实验3:OpenFlow协议分析实践
实验3:OpenFlow协议分析实践
一、实验目的
- 能够运用 wireshark 对 OpenFlow 协议数据交互过程进行抓包;
- 能够借助包解析工具,分析与解释 OpenFlow协议的数据包交互过程与机制。
二、实验环境
- 下载虚拟机软件Oracle VisualBox;
- 在虚拟机中安装Ubuntu 20.04 Desktop amd64,并完整安装Mininet;
三、实验要求
(一)基本要求
- 搭建下图所示拓扑,完成相关 IP 配置,并实现主机与主机之间的 IP 通信。用抓包软件获取控制器与交换机之间的通信数据包。
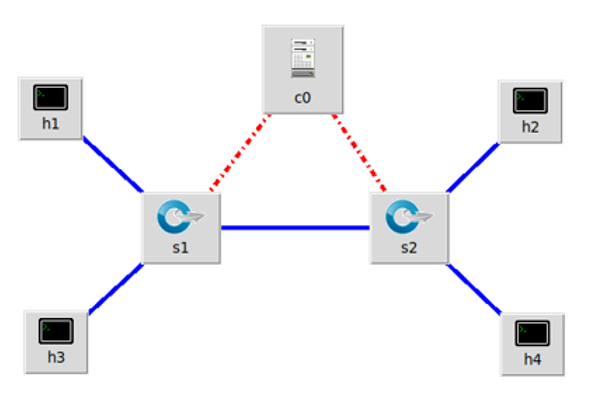
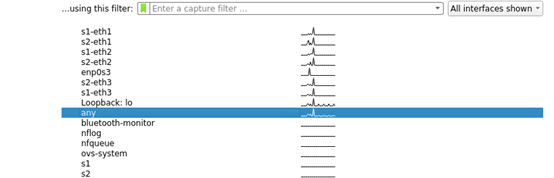
- 执行拓扑文件
- 运行
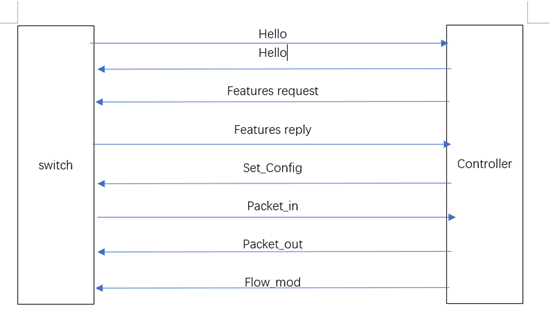
sudo wireshark命令,并选择any模式进行抓包,开启另一个终端,命令行运行031902241.py文件,运行pingall
![]()
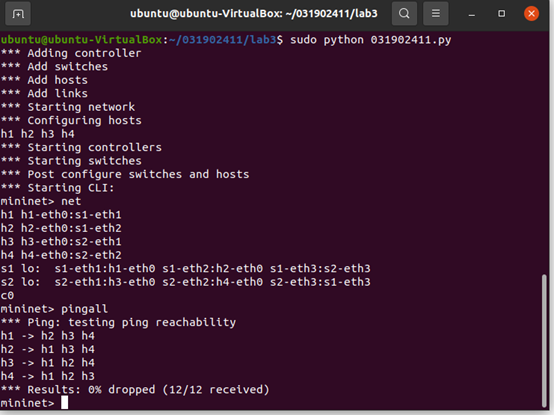
- 查看抓包结果,分析OpenFlow协议中交换机与控制器的消息交互过程,画出相关交互图或流程图。
-
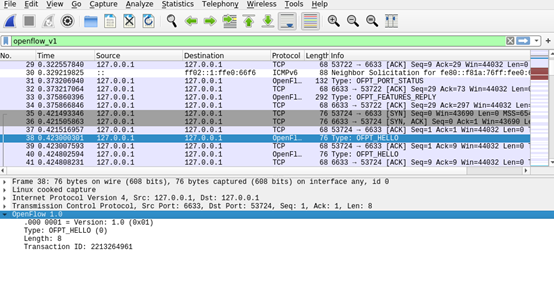
hello
-
6633->53724
![]()
-
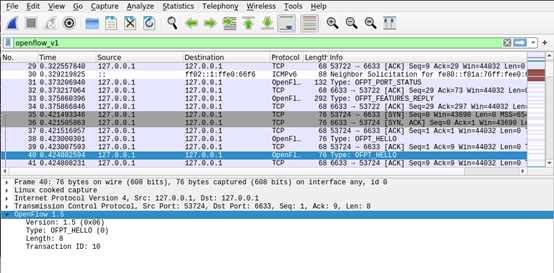
53724->6633
![]()
-
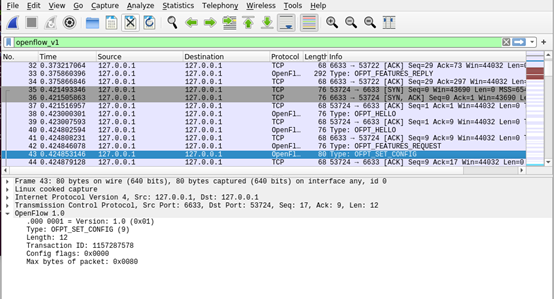
