羊城杯wp babyre
肝了好久,没爆破出来,就很难受,就差这题没写了,其他三题感觉挺简单的,这题其实也不是很难,我感觉是在考算法。
在输入之前有个smc的函数,先动调,attach上去,ida打开那个关键函数。
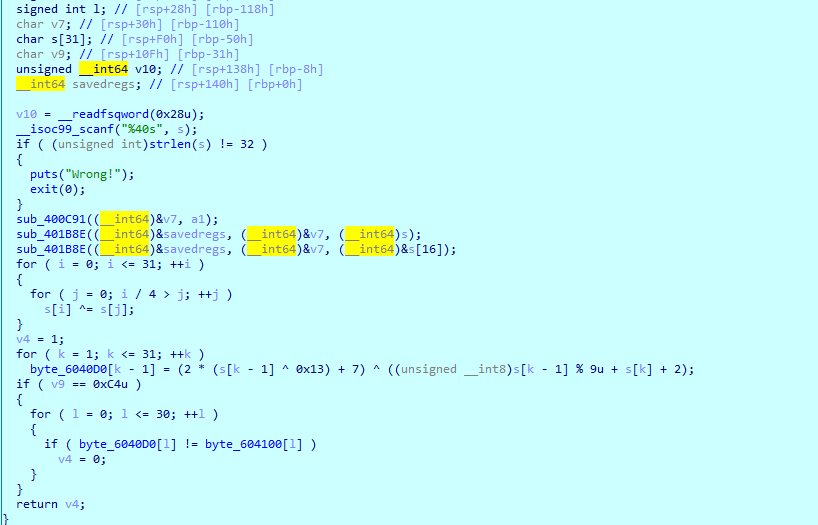
代码逻辑还是很清晰的,坑的地方就是在最后一个异或那里,题目已经给出了最后一个字符是0xC4了,这样我以为可以倒着求,发现写完算法,缺了十几位,
我反复的验证,发现有多解,但是当时凌晨2点多了,我脑子也坏了,没想到是深搜,当时在ipad上演算了一下,发现有多解,相当于分叉,今天看了表哥的,wp
才想起来,就是一个分叉路的图,可以用深搜去解决,下次记得了,这波放个表哥的wp
from Crypto.Cipher import AES from hashlib import md5 input=[0 for i in range(32)] input[31]=0xC4 res=[0xBD, 0xAD, 0xB4, 0x84, 0x10, 0x63, 0xB3, 0xE1, 0xC6, 0x84, 0x2D, 0x6F, 0xBA, 0x88, 0x74, 0xC4, 0x90, 0x32, 0xEA, 0x2E, 0xC6, 0x28, 0x65, 0x70, 0xC9, 0x75, 0x78, 0xA0, 0x0B, 0x9F, 0xA6, 0x00, 0x30, 0xE4, 0xD2, 0xC3, 0xEF, 0x75, 0xED, 0xA8, 0xE1, 0xA1, 0x73, 0x81, 0xE2, 0xE9, 0xAB, 0xC8, 0xBF, 0xCA, 0x52, 0xE8, 0xED, 0x6B, 0xA2, 0x39, 0x86, 0x21, 0xD0, 0xF6, 0x50, 0x3E, 0xF3] res=res[:32] ans=[] def sou(input,deep): if deep==0: x=input.copy() ans.append(x) return else: for i in range(256): if((2*(i^0x13)+7)^(i%9+input[deep]+2))&0xff==res[deep-1]: input[deep-1]=i sou(input,deep-1) sou(input,31) for tmp in ans: for i in range(31, -1, -1): for j in range(int(i/4)): tmp[i] ^= tmp[j] aes = AES.new(b"th1s1sth3n1c3k3y", mode=AES.MODE_ECB) res = aes.decrypt(bytes(tmp)) if res.startswith(b"GWHT{"): print(res) print(md5(res[5:-1]).hexdigest())


 浙公网安备 33010602011771号
浙公网安备 33010602011771号