0xfdf8e802, 0x04272f70, 0x80bb155c, 0x05282ce3, 0x95c11548, 0xe4c66d22,
0x48c1133f, 0xc70f86dc, 0x07f9c9ee, 0x41041f0f, 0x404779a4, 0x5d886e17,
0x325f51eb, 0xd59bc0d1, 0xf2bcc18f, 0x41113564, 0x257b7834, 0x602a9c60,
0xdff8e8a3, 0x1f636c1b, 0x0e12b4c2, 0x02e1329e, 0xaf664fd1, 0xcad18115,
0x6b2395e0, 0x333e92e1, 0x3b240b62, 0xeebeb922, 0x85b2a20e, 0xe6ba0d99,
0xde720c8c, 0x2da2f728, 0xd0127845, 0x95b794fd, 0x647d0862, 0xe7ccf5f0,
0x5449a36f, 0x877d48fa, 0xc39dfd27, 0xf33e8d1e, 0x0a476341, 0x992eff74,
0x3a6f6eab, 0xf4f8fd37, 0xa812dc60, 0xa1ebddf8, 0x991be14c, 0xdb6e6b0d,
0xc67b5510, 0x6d672c37, 0x2765d43b, 0xdcd0e804, 0xf1290dc7, 0xcc00ffa3,
0xb5390f92, 0x690fed0b, 0x667b9ffb, 0xcedb7d9c, 0xa091cf0b, 0xd9155ea3,
0xbb132f88, 0x515bad24, 0x7b9479bf, 0x763bd6eb, 0x37392eb3, 0xcc115979,
0x8026e297, 0xf42e312d, 0x6842ada7, 0xc66a2b3b, 0x12754ccc, 0x782ef11c,
0x6a124237, 0xb79251e7, 0x06a1bbe6, 0x4bfb6350, 0x1a6b1018, 0x11caedfa,
0x3d25bdd8, 0xe2e1c3c9, 0x44421659, 0x0a121386, 0xd90cec6e, 0xd5abea2a,
0x64af674e, 0xda86a85f, 0xbebfe988, 0x64e4c3fe, 0x9dbc8057, 0xf0f7c086,
0x60787bf8, 0x6003604d, 0xd1fd8346, 0xf6381fb0, 0x7745ae04, 0xd736fccc,
0x83426b33, 0xf01eab71, 0xb0804187, 0x3c005e5f, 0x77a057be, 0xbde8ae24,
0x55464299, 0xbf582e61, 0x4e58f48f, 0xf2ddfda2, 0xf474ef38, 0x8789bdc2,
0x5366f9c3, 0xc8b38e74, 0xb475f255, 0x46fcd9b9, 0x7aeb2661, 0x8b1ddf84,
0x846a0e79, 0x915f95e2, 0x466e598e, 0x20b45770, 0x8cd55591, 0xc902de4c,
0xb90bace1, 0xbb8205d0, 0x11a86248, 0x7574a99e, 0xb77f19b6, 0xe0a9dc09,
0x662d09a1, 0xc4324633, 0xe85a1f02, 0x09f0be8c, 0x4a99a025, 0x1d6efe10,
0x1ab93d1d, 0x0ba5a4df, 0xa186f20f, 0x2868f169, 0xdcb7da83, 0x573906fe,
0xa1e2ce9b, 0x4fcd7f52, 0x50115e01, 0xa70683fa, 0xa002b5c4, 0x0de6d027,
0x9af88c27, 0x773f8641, 0xc3604c06, 0x61a806b5, 0xf0177a28, 0xc0f586e0,
0x006058aa, 0x30dc7d62, 0x11e69ed7, 0x2338ea63, 0x53c2dd94, 0xc2c21634,
0xbbcbee56, 0x90bcb6de, 0xebfc7da1, 0xce591d76, 0x6f05e409, 0x4b7c0188,
0x39720a3d, 0x7c927c24, 0x86e3725f, 0x724d9db9, 0x1ac15bb4, 0xd39eb8fc,
0xed545578, 0x08fca5b5, 0xd83d7cd3, 0x4dad0fc4, 0x1e50ef5e, 0xb161e6f8,
0xa28514d9, 0x6c51133c, 0x6fd5c7e7, 0x56e14ec4, 0x362abfce, 0xddc6c837,
0xd79a3234, 0x92638212, 0x670efa8e, 0x406000e0,
),
(
0x3a39ce37, 0xd3faf5cf, 0xabc27737, 0x5ac52d1b, 0x5cb0679e, 0x4fa33742,
0xd3822740, 0x99bc9bbe, 0xd5118e9d, 0xbf0f7315, 0xd62d1c7e, 0xc700c47b,
0xb78c1b6b, 0x21a19045, 0xb26eb1be, 0x6a366eb4, 0x5748ab2f, 0xbc946e79,