OFPT_FEATURES_REQUEST
![]()
-
OFPT_SET_CONFIG
![]()
-
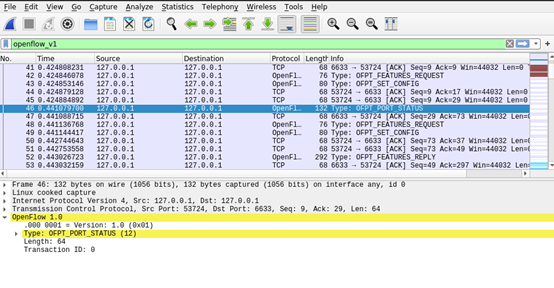
OFPT_PORT_STATUS
![]()
-
OFPT_FEATURES_REPLY
![]()
-
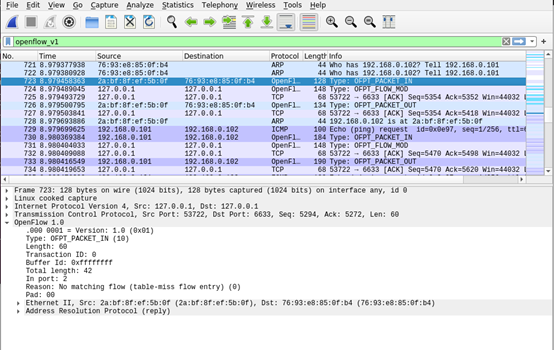
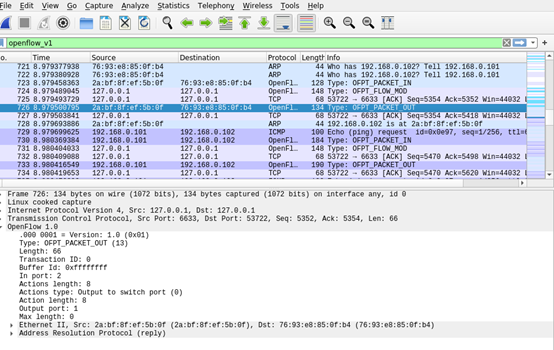
OFPT_PACKET_IN
![]()
-
OFPT_FLOW_MOD
![]()
-
OFPT_PACKET_OUT
![]()
2.相关流程图:
3.回答问题:交换机与控制器建立通信时是使用TCP协议还是UDP协议?
答:从所抓取的报文中可以看到Transmission Control Protocol。故是TCP协议。
(二)进阶要求
将抓包结果对照OpenFlow源码,了解OpenFlow主要消息类型对应的数据结构定义。相关数据结构可在openflow安装目录openflow/include/openflow当中的openflow.h头文件中查询到。
- hello
![]()
struct ofp_header {
uint8_t version; /* OFP_VERSION. */
uint8_t type; /* One of the OFPT_ constants. */
uint16_t length; /* Length including this ofp_header. */
uint32_t xid; /* Transaction id associated with this packet.
