RSA-Java实现私钥签名公钥认证
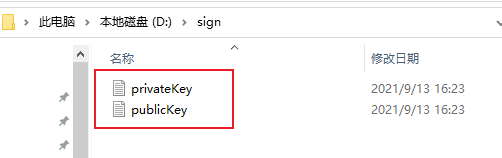
从这里 https://www.cnblogs.com/nastu/p/15224107.html 得到的私钥与公钥分别添加到两个文件中
私钥:
MIICdwIBADANBgkqhkiG9w0BAQEFAASCAmEwggJdAgEAAoGBAIy3Lzb+4VJH3W53xGxB3ZgOgr1ztamIRNBZERhtxS2I3qMx23B9wl50iGk2THwJmH1bgjY4C5IUkPO8TlBKcPi4ACoPqk/oqk1FOdhzkF/ElNZBUNwCTUfttRsLL9yncGZNs6E6MDzzkr3/D9Mlhtp3vPNJANwnmLQm5kd0CnG9AgMBAAECgYEAiPZgKWpqjDjQyY4fjLOLaU5uaNJwNmQhfp3CqwFlE44ODdAgY9y0TFWm1Kl6RpzcZN+l3PouIPCNqf9WRoY+cBaTxI9ur5Sb1FbXdfrroRogGPYNOTO8n3ptP2kU8OzKCenuX6D1lPrFf7bB20g6qO+q02Uz2X2yAXpo/sIgNq0CQQDEHHRiHSEvpasSibWq3iQzIlSj2pxyLsImaShQ/AuG/9QWJdQ7j2AjBwEe5jR00dSYhA7yV463SBmSr1eJbKd3AkEAt7AF0T170+e02ERH79rZuwcPSiFkOl6FTPyNER6bYOujWYAscKKpJZmwmiZDwQ2hYiOIhQqQe0j4T3Ek94XlawJAPW+4miAMDHQ3Aqi3i97pskc4Atjyl+bEFeptoelD5zfwBjw1n68L7A0+saJmno45rsn4ML1zTUG+GTDrGHc8gwJARdtvmu/jE+fe4xC0uwdkHrjEm9CvKXOhBnJVw9j8BpQW/4a7X+q8oUwd2cILqnPgmE4jMVWfNQO/S5cgE/KcGQJBALbb7gWWqrKqqqA2RR9MtLmDPBhs4Yk6eu5J09OXxpCiEftepK1P/OP077LLtgoND7BHBhQfdLAueFsIysX/CJw=
公钥:
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCMty82/uFSR91ud8RsQd2YDoK9c7WpiETQWREYbcUtiN6jMdtwfcJedIhpNkx8CZh9W4I2OAuSFJDzvE5QSnD4uAAqD6pP6KpNRTnYc5BfxJTWQVDcAk1H7bUbCy/cp3BmTbOhOjA885K9/w/TJYbad7zzSQDcJ5i0JuZHdApxvQIDAQAB
代码示例:
1、RSA 加密
import cn.hutool.core.codec.Base64; import javax.crypto.BadPaddingException; import javax.crypto.Cipher; import javax.crypto.IllegalBlockSizeException; import javax.crypto.NoSuchPaddingException; import java.io.*; import java.security.*; import java.security.interfaces.RSAPrivateKey; import java.security.interfaces.RSAPublicKey; import java.security.spec.InvalidKeySpecException; import java.security.spec.PKCS8EncodedKeySpec; import java.security.spec.X509EncodedKeySpec; /** * RSA 加密 */ public class RSAEncrypt { /** * 字节数据转字符串专用集合 */ private static final char[] HEX_CHAR = { '0', '1', '2', '3', '4', '5', '6', '7', '8', '9', 'a', 'b', 'c', 'd', 'e', 'f' }; /** * 随机生成密钥对 * @param filePath */ public static void getKeyPair(String filePath) { // KeyPairGenerator类用于生成公钥和私钥对,基于RSA算法生成对象 KeyPairGenerator keyPairGen = null; try { // keyPairGen = KeyPairGenerator.getInstance("RSA"); } catch (NoSuchAlgorithmException e) { e.printStackTrace(); } // 初始化密钥对生成器,密钥大小为96-1024位 keyPairGen.initialize(1024, new SecureRandom()); // 生成一个密钥对,保存在keyPair中 KeyPair keyPair = keyPairGen.generateKeyPair(); // 得到私钥 RSAPrivateKey privateKey = (RSAPrivateKey) keyPair.getPrivate(); // 得到公钥 RSAPublicKey publicKey = (RSAPublicKey) keyPair.getPublic(); try { // 得到公钥字符串 String publicKeyString = Base64.encode(publicKey.getEncoded()); // 得到私钥字符串 String privateKeyString = Base64.encode(privateKey.getEncoded()); // 将密钥对写入到文件 FileWriter pubfw = new FileWriter(filePath + "publicKey.keystore"); FileWriter prifw = new FileWriter(filePath + "privateKey.keystore"); BufferedWriter pubbw = new BufferedWriter(prifw); BufferedWriter pribw = new BufferedWriter(prifw); pubbw.write(publicKeyString); pribw.write(privateKeyString); pubbw.flush(); pubbw.close(); pubfw.close(); pribw.flush(); pribw.close(); prifw.close(); } catch (IOException e) { e.printStackTrace(); } } /** * 从文件中输入流中加载公钥 * @param path 公钥输入流 * @return * @throws Exception */ public static String loadPublicKeyByFile(String path) throws Exception { try { BufferedReader br = new BufferedReader(new FileReader(path + "publicKey.txt")); String readLine = null; StringBuilder sb = new StringBuilder(); while ((readLine = br.readLine()) != null) { sb.append(readLine); } br.close(); return sb.toString(); } catch (IOException e) { throw new Exception("公钥数据流读取错误"); } catch (NullPointerException e) { throw new Exception("公钥输入流为空"); } } /** * 从字符串中加载公钥 * @param publicKeyStr 公钥数据字符串 * @return * @throws Exception 加载公钥时产生的异常 */ public static RSAPublicKey loadPublicKeyByStr (String publicKeyStr) throws Exception{ try { byte[] buffer = Base64.decode(publicKeyStr); KeyFactory keyFactory = KeyFactory.getInstance("RSA"); X509EncodedKeySpec keySpec = new X509EncodedKeySpec(buffer); return (RSAPublicKey) keyFactory.generatePublic(keySpec); } catch (NoSuchAlgorithmException e) { throw new Exception("无此算法"); } catch (InvalidKeySpecException e) { e.printStackTrace(); throw new Exception("公钥非法"); } catch (NullPointerException e) { throw new Exception("公钥数据为空"); } } /** * 从文件中加载私钥 * * @param keyFileName * 私钥文件名 * @return 是否成功 * @throws Exception */ public static String loadPrivateKeyByFile(String path) throws Exception { try { BufferedReader br = new BufferedReader(new FileReader(path + "privateKey.txt")); String readLine = null; StringBuilder sb = new StringBuilder(); while ((readLine = br.readLine()) != null) { sb.append(readLine); } br.close(); return sb.toString(); } catch (IOException e) { throw new Exception("私钥数据读取错误"); } catch (NullPointerException e) { throw new Exception("私钥输入流为空"); } } public static RSAPrivateKey loadPrivateKeyByStr(String privateKeyStr) throws Exception { try { byte[] buffer = Base64.decode(privateKeyStr); PKCS8EncodedKeySpec keySpec = new PKCS8EncodedKeySpec(buffer); KeyFactory keyFactory = KeyFactory.getInstance("RSA"); return (RSAPrivateKey) keyFactory.generatePrivate(keySpec); } catch (NoSuchAlgorithmException e) { throw new Exception("无此算法"); } catch (InvalidKeySpecException e) { throw new Exception("私钥非法"); } catch (NullPointerException e) { throw new Exception("私钥数据为空"); } } /** * 公钥加密过程 * * @param publicKey * 公钥 * @param plainTextData * 明文数据 * @return * @throws Exception * 加密过程中的异常信息 */ public static byte[] encrypt(RSAPublicKey publicKey, byte[] plainTextData) throws Exception { if (publicKey == null) { throw new Exception("加密公钥为空, 请设置"); } Cipher cipher = null; try { // 使用默认RSA cipher = Cipher.getInstance("RSA"); // cipher= Cipher.getInstance("RSA", new BouncyCastleProvider()); cipher.init(Cipher.ENCRYPT_MODE, publicKey); byte[] output = cipher.doFinal(plainTextData); return output; } catch (NoSuchAlgorithmException e) { throw new Exception("无此加密算法"); } catch (NoSuchPaddingException e) { e.printStackTrace(); return null; } catch (InvalidKeyException e) { throw new Exception("加密公钥非法,请检查"); } catch (IllegalBlockSizeException e) { throw new Exception("明文长度非法"); } catch (BadPaddingException e) { throw new Exception("明文数据已损坏"); } } /** * 私钥加密过程 * * @param privateKey * 私钥 * @param plainTextData * 明文数据 * @return * @throws Exception * 加密过程中的异常信息 */ public static byte[] encrypt(RSAPrivateKey privateKey, byte[] plainTextData) throws Exception { if (privateKey == null) { throw new Exception("加密私钥为空, 请设置"); } Cipher cipher = null; try { // 使用默认RSA cipher = Cipher.getInstance("RSA"); cipher.init(Cipher.ENCRYPT_MODE, privateKey); byte[] output = cipher.doFinal(plainTextData); return output; } catch (NoSuchAlgorithmException e) { throw new Exception("无此加密算法"); } catch (NoSuchPaddingException e) { e.printStackTrace(); return null; } catch (InvalidKeyException e) { throw new Exception("加密私钥非法,请检查"); } catch (IllegalBlockSizeException e) { throw new Exception("明文长度非法"); } catch (BadPaddingException e) { throw new Exception("明文数据已损坏"); } } /** * 私钥解密过程 * * @param privateKey * 私钥 * @param cipherData * 密文数据 * @return 明文 * @throws Exception * 解密过程中的异常信息 */ public static byte[] decrypt(RSAPrivateKey privateKey, byte[] cipherData) throws Exception { if (privateKey == null) { throw new Exception("解密私钥为空, 请设置"); } Cipher cipher = null; try { // 使用默认RSA cipher = Cipher.getInstance("RSA"); // cipher= Cipher.getInstance("RSA", new BouncyCastleProvider()); cipher.init(Cipher.DECRYPT_MODE, privateKey); byte[] output = cipher.doFinal(cipherData); return output; } catch (NoSuchAlgorithmException e) { throw new Exception("无此解密算法"); } catch (NoSuchPaddingException e) { e.printStackTrace(); return null; } catch (InvalidKeyException e) { throw new Exception("解密私钥非法,请检查"); } catch (IllegalBlockSizeException e) { throw new Exception("密文长度非法"); } catch (BadPaddingException e) { throw new Exception("密文数据已损坏"); } } /** * 公钥解密过程 * * @param publicKey * 公钥 * @param cipherData * 密文数据 * @return 明文 * @throws Exception * 解密过程中的异常信息 */ public static byte[] decrypt(RSAPublicKey publicKey, byte[] cipherData) throws Exception { if (publicKey == null) { throw new Exception("解密公钥为空, 请设置"); } Cipher cipher = null; try { // 使用默认RSA cipher = Cipher.getInstance("RSA"); // cipher= Cipher.getInstance("RSA", new BouncyCastleProvider()); cipher.init(Cipher.DECRYPT_MODE, publicKey); byte[] output = cipher.doFinal(cipherData); return output; } catch (NoSuchAlgorithmException e) { throw new Exception("无此解密算法"); } catch (NoSuchPaddingException e) { e.printStackTrace(); return null; } catch (InvalidKeyException e) { throw new Exception("解密公钥非法,请检查"); } catch (IllegalBlockSizeException e) { throw new Exception("密文长度非法"); } catch (BadPaddingException e) { throw new Exception("密文数据已损坏"); } } /** * 字节数据转十六进制字符串 * * @param data * 输入数据 * @return 十六进制内容 */ public static String byteArrayToString(byte[] data) { StringBuilder stringBuilder = new StringBuilder(); for (int i = 0; i < data.length; i++) { // 取出字节的高四位 作为索引得到相应的十六进制标识符 注意无符号右移 stringBuilder.append(HEX_CHAR[(data[i] & 0xf0) >>> 4]); // 取出字节的低四位 作为索引得到相应的十六进制标识符 stringBuilder.append(HEX_CHAR[(data[i] & 0x0f)]); if (i < data.length - 1) { stringBuilder.append(' '); } } return stringBuilder.toString(); } }
