BUUCTF RE reverse3
BUUCTF RE reverse3
下载链接 reverse3
解题步骤
-
拖进EXEInforPE查壳,无壳

-
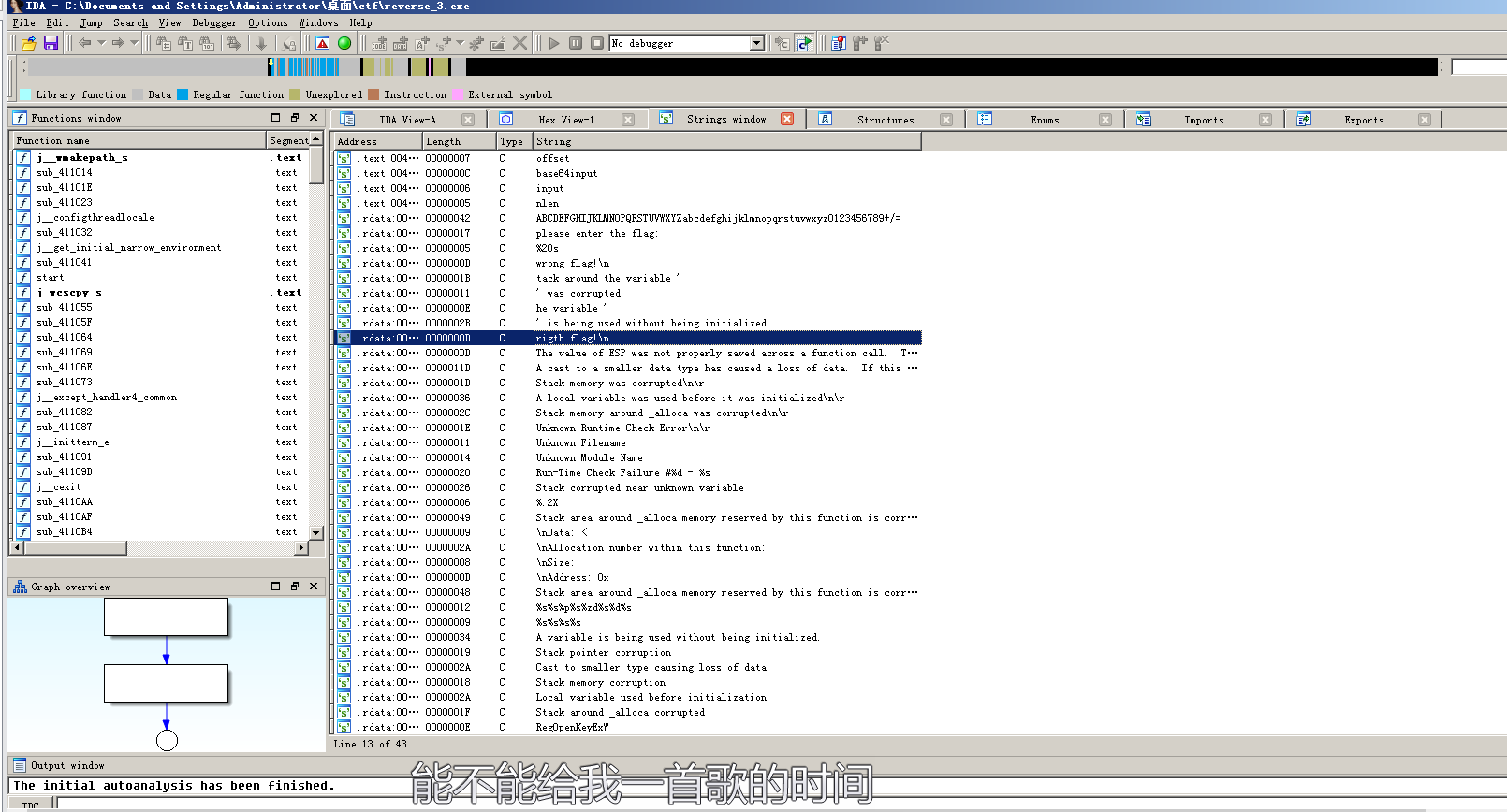
拖进IDA,直接shift+f12查看字符串,发现关键语句
-
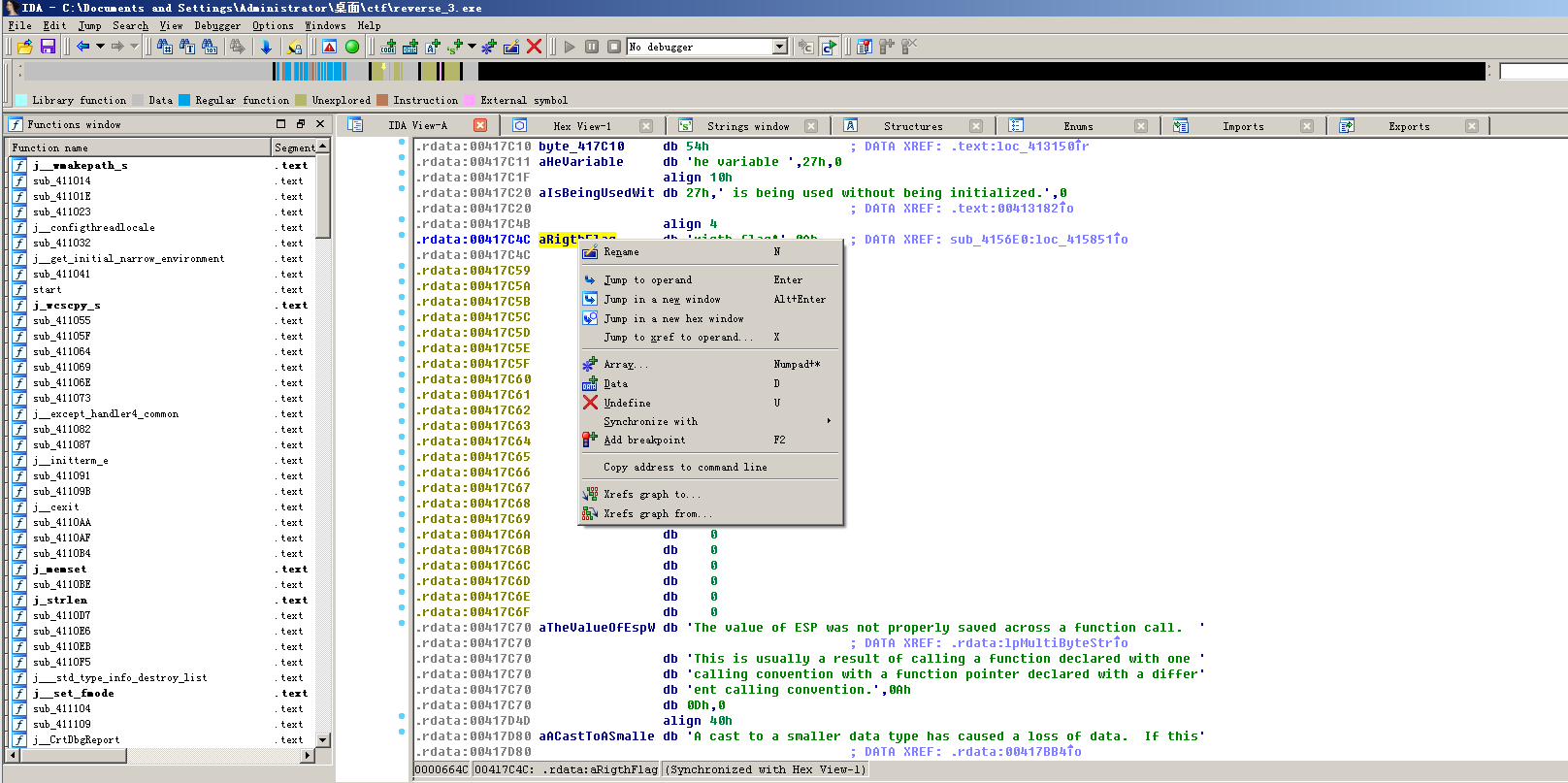
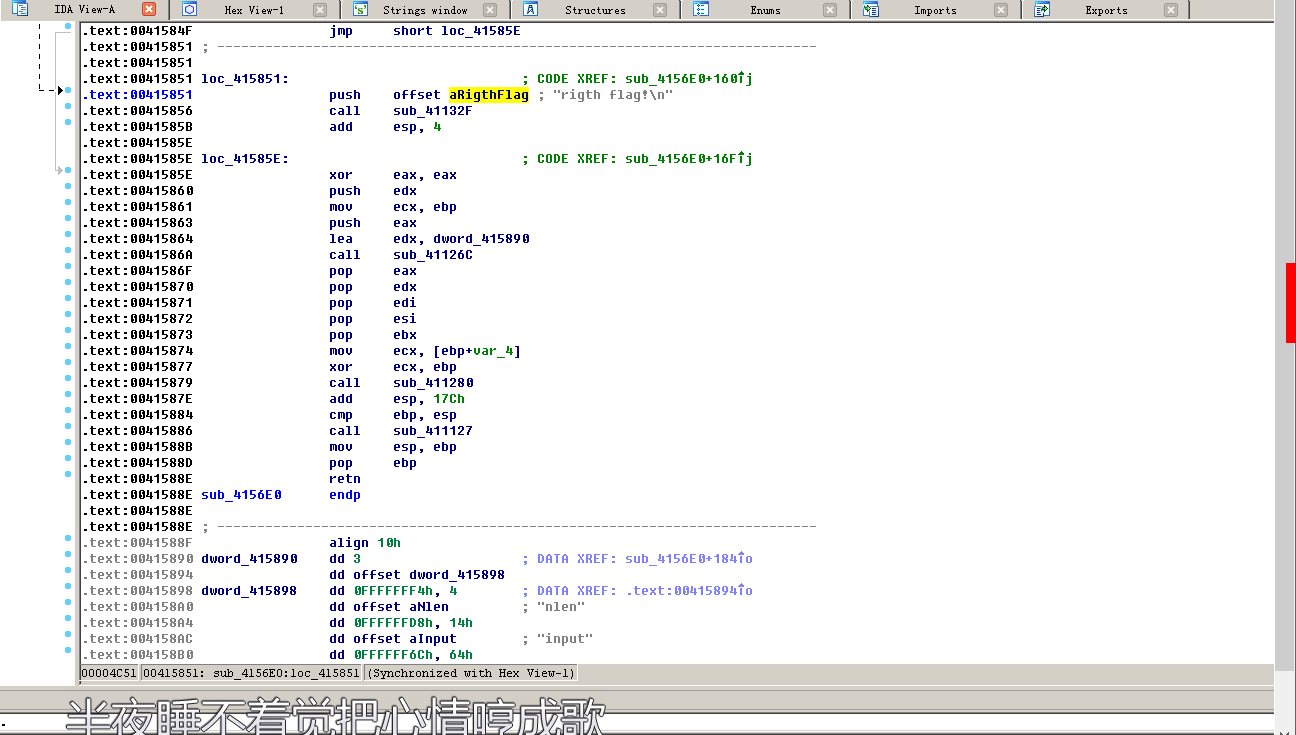
右键进入代码区
-
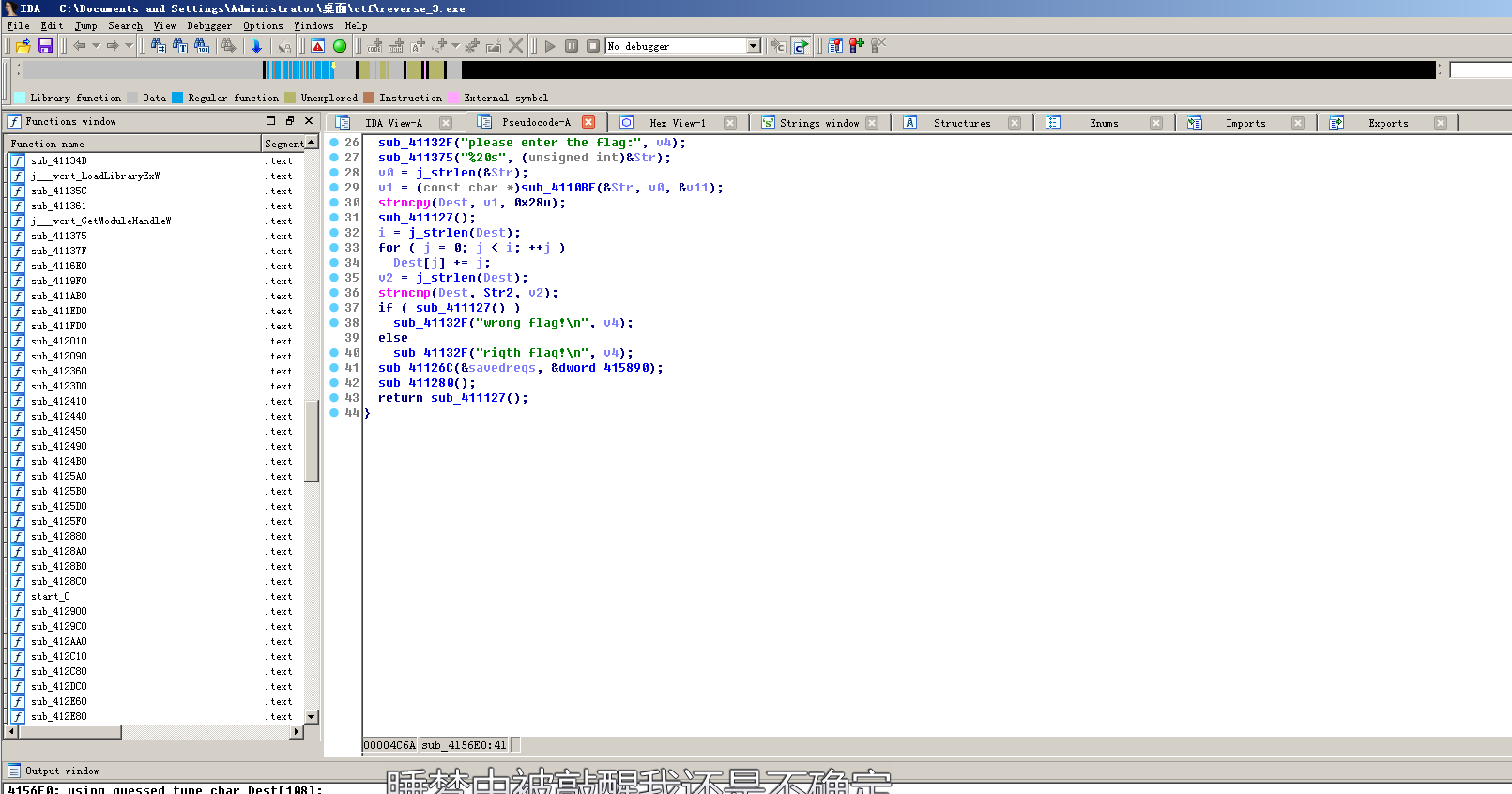
f5转换为伪代码
-
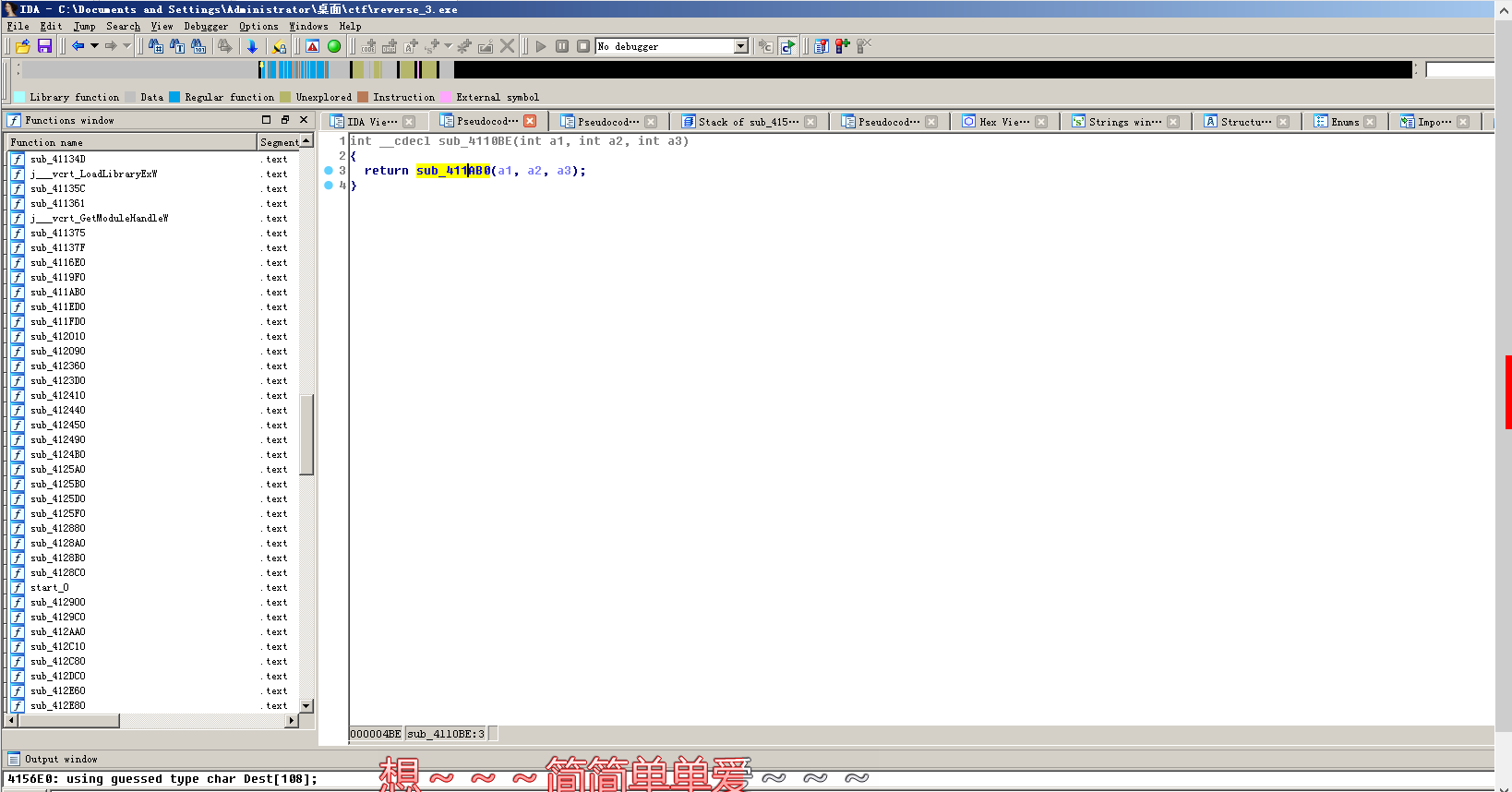
分析代码,发现就是将输入的语句用sub_4110BE函数加密后再进行一个for循环变换,直接进入sub_4110BE