0xc6a376d2, 0x6549c2c8, 0x530ff8ee, 0x468dde7d, 0xd5730a1d, 0x4cd04dc6,
0x2939bbdb, 0xa9ba4650, 0xac9526e8, 0xbe5ee304, 0xa1fad5f0, 0x6a2d519a,
0x63ef8ce2, 0x9a86ee22, 0xc089c2b8, 0x43242ef6, 0xa51e03aa, 0x9cf2d0a4,
0x83c061ba, 0x9be96a4d, 0x8fe51550, 0xba645bd6, 0x2826a2f9, 0xa73a3ae1,
0x4ba99586, 0xef5562e9, 0xc72fefd3, 0xf752f7da, 0x3f046f69, 0x77fa0a59,
0x80e4a915, 0x87b08601, 0x9b09e6ad, 0x3b3ee593, 0xe990fd5a, 0x9e34d797,
0x2cf0b7d9, 0x022b8b51, 0x96d5ac3a, 0x017da67d, 0xd1cf3ed6, 0x7c7d2d28,
0x1f9f25cf, 0xadf2b89b, 0x5ad6b472, 0x5a88f54c, 0xe029ac71, 0xe019a5e6,
0x47b0acfd, 0xed93fa9b, 0xe8d3c48d, 0x283b57cc, 0xf8d56629, 0x79132e28,
0x785f0191, 0xed756055, 0xf7960e44, 0xe3d35e8c, 0x15056dd4, 0x88f46dba,
0x03a16125, 0x0564f0bd, 0xc3eb9e15, 0x3c9057a2, 0x97271aec, 0xa93a072a,
0x1b3f6d9b, 0x1e6321f5, 0xf59c66fb, 0x26dcf319, 0x7533d928, 0xb155fdf5,
0x03563482, 0x8aba3cbb, 0x28517711, 0xc20ad9f8, 0xabcc5167, 0xccad925f,
0x4de81751, 0x3830dc8e, 0x379d5862, 0x9320f991, 0xea7a90c2, 0xfb3e7bce,
0x5121ce64, 0x774fbe32, 0xa8b6e37e, 0xc3293d46, 0x48de5369, 0x6413e680,
0xa2ae0810, 0xdd6db224, 0x69852dfd, 0x09072166, 0xb39a460a, 0x6445c0dd,
0x586cdecf, 0x1c20c8ae, 0x5bbef7dd, 0x1b588d40, 0xccd2017f, 0x6bb4e3bb,
0xdda26a7e, 0x3a59ff45, 0x3e350a44, 0xbcb4cdd5, 0x72eacea8, 0xfa6484bb,
0x8d6612ae, 0xbf3c6f47, 0xd29be463, 0x542f5d9e, 0xaec2771b, 0xf64e6370,
0x740e0d8d, 0xe75b1357, 0xf8721671, 0xaf537d5d, 0x4040cb08, 0x4eb4e2cc,
0x34d2466a, 0x0115af84, 0xe1b00428, 0x95983a1d, 0x06b89fb4, 0xce6ea048,
0x6f3f3b82, 0x3520ab82, 0x011a1d4b, 0x277227f8, 0x611560b1, 0xe7933fdc,
0xbb3a792b, 0x344525bd, 0xa08839e1, 0x51ce794b, 0x2f32c9b7, 0xa01fbac9,
0xe01cc87e, 0xbcc7d1f6, 0xcf0111c3, 0xa1e8aac7, 0x1a908749, 0xd44fbd9a,
0xd0dadecb, 0xd50ada38, 0x0339c32a, 0xc6913667, 0x8df9317c, 0xe0b12b4f,
0xf79e59b7, 0x43f5bb3a, 0xf2d519ff, 0x27d9459c, 0xbf97222c, 0x15e6fc2a,
0x0f91fc71, 0x9b941525, 0xfae59361, 0xceb69ceb, 0xc2a86459, 0x12baa8d1,
0xb6c1075e, 0xe3056a0c, 0x10d25065, 0xcb03a442, 0xe0ec6e0e, 0x1698db3b,
0x4c98a0be, 0x3278e964, 0x9f1f9532, 0xe0d392df, 0xd3a0342b, 0x8971f21e,
0x1b0a7441, 0x4ba3348c, 0xc5be7120, 0xc37632d8, 0xdf359f8d, 0x9b992f2e,
0xe60b6f47, 0x0fe3f11d, 0xe54cda54, 0x1edad891, 0xce6279cf, 0xcd3e7e6f,
0x1618b166, 0xfd2c1d05, 0x848fd2c5, 0xf6fb2299, 0xf523f357, 0xa6327623,
0x93a83531, 0x56cccd02, 0xacf08162, 0x5a75ebb5, 0x6e163697, 0x88d273cc,
0xde966292, 0x81b949d0, 0x4c50901b, 0x71c65614, 0xe6c6c7bd, 0x327a140a,