2、RSA 签名验签类
import cn.hutool.core.codec.Base64; import java.security.KeyFactory; import java.security.PrivateKey; import java.security.PublicKey; import java.security.spec.PKCS8EncodedKeySpec; import java.security.spec.X509EncodedKeySpec; /** * RSA签名验签类 */ public class RSASignature { /** * 签名算法 */ public static final String SIGN_ALGORITHMS = "SHA1WithRSA"; /** * RSA签名 * * @param content * 待签名数据 * @param privateKey * 商户私钥 * @param encode * 字符集编码 * @return 签名值 */ public static String sign(String content, String privateKey, String encode) { try { PKCS8EncodedKeySpec priPKCS8 = new PKCS8EncodedKeySpec( Base64.decode(privateKey)); KeyFactory keyf = KeyFactory.getInstance("RSA"); PrivateKey priKey = keyf.generatePrivate(priPKCS8); java.security.Signature signature = java.security.Signature .getInstance(SIGN_ALGORITHMS); signature.initSign(priKey); signature.update(content.getBytes(encode)); byte[] signed = signature.sign(); return Base64.encode(signed); } catch (Exception e) { e.printStackTrace(); } return null; } public static String sign(String content, String privateKey) { try { PKCS8EncodedKeySpec priPKCS8 = new PKCS8EncodedKeySpec( Base64.decode(privateKey)); KeyFactory keyf = KeyFactory.getInstance("RSA"); PrivateKey priKey = keyf.generatePrivate(priPKCS8); java.security.Signature signature = java.security.Signature .getInstance(SIGN_ALGORITHMS); signature.initSign(priKey); signature.update(content.getBytes()); byte[] signed = signature.sign(); return Base64.encode(signed); } catch (Exception e) { e.printStackTrace(); } return null; } /** * RSA验签名检查 * * @param content * 待签名数据 * @param sign * 签名值 * @param publicKey * 分配给开发商公钥 * @param encode * 字符集编码 * @return 布尔值 */ public static boolean doCheck(String content, String sign, String publicKey, String encode) { try { KeyFactory keyFactory = KeyFactory.getInstance("RSA"); byte[] encodedKey = Base64.decode(publicKey); PublicKey pubKey = keyFactory .generatePublic(new X509EncodedKeySpec(encodedKey)); java.security.Signature signature = java.security.Signature .getInstance(SIGN_ALGORITHMS); signature.initVerify(pubKey); signature.update(content.getBytes(encode)); boolean bverify = signature.verify(Base64.decode(sign)); return bverify; } catch (Exception e) { e.printStackTrace(); } return false; } public static boolean doCheck(String content, String sign, String publicKey) { try { KeyFactory keyFactory = KeyFactory.getInstance("RSA"); byte[] encodedKey = Base64.decode(publicKey); PublicKey pubKey = keyFactory .generatePublic(new X509EncodedKeySpec(encodedKey)); java.security.Signature signature = java.security.Signature .getInstance(SIGN_ALGORITHMS); signature.initVerify(pubKey); signature.update(content.getBytes()); boolean bverify = signature.verify(Base64.decode(sign)); return bverify; } catch (Exception e) { e.printStackTrace(); } return false; } }