-
进入sub_411AB0,发现是3位加密成四位,盲猜base64加密

加密函数:
`while ( v11 > 0 )
{
byte_41A144[2] = 0;
byte_41A144[1] = 0;
byte_41A144[0] = 0;
for ( i = 0; i < 3 && v11 >= 1; ++i )
{
byte_41A144[i] = *v13;
--v11;
++v13;
}
if ( !i )
break;
switch ( i )
{
case 1:
*((_BYTE *)Dst + v7) = aAbcdefghijklmn[(signed int)(unsigned __int8)byte_41A144[0] >> 2];
v4 = v7 + 1;
*((_BYTE *)Dst + v4++) = aAbcdefghijklmn[((byte_41A144[1] & 0xF0) >> 4) | 16 * (byte_41A144[0] & 3)];
*((_BYTE *)Dst + v4++) = aAbcdefghijklmn[64];
*((_BYTE *)Dst + v4) = aAbcdefghijklmn[64];
v7 = v4 + 1;
break;
case 2:
*((_BYTE *)Dst + v7) = aAbcdefghijklmn[(signed int)(unsigned __int8)byte_41A144[0] >> 2];
v5 = v7 + 1;
*((_BYTE *)Dst + v5++) = aAbcdefghijklmn[((byte_41A144[1] & 0xF0) >> 4) | 16 * (byte_41A144[0] & 3)];