Replies use the same id as was in the request
to facilitate pairing. */
};
struct ofp_hello {
struct ofp_header header;
};
可以看到对应了HELLO报文的四个参数:版本号、消息类型、长度、ID
-
Features Request(Features Request的结构同hello),与上述ofp_header结构体中数据相同
-
Set config(除header外增加了两个属性),代码如下:
/* Switch configuration. */
struct ofp_switch_config {
struct ofp_header header;
uint16_t flags; /* OFPC_* flags. */
uint16_t miss_send_len; /* Max bytes of new flow that datapath should
send to the controller. */
};
-
PORT_STATUS(在OpenFlow交换机中添加、删除或修改物理端口时,需要发送Port-Status 消息来通知OpenFlow 控制器)
/* A physical port has changed in the datapath */ struct ofp_port_status { struct ofp_header header; uint8_t reason; /* One of OFPPR_*. */ uint8_t pad[7]; /* Align to 64-bits. */ struct ofp_phy_port desc; }; -
FEATURES_REPLY(除了header还包括唯一ID号、缓冲区可以缓存的最大数据包个数、流表数量、功能、动作、端口等
struct ofp_switch_features { struct ofp_header header; uint64_t datapath_id; /* Datapath unique ID. The lower 48-bits are for a MAC address, while the upper 16-bits are implementer-defined. */ uint32_t n_buffers; /* Max packets buffered at once. */ uint8_t n_tables; /* Number of tables supported by datapath. */ uint8_t pad[3]; /* Align to 64-bits. */ /* Features. */ uint32_t capabilities; /* Bitmap of support "ofp_capabilities". */ uint32_t actions; /* Bitmap of supported "ofp_action_type"s. */ /* Port info.*/ struct ofp_phy_port ports[0]; /* Port definitions. The number of ports is inferred from the length field in the header. */ }; /* Description of a physical port */ struct ofp_phy_port { uint16_t port_no; uint8_t hw_addr[OFP_ETH_ALEN]; char name[OFP_MAX_PORT_NAME_LEN]; /* Null-terminated */ uint32_t config; /* Bitmap of OFPPC_* flags. */ uint32_t state; /* Bitmap of OFPPS_* flags. */ /* Bitmaps of OFPPF_* that describe features. All bits zeroed if * unsupported or unavailable. */ uint32_t curr; /* Current features. */ uint32_t advertised; /* Features being advertised by the port. */ uint32_t supported; /* Features supported by the port. */ uint32_t peer; /* Features advertised by peer. */ }; -
PACKET_IN(数据包括该数据包位于交换机缓冲区的ID、长度、进入端口号、数据包等)
情况1:交换机查找流表,发现没有匹配条目,但是这种包没有抓到过 enum ofp_packet_in_reason { OFPR_NO_MATCH, /* No matching flow. */ OFPR_ACTION /* Action explicitly output to controller. */ }; 情况2:有匹配条目,对应的action是OUTPUT=CONTROLLER,固定收到向控制器发送包 struct ofp_packet_in { struct ofp_header header; uint32_t buffer_id; /* ID assigned by datapath. */ uint16_t total_len; /* Full length of frame. */ uint16_t in_port; /* Port on which frame was received. */ uint8_t reason; /* Reason packet is being sent (one of OFPR_*) */ uint8_t pad; uint8_t data[0]; /* Ethernet frame, halfway through 32-bit word, so the IP header is 32-bit aligned. The amount of data is inferred from the length field in the header. Because of padding, offsetof(struct ofp_packet_in, data) == sizeof(struct ofp_packet_in) - 2. */ }; -
PACKET_OUT(包括动作列表、缓冲区ID等)
struct ofp_packet_out { struct ofp_header header; uint32_t buffer_id; /* ID assigned by datapath (-1 if none). */ uint16_t in_port; /* Packet's input port (OFPP_NONE if none). */ uint16_t actions_len; /* Size of action array in bytes. */ struct ofp_action_header actions[0]; /* Actions. */ /* uint8_t data[0]; */ /* Packet data. The length is inferred from the length field in the header. (Only meaningful if buffer_id == -1.) */ }; -
FLOW_MOD(包括流表项标志符cookie,command代表五种操作,对应值分别为0-4,优先级等)
struct ofp_flow_mod { struct ofp_header header; struct ofp_match match; /* Fields to match */ uint64_t cookie; /* Opaque controller-issued identifier. */ /* Flow actions. */ uint16_t command; /* One of OFPFC_*. */ uint16_t idle_timeout; /* Idle time before discarding (seconds). */ uint16_t hard_timeout; /* Max time before discarding (seconds). */ uint16_t priority; /* Priority level of flow entry. */ uint32_t buffer_id; /* Buffered packet to apply to (or -1). Not meaningful for OFPFC_DELETE*. */ uint16_t out_port; /* For OFPFC_DELETE* commands, require matching entries to include this as an output port. A value of OFPP_NONE indicates no restriction. */ uint16_t flags; /* One of OFPFF_*. */ struct ofp_action_header actions[0]; /* The action length is inferred from the length field in the header. */ }; struct ofp_action_header { uint16_t type; /* One of OFPAT_*. */ uint16_t len; /* Length of action, including this header. This is the length of action, including any padding to make it 64-bit aligned. */ uint8_t pad[4]; };(三)个人总结
-
这次实验比前几次来的简单一点,通过老师上课的实验讲解以及课后的实验指导书学习可以较为轻松的完成这次实验。
-
遇到的困难及解决办法:
困难1:未抓到Hello包 解决方法:先打开wireshark后再运行py文件即可。
困难2:未找到交换机送往控制器的Hello包 解决办法:使用过滤器过滤openflow_v4后成功找到该包
-
本次实验通过抓取数据包并进行分析,学习了解了Openflow协议下控制器与交换机之间的交互过程,作为一次验证性实验,难度并不大。进阶部分通过查看源码并且与数据包字段进行比较,使得对于协议有了进一步的了解,总体感觉相对良好。





 浙公网安备 33010602011771号
浙公网安备 33010602011771号