3、测试+验证
import cn.hutool.core.codec.Base64; /** * RSA私钥签名,公钥验证 */ public class RSATest { public static void main(String[] args) throws Exception{ String filepath="D:\\sign\\"; //RSAEncrypt.genKeyPair(filepath); System.out.println("--------------公钥加密私钥解密过程-------------------"); //需要加密的原文本内容 String plainText="123456"; //公钥加密过程 byte[] cipherData=RSAEncrypt.encrypt(RSAEncrypt.loadPublicKeyByStr(RSAEncrypt.loadPublicKeyByFile(filepath)),plainText.getBytes()); String cipher = Base64.encode(cipherData); //私钥解密过程 byte[] res=RSAEncrypt.decrypt(RSAEncrypt.loadPrivateKeyByStr(RSAEncrypt.loadPrivateKeyByFile(filepath)), Base64.decode(cipher)); String restr=new String(res); System.out.println("原文:"+plainText); System.out.println("加密:"+cipher); System.out.println("解密:"+restr); System.out.println(); System.out.println("--------------私钥加密公钥解密过程-------------------"); //需要加密的原文本内容 plainText="123456"; //私钥加密过程 cipherData=RSAEncrypt.encrypt(RSAEncrypt.loadPrivateKeyByStr(RSAEncrypt.loadPrivateKeyByFile(filepath)),plainText.getBytes()); cipher=Base64.encode(cipherData); //公钥解密过程 res=RSAEncrypt.decrypt(RSAEncrypt.loadPublicKeyByStr(RSAEncrypt.loadPublicKeyByFile(filepath)), Base64.decode(cipher)); restr=new String(res); System.out.println("原文:"+plainText); System.out.println("加密:"+cipher); System.out.println("解密:"+restr); System.out.println(); System.out.println("---------------私钥签名过程------------------"); //需要加密的原文本内容 String content="123456"; String signstr=RSASignature.sign(content,RSAEncrypt.loadPrivateKeyByFile(filepath)); System.out.println("签名原串:"+content); System.out.println("签名串:"+signstr); System.out.println(); System.out.println("---------------公钥校验签名------------------"); System.out.println("签名原串:"+content); System.out.println("签名串:"+signstr); System.out.println("验签结果:"+RSASignature.doCheck(content, signstr, RSAEncrypt.loadPublicKeyByFile(filepath))); System.out.println(); } }
4、输出的结果
--------------公钥加密私钥解密过程------------------- 原文:123456 加密:eK07p5I+vHMKG++vI18SBSkC0ZpBUpLhrLRNSbYo2wADYNt+r1L1dDRKXLGc5V+KjjLSxAolPAx22hJLux/Sprk8c+w3n82Swv0YXBKBxXz/5V3dJTIANW2XUjIqSkpG2OMLJYPgoG75+H8I1EQ1nTQ6o4WHi+sliAMjsu2sxmY= 解密:123456 --------------私钥加密公钥解密过程------------------- 原文:123456 加密:RvcDQDKH86xAWa1UqF8Gsu+y/K/fiqTxNGzXN/SgJknl/3un7QMbuW3Ru6UaeOrUqpv1nDj2gvpNxgVf6PRFfeYIcjWEgTcKvDm23QP5a4+AENXGg6zTWt7NnTV501LydAPgRp3tMYeGROnOKnk8RGy0s9zS32kvZqQ3J+2KyCA= 解密:123456 ---------------私钥签名过程------------------ 签名原串:123456 签名串:fIgsYHuovN1cRKQXePOsK1yRcQ4Rjxm+iAvvk0H1WtAyOMdyAnGQ9euBA3okZcSxtZpUyLjp0mmwunovx5YjiMn176RwtV/XEgzfI4Zid4z8uuavy69F+lJZkZGmiRqPx2m3ARKsQVNFWfoDEJKsnDZ8I4jQHSycIjS+7AcNaDA= ---------------公钥校验签名------------------ 签名原串:123456 签名串:fIgsYHuovN1cRKQXePOsK1yRcQ4Rjxm+iAvvk0H1WtAyOMdyAnGQ9euBA3okZcSxtZpUyLjp0mmwunovx5YjiMn176RwtV/XEgzfI4Zid4z8uuavy69F+lJZkZGmiRqPx2m3ARKsQVNFWfoDEJKsnDZ8I4jQHSycIjS+7AcNaDA= 验签结果:true




 浙公网安备 33010602011771号
浙公网安备 33010602011771号