*((_BYTE *)Dst + v5++) = aAbcdefghijklmn[((byte_41A144[2] & 0xC0) >> 6) | 4 * (byte_41A144[1] & 0xF)];
*((_BYTE *)Dst + v5) = aAbcdefghijklmn[64];
v7 = v5 + 1;
break;
case 3:
*((_BYTE *)Dst + v7) = aAbcdefghijklmn[(signed int)(unsigned __int8)byte_41A144[0] >> 2];
v6 = v7 + 1;
*((_BYTE *)Dst + v6++) = aAbcdefghijklmn[((byte_41A144[1] & 0xF0) >> 4) | 16 * (byte_41A144[0] & 3)];
*((_BYTE *)Dst + v6++) = aAbcdefghijklmn[((byte_41A144[2] & 0xC0) >> 6) | 4 * (byte_41A144[1] & 0xF)];
*((_BYTE *)Dst + v6) = aAbcdefghijklmn[byte_41A144[2] & 0x3F];
v7 = v6 + 1;
break;
}
}
*((_BYTE *)Dst + v7) = 0; -
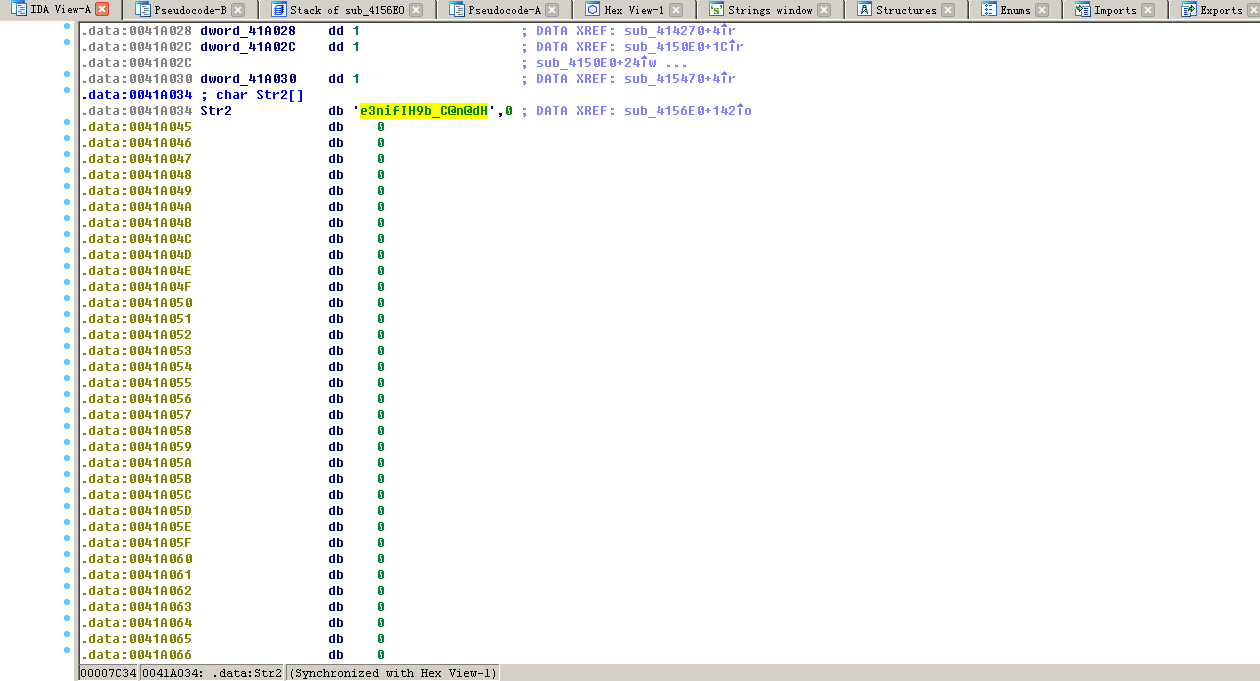
查看str2,e3nifIH9b_C@n@dH
-
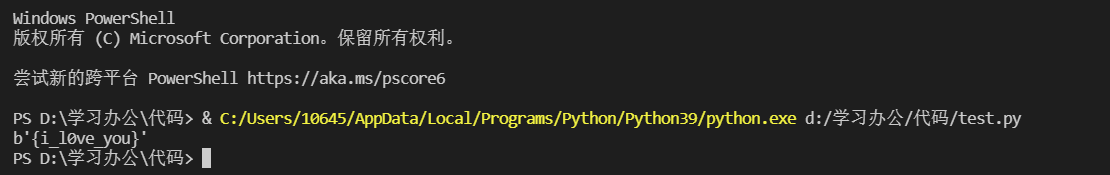
编写python脚本,跑出flag{{i_l0ve_you}}
脚本代码:
`import base64
s = "e3nifIH9b_C@n@dH"
x = ""
for i in range(0,len(s)):
x += chr(ord(s[i]) - i)
print(base64.b64decode(x))`
总结
算是目前为止做到的最难的题了,其实前面的步骤都差不多,主要是这个文件的函数名都很怪,我刚开始把加密函数当作一般的字符串函数来处理了,但是一直出不来flag,后面才发现那是一个自定义函数,用来加密的,然后又是加密函数看了半天,最后才猜的是base64加密。这道题相当于是reverse和crypto结合了,还需要有一定的c语言基础。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号