0x45e1d006, 0xc3f27b9a, 0xc9aa53fd, 0x62a80f00, 0xbb25bfe2, 0x35bdd2f6,
0x71126905, 0xb2040222, 0xb6cbcf7c, 0xcd769c2b, 0x53113ec0, 0x1640e3d3,
0x38abbd60, 0x2547adf0, 0xba38209c, 0xf746ce76, 0x77afa1c5, 0x20756060,
0x85cbfe4e, 0x8ae88dd8, 0x7aaaf9b0, 0x4cf9aa7e, 0x1948c25c, 0x02fb8a8c,
0x01c36ae4, 0xd6ebe1f9, 0x90d4f869, 0xa65cdea0, 0x3f09252d, 0xc208e69f,
0xb74e6132, 0xce77e25b, 0x578fdfe3, 0x3ac372e6,
),
)
class BlowFish:
def __init__(self, key: bytes):
self.key_length = int(len(key) / 4)
self.key_long = []
self.p_box = list(P_Box)
self.s_box = list(list(box) for box in S_Box)
i = 0
while i < self.key_length:
self.key_long.append(int.from_bytes(key[i * 4: (i + 1) * 4], byteorder='big', signed=False))
i += 1
def search(self, direction):
value = (self.s_box[0][direction >> 24] + self.s_box[1][(direction >> 16) & 0xff]) & 0xffffffff
value ^= self.s_box[2][(direction >> 8) & 0xff]
value += self.s_box[3][direction & 0xff]
return value & 0xffffffff
def main_transform(self, left, right):
for i in range(0, 16, 2):
left ^= self.p_box[i]
right ^= self.search(left)
right ^= self.p_box[i + 1]
left ^= self.search(right)
left ^= self.p_box[16]
right ^= self.p_box[17]
return [right, left]
def generate_subkey(self):
for i in range(18):
self.p_box[i] ^= self.key_long[i % self.key_length]
left = right = 0
for i in range(0, 18, 2):
left, right = self.main_transform(left, right)
self.p_box[i] = left
self.p_box[i + 1] = right
for i in range(4):
for j in range(0, 256, 2):
left, right = self.main_transform(left, right)
self.s_box[i][j] = left
self.s_box[i][j + 1] = right
def encrypt(self, data):
data_length = int(len(data) / 8)
data_encrypt = []
for i in range(data_length):
left = int.from_bytes(data[i * 8: i * 8 + 4], byteorder='big', signed=False)
right = int.from_bytes(data[i * 8 + 4: (i + 1) * 8], byteorder='big', signed=False)
left, right = self.main_transform(left, right)
data_encrypt.append(left)
data_encrypt.append(right)
return data_encrypt
ps
注册信息保存在
C:\ProgramData\FastStone\FSC\[xxx]\fsc.db
C:\Users\[xxx]\AppData\Local\FastStone\FSC\fsc.db
C:\Users\[xxx]\AppData\Roaming\FastStone\FSC\fsc.db
TProgramSettings 类进行解析
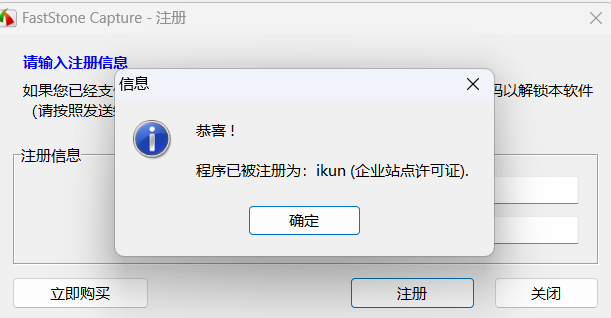

please input a username: ikun
Family License: VPONFKLEKQZBTRRMMFZC
Corporate Site License: XXQQKRFMKVHBVWBJMCER
Corporate Worldwide License: STHRGKQEWVNURHUDVNRH


 浙公网安备 33010602011771号
浙公网安备 33010602011771号